Web VPN/SSL - general Split Tunnel capable?
When I look through some examples of configuration for IOS Web VPN - it seems you attract to the filling of a web page of web sites that users can go to. I would be rather thin client act as client light 4.x CVPN - divided for example tunnel with access to a resource internal resource. Is this possible with Cisco VPN Web? Also - with is WebVPN any ability of the NAC?
I'm not sure IOS SSL vpn, but on the asa webvpn, there is a complete client ssl option. With this, you can either create a tunnel, or all split tunnel and the only defined networks. I hope that answers your question.
Tags: Cisco Security
Similar Questions
-
Impossible to access them Internert through the split tunneling VPN client.
I divided tunnel configured on a PIX 515. The remote VPN client connects to the PIX very well and can ping hosts on the internal network, but cannot access the Internet. Am I missing something? My config as shown below.
In addition, I don't see the routes on the VPN client via statistics (screenshot below)
All opinions are appreciated.
Rob
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------
8.0 (3) version PIX
!
hostname PIX-to-250
enable the encrypted password xxxxx
names of
!
interface Ethernet0
nameif outside
security-level 0
IP address x.x.x.250 255.255.255.240
!
interface Ethernet1
nameif inside
security-level 100
IP 192.168.9.1 255.255.255.0
!
XXXXX encrypted passwd
passive FTP mode
DNS domain-lookup outside
DNS server-group Ext_DNS
Server name 194.72.6.57
Server name 194.73.82.242
the LOCAL_LAN object-group network
object-network 192.168.9.0 255.255.255.0
object-network 192.168.88.0 255.255.255.0
Internet_Services tcp service object-group
port-object eq www
area of port-object eq
EQ object of the https port
port-object eq ftp
EQ object of port 8080
port-object eq telnet
the WAN_Network object-group network
object-network 192.168.200.0 255.255.255.0
ACLOUT list extended access allowed object-group LOCAL_LAN udp any eq log field
ACLOUT list extended access allow icmp object-group LOCAL_LAN no matter what paper
ACLOUT list extended access permitted tcp object-group LOCAL_LAN connect to any object-group Internet_Services
access-list extended ACLIN all permit icmp any what newspaper echo-reply
access-list extended ACLIN all permit icmp any how inaccessible journal
access-list extended ACLIN allowed icmp no matter what newspaper has exceeded the time
Comment by split_tunnel_list-LAN Local access list
split_tunnel_list list standard access allowed 192.168.9.0 255.255.255.0
access-list extended SHEEP allowed object-group ip LOCAL_LAN 192.168.100.0 255.255.255.0
pager lines 24
Enable logging
Outside 1500 MTU
Within 1500 MTU
IP local pool testvpn 192.168.100.1 - 192.168.100.99
no failover
ICMP unreachable rate-limit 1 burst-size 1
don't allow no asdm history
ARP timeout 14400
Global 1 interface (outside)
NAT (inside) 0 access-list SHEEP
NAT (inside) 1 0.0.0.0 0.0.0.0
Access-group ACLIN in interface outside
ACLOUT access to the interface inside group
Route outside 0.0.0.0 0.0.0.0 195.171.252.45 1
Route inside 192.168.88.0 255.255.255.0 192.168.88.254 1
Route inside 192.168.199.0 255.255.255.0 192.168.199.254 1
Timeout xlate 03:00
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout, uauth 0:05:00 absolute
dynamic-access-policy-registration DfltAccessPolicy
Enable http server
No snmp server location
No snmp Server contact
Server enable SNMP traps snmp authentication linkup, linkdown cold start
Crypto ipsec transform-set esp-3des esp-sha-hmac Set_1
Crypto-map dynamic outside_dyn_map 10 game of transformation-Set_1
life together - the association of security crypto dynamic-map outside_dyn_map 10 seconds 280000
Crypto-map dynamic outside_dyn_map 10 the value reverse-road
outside_map 10 card crypto ipsec-isakmp dynamic outside_dyn_map
outside_map interface card crypto outside
crypto ISAKMP allow outside
crypto ISAKMP policy 1
preshared authentication
3des encryption
sha hash
Group 2
life 43200
crypto ISAKMP policy 65535
preshared authentication
3des encryption
sha hash
Group 2
life 86400
Telnet timeout 5
SSH timeout 5
Console timeout 0
a basic threat threat detection
Statistics-list of access threat detection
internal testvpn group policy
attributes of the strategy of group testvpn
Protocol-tunnel-VPN IPSec
Split-tunnel-policy tunnelspecified
name of user testuser encrypted password xxxxxx
type tunnel-group testvpn remote access
tunnel-group testvpn General-attributes
address testvpn pool
Group Policy - by default-testvpn
testvpn group of tunnel ipsec-attributes
pre-shared-key *.
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the netbios
inspect the rsh
inspect the rtsp
inspect the skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect the tftp
inspect the sip
inspect xdmcp
inspect the icmp
!
global service-policy global_policy
context of prompt hostname
Cryptochecksum:5dcb5dcdff277e1765a9a0c366b88b9e
: end
# 250 A - PIX
You have not assigned the ACL split tunnel to your strategy.
PLS, configure the following:
attributes of the strategy of group testvpn
value of Split-tunnel-network-list split_tunnel_list
-
Windows - Internet access, no split Tunnel L2TP VPN Clients does not
Greetings!
I have four ASA 5505 that I configured with 4 site to site VPN tunnels (works perfectly) to connect to our company facilities 4. The ASA is also configured with remote access L2TP/IPsec so that a specific group of users of portable computers can connect to and access to all facilities. It also works very well except for one important exception - my split tunnel setting doesn't seem to work, because I can't connect to the Internet outside the VPN resources.
I accept the inherent risk of allowing tunnels to split from a security point of view since I take the necessary steps to secure the systems used for remote access. I would appreciate any feedback on how to get the job of split tunnel.
Here is the configuration:
: Saved
:
ASA Version 1.0000 11
!
