denying access to the administrator
Trying to install my printer. It is compatible with vista. tell me, he needs administrator access denied. I am the administrator. How to spend it
Right click > run as admin.
See you soon. Mick Murphy - Microsoft partner
Tags: Windows
Similar Questions
-
Access to the administration via VPN to 887 after config setup pro
Hi all
Ive just made a three 887w for a client in a few branches, and as this is the first time I have deployed these devices, I decided to go with the GUI (downloaded config pro 2.3) to get the configuration made that I had some constraints of time to get them in place (sometimes I go with the graphical interface first and then look back at the CLI to see what as its been) (, then hand it in Notepad to get a better understanding of the new features of the CLI may be gone and allowed).
One thing I again, that I was going to do face was my first experience of the firewall IOS area type of config...
At this point, I'm still unclear on the config (where why Im posting here I guess!) - but the main problem I have at the moment is with managing access to devices.
Particularly with regard to access to the administration of headquarters inside the IP address of the branch routers.
I should mention that the branch routers are connected to Headquarters by connections IPSec site-to-site VPN and these connections are all very good, all connectivity (PC server, PC, printer, etc.) is very well... I can also send packets (using the inside of the interface as a source) ping from branch routers to servers on the headquarters LAN.
Set up access to administration using config pro to allow access to the router on the subnet headquarters (on its inside interface), as well as the local subnet and also SSH access to a specific host from the internet - the local subnet and the only host on the internet can access the router very well.
I'm not sure if the problem is with the ZBF config or if its something really obvious Im missing! -Ive done routers branch several times previously, so with this being the first config ZBF I did, so I came to the conclusion that there must be something in the absence of my understanding.
Any help greatly appreciated... sanitized config below!
Thanks in advance
Paul
version 15.1
no service button
tcp KeepAlive-component snap-in service
a tcp-KeepAlive-quick service
horodateurs service debug datetime localtime show-timezone msec
Log service timestamps datetime localtime show-timezone msec
encryption password service
sequence numbers service
!
hostname name-model
!
boot-start-marker
boot-end-marker
!
logging buffered 51200
recording console critical
enable secret 5 xxxxxxxxxxxxxxxxxxxxxxxx
!
No aaa new-model
!
iomem 10 memory size
clock timezone PCTime 0
PCTime of summer time clock day March 30, 2003 01:00 October 26, 2003 02:00
Service-module wlan-ap 0 autonomous bootimage
!
Crypto pki trustpoint TP-self-signed-2874941309
enrollment selfsigned
name of the object cn = IOS - Self - signed - certificate - 2874941309
revocation checking no
rsakeypair TP-self-signed-2874941309
!
!
TP-self-signed-2874941309 crypto pki certificate chain
certificate self-signed 01
no ip source route
!
!
DHCP excluded-address IP 10.0.0.1 10.0.0.63
DHCP excluded-address IP 10.0.0.193 10.0.0.254
!
DHCP IP CCP-pool
import all
Network 10.0.0.0 255.255.255.0
default router 10.0.0.1
xxxxxxxxx.com domain name
Server DNS 192.168.xx.20 194.74.xx.68
Rental 2 0
!
!
IP cef
no ip bootp Server
IP domain name xxxxxxx.com
name of the server IP 192.168.XX.20
name of the server IP 194.74.XX.68
No ipv6 cef
!
!
Authenticated MultiLink bundle-name Panelparameter-card type urlfpolicy websense cpwebpara0
Server 192.168.xx.25
source-interface Vlan1
allow mode on
parameter-card type urlf-glob cpaddbnwlocparapermit0
model citrix.xxxxxxxxxxxx.comlicense udi pid xxxxxxxxxxx sn CISCO887MW-GN-E-K9
!
!
username xxxxxxx privilege 15 secret 5 xxxxxxxxxxxxxxxxxxxxx
username privilege 15 secret 5 xxxxxxxxx xxxxxxxxxxxxxxxxxxxxxxxxxx
!
!
!
