Questions of VPN tunnel
People,
You can help me understand how I can fix the following issues I have with a 1721 router (Version 12.3 (8) T5) and client VPN 4.6.01.x please.
BTW, the server at 192.168.3.2 is a file, DNS, WINS server and proxy for the LAN environment. All the staff of the PC is required to use the proxy but visitors on the 192.168.2.0 network can access the internet directly.
Back to my questions. I have the obligation to set up a VPN tunnel to connect to a PC that is running Terminal Server services / remote desktop on a PC to 192.168.1.9. When running the VPN software on the laptop I get a login prompt and everything seems fine. I ping the addresses of router and that works.
But the three things I don't understand:
1. I can't telnet with great success to the loopback address of the router, as well as other addresses 192.168.x.x. very well, but why is it possible that I can telnet to the 192.168.4.1 loopback address?
2. I can't DRC to the server on 192.168.3.2. The server can (and) accepts connections on a subnet, I created the network of 192.168.6.x I put up as VLAN6 on SEA4 (the port of spare on the map of ether 4 ports). The only thing I did not in the configuration of the interface was the nat ip within the statement.
3. I can't do a nslookup through the tunnel VPN (delays all the time) and neither can I http to the IIS server on the same 192.168.3.2 box. What I mean here is that other applications seem to work except telnet!)
Then...:
Why the telnet is so special? I thought that if I could telnet to the router, then I should be able to access the server. And before ask you, there is no firewall or whatever it is executed on the server by stopping this stupid connections. Hey, I'm the guy from router, not the jockey of server!
I've managed to misinterpret the statement "corresponds to the address 105" in the cryptomap? The ACL would reflect the traffic flow both ways?
I should have a statement of hash in the section of "crypto isakmp policy 5. The client indicates that the connection is OK then why should I need it?
I appreciate your time to help. I was scratching my head a lot in the last two days.
Timothy
Your NAT config, it is what kills you here. You can telnet to the router interface, because then the NAT configuration does not take effect (because NAT doesn't happen for passing traffic THROUGH the router, FOR her). You must refuse the IPSec traffic to be NAT would have, otherwise, it does not match the encryption access list and is not encrypted on the way back.
Your 100 access list is incorrect, remove it and add in the following:
access-list 100 deny ip 192.168.0.0 0.0.255.255 192.168.5.0 0.0.0.255
access-list 100 permit ip 192.168.0.0 0.0.255.255 everything
That said NAT VPN traffic does 192.168.5.0, but NAT do it if he goes anywhere else (Internet).
Also, you seem to have defined a map static encryption for your customer traffic, it is not used and may cause you problems with the list of access-105. Follow these steps to get rid of it and just use the dynamic encryption card:
no card crypto clientmap 1
You just need to have dynamic instance map (number 20) crypto left in your config file.
Tags: Cisco Security
Similar Questions
-
Question of access list for Cisco 1710 performing the 3DES VPN tunnel
I have a question about the use of access lists in the configuration of a router Cisco 1710 that uses access lists to control traffic through the VPN tunnel.
For example the following lines in a configuration on the remote router. My question is whether or not the traffic that matches the definition of list access-130 (something other than 192.168.100.0/24), cross the VPN tunnel or go directly to the Ethernet0 interface.
My understanding is that traffic that matches the access list 120 would be encrypted and sent through the IPSec tunnel. If there was "ban" set out in the statements of 120 access-list, the traffic for those would be sent through the IPSec tunnel but not encrypted (if possible). And finally, given that the definition of crypto card reference only "adapt to 120", any traffic that matches 130 access list would be sent Ethernet0 but not associated with the card encryption and thus not sent through the IPSec tunnel. "
Any input or assistance would be greatly appreciated.