SGC hostname
domain somewhere.com
names of
COMMENTS COMMENTS LAN 192.168.2.0 name description
name 75.185.129.13 description of SGC - external INTERNAL ASA
name 172.22.0.0 description of SITE1-LAN Ohio management network
description of SITE2-LAN name 172.23.0.0 Lake Club Network
name 172.24.0.0 description of training3-LAN network Southwood
description of training3 - ASA 123.234.8.124 ASA Southwoods name
INTERNAL name 192.168.10.0 network Local INTERNAL description
description of name 192.168.11.0 INTERNAL - VPN VPN INTERNAL Clients
description of Apollo name 192.168.10.4 INTERNAL domain controller
description of DHD name 192.168.10.2 Access Point #1
description of GDO name 192.168.10.3 Access Point #2
description of Odyssey name 192.168.10.5 INTERNAL Test Server
CMS internal description INTERNAL ASA name 192.168.10.1
name 123.234.8.60 description of SITE1 - ASA ASA management Ohio
description of SITE2 - ASA 123.234.8.189 Lake Club ASA name
description of training3-VOICE name Southwood Voice Network 10.1.0.0
name 172.25.0.0 description of training3-WIFI wireless Southwood
!
interface Vlan1
nameif outside
security-level 0
IP address dhcp setroute
!
interface Vlan2
nameif INSIDE
security-level 100
255.255.255.0 SGC-internal IP address
!
interface Vlan3
nameif COMMENTS
security-level 50
IP 192.168.2.1 255.255.255.0
!
interface Ethernet0/0
Time Warner Cable description
!
interface Ethernet0/1
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/2
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/3
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/4
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/5
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/6
Description for Wireless AP Trunk Port
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/7
Description for Wireless AP Trunk Port
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
boot system Disk0: / asa821-11 - k8.bin
Disk0: / config.txt boot configuration
passive FTP mode
clock timezone IS - 5
clock to summer time EDT recurring
DNS domain-lookup outside
INTERNAL DNS domain-lookup
DNS domain-lookup GUEST
DNS server-group DefaultDNS
Name-Server 4.2.2.2
domain somewhere.com
permit same-security-traffic inter-interface
permit same-security-traffic intra-interface
DM_INLINE_TCP_1 tcp service object-group
EQ port 3389 object
port-object eq www
EQ object of the https port
EQ smtp port object
the DM_INLINE_NETWORK_1 object-group network
network-object SITE1-LAN 255.255.0.0
network-object SITE2-LAN 255.255.0.0
network-object training3-LAN 255.255.0.0
object-group training3-GLOBAL network
Southwood description Global Network
network-object training3-LAN 255.255.0.0
network-object training3-VOICE 255.255.0.0
network-object training3-WIFI 255.255.0.0
DM_INLINE_TCP_2 tcp service object-group
EQ port 5900 object
EQ object Port 5901
object-group network INTERNAL GLOBAL
Description Global INTERNAL Network
network-object INTERNAL 255.255.255.0
network-object INTERNALLY-VPN 255.255.255.0
access-list outside_access note Pings allow
outside_access list extended access permit icmp any CMS-external host
access-list outside_access note that VNC for Camille
outside_access list extended access permit tcp any host CMS-external object-group DM_INLINE_TCP_2
access-list outside_access note INTERNAL Services
outside_access list extended access permit tcp any host CMS-external object-group DM_INLINE_TCP_1
DefaultRAGroup_splitTunnelAcl list standard access allowed INTERNAL 255.255.255.0
access-list sheep extended ip INTERNAL 255.255.255.0 allow INTERNAL VPN 255.255.255.0
access-list extended sheep allowed ip IN-HOUSE-GLOBAL SITE1-LAN 255.255.0.0 object-group
access-list extended sheep allowed ip IN-HOUSE-GLOBAL SITE2-LAN 255.255.0.0 object-group
access-list extended sheep allowed ip object-IN-HOUSE-GLOBAL object group training3-GLOBAL
access-list INTERNAL-to-SITE1 extended permit ip IN-HOUSE-GLOBAL SITE1-LAN 255.255.0.0 object-group
access-list INTERNAL-to-training3 extended permitted ip object-IN-HOUSE-GLOBAL object group training3-GLOBAL
access-list INTERNAL-to-SITE2 extended permit ip IN-HOUSE-GLOBAL SITE2-LAN 255.255.0.0 object-group
no pager
Enable logging
exploitation forest asdm warnings
Debugging trace record
Outside 1500 MTU
MTU 1500 INTERNAL
MTU 1500 COMMENTS
192.168.11.1 mask - local 192.168.11.25 pool IN-HOUSE VPN IP 255.255.255.0
no failover
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 623.bin
enable ASDM history
ARP timeout 14400
Global 1 interface (outside)
(INTERNAL) NAT 0 access-list sheep
NAT (INTERNAL) 1 0.0.0.0 0.0.0.0
NAT (GUEST) 1 0.0.0.0 0.0.0.0
5900 5900 Camille netmask 255.255.255.255 interface static tcp (GUEST, outdoor)
3389 3389 Apollo netmask 255.255.255.255 interface static tcp (INDOOR, outdoor)
public static tcp (INDOOR, outdoor) interface www Apollo www netmask 255.255.255.255
public static tcp (INDOOR, outdoor) interface https Apollo https netmask 255.255.255.255
public static tcp (INDOOR, outdoor) interface smtp smtp Apollo netmask 255.255.255.255
5901 puppy 5901 netmask 255.255.255.255 interface static tcp (GUEST, outdoor)
Access-group outside_access in interface outside
Timeout xlate 0:05:00
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-registration DfltAccessPolicy
RADIUS protocol AAA-server Apollo
Apollo (INTERNAL) AAA-server Apollo
Timeout 5
key *.
AAA authentication enable LOCAL console
the ssh LOCAL console AAA authentication
AAA authentication LOCAL telnet console
AAA authentication http LOCAL console
Enable http server
http 0.0.0.0 0.0.0.0 INTERNAL
http 0.0.0.0 0.0.0.0 COMMENTS
No snmp server location
No snmp Server contact
Community SNMP-server
Server enable SNMP traps snmp authentication linkup, linkdown cold start
Crypto ipsec transform-set ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ESP-DES-MD5 esp - esp-md5-hmac
Crypto ipsec transform-set ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ESP-AES-256-SHA 256 - aes - esp esp-sha-hmac
Crypto ipsec transform-set ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec transform-set esp-3des esp-sha-hmac TRANS_ESP_3DES_SHA
Crypto ipsec transform-set transit mode TRANS_ESP_3DES_SHA
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
life crypto ipsec security association seconds 28800
Crypto ipsec kilobytes of life - safety 4608000 association
SYSTEM_DEFAULT_CRYPTO_MAP game 65535 dynamic-map crypto transform-set ESP-3DES-SHA TRANS_ESP_3DES_SHA
correspondence address 1 card crypto outside_map INTERNAL SITE1
card crypto outside_map 1 set of peer SITE1 - ASA
card crypto outside_map 1 set of transformation-ESP-3DES-SHA
address for correspondence card crypto outside_map 2 INTERNAL training3
outside_map 2 peer training3 - ASA crypto card game
card crypto outside_map 2 game of transformation-ESP-3DES-SHA
address for correspondence outside_map 3 card crypto INTERNAL SITE2
game card crypto outside_map 3 peers SITE2 - ASA
card crypto outside_map 3 game of transformation-ESP-3DES-SHA
outside_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
outside_map interface card crypto outside
crypto ISAKMP allow outside
crypto ISAKMP policy 10
preshared authentication
3des encryption
sha hash
Group 2
life 86400
delimiter group @.
