VPN tunnel via PPPoE connection
The remote site uses a PPPoE DSL connection on a wic etihernet. We have the work of setting up PPPoE, but we are unable to establish the VPN tunnel. When the tunnel is activated, since the PIX debugging logs show the following:
PEER_REAPER_TIMERIPSEC (ipsec_prepare_encap_request): fragmentation, IP packet<>
0 > greater than the effective mtu 1444
IPSec (ipsec_prepare_encap_request): fragmentation, IP <1500>packet greater than e
effective MTU 1444
IPSec (ipsec_prepare_encap_request): fragmentation, IP <1500>packet greater than e
effective MTU 1444
On the router when the encryption card is linked to the Dialer, debug information indicates the following:
Sep 15 12:17:31.111: IPSEC (adjust_mtu): setting ip mtu of 1500 to 1444.
local (identity) = *. *. *. *, distance = *. *. *. *,
local_proxy = 192.168.50.0/255.255.255.0/0/0 (type = 4),
remote_proxy = 0.0.0.0/0.0.0.0/0/0 (type = 4)
Sep 15 12:17:31.115: IPSEC (adjust_mtu): setting mtu of 1500 path to 1444.
local (identity) = *. *. *. *, distance = *. *. *. *,
local_proxy = 192.168.50.0/255.255.255.0/0/0 (type = 4),
remote_proxy = 0.0.0.0/0.0.0.0/0/0 (type = 4)
Sep 15 12:17:31.115: IPSEC (adjust_mtu): setting ip mtu of 1500 to 1444.
local (identity) = *. *. *. *, distance = *. *. *. *,
local_proxy = 192.168.50.0/255.255.255.0/0/0 (type = 4),
remote_proxy = 192.168.0.0/255.255.240.0/0/0 (type = 4)
Sep 15 12:18:16.984: ISAKMP (0:0): no BID in demand
Sep 15 12:18:16.988: ISAKMP (0:0): profile of THE request is (NULL)
Sep 15 12:18:16.988: ISAKMP: 0 local port, remote port 0
Sep 15 12:18:16.988: ISAKMP: set new node 0 to QM_IDLE
If I run the following command on the router, test crypto isakmp. * *. *. * *. *. *. * ESP. I get the following information from the journal of debugging on the router. In the journal of Pix I start reporting the fragmentation, IP <1500>packet greater than the effective mtu 1444.
Sep 15 12:18:16.988: ISAKMP: insert his with his 82121DD4 = success
Sep 15 12:18:16.988: ISAKMP (0:1): cannot start aggressive mode, try main MB
FEL
Sep 15 12:18:16.988: ISAKMP: looking for a key for *. *. *. * in default: success
Sep 15 12:18:16.988: ISAKMP (0:1): found peer pre-shared key matching *. *. *. *
.62
Sep 15 12:18:16.992: ISAKMP (0:1): built the seller-07 ID NAT - t
Sep 15 12:18:16.992: ISAKMP (0:1): built of NAT - T of the seller-03 ID
Sep 15 12:18:16.992: ISAKMP (0:1): built the seller-02 ID NAT - t
Sep 15 12:18:16.992: ISAKMP (0:1): entry = IKE_MESG_FROM_IPSEC, IKE_SA_REQ_MM
Sep 15 12:18:16.992: ISAKMP (0:1): former State = new State IKE_READY = IKE_I_MM1
Sep 15 12:18:16.992: ISAKMP (0:1): early changes of Main Mode
Sep 15 12:18:16.992: ISAKMP (0:1): package is sent to *. *. *. * my_port 0 wee
r_port 0 (I) MM_NO_STATE
Sep 15 12:18:20.440: ISAKMP: ke received message (1/1)
Sep 15 12:18:20.440: ISAKMP: set new node 0 to QM_IDLE
Sep 15 12:18:20.444: ISAKMP (0:1): SA is still budding. Attached is the new ipsec applicant
She St. (local *. *. *. * distance *. *. *. *)
Sep 15 12:18:26.996: ISAKMP (0:1): retransmission phase 1 MM_NO_STATE...
Sep 15 12:18:26.996: ISAKMP (0:1): will increment the error counter on his: broadcast
Phase 1
I tried setting the IP MTU size to 1492 and 1500 on the interface of the router Dialer but I still get the same case. You have any ideas or places to look. We are able to establish a VPN tunnel from this location with a Linksys VPN router or router Drakor. This same router also works when you are using a DSL connection, requiring no PPPoE.
Thank you
JUan
Remove this line on the router:
IP nat inside source list Dialer1 160 interface overload
because this would cause the NAT router all encrypted packets which you don't want. On the PIX, you must change this:
NAT (inside) 0-list of access splittunnel
to reference the ACL sheep or add the 192.168.50.0 subnet in the ACL splittunnel.
On the PIX, enter in the following (I know they are there already):
Outside 1500 MTU
Within 1500 MTU
MTU 1500 dmz
then save the config and rebooting, it must get rid of the MTU messages.
Tags: Cisco Security
Similar Questions
-
VPN tunnel via Cisco to SBS 2008 RRAS router
I need to provide access to remote users outside of ro on the VPN connection. I have a SBS 2008 Server with 1 NIC (10.1.1.1) and active VPN via the option "set up Virtual Private Network" on the SBS console, I enabled the GRE and port 1723 on my Cisco firewall so (10.1.1.254).