Map Test 11 ipsec-isakmp crypto
..
match address 120
Interface Ethernet0
..
card crypto Test
IP nat inside source overload map route sheep interface Ethernet0
access-list 120 allow ip 192.168.100.0 0.0.0.255 10.10.0.0 0.0.255.255
access-list 130 refuse ip 192.168.100.0 0.0.0.255 10.10.0.0 0.0.255.255
access-list 130 allow ip 192.168.100.0 0.0.0.255 any
sheep allowed 10 route map
corresponds to the IP 130
He would go through the interface e0 to the Internet in clear text without going above the tunnel
Jean Marc
-
Allowing ports through a VPN tunnel question
I have a VPN tunnel established and I can ping above but my application fails and I think its because I encouraged not 2 ports (ports TCP 19813 and 19814) through. I'm not clear how should I do for allowing these ports through. I need to add a statement to permit to access my list 'sheep' or what I need to add a statement of license to my list of access interface "external"?
Remote users have an IP address of 172.16.5.x 24 and they're trying to connect to users on the 192.168.200.x 24 192.168.201.x 24. I can't do a ping of the 24 192.168.200.x to the 172.16.5.0/24.
The commands below are what I currently have in my PIX.
My current sheep-access list:
IP 192.168.201.0 allow Access-list sheep 255.255.255.0 172.16.5.0 255.255.255.0
IP 192.168.200.0 allow Access-list sheep 255.255.255.0 172.16.5.0 255.255.255.0
My current outside of the access-list interface:
acl_inbound list access permit tcp any host xx.xx.xx.xx eq smtp
acl_inbound list access permit tcp any host xx.xx.xx.xx eq - ica citrix
acl_inbound list access permit tcp any host xx.xx.xx.xx eq www
acl_inbound list access permit tcp any host xx.xx.xx.xx eq www
acl_inbound list access permit tcp any host xx.xx.xx.xx eq www
acl_inbound list access permit tcp any host xx.xx.xx.xx eq 500
acl_inbound esp allowed access list any host xx.xx.xx.xx
acl_inbound list access permit icmp any any echo response
access-list acl_inbound allow icmp all once exceed
acl_inbound list all permitted access all unreachable icmp
acl_inbound list access permit tcp any host xx.xx.xx.xx eq www
acl_inbound list access permit tcp any host xx.xx.xx.xx eq https
first of all, you disable the commnad "sysopt connection permit-ipsec" on the pix? with this enabled command, which is enabled by default, the pix will ignore any ACLs for encrypted traffic. so if you have Hell no this command, then the acl that you applied on the outside int won't make a difference.
However, if "sysopt connection permit-ipsec" is always on, and then all the port/protocol should be allowed.
you said you could do a ping of 192.168.200.0 to 172.16.5.0. How about you 172.16.5.0 to 192.168.200.0 and 192.168.201.0?
also, just wondering if the vpn lan-to-lan or access remote vpn (i.e. using the cisco vpn client).
-
I was wondering if there is a way to allow only one side of a vpn tunnel to create connections?
Example I have a vpn tunnel going to a site with servers that I manage. I want to be able to get on the servers (via rdp, ssh, etc.) and allow the return of traffic but I don't want the servers to be able to reach me (via rdp, ssh, etc.).
Any ideas?
I use a cisco ASA5540
Hello
You have alteast 2 possibilities
- You can configure a filter ACL on the L2L VPN connection VPN
- Long-term a solution a little messier. Mainly due to the ACL filter of VPN L2L having a slightly different configuration than the usual ACL interface format
- You can turn off (if not already disabled) feature that allows to bypass your 'outer' interface ACL all traffic entering from a VPN connection. In this way, you can control incoming VPN L2L with ACL 'outside' interface traffic.
- connections are allowed as any other Internet connection in the "outside" interface ACL if its fairly simple to manage.
If this is something you are looking for I can tell you how to get to one of them.
-Jouni
- You can configure a filter ACL on the L2L VPN connection VPN
-
Question regarding full mesh with ASA5505 vpn tunnels.
I have 5 remote sites, all of which are connected to the internet through different Internet service providers. My plan was to do a VPN tunnels on each ASA L2L going to other sites (4 tunnels on each SAA). I was wondering if it's the best way to go about this or if I do something else? A full mesh is necessary in this case.
Thank you!