Telnet training3 - ASA 255.255.255.255 outside
Telnet SITE2 - ASA 255.255.255.255 outside
Telnet SITE1 - ASA 255.255.255.255 outside
Telnet 0.0.0.0 0.0.0.0 INTERNAL
Telnet 0.0.0.0 0.0.0.0 COMMENTS
Telnet timeout 60
SSH enable ibou
SSH training3 - ASA 255.255.255.255 outside
SSH SITE2 - ASA 255.255.255.255 outside
SSH SITE1 - ASA 255.255.255.255 outside
SSH 0.0.0.0 0.0.0.0 INTERNAL
SSH 0.0.0.0 0.0.0.0 COMMENTS
SSH timeout 60
Console timeout 0
access to the INTERNAL administration
Hello to tunnel L2TP 100
interface ID client DHCP-client to the outside
dhcpd dns 4.2.2.1 4.2.2.2
dhcpd ping_timeout 750
dhcpd outside auto_config
!
address INTERNAL 192.168.10.100 dhcpd - 192.168.10.200
dhcpd Apollo Odyssey interface INTERNAL dns
dhcpd somewhere.com domain INTERNAL interface
interface of dhcpd option 150 ip 10.1.1.40 INTERNAL
enable dhcpd INTERNAL
!
dhcpd address 192.168.2.100 - 192.168.2.200 COMMENTS
dhcpd dns 4.2.2.1 4.2.2.2 interface COMMENTS
enable dhcpd COMMENTS
!a basic threat threat detection
statistical threat detection port
Statistical threat detection Protocol
Statistics-list of access threat detection
a statistical threat detection tcp-interception rate-interval 30 burst-400-rate average rate 200
NTP server 192.43.244.18 prefer external source
WebVPN
allow outside
CSD image disk0:/securedesktop-asa-3.4.2048.pkg
SVC disk0:/sslclient-win-1.1.4.179.pkg 1 image
SVC disk0:/anyconnect-win-2.4.1012-k9.pkg 2 image
enable SVC
Group Policy DefaultRAGroup INTERNAL
attributes of Group Policy DefaultRAGroup
Server DNS 192.168.10.4 value
Protocol-tunnel-VPN l2tp ipsec
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list DefaultRAGroup_splitTunnelAcl
value by default-domain somewhere.com
Group Policy DefaultWEBVPNGroup INTERNAL
attributes of Group Policy DefaultWEBVPNGroup
VPN-tunnel-Protocol webvpn
Group Policy DefaultL2LGroup INTERNAL
attributes of Group Policy DefaultL2LGroup
Protocol-tunnel-VPN IPSec l2tp ipsec
Group Policy DefaultACVPNGroup INTERNAL
attributes of Group Policy DefaultACVPNGroup
VPN-tunnel-Protocol svc
attributes of Group Policy DfltGrpPolicy
value of 192.168.10.4 DNS Server 4.2.2.2
VPN - 25 simultaneous connections
VPN-idle-timeout no
Protocol-tunnel-VPN IPSec
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list DefaultRAGroup_splitTunnelAcl
value by default-domain somewhere.com
the value INTERNAL VPN address pools
chip-removal-disconnect disable card
WebVPN
SVC keepalive no
client of dpd-interval SVC no
dpd-interval SVC bridge no
value of customization DfltCustomization
attributes global-tunnel-group DefaultRAGroup
VPN INTERNAL address pool
Group Policy - by default-DefaultRAGroup
IPSec-attributes tunnel-group DefaultRAGroup
pre-shared-key *.
Disable ISAKMP keepalive
tunnel-group DefaultRAGroup ppp-attributes
No chap authentication
no authentication ms-chap-v1
ms-chap-v2 authentication
attributes global-tunnel-group DefaultWEBVPNGroup
VPN INTERNAL address pool
Group Policy - by default-DefaultWEBVPNGroup
tunnel-group 123.234.8.60 type ipsec-l2l
IPSec-attributes tunnel-group 123.234.8.60
pre-shared-key *.
tunnel-group 123.234.8.124 type ipsec-l2l
IPSec-attributes tunnel-group 123.234.8.124
pre-shared-key *.
tunnel-group 123.234.8.189 type ipsec-l2l
IPSec-attributes tunnel-group 123.234.8.189
pre-shared-key *.
type tunnel-group DefaultACVPNGroup remote access
attributes global-tunnel-group DefaultACVPNGroup
VPN INTERNAL address pool
Group Policy - by default-DefaultACVPNGroup
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the netbios
inspect the rsh
inspect the rtsp
inspect the skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect the tftp
inspect the sip
inspect xdmcp
inspect the http
inspect the they
!
global service-policy global_policy
context of prompt hostname
Cryptochecksum:423c807c0d63cb3e9aeceda977053f84
: end
ASDM image disk0: / asdm - 623.bin
ASDM location Camille 255.255.255.255 INTERNAL
ASDM location INTERNAL CGT-external 255.255.255.255
ASDM location INTERNAL SITE1-LAN 255.255.0.0
ASDM location INTERNAL SITE2-LAN 255.255.0.0
ASDM location INTERNAL training3-LAN 255.255.0.0
ASDM location INTERNAL training3 - ASA 255.255.255.255
ASDM location INTERNAL GDO 255.255.255.255
ASDM location INTERNAL SITE1 - ASA 255.255.255.255
ASDM location INTERNAL SITE2 - ASA 255.255.255.255
ASDM location INTERNAL training3-VOICE 255.255.0.0
ASDM location puppy 255.255.255.255 INTERNAL
enable ASDM historyI should also mention that my test clients are a combination of Windows XP, Windows 7, and Windows Mobile. Other that in specifying the preshared key and forcing L2TP/IPsec on the client side, the VPN settings on clients are the default settings with the help of MS-CHAP/MS-CHAPv2.
You must configure * intercept-dhcp enable * in your group strategy:
attributes of Group Policy DefaultRAGroup
attributes of Group Policy DefaultRAGroup
Server DNS 192.168.10.4 value
Protocol-tunnel-VPN l2tp ipsec
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list DefaultRAGroup_splitTunnelAcl
value by default-domain somewhere.comIntercept-dhcp enable
-Latptop VPN clients (which I assume are on windows computers) is also the * use on remote network default gateway * box unchecked. It is located on the Advanced tab of VPN client TCP/IP properties. Select Client VPN > properties > Networking > TCP/IP Internet Protocol > properties > advanced and uncheck the box.
Alex
-
Access restricted without the split tunneling
I'm disabled with Split tunneling VPN concentrator. Split tunneling has been disabled to carry the internet traffic of vpn clients via our internal web filtering server. But I must restrict access to my internal servers. How can I do that. I tried with filters/Rules but his does not work, and depending on the traffic of documents filter applies only to the traffic unencrypted.