I can VPN to SBS internally very well and can telnet to port 1723, but cannot spend outdoors.
I get error 800 how connection on windown 7 PC.I can't telnet to port 1723 on the outside (on the internet), please see my Cisco confug and advice if I missed anythings:
wrsydgw #sh run
Building configuration...Current configuration: 8337 bytes
!
version 12.4
no service button
horodateurs service debug datetime msec
Log service timestamps datetime msec
encryption password service
!
hostname wrsydgw
!
boot-start-marker
start the flash c870-advsecurityk9 - mz.124 - 15.T4.bin system
boot-end-marker
!
forest-meter operation of syslog messages
enable secret 5 $1$ rroD$ / R.6Ce8EdSw7S7B3AJjX81
!
AAA new-model
!
!
!
!
AAA - the id of the joint session
clock timezone 10 30 sydney
!
Crypto pki trustpoint TP-self-signed-432125903
enrollment selfsigned
name of the object cn = IOS - Self - signed - certificate - 432125903
revocation checking no
rsakeypair TP-self-signed-432125903
!
!
TP-self-signed-432125903 crypto pki certificate chain
certificate self-signed 01
30820255 308201BE A0030201 02020101 300 D 0609 2A 864886 F70D0101 04050030
2 060355 04031325 494F532D 53656 C 66 2 AND 536967 6E65642D 43657274 30312E30
69666963 34333231 32353930 33301E17 303230 33303130 30313331 0D 6174652D
315A170D 2E302C06 1325494F 03550403 32303031 30313030 30303030 5A 303031
532D 5365 6C662D53 69676E65 4365 72746966 69636174 652 3433 32313235 642D
06092A 86 4886F70D 01010105 39303330 819F300D 00308189 02818100 0003818D
D54A7EE8 D5B13EED 87D8B177 BC34EDD3 3F2BE37D CEF6E57A 1EDBCF29 344B54C4
EC4DDA6C 8CD07E5C C7E1E6AF 667A5A14 1 HAS 390265 634152D 344D430F 0 ACB0A9F0
A78CA88C C14B4839 6B367DD1 8D8D726A 36624CC2 3CEC616D D72EC30E D27DE845
6F443BE2 51EB9660 981EF07B 097C335D 12D06DD3 2FA8EB3C C20F148B EF367A1F
02030100 01A37F30 7D300F06 03551 D 13 0101FF04 05300301 01FF302A 0603551D
21821F77 11042330 7274732E 726F6265 6D2E696E 63383737 7465726E 6F64652E
6F6E2E6E 6574301F 0603551D 23041830 16801450 41DDCEFD CF041B7B B 48371, 91
5E7EC2D5 D7F6C330 1 D 060355 1D0E0416 DDCEFDCF 04145041 041B7B48 371B915E
7EC2D5D7 F6C3300D 06092 HAS 86 01010405 00038181 004B1DB1 6EA45622 4886F70D
2697E497 BE5D2F71 C15F70B5 9DE07318 A1AD6451 E2502A89 22EC2B7D 26D1C4B7
BC7D09EA F376A2E1 0DF851F2 52C5CFE2 3660BF22 D58E2B15 8A3610BF EDA2FCDC
B5F7429B A89D84D2 EC126229 489CA0D4 E178FC1E E1FBA853 C78AD740 C5A98B4D
4CB58F93 1019D06B 78 C 45799 A5BB1A6F 17FE4C6D 7CE5135B DF
quit smoking
dot11 syslog
no ip source route
!
!
!
!
IP cef
no ip domain search
IP domain name internode.on.net
name of the IP-server 192.231.203.132
name of the IP-server 192.231.203.3
No ipv6 cef
!
Authenticated MultiLink bundle-name Panel
!
!
!
!
No vlan spanning tree 1
No vlan spanning tree 100
username xxxprivilege 15 password 7 xxxxxx
username privilege 15 secret 5 xxxx xxxxxx.
username, password 7 xxxxprivilege 15 xxxxxx!
!
crypto ISAKMP policy 1
BA 3des
md5 hash
preshared authentication
ISAKMP crypto key QnrpzdFI address 139.130.36.42
ISAKMP crypto 5 30 keepalive
!
!
Crypto ipsec transform-set esp-3des esp-md5-hmac vpn - ts
!
RTP 1 ipsec-isakmp crypto map
defined by peer 139.130.36.42
the value of the transform-set vpn - ts
match address Maria
!
Archives
The config log
hidekeys
!
!
property intellectual ssh version 2
!
!
!
ATM0 interface
Description - The internode ADSL-
no ip address
no ip-cache cef route
no ip route cache
no ip mroute-cache
No atm ilmi-keepalive
!
point-to-point interface ATM0.1
no ip route cache
PVC 8/35
PPPoE-client dial-pool-number 1
!