!
synwait-time of tcp IP 10
!
type of class-card inspect correspondence sdm-cls-VPNOutsideToInside-1
game group-access 106
type of class-card inspect entire game SDM_SHELL
match the name of group-access SDM_SHELL
type of class-card inspect entire game SDM_SSH
match the name of group-access SDM_SSH
type of class-card inspect entire game SDM_HTTPS
match the name of group-access SDM_HTTPS
type of class-card inspect all match sdm-mgmt-cls-0
corresponds to the SDM_SHELL class-map
corresponds to the SDM_SSH class-map
corresponds to the SDM_HTTPS class-map
type of class-card inspect entire game SDM_AH
match the name of group-access SDM_AH
type of class-card inspect entire game SDM_ESP
match the name of group-access SDM_ESP
type of class-card inspect entire game SDM_VPN_TRAFFIC
match Protocol isakmp
match Protocol ipsec-msft
corresponds to the SDM_AH class-map
corresponds to the SDM_ESP class-map
type of class-card inspect the correspondence SDM_VPN_PT
game group-access 105
corresponds to the SDM_VPN_TRAFFIC class-map
type of class-card inspect entire game PAC-cls-insp-traffic
match Protocol cuseeme
dns protocol game
ftp protocol game
h323 Protocol game
https protocol game
match icmp Protocol
match the imap Protocol
pop3 Protocol game
netshow Protocol game
Protocol shell game
match Protocol realmedia
match rtsp Protocol
smtp Protocol game
sql-net Protocol game
streamworks Protocol game
tftp Protocol game
vdolive Protocol game
tcp protocol match
udp Protocol game
inspect the class-map match PAC-insp-traffic type
corresponds to the class-map PAC-cls-insp-traffic
type of class-map urlfilter match - all cpaddbnwlocclasspermit0
Server-domain urlf-glob cpaddbnwlocparapermit0 match
type of class-card inspect entire game PAC-cls-icmp-access
match icmp Protocol
tcp protocol match
udp Protocol game
class-map type urlfilter websense match - all cpwebclass0
match any response from the server
type of class-card inspect correspondence ccp-invalid-src
game group-access 100
type of class-card inspect correspondence ccp-icmp-access
corresponds to the class-ccp-cls-icmp-access card
type of class-card inspect sdm-mgmt-cls-ccp-permit-0 correspondence
corresponds to the class-map sdm-mgmt-cls-0
game group-access 103
type of class-card inspect correspondence ccp-Protocol-http
http protocol game
!
!
type of policy-card inspect PCB-permits-icmpreply
class type inspect PCB-icmp-access
inspect
class class by default
Pass
type of policy-card inspect sdm-pol-VPNOutsideToInside-1
class type inspect sdm-cls-VPNOutsideToInside-1
inspect
class class by default
drop
type of policy-card inspect urlfilter cppolicymap-1
urlfpolicy websense cpwebpara0 type parameter
class type urlfilter cpaddbnwlocclasspermit0
allow
Journal
class type urlfilter websense cpwebclass0
Server-specified-action
Journal
type of policy-map inspect PCB - inspect
class type inspect PCB-invalid-src
Drop newspaper
class type inspect PCB-Protocol-http
inspect
service-policy urlfilter cppolicymap-1
class type inspect PCB-insp-traffic
inspect
class class by default
drop
type of policy-card inspect PCB-enabled
class type inspect SDM_VPN_PT
Pass
class type inspect sdm-mgmt-cls-ccp-permit-0
inspect
class class by default
drop
!
security of the area outside the area
safety zone-to-zone
zone-pair security PAC-zp-self-out source destination outside zone auto
type of service-strategy inspect PCB-permits-icmpreply
zone-pair security PAC-zp-in-out source in the area of destination outside the area
type of service-strategy inspect PCB - inspect
source of PAC-zp-out-auto security area outside zone destination auto pair
type of service-strategy inspect PCB-enabled
sdm-zp-VPNOutsideToInside-1 zone-pair security source outside the area of destination in the area
type of service-strategy inspect sdm-pol-VPNOutsideToInside-1
!