Thank you
Avil
If you use a VPN3000 while you can apply a filter to the users configured in group. This filter can restrict access to the servers as a list of specific protocols and access. This filter certainly applies to ENCRYPTED traffic, do not know what you are referring to your last sentence.
You must first define the rules to define the traffic you want to restrict address., see here for more details:
http://www.Cisco.com/univercd/CC/TD/doc/product/VPN/vpn3000/4_1/config/polmgt.htm#1321359
Define a filter, then add the rules you just set it to him:
http://www.Cisco.com/univercd/CC/TD/doc/product/VPN/vpn3000/4_1/config/polmgt.htm#1007037
Thne go under the group that these users are configured with, and then apply the filter to it.
A couple of sample filter are the following:
Allow access to 10.1.1.2 and block everything else:
To block access to everything, but 10.10.1.2, create a rule that is Inbound/Forward, Source of Anything, Destination of 10.1.1.2/0.0.0.0. Create another rule, it can be left at the default value which is incoming, drop, no matter what Source Dest what whatsoever. Create a filter with the default action of the front and add two new your rules, ensuring that rule that allows access to the host 10.1.12 is above the default rule which will pass everything else.
Block access to 10.1.1.2, and leave all the rest:
To allow access to everything except 10.10.1.2, create a rule that said, drop, no matter what Source and Destination of 10.10.1.2/0.0.0.0. Add a filter that has a default action is to send, add the rule to the filter.
Notes:
-You can allow or block access to subnets simply by changing your address/mask to something like combination: 10.1.1.0/0.0.0.255
-
Hello everyone
I have setup a VPN connection, which I can connect to. For all customers of connection, I want to give them an IP (from a subnet maybe) and let them use this IP address for all that they do.
Therefore, this:
and not current:
My inside is 192.168.1.0
My VPN IP pool is 192.168.30.5 - 200
My server (DNS, files, Web site) is 192.168.1.222Here's my setup. I scored what I thought might have something to do with it:
ASA Version 9.2 (1)
!
ciscoasa hostname
activate 8Ry2YjIyt7RRXU24 encrypted password
volatile xlate deny tcp any4 any4
volatile xlate deny tcp any4 any6
volatile xlate deny tcp any6 any4
volatile xlate deny tcp any6 any6
volatile xlate deny udp any4 any4 eq field
volatile xlate deny udp any4 any6 eq field
volatile xlate deny udp any6 any4 eq field
volatile xlate deny udp any6 any6 eq field
2KFQnbNIdI.2KYOU encrypted passwd
names of
pool of IP local IP-pool 192.168.30.5 - 192.168.30.200 mask 255.255.255.0
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
IP 192.168.1.253 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
IP address dhcp setroute
!
boot system Disk0: / asa921 - k8.bin
passive FTP mode
permit same-security-traffic intra-interface
network obj_any object
subnet 0.0.0.0 0.0.0.0
network of the object Server-25
Home 192.168.1.222
Description of the test server
network of the object server-80
Home 192.168.1.222
Description of the test server
network of the object server-443
Home 192.168.1.222
Description of the test server
network of the object server-2525
Home 192.168.1.222
Description of the test server
network of the object server-993
Home 192.168.1.222
Description of the test server
network of the object server-6001
Home 192.168.1.222
Description of the test server
network of the object server-6002
Home 192.168.1.222
Description of the test server
network of the object server-6003
Home 192.168.1.222
Description of the test server
network of the object server-6004
Home 192.168.1.222
Description of the test server
network of the VPN HOST object
192.168.30.0 subnet 255.255.255.0
the object to the Interior-net network
host 192.168.1.0
the VPN server object network
Home 192.168.1.222
outside_access_in list extended access permit tcp any object Server-25 eq smtp
outside_access_in list extended access permit tcp any object server-2525 2525 eq
outside_access_in list extended access permit tcp any object server-80 eq www
outside_access_in list extended access permit tcp any object server-443 https eq
outside_access_in list extended access permit tcp any object server-993 993 eq
outside_access_in list extended access permit tcp any object server-6001 eq 6001
outside_access_in list extended access permit tcp any object server-6002 6002 eq
outside_access_in list extended access permit tcp any object server-6003 eq 6003
outside_access_in list extended access permit tcp any object server-6004 eq 6004
outside_access_in to access ip 192.168.1.0 scope list allow 255.255.255.0 192.168.30.0 255.255.255.0
permit access-list Split-Tunnel-ACL standard 192.168.30.0 255.255.255.0
no pager
Enable logging
asdm of logging of information
Within 1500 MTU
Outside 1500 MTU
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 721.bin
don't allow no asdm history
ARP timeout 14400
no permit-nonconnected arp
NAT (indoor, outdoor) Interior-net Interior-NET static source static destination HOST-VPN-VPN-HOST
NAT VPN VPN-server destination (indoor, outdoor) static static source HOST-VPN-VPN-HOST
!
network obj_any object
NAT dynamic interface (indoor, outdoor)
network of the object Server-25
NAT (inside, outside) interface static tcp smtp smtp service
network of the object server-80
NAT (inside, outside) interface static tcp www www service
network of the object server-443
NAT (inside, outside) interface static tcp https https service
network of the object server-2525
NAT (inside, outside) interface static 2525 2525 tcp service
network of the object server-993
NAT (inside, outside) interface static tcp 993 993 service
network of the object server-6001
NAT (inside, outside) interface static tcp 6001 6001 service
network of the object server-6002
NAT (inside, outside) interface static tcp 6002 6002 service
network of the object server-6003
NAT (inside, outside) interface static 6003 6003 tcp service
network of the object server-6004
NAT (inside, outside) interface static service tcp 6004 6004
Access-group outside_access_in in interface outside
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
RADIUS AAA server HSS-auth-server protocol
allow only
AAA-server HSS-auth-server (inside) host 192.168.1.222
Timeout 5
key *.
identity of the user by default-domain LOCAL
Enable http server
http 192.168.1.0 255.255.255.0 inside
No snmp server location
No snmp Server contact
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec pmtu aging infinite - the security association
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 define ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
outside_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
outside_map interface card crypto outside
trustpool crypto ca policy
Crypto isakmp nat-traversal 30
Crypto ikev1 allow outside
IKEv1 crypto policy 10
authentication crack
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 20
authentication rsa - sig
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 30
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 40
authentication crack
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 50
authentication rsa - sig
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 60
preshared authentication
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 70
authentication crack
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 80
authentication rsa - sig
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 90
preshared authentication
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 100
authentication crack
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 110
authentication rsa - sig
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 120
preshared authentication
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 130
authentication crack
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 140
authentication rsa - sig
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 150
preshared authentication
the Encryption
sha hash
Group 2
life 86400
Telnet timeout 5
SSH stricthostkeycheck
SSH timeout 5
SSH group dh-Group1-sha1 key exchange
Console timeout 0interface ID client DHCP-client to the outside
dhcpd outside auto_config
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
internal HSSvpn group strategy
attributes of Group Policy HSSvpn
value of server WINS 192.168.1.222
value of server DNS 192.168.1.222
Ikev1 VPN-tunnel-Protocol
Split-tunnel-policy tunnelall
Split-tunnel-network-list value Split-Tunnel-ACL
HSS.dk value by default-field
activate dns split-tunnel-all
type tunnel-group HSSvpn remote access
attributes global-tunnel-group HSSvpn
address IP-pool pool
HSS-auth-server authentication-server-group
Group Policy - by default-HSSvpn
password-management
IPSec-attributes tunnel-group HSSvpn
IKEv1 pre-shared-key *.