!
interface FastEthernet0
spanning tree portfast
!
interface FastEthernet1
switchport access vlan 100
!
interface FastEthernet2
spanning tree portfast
!
interface FastEthernet3
spanning tree portfast
!
interface Vlan1
10.1.1.254 IP address 255.255.255.0
IP access-group INOUT in
penetration of the IP stream
stream IP output
IP nat inside
IP virtual-reassembly
IP tcp adjust-mss 1450
!
interface Vlan100
IP 10.1.2.254 255.255.255.0
IP nat inside
IP virtual-reassembly
IP tcp adjust-mss 1450
!
interface Dialer0
Description OF the internode
the negotiated IP address
IP access-group DRY in
IP mtu 1452
NAT outside IP
IP virtual-reassembly
encapsulation ppp
Dialer pool 1
Dialer-Group 1
Authentication callin PPP chap Protocol
PPP chap hostname [email protected] / * /PPP chap password 7 xxxxxxx
crypto rtp map
!
IP forward-Protocol ND
IP route 0.0.0.0 0.0.0.0 Dialer0
IP route 10.2.0.0 255.255.0.0 10.1.1.247
no ip address of the http server
no ip http secure server
!
IP high speed-flyers
Top 50
Sorting bytes
cache-timeout 5000
!
IP nat inside source map route VPN-sheep interface Dialer0 overload
IP nat inside source static tcp 10.1.1.1 25 59.167.239.185 25-card route-bypass extensible portfwd
IP nat inside source static tcp 10.1.1.1 443 59.167.239.185 443-route-bypass portfwd expandable card
IP nat inside source static tcp 10.1.1.1 1723 59.167.239.185 1723-route bypass-portfwd expandable map
IP nat inside source static tcp 10.1.1.1 3389 59.167.239.185 route-bypass extensible portfwd 3390-card
IP nat inside source static tcp 10.1.1.7 3389 59.167.239.185 3391-route-bypass portfwd expandable card
IP nat inside source static tcp 10.1.1.125 4333 59.167.239.185 route-bypass extensible portfwd 4333-card
IP nat inside source static tcp 10.1.1.133 4334 59.167.239.185 route-bypass extensible portfwd 4334-card
IP nat inside source static tcp 10.1.1.112 59.167.239.185 4335 4335-route-bypass portfwd expandable card
IP nat inside source static tcp 10.1.2.200 8000 59.167.239.185 8000-route-bypass portfwd expandable card
IP nat inside source static tcp 10.1.2.201 443 59.167.239.185 8001-route-bypass portfwd expandable card
IP nat inside source static tcp 10.1.2.10 80 59.167.239.185 8002-route-bypass portfwd expandable card
IP nat inside source static tcp 10.1.2.11 80 59.167.239.185 8003-route-bypass portfwd expandable card
IP nat inside source static tcp 10.1.1.10 80 59.167.239.185 route-bypass extensible portfwd 8004-card
IP nat inside source static tcp 10.1.1.11 80 59.167.239.185 8005-route-bypass portfwd expandable card
IP nat inside source static tcp 10.1.2.200 80 59.167.239.185 - extensible 8008 portfwd bypass road map
!
DRY extended IP access list
allow tcp any a Workbench
permit tcp any any eq 22
allow any host 59.167.239.185 eq tcp smtp
allow any host 59.167.239.185 eq 443 tcp
allow any host 59.167.239.185 eq 8000 tcp
allow any host 59.167.239.185 eq 8008 tcp
permit tcp any host 59.167.239.185 eq 8001
permit tcp any host 59.167.239.185 eq 8002
permit tcp any host 59.167.239.185 eq 8003
allow any host 59.167.239.185 eq 4333 tcp
allow any host 59.167.239.185 eq 4334 tcp
allow any host 59.167.239.185 eq 4335 tcp
allow any host 59.167.239.185 eq 8004 tcp
allow any host 59.167.239.185 eq 8005 tcp
permit any any icmp echo response
allow an esp
allow a gre
allow a whole ahp
allow icmp all once exceed
ICMP all all ttl-exceeded allow it
allow all all unreachable icmp
permit any any icmp echo
allowed UDP any eq field all
permit udp host 192.231.203.132 eq ntp all
permit any any eq non500-isakmp udp
allow udp any any eq isakmp
deny ip 127.0.0.0 0.255.255.255 everything
refuse the ip 255.255.255.255 host everything
refuse the host ip 0.0.0.0 everything
IP 10.2.0.0 allow 0.0.255.255 everything
allow any host 59.167.239.185 eq 3389 tcp
permit tcp host 67.15.24.9 host 59.167.239.185 eq smtp
permit tcp host 67.15.42.51 host 59.167.239.185 eq smtp
permit tcp host 67.15.52.7 host 59.167.239.185 eq smtp
permit tcp host 69.16.202.203 host 59.167.239.185 eq smtp
permit tcp host 69.16.202.216 host 59.167.239.185 eq smtp
permit tcp host 70.84.109.196 host 59.167.239.185 eq smtp
permit tcp host 207.44.218.60 host 59.167.239.185 eq smtp
permit tcp any host 59.167.239.185 eq 3390
permit tcp any host 59.167.239.185 eq 3391
deny ip any any newspaper
permit tcp any any eq 1723
allow any host 59.167.239.185 eq tcp 1723
INOUT extended IP access list
refuse tcp 10.1.1.3 host no matter what newspaper eq 3389
allow an ip
SHEEP extended IP access list
deny ip 10.0.0.0 0.255.255.255 10.0.0.0 0.255.255.255
ip licensing 10.1.1.0 0.0.0.255 any
IP 10.1.2.0 allow 0.0.0.255 any
NOPFW extended IP access list
deny ip 10.0.0.0 0.255.255.255 10.0.0.0 0.255.255.255
IP enable any 10.1.1.0 0.0.0.255
IP enable any 10.1.2.0 0.0.0.255
Maria extended IP access list
IP 10.1.0.0 allow 0.0.255.255 10.2.0.0 0.0.255.255
!