Jason
We don't know enough about your environment to give really good advice on what is best. But according to the description you provided I'd say a VPN L2L of each ASA to all other ASAs would be a very reasonable thing to do.
HTH
Rick
-
SBS 2008 office1 Serv2008 Office 2 need to share assets between them via a site to site VPN tunnel
Hi all.
I really need help on this one.
The office 1 installer running SBS2008 Office 2 running Server 2008.
Each firm has its own FQDN Office 1 CompanyABC 2 A_B_C of the company office.
Each firm has its own internal IP address pool Office 1 192.168.69.xxx and office 192.168.20.xxx 2.
Site to site VPN tunnel between 2 office routers Netgear SRX5308 1 and 2 Netgear FVS318G Office established and working.
Each firm has its own DNS server and acts as a domain controller
How to configure the 2 networks to see each other and be able to use assets on every network (files, printers)?
Is it so simple that the addition of another pool internal IP for each DNS server?
Thanks in advance for your help.
Hello
Your Question is beyond the scope of this community.
I suggest that repost you your question in the Forums of SBS.
https://social.technet.Microsoft.com/forums/en-us/home?Forum=smallbusinessserver
"Windows Small Business Server 2011 Essentials online help"
https://msdn.Microsoft.com/en-us/library/home-client.aspx
TechNet Server forums.
http://social.technet.Microsoft.com/forums/WindowsServer/en-us/home?category=WindowsServer
See you soon.
-
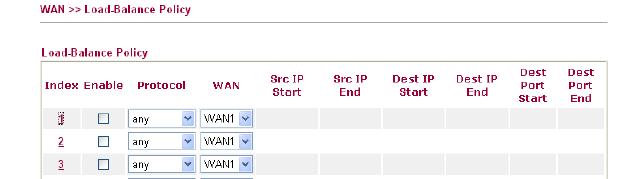
VPN connected, stream out of VPN tunnel
I mean that we have in place of the VPN Sites manage to sites with 2 RV042 router but it seams not as I wanted. Are you sure that each transfer of data through Router 2 will go into the VPN tunnel or it shuts down the VPN tunnel. I checked the routing table and saw that:
Sources mask Gateway Interface
2 1 or wan wan IP 255.255.255.0 ipsec0 private
By default 0.0.0.0 (ip wan 1 or 2) wan1 or wan2
.........
So what you think what sense data will pass through the line, it will go through the ipsec section or through wan1 or wan2. Ofcouse each data will pass through wan1 or wan2, but it can go inside the ipsec tunnel or ipsec outside tunnel. If she goes inside the ipsec tunnel, everything is ok, but if this isn't the case, transfer of unsecured data. I'm trying to access some website is not in private ip and it was outside ipsec tunnel go, I can capture and now that you have access.
Why with linksys have 2 work as draytek product even photos follow:
Can someone help me to answer this question, thank you for your attention
1. it depends on what the tunnels of your business allows. As I've written before, there are other protocols that allows you to route traffic through the VPN tunnel. Only IPSec cannot do this. For example, if your company uses GRE over IPSec then they can route traffic through their tunnels. Your RV does not support this.
2. If it's really plain IPSec then you cannot configure several subnets. You can try to implement the security group remote as a subnet more grand, such as 10.0.0.0/8. Of course the groups must match on both sides.
3. If you want to route all traffic through the tunnel, and then try to set the local/remote security to 0.0.0.0/0.0.0.0 group. Maybe it works.
The configuration of IPSec in the RV042 does not allow extremely complex configurations. It's mainly to connect two subnets between them.
-
VPN tunnel cascade w / SW NSA FWs
Hello
I have questions about VPN cascading between 3 firewall SonicWALL NSA. Let me explain my situation and what I want to achieve.
As shown in the diagram above, I have 3 branches connected to the Internet, which advanced to the LAN is the NSA SW FW. There is a VPN tunnel between each site: Site_A Site_ B, Site_A Site_ C, Site_B Site_ C. The Internet of the Site A traffic is redirected to the Site B. This Site A Cross Site B to access the Internet and LAN B. Site A through C access LAN C Site.