tunnel-group HSSvpn ppp-attributes
No chap authentication
no authentication ms-chap-v1
ms-chap-v2 authentication
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:c85ff8bf61669bef56b4dad704a4930a
: endHello
Change Split Tunnel VPN in full Tunnel VPN, you have really do much in your configuration.
Seems that have already changed you the 'tunnelspecified' 'tunnelall' in configurations of the 'group policy' . You can delete the setup but that defines the ACL of Split Tunnel
attributes of Group Policy HSSvpn
No split-tunnel-network-list value Split-Tunnel-ACLSeems that you use an internal AAA server to manage authentication rather than on the SAA. I guess if you want to assign a specific IP address for VPN user/username, then it must be done on the side Server?
If you had the "username" on the SAA configurations you can set it up under its framework which "username" IP address gets when he or she connects with the VPN Client.
As naturally as you start using the complete Tunnel and all traffic from the VPN Client starts to get in the tunnel to the ASA you will need a NAT for VPN Client users Internet traffic. You can configure this NAT like this for example:
network of the VPN-POOL object
192.168.30.0 subnet 255.255.255.0interface of VPN-POOL dynamic NAT (outside, outside) after auto source
Note that this is a manual of NAT / double NAT statement real "nat" IS NOT inserted under the 'object' , but the 'object' is rather created it can be used in the "nat" command. I see that your other dynamic PAT configurations are configured with NAT Auto / object NAT network. You can do this like that too if you wish. Personally I do like that.
But as I said before, it seems that you have already configured the VPN to be full of Tunnel. It is perhaps not as it is? While it is connected with VPN, you should be able to check the secure routes (or something like that) section to see if it says "0.0.0.0" If Yes, then it should be tunneling all traffic.
Hope this helps :)
-Jouni
-
Hello
First of all - thanks to all who post here. I often browse the forums and search for help here and its very useful, so a big pat on the back for all who contribute. My first post, so here goes...
I've got my ASA 5505 v8.2 configured to allow the AnyConnect. This works. Client can connect and access remote systems via VPN. What causes me a massive headache, is the customer loses internet connectivity. I played a bit with my config a bit so what I am about to post that I know for sure is incorrect, but any help is greatly appreciated.
Notes
1. the router was set up for a VPN site to site standard that is no longer functional, but as you can see all the settings are always in the router.
2. the router also a DMZ configuration has to allow access to the internet with the help of the DMZ to some customers
CONFIGURATION:
ASA Version 8.2 (5)
!
hostname MYHOST
activate mUUvr2NINofYuSh2 encrypted password
UNDrnIuGV0tAPtz2 encrypted passwd
names of
name x.x.x.x LIKES-SD
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
switchport access vlan 7
!
interface Vlan1
nameif inside
security-level 100
192.168.101.1 IP address 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
IP x.x.x.x 255.255.0.0
!
interface Vlan7
prior to interface Vlan1
nameif DMZ
security-level 20
IP 137.57.183.1 255.255.255.0
!
passive FTP mode
clock timezone STD - 7
the obj_any_dmz object-group network
10 extended access-list allow ip 192.168.25.0 255.255.255.0 192.168.6.0 255.255.255.0
permit access ip host x.x.x.x 192.168.25.0 extended list no_nat 255.255.25 5.0
tunneling split list of permitted access standard 192.168.101.0 255.255.255.0
192.168.101.0 IP Access-list extended sheep 255.255.255.0 allow all
pager lines 24
Enable logging
debug logging in buffered memory
asdm of logging of information
Within 1500 MTU
Outside 1500 MTU
MTU 1500 DMZ
mask 192.168.101.125 - 192.168.101.130 255.255.255.0 IP local pool Internal_Range
ICMP unreachable rate-limit 1 burst-size 1
don't allow no asdm history
ARP timeout 14400
Global interface 10 (external)
NAT (inside) 0-list of access no_nat
NAT (inside) 1 access-list sheep
NAT (DMZ) 10 137.57.183.0 255.255.255.0
Route outside 0.0.0.0 0.0.0.0 x.x.x.x 1
Route inside 192.168.8.0 255.255.255.0 192.168.101.2 1
Timeout xlate 03:00
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
the ssh LOCAL console AAA authentication
http server enable 64000
http 0.0.0.0 0.0.0.0 inside
No snmp server location
No snmp Server contact
Server enable SNMP traps snmp authentication linkup, linkdown cold start
Crypto ipsec transform-set esp-aes-256 batus, esp-sha-hmac
life crypto ipsec security association seconds 28800
Crypto ipsec kilobytes of life - safety 4608000 association
correspondence address card crypto 100 10 batus
crypto batus 100 peer LIKES-SD card game
batus batus 100 transform-set card crypto
batus outside crypto map interface
Crypto ca trustpoint ASDM_TrustPoint1
registration auto
name of the object CN = MYHOST
ClientX_cert key pair
Configure CRL
string encryption ca ASDM_TrustPoint1 certificates
certificate 0f817951
308201e7 a0030201 30820150 0202040f 0d06092a 81795130 864886f7 0d 010105
05003038 31173015 06035504 03130e41 494d452d 56504e2d 42415455 53311d 30
1b06092a 864886f7 0d 010902 160e4149 4d452d56 504e2d42 41545553 301e170d
31333036 32373137 32393335 5a170d32 33303632 35313732 3933355a 30383117
30150603 55040313 0e41494d 452-5650 4e2d4241 54555331 1d301b06 092 d has 8648
86f70d01 0902160e 41494d 45 2d56504e 424154 55533081 9f300d06 092 2d has 8648
86f70d01 01010500 03818d 30818902 00 818100c 9 ff840bf4 cfb8d394 2 c 940430
1887f25a 49038aa0 1299cf10 bda2a436 227dcdbf f1c5566b c35c2f19 8b3514d3
4e24f5b1 c8840e8c 60e2b39d bdc0082f 08cce525 97ffefba d42bb087 81b9adb9
db0a8b2f b643e651 d17cd6f8 f67297f2 d785ef46 c3acbb39 615e1ef1 23db072c
783fe112 acd6dc80 dc38e94b 6e56fe94 d59d5d02 03010001 300 d 0609 2a 864886
8181007e f70d0101 05050003 29e90ea0 e337976e 9006bc02 402fd58a a1d30fe8
b2c1ab49 a1828ee0 488d1d2f 1dc5d150 3ed85f09 54f099b2 064cd 622 dc3d3821
fca46c69 62231fd2 6e396cd1 7ef586f9 f41205af c2199174 3c5ee887 42b684c9
7f4d2045 4742adb5 d70c3805 4ad13191 8d802bbc b2bcd8c7 8eec111b 761d89f3
63ebd49d 30dd06f4 e0fa25
quit smoking
crypto ISAKMP allow outside
crypto ISAKMP policy 40
preshared authentication
aes-256 encryption
sha hash
Group 5
life 86400
Telnet timeout 5
SSH 0.0.0.0 0.0.0.0 inside
SSH 0.0.0.0 0.0.0.0 DMZ
SSH timeout 10
Console timeout 0
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
SSL encryption rc4 - md5, rc4-aes128-sha1 aes256-3des-sha1 sha1 sha1
SSL-trust outside ASDM_TrustPoint1 point
WebVPN
allow outside
SVC disk0:/anyconnect-win-2.4.1012-k9.pkg 1 image
enable SVC
internal ClientX_access group strategy
attributes of Group Policy ClientX_access
VPN-tunnel-Protocol svc
Split-tunnel-network-list value split tunneling
access.local value by default-field
the address value Internal_Range pools
IPv6 address pools no
WebVPN
SVC mtu 1406
generate a new key SVC time no
SVC generate a new method ssl key
username privilege 15 encrypted password ykAxQ227nzontdIh ClientX
ClientX username attributes
VPN-group-policy ClientX_access
type of service admin
tunnel-group x.x.x.x type ipsec-l2l
tunnel-group ipsec-attributes x.x.x.x
pre-shared key *.