!
!
!
!
route map VPN-sheep permit 1
corresponds to the IP SHEEP
!
bypass-portfwd allowed 10 route map
corresponds to the IP NOPFW
!
!
control plan
!
!
Line con 0
no activation of the modem
line to 0
line vty 0 4
privilege level 15
Synchronous recording
entry ssh transport
!
max-task-time 5000 Planner
NTP 192.231.203.132 Server prefer
endFor this line of NAT:
IP nat inside source static tcp 10.1.1.1 1723 59.167.239.185 1723-route bypass-portfwd expandable map
Can you please try to remove it and change it to all the following:
IP nat inside source static tcp 10.1.1.1 1723 59.167.239.185 1723 extensible
-
I have read on several posts on the topic and still think I'm missing something, I'm looking for help.
Basically, I'm now implementing multiple VPN tunnels for external connections. We strive to keep the external "private addresses" our basic using NAT network.
I can get the Tunnel to work without problems using the ACL SHEEP; However, this technique requires that our internal network is aware of their external addresses "private." Our goal is to enter an address on the inside that is NAT to the external address 'private' and then shipped via the VPN tunnel. Basically to hide the external address 'private' of our internal systems that they would appear as thought the connection was one of our own networks.
The reverse is true coming from their external 'private' network. Any information of "their" private network external origin would result in our 'private' on arrival address space.
Is this possible? I am attaching a schema, which could help.
Hello
Yes, this should be possible. Lets say you allocate 10.112.2.250 as the address that you use to present the external server 192.168.10.10.
On your ASA device
public static 10.112.2.250 (exterior, Interior) 192.168.10.10 netmask 255.255.255.255
You will need to make sure that when the system tries to connect to 10.112.2.250 it is routed to the device of the SAA.
HTH
Jon
-
I was wondering if there is a way to allow only one side of a vpn tunnel to create connections?
Example I have a vpn tunnel going to a site with servers that I manage. I want to be able to get on the servers (via rdp, ssh, etc.) and allow the return of traffic but I don't want the servers to be able to reach me (via rdp, ssh, etc.).
Any ideas?
I use a cisco ASA5540
Hello
You have alteast 2 possibilities
- You can configure a filter ACL on the L2L VPN connection VPN
- Long-term a solution a little messier. Mainly due to the ACL filter of VPN L2L having a slightly different configuration than the usual ACL interface format
- You can turn off (if not already disabled) feature that allows to bypass your 'outer' interface ACL all traffic entering from a VPN connection. In this way, you can control incoming VPN L2L with ACL 'outside' interface traffic.
- connections are allowed as any other Internet connection in the "outside" interface ACL if its fairly simple to manage.
If this is something you are looking for I can tell you how to get to one of them.
-Jouni
- You can configure a filter ACL on the L2L VPN connection VPN
-
Hi I have a question.
I hope one of you can help me.
My problem is that I want to the internet using VPN tunnenl.
I have a VPN connection with my ASA 5505 at home.
I am able to access the entire inside of the devices. But I'm unable to access the internet.
is it possible the internet using the internet connection I have at home.
i'f played a bit with the following commands:
same-security-traffic permits intera-interface &
same-security-traffic permit intera-interface & split-tunnel-policy tunnelall
ASA version: 9.1 2
ASDM version: 7.1 (3)
Greetings
Palermo
the client that is connected via VPN you are able to ping 4.2.2.2?
If Yes, if you issue a nslookup google.com is the resolved name?
If this isn't the case, then I think that the following command highlighted is the problem:
Group Policy home-attributes VPNSSL
WINS server no
DNS server no
Ikev1 VPN-tunnel-Protocol, l2tp ipsec ikev2 ssl-clientTry setting your DNS here server and test.
--
Please do not forget to select a correct answer and rate useful posts
-
To connect via PPPoE (dialer) Wireless ADSL
Hello
I have a WAG200G Annex-A Wireless G modem router ADSL residential, I used as a wireless router. Now I've changed suppliers (Auntie Indicom - in India), and they have a 'new technology '. Basically, instead of giving me a DSL line in my house, now they directly give me an Ethernet cable in my house (they have a local DSL box somewhere on the roof with various Cisco switches for each household). Then, they want to connect via PPPoE by starting a Dialer on my computer, this particular Ethernet cable is connected.
Now, that works all very well, but we have more than one computer at home, and I would like to use Wifi instead of being connected at all times via the cable on my laptop.
So now my question is:
Can I configure the Linksys router so that IT don't the PPPoE dial for me? Basically this means plug the Ethernet cable provided by my ISP in one of the ETHERNET Ports and set up allowing to switch on (since there is no cable "line" adsl connected more) with my user name and password.
Anyone know how to do this, or if this is possible?
Thank you!