!
crypto ISAKMP policy 1
BA 3des
preshared authentication
Group 2
ISAKMP crypto key address 194.105.xxx.xxx xxxxxxxxxxxx
!
!
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
!
map SDM_CMAP_1 1 ipsec-isakmp crypto
Description Tunnel to194.105.xxx.xxx
the value of 194.105.xxx.xxx peer
game of transformation-ESP-3DES-SHA
match address VPN - ACL
!
!
!
!
!
interface BRI0
no ip address
no ip redirection
no ip unreachable
no ip proxy-arp
penetration of the IP stream
encapsulation hdlc
Shutdown
Multidrop ISDN endpoint
!
ATM0 interface
no ip address
no ip redirection
no ip unreachable
no ip proxy-arp
penetration of the IP stream
No atm ilmi-keepalive
!
point-to-point interface ATM0.1
Description $ES_WAN$
no ip redirection
no ip unreachable
no ip proxy-arp
penetration of the IP stream
PVC 0/38
aal5mux encapsulation ppp Dialer
Dialer pool-member 1
!
!
interface FastEthernet0
!
interface FastEthernet1
!
interface FastEthernet2
!
interface FastEthernet3
!
wlan-ap0 interface
description of the Service interface module to manage the embedded AP
IP unnumbered Vlan1
no ip redirection
no ip unreachable
no ip proxy-arp
penetration of the IP stream
ARP timeout 0
!
interface GigabitEthernet0 Wlan
Description interface connecting to the AP the switch embedded internal
!
interface Vlan1
Description $ETH - SW - LAUNCH, INTF-INFO-HWIC $$ $4ESW $FW_INSIDE$
the IP 10.0.0.1 255.255.255.0
IP access-group 104 to
no ip redirection
no ip unreachable
no ip proxy-arp
penetration of the IP stream
IP nat inside
IP virtual-reassembly
Security members in the box area
IP tcp adjust-mss 1452
!
interface Dialer0
Description $FW_OUTSIDE$
IP address 81.142.xxx.xxx 255.255.xxx.xxx
IP access-group 101 in
no ip redirection
no ip unreachable
no ip proxy-arp
penetration of the IP stream
NAT outside IP
IP virtual-reassembly
outside the area of security of Member's area
encapsulation ppp
Dialer pool 1
Dialer-Group 1
Authentication callin PPP chap Protocol
PPP chap hostname xxxxxxxxxxxxxxxx
PPP chap password 7 xxxxxxxxxxxxxxxxx
No cdp enable
map SDM_CMAP_1 crypto
!
IP forward-Protocol ND
IP http server
23 class IP http access
local IP http authentication
IP http secure server
IP http timeout policy slowed down 60 life 86400 request 10000
!
!
IP nat inside source overload map route SDM_RMAP_1 interface Dialer0
IP route 0.0.0.0 0.0.0.0 Dialer0
!
SDM_AH extended IP access list
Note the category CCP_ACL = 1
allow a whole ahp
SDM_ESP extended IP access list
Note the category CCP_ACL = 1
allow an esp
SDM_HTTP extended IP access list
Note the category CCP_ACL = 0
permit tcp any any eq www
SDM_HTTPS extended IP access list
Note the category CCP_ACL = 0
permit any any eq 443 tcp
SDM_SHELL extended IP access list
Note the category CCP_ACL = 0
permit tcp any any eq cmd
SDM_SNMP extended IP access list
Note the category CCP_ACL = 0
allow udp any any eq snmp
SDM_SSH extended IP access list
Note the category CCP_ACL = 0
permit tcp any any eq 22
SDM_TELNET extended IP access list
Note the category CCP_ACL = 0
permit tcp any any eq telnet
scope of access to IP-VPN-ACL list
Note ACLs to identify a valuable traffic to bring up the VPN tunnel
Note the category CCP_ACL = 4
Licensing ip 10.0.0.0 0.0.0.255 192.168.xx.0 0.0.0.255
Licensing ip 10.0.0.0 0.0.0.255 10.128.xx.0 0.0.255.255
Licensing ip 10.0.0.0 0.0.0.255 160.69.xx.0 0.0.255.255
!