tunnel-group ClientX type remote access
attributes global-tunnel-group ClientX
address pool Internal_Range
Group Policy - by default-ClientX_access
type tunnel-group SSLClientProfile remote access
attributes global-tunnel-group SSLClientProfile
Group Policy - by default-ClientX_access
type tunnel-group ClientX_access remote access
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:e7d92a387d1c5f07e14b3c894d159ec1
: end
-----------------------
Thanks for any help!
In your group strategy, you specified the ACLs that should be used for split Tunneling, but you forgot to change the policy, so the ASA always uses tunnel-all. Here's what you'll need:
attributes of Group Policy ClientX_access
Split-tunnel-network-list value split tunneling
Split-tunnel-policy tunnelspecified
--
Don't stop once you have upgraded your network! Improve the world by lending money to low-income workers:
http://www.Kiva.org/invitedBy/karsteni -
Remote VPN: split tunnel filtering
Hello!
The question is about the split tunnel filtering capabilities without using the vpn-filter.
Suppose, we have ASA configured for remote VPN tunneling with split without VPN filter.
- 10.0.0.0/8 is the private netwrok.
- 10.1.0.0/24 is the private network, defined in the split tunnel
- 172.16.1.0/24 is the VPN SECURE network
When the remote client connects, it receives the routes to the private network (10.1.0.0/24).
What happens if the remote client adds the route to a private network (which is not defined by a tunnel of split) by itself (e.g. 10.2.0.0/24)?
Our test LAB, we can see that the customer does not have access to 10.2.0.0/24.
Where the place in this case filtering?
- By default, all vehicles coming from VPN, bypasses all ACLs configured on interfaces ASA.
- Filter VPN is not configured.
- Nat0 don't traffic 10.0.0.0/8 to 172.16.1.0/24 NAT
- of the sh ip cry his on the VPN server, we can see, this ident is 0.0.0.0/0
- local ident (addr, mask, prot, port): (0.0.0.0/0.0.0.0/0/0)
- Remote ident (addr, mask, prot, port): (172.16.1.1/255.255.255.255/0/0)
The ACL of split tunnel is capable for remote client traffic filtering?
I understand that your question is in what regards the IPSec VPN Client, no AnyConnect VPN Client, however, I think that the behavior of the split tunnel is the same.
Here's the answer to your question:
A. AnyConnect applies the policy of tunnel in 2 ways:
Monitoring of track 1) and repair (for example if you change the routing table), AnyConnect will restore it to what has been configured.
(2) filtering (on platforms that support filter engines). Filtering ensures that even if you can perform a kind of injection of the route, the filters would block packets.
-
Hello
I don't know what could be held, vpn users can ping to the outside and inside of the Cisco ASA interface but can not connect to servers or servers within the LAN ping.
is hell config please kindly and I would like to know what might happen.
hostname horse
domain evergreen.com
activate 2KFQnbNIdI.2KYOU encrypted password
2KFQnbNIdI.2KYOU encrypted passwd
names of
ins-guard
!
interface GigabitEthernet0/0
LAN description
nameif inside
security-level 100
192.168.200.1 IP address 255.255.255.0
!
interface GigabitEthernet0/1
Description CONNECTION_TO_FREEMAN
nameif outside
security-level 0
IP 196.1.1.1 255.255.255.248
!
interface GigabitEthernet0/2
Description CONNECTION_TO_TIGHTMAN
nameif backup
security-level 0
IP 197.1.1.1 255.255.255.248
!
interface GigabitEthernet0/3
Shutdown
No nameif
no level of security
no ip address
!
interface Management0/0
Shutdown
No nameif
no level of security
no ip address
management only
!