P.s.: I've set up the Internet connection sharing via ad-hoc wireless, which works very well, but is only a temporary solution because I don't want to use my laptop as a router...
It is not possible to configure WAG200G without ADSL line.
-
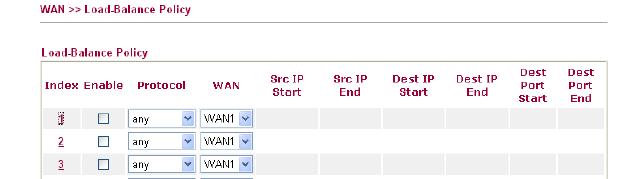
VPN connected, stream out of VPN tunnel
I mean that we have in place of the VPN Sites manage to sites with 2 RV042 router but it seams not as I wanted. Are you sure that each transfer of data through Router 2 will go into the VPN tunnel or it shuts down the VPN tunnel. I checked the routing table and saw that:
Sources mask Gateway Interface
2 1 or wan wan IP 255.255.255.0 ipsec0 private
By default 0.0.0.0 (ip wan 1 or 2) wan1 or wan2
.........
So what you think what sense data will pass through the line, it will go through the ipsec section or through wan1 or wan2. Ofcouse each data will pass through wan1 or wan2, but it can go inside the ipsec tunnel or ipsec outside tunnel. If she goes inside the ipsec tunnel, everything is ok, but if this isn't the case, transfer of unsecured data. I'm trying to access some website is not in private ip and it was outside ipsec tunnel go, I can capture and now that you have access.
Why with linksys have 2 work as draytek product even photos follow:
Can someone help me to answer this question, thank you for your attention
1. it depends on what the tunnels of your business allows. As I've written before, there are other protocols that allows you to route traffic through the VPN tunnel. Only IPSec cannot do this. For example, if your company uses GRE over IPSec then they can route traffic through their tunnels. Your RV does not support this.
2. If it's really plain IPSec then you cannot configure several subnets. You can try to implement the security group remote as a subnet more grand, such as 10.0.0.0/8. Of course the groups must match on both sides.
3. If you want to route all traffic through the tunnel, and then try to set the local/remote security to 0.0.0.0/0.0.0.0 group. Maybe it works.
The configuration of IPSec in the RV042 does not allow extremely complex configurations. It's mainly to connect two subnets between them.
-
Hi all
I have a little problem concerning ASA and syslogs. I have a tunnel from site to site between a local ASA and ASA distance. Behind the ASA local, I have a central syslog server (which has no ASA as default gateway) which collects messages from all network devices and I want to get messages from the ASA remote as well.
The tunnel protects traffic between local networks behind each ASA, which includes ASA inside remote interface as well. The problem is that if I specify on the SAA distance my syslog server it does not pass through the VPN tunnel. The ASA remote sees my server syslog as being 'outside' so he's using the external IP address as the source-interface for the syslog message. Which of course does not pass through the tunnel. As much as I know there is no way to configure the interface source for logging under the SAA, that you can do on a normal IOS router.
I've found a few documents explaining this Setup on CCO, but they all imply I have extend the list for interesting traffic to access allow remote UDP/514 of the PIX traffic outside my local syslog server interface. This isn't something I want to do what I would get in routing complication in my LAN with a public IP address of the ASA remote.
Any suggestions? I thought I could use some sort of NAT on the ASA remote so that all traffic for my local network a source the remote PIX is translated on the inside interface, which in theory should pass the package via the tunnel. I did not go so far.
Any help is appreciated.
Best regards
Stefan
You can define the interface that the ASA will use to send the newspapers "syslog_ip host record.
Make sure you also do "access management".
Then the SAA should source the syslogs from inside the interface, which is probably encrypted with the crypto ACL.
I hope it helps.
PK
-
Client VPN will travel not connected via 877w
Hello
I've implemented a Cisco 877w and it works very well for web access
Client VPN on my laptop connects via the 877w and authenticates on my remote work ASA5510 firewall.
Problem is after you connect to the ASA, I can not connect anything internally work network (10.0.0.0/24), ping, etc. RDP is back with no answer.
I've attached the config, can someone tell me what I am missing, might access a list?
Thanks for your help
Chris
This router is made PAT/NAT, Ipsec blocking.
Activate Nat on the ASA course remote.
ISAKMP nat - t or crypto isakmp nat - t
HTH
Sangaré
Pls rate helpful messages
-
Connectivity on the VPN tunnel problem.
Hello
I have a site to tunnel between the PIX506 and Cisco VPN 3000 Concentrator. I'll be spending it again ASA5510, so the tunnel will be established between the ASA and PIX. After inistial tests, I found only one box of remote network (time clock lol) is down by connectivity while tunnel between Pix and ASA (works fine with the hub). All traffic is allowed through the VPN tunnel built on SAA is? I understand it should be as long as the tunnel is running, correct? (Note: the remote clock uses ports TCP 8888 and 8889 to communicate with the server)
Thank you
If there is no filter, again all traffic should be allowed.
You need not choose L2TP connection is pure IPsec.
If you wish, you can post your configurations to check them out (you can remove sensitive information)
Federico.
-
SBS 2008 office1 Serv2008 Office 2 need to share assets between them via a site to site VPN tunnel
Hi all.