recording of debug trap
Note category of access list 1 = 2 CCP_ACL
access-list 1 permit 10.0.0.0 0.0.0.255
access-list 23 allow 193.195.xxx.xxx
Note access-list 23 category CCP_ACL = 17
access-list 23 permit 192.168.xx.0 0.0.0.255
access-list 23 allow 10.0.0.0 0.0.0.255
Access-list 100 category CCP_ACL = 128 note
access-list 100 permit ip 255.255.255.255 host everything
access-list 100 permit ip 127.0.0.0 0.255.255.255 everything
access-list 100 permit ip 81.142.xxx.xxx 0.0.0.7 everything
Access-list 101 remark self-generated by SDM management access feature
Note access-list 101 category CCP_ACL = 1
access-list 101 permit tcp host 193.195.xxx.xxx host 81.142.xxx.xxx eq 22
access-list 101 permit tcp host 193.195.xxx.xxx host 81.142.xxx.xxx eq 443
access-list 101 permit tcp host 193.195.xxx.xxx host 81.142.xxx.xxx eq cmd
access-list 101 tcp refuse any host 81.142.xxx.xxx eq telnet
access-list 101 tcp refuse any host 81.142.xxx.xxx eq 22
access-list 101 tcp refuse any host 81.142.xxx.xxx eq www
access-list 101 tcp refuse any host 81.142.xxx.xxx eq 443
access-list 101 tcp refuse any host 81.142.xxx.xxx eq cmd
access-list 101 deny udp any host 81.142.xxx.xxx eq snmp
access-list 101 permit ip 160.69.0.0 0.0.255.255 10.0.0.0 0.0.0.255
access-list 101 permit ip 10.128.0.0 0.0.255.255 10.0.0.0 0.0.0.255
access-list 101 permit ip 192.168.xx.0 0.0.0.255 10.0.0.0 0.0.0.255
access-list 101 permit udp host 194.105.xxx.xxx host 81.142.xxx.xxx eq non500-isakmp
access-list 101 permit udp host 194.105.xxx.xxx host 81.142.xxx.xxx eq isakmp
access-list 101 permit host 194.105.xxx.xxx host 81.142.xxx.xxx esp
access-list 101 permit ahp host 194.105.xxx.xxx host 81.142.xxx.xxx
access list 101 ip allow a whole
Note access-list 102 CCP_ACL category = 1
access-list 102 permit ip 192.168.xx.0 0.0.0.255 everything
access-list 102 permit ip host 193.195.xxx.xxx all
access-list 102 permit ip 10.0.0.0 0.0.0.255 any
Note access-list 103 self-generated by SDM management access feature
Note access-list 103 CCP_ACL category = 1
access-list 103 allow ip host 193.195.xxx.xxx host 81.142.xxx.xxx
Note access-list 104 self-generated by SDM management access feature
Note access-list 104 CCP_ACL category = 1
access-list 104 permit tcp 192.168.xx.0 0.0.0.255 host 10.0.0.1 eq telnet
access-list 104 permit tcp 10.0.0.0 0.0.0.255 host 10.0.0.1 eq telnet
access-list 104 permit tcp 192.168.xx.0 0.0.0.255 eq on host 10.0.0.1 22
access-list 104 permit tcp 10.0.0.0 0.0.0.255 host 10.0.0.1 eq 22
access-list 104 permit tcp 192.168.xx.0 0.0.0.255 host 10.0.0.1 eq www
access-list 104 permit tcp 10.0.0.0 0.0.0.255 eq to host 10.0.0.1 www
access-list 104 permit tcp 192.168.xx.0 0.0.0.255 host 10.0.0.1 eq 443
access-list 104 permit tcp 10.0.0.0 0.0.0.255 host 10.0.0.1 eq 443
access-list 104 permit tcp 192.168.xx.0 0.0.0.255 host 10.0.0.1 eq cmd
access-list 104 permit tcp 10.0.0.0 0.0.0.255 host 10.0.0.1 eq cmd
access-list 104 tcp refuse any host 10.0.0.1 eq telnet
access-list 104 tcp refuse any host 10.0.0.1 eq 22
access-list 104 tcp refuse any host 10.0.0.1 eq www
access-list 104 tcp refuse any host 10.0.0.1 eq 443
access-list 104 tcp refuse any host 10.0.0.1 eq cmd
access-list 104 deny udp any host 10.0.0.1 eq snmp