boot system Disk0: / asa844-1 - k8.bin
boot system Disk0: / asa707 - k8.bin
passive FTP mode
clock timezone WAT 1
DNS server-group DefaultDNS
domain green.com
network of the NETWORK_OBJ_192.168.2.0_25 object
Subnet 192.168.2.0 255.255.255.128
network of the NETWORK_OBJ_192.168.202.0_24 object
192.168.202.0 subnet 255.255.255.0
network obj_any object
subnet 0.0.0.0 0.0.0.0
the DM_INLINE_NETWORK_1 object-group network
object-network 192.168.200.0 255.255.255.0
object-network 192.168.202.0 255.255.255.0
the DM_INLINE_NETWORK_2 object-group network
object-network 192.168.200.0 255.255.255.0
object-network 192.168.202.0 255.255.255.0
access-list extended INSIDE_OUT allow ip 192.168.202.0 255.255.255.0 any
access-list extended INSIDE_OUT allow ip 192.168.200.0 255.255.255.0 any
Access extensive list permits all ip a OUTSIDE_IN
gbnlvpntunnel_splitTunnelAcl standard access list allow 192.168.200.0 255.255.255.0
standard access list gbnlvpntunnel_splitTunnelAcl allow 192.168.202.0 255.255.255.0
gbnlvpntunnell_splitTunnelAcl standard access list allow 192.168.200.0 255.255.255.0
standard access list gbnlvpntunnell_splitTunnelAcl allow 192.168.202.0 255.255.255.0
pager lines 24
Enable logging
asdm of logging of information
Within 1500 MTU
Outside 1500 MTU
backup of MTU 1500
mask of local pool VPNPOOL 192.168.2.0 - 192.168.2.100 IP 255.255.255.0
no failover
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm-645 - 206.bin
don't allow no asdm history
ARP timeout 14400
NAT (inside, outside) static source NETWORK_OBJ_192.168.202.0_24 NETWORK_OBJ_192.168.202.0_24 NETWORK_OBJ_192.168.2.0_25 NETWORK_OBJ_192.168.2.0_25 non-proxy-arp-search of route static destination
NAT (inside, backup) static source NETWORK_OBJ_192.168.202.0_24 NETWORK_OBJ_192.168.202.0_24 NETWORK_OBJ_192.168.2.0_25 NETWORK_OBJ_192.168.2.0_25 non-proxy-arp-search of route static destination
NAT (inside, outside) static source DM_INLINE_NETWORK_1 DM_INLINE_NETWORK_1 NETWORK_OBJ_192.168.2.0_25 NETWORK_OBJ_192.168.2.0_25 non-proxy-arp-search of route static destination
NAT (inside, backup) static source DM_INLINE_NETWORK_2 DM_INLINE_NETWORK_2 NETWORK_OBJ_192.168.2.0_25 NETWORK_OBJ_192.168.2.0_25 non-proxy-arp-search of route static destination
!
network obj_any object
dynamic NAT interface (inside, backup)
Access-group interface inside INSIDE_OUT
Access-group OUTSIDE_IN in interface outside
Route outside 0.0.0.0 0.0.0.0 196.1.1.2 1 track 10
Route outside 0.0.0.0 0.0.0.0 197.1.1.2 254
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
identity of the user by default-domain LOCAL
Enable http server
http 192.168.200.0 255.255.255.0 inside
http 192.168.202.0 255.255.255.0 inside
No snmp server location
No snmp Server contact
Server enable SNMP traps snmp authentication linkup, linkdown cold start
monitor SLA 100
type echo protocol ipIcmpEcho 212.58.244.71 interface outside
Timeout 3000
frequency 5
monitor als 100 calendar life never start-time now
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 pfs Group1 set
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 define ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
outside_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
outside_map interface card crypto outside
backup_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
backup of crypto backup_map interface card
Crypto ikev1 allow outside
Crypto ikev1 enable backup
IKEv1 crypto policy 10
authentication crack
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 20
authentication rsa - sig
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 30
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 40
authentication crack
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 50
authentication rsa - sig
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 60
preshared authentication
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 70
authentication crack
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 80
authentication rsa - sig
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 90
preshared authentication
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 100
authentication crack
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 110
authentication rsa - sig
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 120
preshared authentication
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 130
authentication crack
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 140
authentication rsa - sig
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 150
preshared authentication
the Encryption
sha hash
Group 2
life 86400
!
track 10 rtr 100 accessibility
Telnet 192.168.200.0 255.255.255.0 inside
Telnet 192.168.202.0 255.255.255.0 inside
Telnet timeout 5
SSH 192.168.202.0 255.255.255.0 inside
SSH 192.168.200.0 255.255.255.0 inside
SSH 0.0.0.0 0.0.0.0 outdoors
SSH timeout 15
SSH group dh-Group1-sha1 key exchange
Console timeout 0
management-access inside
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
WebVPN
internal group vpntunnel strategy
Group vpntunnel policy attributes
Ikev1 VPN-tunnel-Protocol
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list vpntunnel_splitTunnelAcl
field default value green.com
internal vpntunnell group policy
attributes of the strategy of group vpntunnell
Ikev1 VPN-tunnel-Protocol
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list gbnlvpntunnell_splitTunnelAcl
field default value green.com
Green user name encrypted BoEFKkDtbnX5Uy1Q privilege 15 password
attributes of user name THE
VPN-group-policy gbnlvpn
tunnel-group vpntunnel type remote access
tunnel-group vpntunnel General attributes
address VPNPOOL pool
strategy-group-by default vpntunnel
tunnel-group vpntunnel ipsec-attributes
IKEv1 pre-shared-key *.
type tunnel-group vpntunnell remote access
tunnel-group vpntunnell General-attributes
address VPNPOOL2 pool
Group Policy - by default-vpntunnell
vpntunnell group of tunnel ipsec-attributes
IKEv1 pre-shared-key *.
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns migrated_dns_map_1
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the migrated_dns_map_1 dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
call-home
Profile of CiscoTAC-1
no active account
http https://tools.cisco.com/its/service/oddce/services/DDCEService destination address
email address of destination [email protected] / * /
destination-mode http transport
Subscribe to alert-group diagnosis
Subscribe to alert-group environment
Subscribe to alert-group monthly periodic inventory
monthly periodicals to subscribe to alert-group configuration
daily periodic subscribe to alert-group telemetry
Cryptochecksum:7c1b1373bf2e2c56289b51b8dccaa565
Hello
1 - Please run these commands:
"crypto isakmp nat-traversal 30.
"crypto than dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 Road opposite value.
The main issue here is that you have two roads floating and outside it has a better than backup metric, that's why I added the command 'reverse-road '.
Please let me know.
Thank you.
-
Easy VPN between two ASA 9.5 - Split tunnel does not
Hi guys,.
We have set up a site to site vpn using easy configuration vpn between ver 9.5 race (1) two ASA. The tunnels are up and ping is reached between sites. I also configured split tunnel for internet traffic under the overall strategy of the ASA easy vpn server. But for some unknown reason all the customer same internet traffic is sent to the primary site. I have configured NAT to relieve on the side of server and client-side. Please advise if no limitation so that the installation program.
Thank you and best regards,
Arjun T P
I have the same question and open a support case.
It's a bug in the software 9.5.1. See the bug: CSCuw22886
-
Best Soho - Split Tunnel VPN router
Hi - I'm looking for some advice for a soho router.
Basically the main feature, I'm looking for is to run, which I think is a VPN split tunnel, so that all internal clients route default traffic out to the gateway of the ISP. However, if the traffic is destined for a list of several specific subnets (x.x.x.x/24, y.y.y.y/24 etc.), then it should establish a tunnel to an only PPTP/IPSEC host and route remote traffic for these subnets via the tunnel. To be clear, that these subnets (x.x.x.x and y.y.y.y) is not attached to the end of the tunnel - which is a gateway device that will route them further.
I've been watching the various VPN router offers and is not clear to me if I can do it with a RV - 042, BEFVP41 or something like the other thing SRP521W I must be able to manipulate the routing tables directly on.