I really need help on this one.
The office 1 installer running SBS2008 Office 2 running Server 2008.
Each firm has its own FQDN Office 1 CompanyABC 2 A_B_C of the company office.
Each firm has its own internal IP address pool Office 1 192.168.69.xxx and office 192.168.20.xxx 2.
Site to site VPN tunnel between 2 office routers Netgear SRX5308 1 and 2 Netgear FVS318G Office established and working.
Each firm has its own DNS server and acts as a domain controller
How to configure the 2 networks to see each other and be able to use assets on every network (files, printers)?
Is it so simple that the addition of another pool internal IP for each DNS server?
Thanks in advance for your help.
Hello
Your Question is beyond the scope of this community.
I suggest that repost you your question in the Forums of SBS.
https://social.technet.Microsoft.com/forums/en-us/home?Forum=smallbusinessserver
"Windows Small Business Server 2011 Essentials online help"
https://msdn.Microsoft.com/en-us/library/home-client.aspx
TechNet Server forums.
http://social.technet.Microsoft.com/forums/WindowsServer/en-us/home?category=WindowsServer
See you soon.
-
Routing access to Internet through an IPSec VPN Tunnel
Hello
I installed a VPN IPSec tunnel for a friend's business. At his desk at home, I installed a Cisco SA520 and at it is remote from the site I have a Cisco RVS4000. The IPSec VPN tunnel works very well. The remote site, it can hit all of its workstations and peripheral. I configured the RVS4000 working in router mode as opposed to the bridge. In the Home Office subnet is 192.168.1.0/24 while the subnet to the remote site is 192.168.2.0/24. The SA520 is configured as Internet gateway for the headquarters to 192.168.1.1. The remote desktop has a gateway 192.168.2.1.
I need to configure the remote site so that all Internet traffic will be routed via the Home Office. I have to make sure that whatever it is plugged into the Ethernet on the RVS4000 port will have its Internet traffic routed through the Internet connection on the SA520. Currently I can ping any device on the headquarters of the remote desktop, but I can't ping anything beyond the gateway (192.168.1.1) in the Home Office.
Any help would be greatly appreciated.
Thank you.
Hi William, the rvs4000 does not support the tunnel or esp transfer wild-card.
-
SA520w routing through site-to-site VPN tunnels
I have several offices that are connected using site-to-site VPN tunnels and all will use the SA520W (firmware 2.1.18). I currently have 3 routers in place, router tunnels created for the router B and c of router. I need assistance with the configuration to allow the guests to router site B get to the router site C. I have attempted to add a static route, but get a destination unreachable host trying to ping. Also, if I connect to the router site has via the Cisco VPN client, I'm not able to get resources on each site, B, or C.
A - the site 10.10.0.0/24
Site B - 10.0.0.0/24
Site of the C - 10.25.0.0/24
Any help is greatly appreciated.
So, that's what you have configured correctly?
RTR_A
||
_____________ || ___________
|| ||
RTR_B RTR_C
Since there is no tunnel between B and C there is no way for us past that traffic through RTR_A for two reasons. The most important reason is that subnet 10.25.0.0/24 (rtr_c) is not allowed to pass through the IPSec tunnel (it's okay to IPSec?) of rtr_a ==> rtr_b. You can't just add a statement of road because your addresses are not routable which is the reason why it fails.
Your only option is to create another tunnel between rtr_b and rtr_c. This may not be the ONLY option, but you should get what you need.
I hope this helps.
-
NAT, ASA, 2 neworks and a VPN tunnel
Hello. I have a following question. I am trying to establish a VPN tunnel to a remote network used to be connected to our via a VPN tunnel. The problem is that the previous tunnel their share has been created for the x.x.x.x our coast network which will serve no more time a month, but is currently still active and used. As I'm trying to get this VPN tunnel as soon as possible without going through all the paperwork on the other side (political, don't ask) is it possible to make NAT of the new network in the network x.x.x.x for traffic through the VPN tunnel.
Something like this:
new network-> policy NAT in old x.x.x.x fork on ASA-> VPN tunnel to the remote network using x.x.x.x addresses
It is possible to add the new policy, but sometimes it can conflict with the former.
-
VPN Tunnel access to several subnets ASA 5505
Greetings,
We spent a little time trying to configure our ASA 5505 in order to TUNNEL into several different subnets. Subnets include 192.168.1.0 / 192.168.2.0 / 192.168.10.0
Someone is about to review this setup running and indicate where we have gone wrong. When I connect via the VPN Client, I can access the 192.168.1.0 network, no problem. But fail to reach the other two. Thank you very much.
Output from the command: 'show running-config '.