My question is: is it possible to remove the tunnel VPN Site_A-Site_C to and instead, through Site B to C LAN access? If so, how you can achieve this configuration?
What worries me is the VPN tunnel options that allow you to redirect all Internet traffic or a specific destination of LAN through objects (screenshots from Site A) address:
Without the redirection of Internet traffic, I thought about creating a group of addresses, including 2 B LAN and LAN C address objects. But I want to keep the Internet through Site B traffic redirection.
What do you think?
Thanks in advance for your help.
Hello
My comments below:
If you route indeed all traffic from A to B, the following must fill.
1. remove the tunnel A C
Ok.
2. site B will have A subnet that is defined as a local resource for C
Do you mean this by local resource?
3 C is going to have A subnet defined as remote resource
Ok.
If you route any traffic from A to B, the following must fill.
First step would be to remove the tunnel VPN between A and C, but I guess that you have assumed that it was already done.
1. define the C subnet as a remote resource on Site A
Yes, like a remote network for the A - B VPN tunnel.
2. tunnel of site B to A will need to subnet C defined as local resource
Ok.
3. tunnel of site B and C will need subnet defined as local resource
Ok.
4. the site will need to subnet C has defined as remote resource
Yes.
I'll do a test soon with 3 sites and see how it goes.
-
How to change an existing in ASDM VPN tunnel?
I currently have a VPN tunnel together upwards, but to change some of the configurations as making ikev2, replacing the SHA512 hash and change it in the DH group 14. I intend to do this in ASDM. I already created a group of tunnel ikev2 that I put the tunnel and created a Card Crypto that is configured with the right proposal ikev2 IPSec and Diffie-Hellman group. All other configurations such as the IP of Peer address and subnets configured and I'll work with the engineers at the other end of the tunnel to ensure that configurations are, I want to just make sure I'm not missing anything. Someone at - he never comes to change the configuration of an existing ASDM so tunnel, and it worked correctly? Here are the steps that I have will be taken as well as those I've already mentioned:
-Edit the connection profile so that the name of group policy use the correct tunnel that was created for ikev2
-Enter the pre-shared key local and remote pre-shared key ikev2 tab
-Change the IKE Policy so that it uses the ikev2 policy that was created to use SHA512
-Modify the IPSEC proposal so that it uses AES256-SHA512
-THE CRYPTO MAP IS ALREADY CREATED
-Change the secret of transfer perfect in group 14
Hello
Let me go through your questions to clarify this double:
1. If I have a Crypto map applied to my external interface with a proposal of IPSec of ikev1 can I just add a proposal ikev2 in this Crypto map as well?
If you have a card encryption applied to different peers outside and 3 with different order number, you will need to replace the proposal for the peer using IKEv2: IKEv2 IKEv1, the others must continue to use their IKEv1 IPSec proposal.
2. so can I add an ikev2 with AES256 SHA512 hash proposal to my 123.123.123.456 tunnel group and continue to have all three tunnel groups always pass traffic? What happens if I add the proposal ikev2, but REMOVE the ikev1 this group of tunnel proposal because I don't want this group of tunnel use one other than AES256-SHA512 hash?
123.123.123.456 - ikev2 - AES256-SHA512
I would like to expand this a little more, if her counterpart 123.123.123.456, must use IKEv2, you need to declare the IKEv2 in the tunnel group and add the relevant "Local and remote PSK"--> is for phase 1, and this means that it will use the IKEv2 defined policy before, and IPSec IKEv2 proposal is on phase 2, where the encryption card is you will need to replace the IKEv1 and use IPSec IKEv2 proposal. That way it will use for the phase 1 of the policy of IKEv2, that you set and defined transformation IKEv2, by making this change make sure that both sides are mirrored with IKEv2 and IPSec policy projects, as well as the tunnel will remain and will come with the new proposals.
This custom affect no matter what another tunnel, as long as you change the settings to the correct tunnel group and do not delete all the proposals, simply remove the profile connection, those employees.
3. you know what I mean? All groups of three tunnels on that off interface use different cryptographic cards, with only two of the three using ikev1 as a proposal of IPSec. Which will work?