104 ip access list allow a whole
Note access-list 105 CCP_ACL category = 128
access-list 105 permit ip host 194.105.xxx.xxx all
Note access-list 106 CCP_ACL category = 0
access-list 106 allow ip 192.168.xx.0 0.0.0.255 10.0.0.0 0.0.0.255
access-list 106 allow ip 10.128.0.0 0.0.255.255 10.0.0.0 0.0.0.255
access-list 106 allow ip 160.69.0.0 0.0.255.255 10.0.0.0 0.0.0.255
Note category from the list of access-107 = 2 CCP_ACL
access-list 107 deny ip 10.0.0.0 0.0.0.255 160.69.0.0 0.0.255.255
access-list 107 deny ip 10.0.0.0 0.0.0.255 10.128.0.0 0.0.255.255
access-list 107 deny ip 10.0.0.0 0.0.0.255 192.168.xx.0 0.0.0.255
access-list 107 allow ip 10.0.0.0 0.0.0.255 any
Dialer-list 1 ip protocol allow
not run cdp!
!
!
!
allowed SDM_RMAP_1 1 route map
corresponds to the IP 107
!
!
control plan
!
!
Line con 0
local connection
no activation of the modem
line to 0
line 2
no activation-character
No exec
preferred no transport
transport of entry all
line vty 0 4
access-class 102 in
privilege level 15
local connection
transport input telnet ssh
!
Scheduler allocate 4000 1000
Scheduler interval 500
NTP-Calendar Update
130.159.196.118 source Dialer0 preferred NTP server
endHi Paul,.
Here is the relevant configuration:
type of policy-card inspect PCB-enabled
class type inspect sdm-mgmt-cls-ccp-permit-0
inspecttype of class-card inspect sdm-mgmt-cls-ccp-permit-0 correspondence
corresponds to the class-map sdm-mgmt-cls-0
game group-access 103type of class-card inspect all match sdm-mgmt-cls-0
corresponds to the SDM_SHELL class-map
corresponds to the SDM_SSH class-map
corresponds to the SDM_HTTPS class-maptype of class-card inspect entire game SDM_SHELL
match the name of group-access SDM_SHELL
type of class-card inspect entire game SDM_SSH
match the name of group-access SDM_SSH
type of class-card inspect entire game SDM_HTTPS
match the name of group-access SDM_HTTPSSDM_SHELL extended IP access list
Note the category CCP_ACL = 0
permit tcp any any eq cmd
SDM_SSH extended IP access list
Note the category CCP_ACL = 0
permit tcp any any eq 22
SDM_HTTPS extended IP access list
Note the category CCP_ACL = 0
permit any any eq 443 tcpNote access-list 103 self-generated by SDM management access feature
Note access-list 103 CCP_ACL category = 1
access-list 103 allow ip host 193.195.xxx.xxx host 81.142.xxx.xxxThe above configuration will allow you to access the router on the 81.142.xxx.xxx the IP address of the host 193.195.xxx.xxx using HTTPS/SSH/SHELL. To allow network 192.168.16.0/24 access to the router's IP 10.0.0.1, add another entry to the access list 103 as below:
access-list 103 allow ip 192.168.16.0 0.0.0.255 host 10.0.0.1
This should take enable access to this IP address for hosts using ssh and https. Try this out and let me know how it goes.
Thank you and best regards,
Assia
-
"The operating system denied access to the specified file"
I'm playing simcity4 & it keeps saying "operating system denied access to the specified file.
Hello
- Exactly when you receive this error message?
- This occurs during the installation of the game or the game?
SimCity 4 is not compatible with Windows vista. You can check this link:
I suggest you to contact the support of the environmental assessment for better assistance.