: Saved
:
ASA Version 8.2 (5)
!
hostname BakerLofts
activate kn7RHw13Elw2W2eU encrypted password
2KFQnbNIdI.2KYOU encrypted passwd
names of
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
switchport access vlan 12
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
IP 192.168.1.254 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
IP 74.204.54.4 255.255.255.248
!
interface Vlan12
nameif Inside2
security-level 100
IP address 192.168.10.254 255.255.255.0
!
passive FTP mode
permit same-security-traffic inter-interface
permit same-security-traffic intra-interface
vpn_splitTunnelAcl list standard access allowed 192.168.1.0 255.255.255.0
outside_access_in of access allowed any ip an extended list
inside_nat0_outbound to access ip 192.168.1.0 scope list allow 255.255.255.0 192.168.3.0 255.255.255.0
Inside2_access_in of access allowed any ip an extended list
permit Inside2_nat0_outbound to access extended list ip 192.168.10.0 255.255.255.0 192.168.3.0 255.255.255.0
pager lines 24
Enable logging
asdm of logging of information
Within 1500 MTU
Outside 1500 MTU
MTU 1500 Inside2
IP local pool vpn 192.168.3.1 - 192.168.3.254 mask 255.255.255.0
no failover
ICMP unreachable rate-limit 1 burst-size 1
don't allow no asdm history
ARP timeout 14400
Global 1 interface (outside)
NAT (inside) 0-list of access inside_nat0_outbound
NAT (inside) 1 0.0.0.0 0.0.0.0
NAT (outside) 0 192.168.3.0 255.255.255.0 outside
NAT (Inside2) 0-list of access Inside2_nat0_outbound
NAT (Inside2) 1 0.0.0.0 0.0.0.0
Access-group outside_access_in in interface outside
Access-group Inside2_access_in in the interface Inside2
Route outside 0.0.0.0 0.0.0.0 74.204.54.1 1
Timeout xlate 03:00
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
AAA authentication enable LOCAL console
AAA authentication LOCAL telnet console
Enable http server
http 192.168.1.0 255.255.255.0 inside
No snmp server location
No snmp Server contact
Server enable SNMP traps snmp authentication linkup, linkdown cold start
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
Crypto ipsec transform-set ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ESP-DES-MD5 esp - esp-md5-hmac
Crypto ipsec transform-set ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ESP-AES-256-SHA 256 - aes - esp esp-sha-hmac
Crypto ipsec transform-set ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ESP-AES-128-MD5-esp - aes esp-md5-hmac
life crypto ipsec security association seconds 28800
Crypto ipsec kilobytes of life - safety 4608000 association
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 pfs Group1 set
Crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 value transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
outside_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
outside_map interface card crypto outside
Crypto ca trustpoint _SmartCallHome_ServerCA
Configure CRL
Crypto ca certificate chain _SmartCallHome_ServerCA
certificate ca 6ecc7aa5a7032009b8cebcf4e952d491
308204 4 a0030201 d 308205ec 0202106e cc7aa5a7 032009b 8 cebcf4e9 52d 49130
010105 05003081 09060355 04061302 55533117 ca310b30 0d 864886f7 0d06092a
30150603 55040 has 13 0e566572 69536967 6e2c2049 6e632e31 1f301d06 0355040b
13165665 72695369 676e2054 72757374 204e6574 776f726b 313 has 3038 06035504
0b 133128 63292032 30303620 56657269 5369676e 2c20496e 632e202d 20466f72
20617574 7a 656420 75736520 6f6e6c79 31453043 06035504 03133c 56 686f7269
65726953 69676e20 436c 6173 73203320 5075626c 69632050 72696 72792043 61 d
65727469 66696361 74696f6e 20417574 686f7269 7479202d 20473530 1e170d31
30303230 38303030 3030305a 170d 3230 30323037 32333539 35395a 30 81b5310b
30090603 55040613 02555331 17301506 0355040a 130e5665 72695369 676e2c20
496e632e 311f301d 06035504 0b 131656 65726953 69676e20 54727573 74204e65
74776f72 6b313b30 5465726d 20757365 20617420 73206f66 39060355 040b 1332
68747470 7777772e 733a2f2f 76657269 7369676e 2e636f6d 2f727061 20286329
302d 0603 55040313 26566572 69536967 61737320 33205365 6e20436c 3130312f
63757265 20536572 76657220 20473330 82012230 0d06092a 864886f7 4341202d
010101 05000382 010f0030 82010 0d has 02 b187841f 82010100 c20c45f5 bcab2597
a7ada23e 9cbaf6c1 39b88bca c2ac56c6 e5bb658e 444f4dce 6fed094a d4af4e10
9c688b2e 957b899b 13cae234 34c1f35b f3497b62 d188786c 83488174 0253f9bc
7f432657 5833833b 330a17b0 d04e9124 ad867d64 12dc744a 34a11d0a ea961d0b
15fca34b 3bce6388 d0f82d0c 948610ca b69a3dca eb379c00 48358629 5078e845
1941 4ff595ec 7b98d4c4 71b350be 28b38fa0 b9539cf5 ca2c23a9 fd1406e8 63cd
18b49ae8 3c6e81fd e4cd3536 b351d369 ec12ba56 6e6f9b57 c58b14e7 0ec79ced
4a546ac9 4dc5bf11 b1ae1c67 81cb4455 33997f24 9b3f5345 7f861af3 3cfa6d7f