You can only have one card encryption applied by interface, and 3 tunnels using different sequence number with the same crypto map name, you cannot 2 tunnels on the same card encryption using IKEV1, and always in the same encryption card have the third tunnel using IKEv2 (different transformation defined using IKEv2). This custom cause no problem.
4. what Group Policy DfltGrpPolicy? Currently use all my groups of tunnel, but it is configured for ikev1. I'm not really sure what role is in everything it can so I simply add ikev2?
Default group policy is added by default to all your groups of tunnel (connection profile), whenever create you one default group policy is inherited him by default, you can change to group policy that you can create, group policy is a set of attributes that will be used to define something or limit , for example, for a site, you can configure a VPN filter (filters the traffic that goes through the tunnel), now back to your topic, you define the protocols that will be negotiated as for an L2L IKEv1 or IKEv2, Anyconnect SSL or IKEv2, on default group policy, and so on, it is therefore important that you add the IKEv2 , so trading will be permitted, or both to create a new group policy and add the IKEv2 Protocol; and in the tunnel group, add the group policy relevant, that you just created.
I hope that this is precisely, keep me posted!
Please go to the note, and mark it as correct this post and the previous that it helped you!
David Castro,
-
We have VPN tunnel in our firewall with the other partner peer. We use ASA 5520 with IOS "asa825-k8" and ASDM version 6.4.
our partner has several services running in this tunnel VPN, including the SIP.
other services work very well only SIP connections cannot come.
the question is we allowed any IP service on the inside and outside interfaces, but this topic could not come to the top.
is - there any SIP over VPN option must be configured on ASA?
Hello
As you can see in the newspapers, it is denied to the inside interface.
If you just need to allow this by opening an ACL for this traffic on port 5060.
I would like to know if it works.
Kind regards
Aditya
Please evaluate the useful messages and mark the correct answers.
-
NAT, ASA, 2 neworks and a VPN tunnel
Hello. I have a following question. I am trying to establish a VPN tunnel to a remote network used to be connected to our via a VPN tunnel. The problem is that the previous tunnel their share has been created for the x.x.x.x our coast network which will serve no more time a month, but is currently still active and used. As I'm trying to get this VPN tunnel as soon as possible without going through all the paperwork on the other side (political, don't ask) is it possible to make NAT of the new network in the network x.x.x.x for traffic through the VPN tunnel.
Something like this:
new network-> policy NAT in old x.x.x.x fork on ASA-> VPN tunnel to the remote network using x.x.x.x addresses
It is possible to add the new policy, but sometimes it can conflict with the former.
-
HELO all
I'm in this situation:
I have a tunnel VPN setup and running on a router 1800.
Our customer wants a tunnel of intervention similar to this (with other peer IP of course).When the main vpn tunnel has dropped the other will take over.
My question: can I put a second peer who will take over when the first falls:
Nome-240 crypto map ipsec-isakmp crypto
VPN CLIENT description
defined by peer 201.94.151.141
defined by peer 201.94.151.142
86400 seconds, life of security association set
the value of the transform-set 3des-sha
match the address vpn_intlfcstoneor
I have to make another card encryption as follows (using the same access list)?
Nome- 240 crypto map ipsec-isakmp crypto
VPN CLIENT description
defined by peer 201.94.151.141 -(main post)
86400 seconds, life of security association set
the value of the transform-set 3des-sha
address for correspondence vpn_intlfcstoneNome- 250 crypto map ipsec-isakmp crypto
VPN CLIENT description
defined by peer 201.94.151.142 -(second peer)
86400 seconds, life of security association set
the value of the transform-set 3des-sha
address for correspondence vpn_intlfcstoneThe two Tunnel VPN must be on the same router (unfortunately) (1800).
Hello edilson.silva1,
You can configure a second IP for backup VPN peer.
Creating a different sequence in the encryption for the same traffic map will generate a problem that overlap.