-
SSL certificate for access to the administration of a WSA
Can someone point me to a guide on how to install an ssl certificate for access to the administration of a WSA?
Curiously, all the documents that I could find so far talk of SSL certificate for HTTPS decryption...
Page 367 of this doc. http://www.Cisco.com/c/dam/en/us/TD/docs/security/WSA/wsa8-0/wsa8-0-6/WSA_8-0-6_User_Guide.PDF
-
Political dynamic VPN access and access to the administration
Hi all
I'm testing a scenerio with an ASA 5520 so he could authenticate VPN users against and an environment Active Directory more access to management as well. I created a dynamic access on the ASA policy indicating that, if you are a member of the Active Directory 'Managment' group continue. I have chagned the DefaultAccessPolicy to "Finish." With it, users could not connect VPN because they are not a member of this group, but access to manage the ASA is allowed due to this policy.
Is there a way through the use of dynamic access policies I can afford access to the administration (SSH, AMPS, etc.) by matching to membership in a group and will allow normal users to VPN in successfully, but not give them access to the management of the ASA?
I just try this but it seems that I should be able to swing that?
Thaks in advance.
Hello
You can try to apply the DAP and configure the filter ACL network. allowing only the protocols you want to that they can access.
Kind regards
Anisha
P.S.: Please mark this thread as answered if you feel that your query is resolved. Note the useful messages.
-
I am very new to Cisco firewalls (got a little thrown in there) and I had a request to come down the pipe to deny access to the internet for a single internal IP address. My firewall is a PIX 515e. I'm guessing this has to do with the access list, but I don't know if I need to create a group and add only a single IP address to it or how really, even go about it. Any help would be appreciated.
Andrew
What you posted, it is difficult to find how different access lists are applied (how they are used). But it seems that you need another list of access. What you might look like this:
inside_access_out access-list deny ip host everything
inside_access_out ip access list allow a whole
inside_access_out access to the interface inside group
HTH
Rick
-
Need to deny access to the file for the User Manager
Hello
I need be able to deny access to the file manager, as I don't want my client, deleting files. However, for some reason, I have to allow him access to what he should be able to download files via InContext Editor (he needs to link the pages to documents that are not on the server so he needs to download and do it, I have to grant access to the file manager). How can I get around this? I don't want to reupload the site whenever it deletes a file...
Unfortunately we can not do - file manager access to removal as well as download and at this stage that cannot be changed.
-
Administrator to deny access to the file
I am running Windows Vista Home Basic with service pack 2. As an administrator I am frequently refused access to certain folders, e.g., data application. I thought that the administrator has access to all folders on the computer. Is this something common to the basic family version?
No, it is new with Vista. Even administrators do have access to some system, junction points files and folders even in their own profiles to prevent the problems of changes, deletions or additions which might cause problems (and even administrators don't know enough to work safely in these areas). You can use permissions to work around these problems of access; However, I would just leave them alone because most of the time (except if it is advised by Microsoft Support) there is no reason to be in these places. It is a big change in XP where access was essentially unlimited, but just adjust in Vista. It is not only your version but in all versions.
I hope this helps.
Good luck!
Lorien - MCSA/MCSE/network + / has + - if this post solves your problem, please click the 'Mark as answer' or 'Useful' button at the top of this message. Marking a post as answer, or relatively useful, you help others find the answer more quickly.
-
VISA: Is denied access to the resource or to the remote machine.
Hello.
I use a cRIO-9076 to communicate with a Keithley 2400 via port RS-232 on the cRIO. I have a vi test which is built using the Keithley 2400 drivers and it works perfectly fine with the vi is located under 'My Computer' in my project. If I'm moving that vi on the potion of distance OR cRIO9076 of the project and try to run the vi I get a
VISA: (Hex 0xBFFF00A8 to the resource or the remote machine access is denied...
I realized I need to add something to the list of remote access on the cRIO that I find a little confusing. I want to use the serial port on the cRIO by VISA to communicate to the Keithley, so I need to give permission to cRIO on the cRIO? I'm obviously confused.