81f5b84a d3f58537 1cb5a6d0 09e4187b 384efa0f 01 has 38201 02030100 df308201
082b 0601 05050701 01042830 26302406 082 b 0601 db303406 05050730 01861868
7474703a 2f2f6f63 73702e76 65726973 69676e2e 636f6d30 12060355 1 d 130101
ff040830 02010030 70060355 b 200469 30673065 060, 6086 480186f8 1 d 060101ff
45010717 03305630 2806082b 06010505 07020116 1 c 687474 70733a2f 2f777777
2e766572 69736967 6e2e636f 6d2f6370 73302 has 06 082 b 0601 05050702 02301e1a
1 c 687474 70733a2f 2f777777 2e766572 69736967 6e2e636f 6d2f7270 61303406
03551d1f 042d302b 3029 has 027 a0258623 68747470 3a2f2f63 726c2e76 65726973
69676e2e 636f6d2f 2d67352e 70636133 63726c 30 0e060355 1d0f0101 ff040403
02010630 6d06082b 06010505 07010c 59305730 55160969 5da05b30 04 61305fa1
6 d 616765 2f676966 3021301f 2b0e0302 30070605 1a04148f e5d31a86 ac8d8e6b
c3cf806a d448182c 7b192e30 25162368 7474703a 2f2f6c6f 676f2e76 65726973
69676e2e 636f6d2f 76736c6f 676f2e67 69663028 0603551d 11042130 1fa41d30
1 b 311930 17060355 04031310 56657269 5369676e 4d504b49 2d322d36 301D 0603
445 1653 44c1827e 1d20ab25 f40163d8 be79a530 1f060355 c 1604140d 551d0e04
1 230418 30168014 7fd365a7 c2ddecbb f03009f3 4339fa02 af333133 300 d 0609 d
2a 864886 05050003 82010100 0c8324ef ddc30cd9 589cfe36 b6eb8a80 f70d0101
4bd1a3f7 9df3cc53 ef829ea3 a1e697c1 589d756c e01d1b4c fad1c12d 05c0ea6e
b2227055 d9203340 3307c 265 83fa8f43 379bea0e 9a6c70ee f69c803b d937f47a
99 c 71928 8705 404167d 1 273aeddc 866d 24f78526 a2bed877 7d494aca 6decd018
481d22cd 0b0b8bbc f4b17bfd b499a8e9 762ae11a 2d876e74 d388dd1e 22c6df16
b62b8214 0a945cf2 50ecafce ff62370d ad65d306 4153ed02 14c8b558 28a1ace0
5becb37f 954afb03 c8ad26db e6667812 4ad99f42 fbe198e6 42839b8f 8f6724e8
6119b5dd cdb50b26 058ec36e c4c875b8 46cfe218 065ea9ae a8819a47 16de0c28
6c2527b9 deb78458 c61f381e a4c4cb66
quit smoking
crypto ISAKMP allow outside
crypto ISAKMP policy 10
preshared authentication
3des encryption
sha hash
Group 2
life 86400
Telnet 192.168.1.0 255.255.255.0 inside
Telnet timeout 5
SSH timeout 5
Console timeout 0
dhcpd outside auto_config
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
WebVPN
internal vpn group policy
attributes of vpn group policy
value of server DNS 8.8.8.8
Protocol-tunnel-VPN IPSec
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list vpn_splitTunnelAcl
username, password samn aXJbUl92B77AGcc. encrypted privilege 0
samn attributes username
Strategy-Group-VPN vpn
username password encrypted QUe2MihLFbj2.Iw0 privilege 0 jmulwa
username jmulwa attributes
Strategy-Group-VPN vpn
jangus Uixpk4uuyEDOu9eu username encrypted password
username jangus attributes
Strategy-Group-VPN vpn
vpn tunnel-group type remote access
VPN tunnel-group general attributes
vpn address pool
Group Policy - by default-vpn
Tunnel vpn ipsec-attributes group
pre-shared key *.
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
anonymous reporting remote call
Cryptochecksum:d41d8cd98f00b204e9800998ecf8427e
: end
I see two problems:
1. your ASA has not an interior road to the Incas inside networks. You must add:
Route inside 192.168.2.0 255.255.255.0
Route inside 192.168.10.0 255.255.255.0
.. .specifying your gateway address of these networks.
2. the statement "access-list standard vpn_splitTunnelAcl permit 192.168.1.0 255.255.255.0" sends only a route for 192.168.1.0/24 to your customer. You need to add entries for the other two networks.
Maybe you are looking for
-
IPhone SE a1723 unlocked phone can be used in India?
2 days back I went a nearby naperville apple store and asked a gsm unlocked iphone is. I was about to return to the India and I wanted to use it there. Through this (www.apple.com/iphone/LTE/#iphone-se), I came to know that the India is listed under
-
Error Code 10 Intel 82579LM LAN connection on Portege R830 - 13 c
After the recent update 32-bit Windows 7, the connection to the local network cannot start (Code 10) in Device Manager "This device cannot start. (Code 10) » I tried to uninstall drivers / back / and install which follows Toshiba support page files,
-
Satellite Pro U400-247 - noise static when the AC adapter is plugged
Hello I got by Satellite Pro U400-247 and you have a problem with the sound. Everytime I plugg in adapter (external power supply) there is a kind of droning noise static noise when I use the audio out (headphones). Does anyone have a solution for thi
-
How to temporarily disable third-party firewalls
-
80070490 error code please help me. not getting not updates
My Windows updates have stopped working. I had an accident and has made a recovery system just before it happened. How can I fix this. I paid on-site Computer Solutions LLC $150.00 to help him find my computer, but it has not been repaired. It is