-
Transfer between Cisco ASA VPN Tunnels
Hi Experts,
I have a situation where I need to set up the transfer between two VPN Tunnels completed in the same box ASA. A VPN Tunnel will incoming traffic and that traffic should be sent to the bottom of the other VPN Tunnel to the ASA. The two VPN Tunnels are from the Internet and speak with the same IP address of the ASA peers.
Retail
Tunnel A
Source: 192.168.1.0/25
Destination: 10.1.1.0/25
Local counterpart: 170.252.100.20 (ASA in question)
Remote peer: 144.36.255.254
Tunnel B
Source: 192.168.1.0/25
Destination: 10.1.1.0/25
Local peer IP: 170.252.100.20 (box of ASA in question)
Distance from peer IP: 195.75.75.1
Can this be achieved? what configurations are needed in the ASA apart cryptographic ACL entries?
Thanks in advance for your time.
Believed that, in this case your config is good, and you can avoid using routes on your asa since it must route based on its default gateway, make sure you have good sheep in place rules and the inter-to interface same-security-interface allowed return you will need.
-
How to apply internet traffic in VPN tunnel users
Hello
Perhaps it is a simple matter to most of you, but it confuses me right now.
Here's my situation:
home - internet - ASA 5510 users - CORP LAN
We have remote Ipsec VPN and anyconnect VPN, I think that the solution must work on two of them.
My question is: "how to apply internet traffic user home to the VPN tunnel?
We have "split tunnel" to only"'interesting traffic' VPN tunnel access LAN CORP.
but now I need apply all traffic (internet + CORP LAN) user through VPN tunnel passes.
so far, I did what I know:
1. remove the "split tunnle" group policy
2. the address in "remote user VPN address pool" are perhaps NAT/PAT travers ASA5510
but I don't get why it doesn't work.
all suggestions are appreciate!
Thank you!
A few things to configure:
(1) Split tunnel policy to be passed under split in tunnelall tunnel
(2) configure NAT on the external interface to PAT to the same global address.
(3) configure "allowed same-security-traffic intra-interface" so that the tunnel VPN for Internet traffic can make a u-turn.
Please share the current configuration if the foregoing still does not solve the problem. Thank you.
-
Currently, I am trying to decide if what VPN creation filters, if I just create one and apply to multiple VPN tunnels or if each must have their own VPN tunnel filter VPN. Creating a VPN filter for each VPN tunnel seems like extra work but do not know if this is the best choice. I looked through the documentation, but they never mention the VPN application filters to several tunnels.
Hello Jork,
If you add filters for each VPN tunnel group, it will be more work, but at the same, you will have more control over the external users trying to connect to your network.
I would say that you have different groups tunnel (each of them will have their own funcionallity) therefore its depends on what you're trying to implement.
If the people who are going to use X tunnel-group are the same as those who use the tunnel-group is then you can use the same than that.
I hope I understood your question.
Kind regards.
Julio
M Note all the useful po
Maybe you are looking for
-
Problem seeing events & birthdays on icloud calendar
Why can I not see all events & birthdays on my icloud calendar that are on my iphone?
-
Where can I find 64-bit drivers WLAN chip Atheros on Qosmio F50?
So I have a Qosmio F50, and I upgraded to 4 GB of RAM, I decided to format it and install 64-bit of Windows Vista. Everything seems fine, except for the wireless LAN. I was able to find 64-bit drivers for each component with the exception of the wire
-
Problems with a digital slide switch.
Hi all First off thank you in advance for your help. Here's a description of my problem. I try to use a digital slide switch to adjust my z-scale on a graph of intensity. I use several images to create a high dynamic range (HDR) image and having a
-
SRA 4200 for import of 4600 SRA parameters?
Have a HA of SRA4200s set behind a HA of NSA3500s together as a single arm on DMZ mode. Looking to replace the with the new SRA4600s securities regulators. Is the settings of export / import supported 4200 to 4600? Could not find a relevant article o
-
Classic blackBerry alert settings
I recently bought a classic handset to replace my Bold 9780 and get used to it, the only thing that I can not set the text change message alert tone. A single beep is simply not enough, it's inaudible above the background noise in my environment. The