I tried to add a simple * (wildcard) to the list of access as a temporary solution but I still get the same error.
I would like some advice.
Thank you
Roth
cRIO 9076
Lab View 2013
Keithley 2400
NI-VISA 5.4.0
If you want to move the vi to the CRIO, you can change the name of the resource.
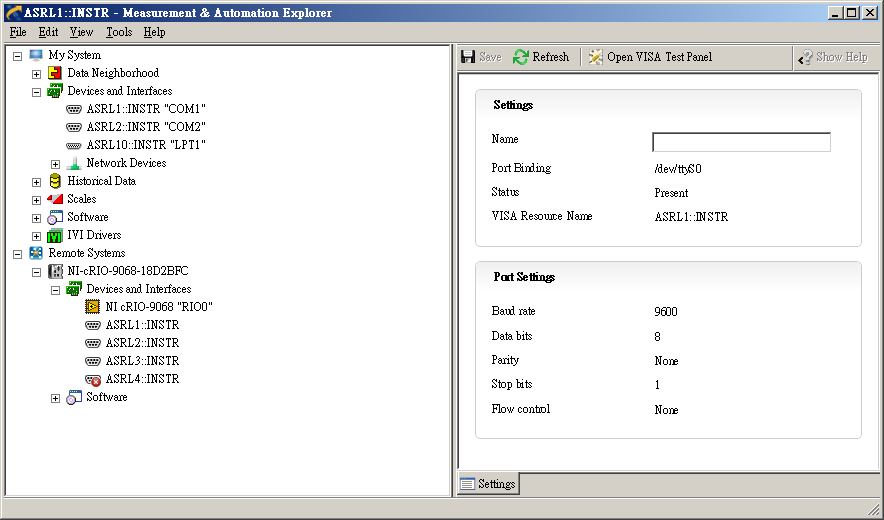
my example is based on the cRIO-9068. When running at MAX on my local host, it can show as below.
The resource for the cRIO-9068 should like 'ASRLx:INSTR '.
Good luck!
-
Why the system operating to deny access to the file specified to run wipe Drive 5
Why deny operating system access to the specified file for execution unit 5 Wipe to wipe my hard drive, I need permission.
Hi JoyceScott,
· What is the operating system installed on the computer?
If you receive no error message indicating that access is denied, take the permissions on the drive and check if it helps.
a. right click on the external hard drive, and then select Properties.
b. click on the Security tab, select the user name and click on modify.
c. now, click Add and type the user name that you want to grant permissions to sub enter the names of the objects to select, and then click on check names. Click OK.
d. now, select the user name you typed in group or user names and check full control under the terms of the authorization for.
e. click on apply and OK. Check whether the problem exists.
For more information, visit: What are the permissions?
-
Access secure site HTTP is preventing access to the administrator and security pages.
I'm trying to access the administrator and security settings, but when I select the option I get a message that I am connected to a secure site, and when I click OK there is a warning that tells me that I can meet with a message indicating that the certificate is not approved to continue anyway; I keep being stopped by the message: error system internal system error accompanied by what seems to be a status bar that does nothing and I can't continue after that screen. Any help would be greatly appreciated. Thank you in advance.
Ben
I was not able to change my URL to get changes to compatibility mode, but I found a free application of IE button on Google Chrome app site that allowed me to make the changes to the printer settings.
Thanks for your suggestion!
Ben
-
Unauthorized access to the administrator account
Original title: my stepson accessed my account
My wife and I are defined as administrators for our computer. We have children accounts set up as limited. Last night, my old stepson of 16 said he knew our password and it did. I don't want him on our behalf! How is this possilble and how can I stop this happenning again?
Hello
You can change the password for the account and ensure that it cannot access the administrator account. Change password for the user account
1. click on Start orb
2. go in Control Panel
3. Select the category of user account and parental control
4. click on user account
5. click on change password
6. follow the on-screen instructions
Hope this information is useful.
Amrita M
Microsoft Answers Support Engineer
Visit our Microsoft answers feedback Forum and let us know what you think. -
Access to the administrative share to XP from Vista
Really Microsoft?
The installer: A machine XP Pro (SP3) and the other Windows Vista Home premium 64-bit (SP1).
Problem: Vista, I can not access the administrative share (C$) located on the Windows XP computer.
Frustrating part: I AM able to access shares administrative, located on the Vista machine, the Windows XP machine
Notes: Has) I turned off all firewalls and antivirus/anti-malware programs on both machines to help determine the root cause of the problems. B) when you try to connect to the administrative share on the XP machine I have do I get prompted for a user name and password. I tried to connect, with the help of two standard (username) and the fully qualified name (machine_name\username AND workgroup_name\username), without success.
Try resetting the share of home networking on the XP machine following its procedures to the letter). It seems that it requires that the machine XP access rights when a properly conifigured hand should access the share without requireing authentication. Something is not set correctly, and again can help solve the problem.
If this isn't the case, after return and we will try something else. Vista and XP often have trouble talking to each other - this isn't the first post I've seen on this issue. The two, they have the same name of working group and they have the same included user names - if not add the correct user name and make the same working group.
I hope this helps.
Good luck!
Lorien - MCSA/MCSE/network + / has + - if this post solves your problem, please click the 'Mark as answer' or 'Useful' button at the top of this message. Marking a post as answer, or relatively useful, you help others find the answer more quickly.
-
Issues of access to the administrator account of
I have a laptop that has 3 users. I'm the administrator of this laptop and I recently tried to log in under my user name, but I am unable to do it because the computer does not recognize my password. I made no change my password. Accordingly, any changes that I want to do, to access my files, etc, are not possible. I can still use my laptop, but only by a guest account. What happened and how do I access my user/account name?
MS Answers does not allow anyone help users to bypass the password protection... Regardless of the reasons.
Here is the link to the policy:
The only suugestion that I am authorized to offer is to reinstall Vista.
-
Remote clients are denied access to the portal...
We're having sporadic problems with remote clients are denied access to our portal, they do not even have a login prompt. We use a SRA 4600 with SonicOS SSL - VPN 8.0.0.3 - 23sv but have see on 8.0.0.1 as well.
Journal entry:
Threat of prevented WAF: Injection SQL 1 attack
More detailsEntry matching: _ga = ga1.2.676072112.1440205737; _dc_gtm_ua-21325736-1 = 1
Threat: SQL Injection attack 1
Threat ID: 9005
Description: SQL Injection is a technique of attack used to exploit websites that construct SQL statements from user-supplied input
URI: remote.ncmic.com:443/
Agent: Mozilla/5.0 (Windows NT 10.0;) WOW64; Trident/7.0; RV:11.0) as the GeckoThe field 'entry matched' is not indicative of the entry that is triggering the signature. There would be something else, we need to study. Can you please make a ticket and we provide access to the portal so we can try to reproduce it?
Maybe you are looking for
-
Safari does not support drive html5 video
I can't play videos over youtube for some reason any. My browser {safari} does not support the reader formats.
-
Reset the printing preferences
Is there a reason to print now remembers the printing preferences (in particular, the number of copies) made during printing? I now fear an increase in my number of printed copies. He ALWAYS remembers it now. If any time I print 20 copies, the nex
-
HP Elitebook 8730w: Eject CD (context menu) doesn't work does not and can not play music CD
Hello After the upgrade to Windows 10 (starting from Windows 7) my CD drive (HL-DT-ST DVDRAM GSA-T50L) does not work properly. I can play the audio files located on the hard disk or over the internet, but I can't play a music CD. Eject the DVD from t
-
iTunes 10.5 download not finish
I can't download itunes 10.5 - system: "the problem with this Windows Installer Package. A program run as part of Setup did not finish as expected". The only thing I can find is maybe I have XP 64-bit edition, which does not support the download.
-
BlackBerry Web Services API 10.1.3 migration
Hi, we have a few developed internal tools that use old BES Web Services (5.0.3 / 6.2) to perform a device admin now measures via custom web pages and we will need to update these to use the new (10.1.3) web services API to perform the management of