As an additional note, I have complete control over the end of SOHO - but simply an account at the end of the tunnel with (it is a service provider). The idea is to use public services for 90% of the traffic, but if customers want to access a specific set of addresses, it will forward this specific traffic through the tunnel.
Thanks in advance...
On current view, do not touch the RPS with a bargepole.
Adding access to additional subnets through a VPN tunnel is pretty standard, routing will be automatic if the VPN was established, but you must ensure that
1. politics VPN at BOTH ENDS allows your local subnet to access these networks
2. your subnet is not incompatible with other subnets or roads that can be used on remote networks
3. assuming you're OK so far, remote subnets must have a route is added to the default gateway to point to your subnet via intermediate networks
Good luck!
-
VPN, Internet and a Split Tunnels traffic
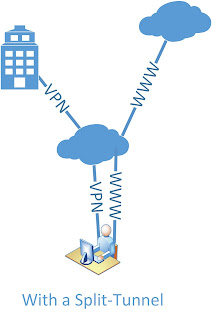
Please attached photo because I hope that explains what I really want to do, but here's the break down.
When a VPN Client connects to remote access to 1-ASA5510 I want all Internet traffic to send to 2 - ASA5510 instead of back to the default route. When it comes out 2-ASA5510, it passes through the content filter. 2 - ASA5510 has Split Tunnel put in place and we are trying to do away with Tunnel from SPlit.
I hope this is clear enough.
Any ideas would be helpful
Dan
Dan,
Difficult but doable! First of all, there is a nice feature in the ASA that allows configuration of remote proxy based on VPN profile by: -.
Group Policy <> attributes
use a MSIE-proxy-server method
Internet Explorer-proxy server value x.x.x.x
activate Internet Explorer-proxy local-bypass
Well Yes you guessed it - works only on Microsoft Internet Explorer.
I don't think that any policy based routing would work for you - bad luck.
But you can try another feature - traffic through the tunnel, which is normally used in the topllogy of EasyVPN: -.
Configuration of the ASA at the bottom, I probably would test this with the IP address of the 2651 router!
HTH.
-
Internet access without split tunneling VPN PIX
I have a PIX 515E with code 6.31. I installed a VPN to allow access to the internal network from the Internet using the Cisco VPN client. It does not work properly. We have some sellers who demand that we come from our Internet IP range to allow us access to their database on the Internet. This works very well for our internal users, but I will allow users VPN for this also.
Is there a way to allow the user from the VPN client to use the Internet for business access to the internet instead of use the split tunneling to access the internet through their own connection? I would like users to vpn to be NAT would have réécrirait Internet and seeming come from our pool of Internet addresses. What I found references by using the split tunneling, but this won't work for me. Am I stuck getting a VPN concentrator to achieve?
Thank you
Josh
The PIX cannot route a package back on the same interface, he entered the, which includes a customer entering the interface external and routed VPN package back on the same interface.
A router or a VPN concentrator would be able to do this, but not a PIX, sorry.
-
Help: Customer Cisco VPN & Split Tunnel but not Internet
Hi Forum.
We are faced with this problem: after having successfully open a VPN connection with the Cisco VPN Client to a router Cisco, the rest of the world are not properly available more.
This is what has been verified / so far attempted to identify the problem on a Windows Vista computer:
-Router: Split Tunneling is allowed according to sysop
-On the VPN-Client: "allow Local Lan access" is checked
-On the Client (statistics): only STI VPN-rout configured listed unter "guarantee routes." "Local Lan routes" is empty.
-Calling 'http://www.google.com' in IE fails
-Call ' 74.125.232.116' (IE IP) IE works / ping the IP works.
-nslookup properly lists the current DNS server
-nslookup www.google.com resolves correctly the name of intellectual property
It seems that it is not that the connection with the rest of the Internet is deleted, but DNS resolution fails somehow, even though all signs point to the appropriate DNS server is in force and although the command line can resolve the name.
does anyone have a tip how to debug this correctly?
No worries Pat...
Sent by Cisco Support technique iPhone App
-Please evaluate solutions
-
Split tunneling VPN site-to-site
Dear all,
I have two ASA 5510 with VPN site-to-site, I can send all Internet traffic to the central site (HQ),
How to set the split tunneling to access Campus LAN (192.168.2.0/24) of LAN2.
Thank you in advance.
Best regards
Zoltan
You can have 'decline' instruction on your ACL crypto and he will deviate the traffic is encrypted to the site-to-site VPN tunnel.
For ASA 1:
access-list extended 100 permit ip 10.10.16.192 255.255.255.192 10.10.16.128 255.255.255.192
access-list extended 100 permit ip 10.0.0.0 255.0.0.0 10.10.16.128 255.255.255.192
access-list extended 100 deny ip 192.168.2.0 255.255.255.0 10.10.16.128 255.255.255.192
access-list extended 100 permit ip any 10.10.16.128 255.255.255.192
For ASA 2:
access-list extended 100 permit ip 10.10.16.128 255.255.255.192 10.10.16.192 255.255.255.192
access-list extended 100 permit ip 10.10.16.128 255.255.255.192 10.0.0.0 255.0.0.0
access-list extended 100 deny ip 10.10.16.128 255.255.255.192 192.168.2.0 255.255.255.0
access-list extended 100 permit ip 10.10.16.128 255.255.255.192 all
Hope that helps.
-
Access remote VPN, no split tunneling, internet access. Translation NAT problem
Hi all, I'm new to the forum. I have a Cisco ASA 5505 with confusing (to me) question NAT.
Unique external IP (outside interface) with several translations of NAT static object to allow the redirection of port of various internal devices. The configuration worked smoothly during the past years.
Recently, I configured a without the split tunneling VPN remote access and access to the internet and noticed yesterday that my port forwarding has stopped working.
I reviewed the new rules for the VPN NAT and found the culprit.
I've been reviewing the rules again and again, and all I can think about and interpret it, I don't know how this rule affects the port forwarding on the device or how to fix.
Here's the NAT rules, I have in place: ('inactive' rule is the culprit. Once I have turn on this rule, the port forwarding hits a wall)
NAT (inside, outside) static source any any static destination VPN_Subnet VPN_Subnet non-proxy-arp-search to itinerary
NAT (outside, outside) static source VPN_Subnet VPN_Subnet VPN_Subnet VPN_Subnet non-proxy-arp-search of route static destination
NAT (outside, outside) source VPN_Subnet dynamic interface inactive
!
network obj_any object
NAT dynamic interface (indoor, outdoor)
network of the XXX_HTTP object
NAT (inside, outside) interface static tcp www www service
Access-group outside_access_in in interface outside
Route outside 0.0.0.0 0.0.0.0 xxx.xxx.xxx.xxx 1Any help would be appreciated.
Try changing the nat rule to VPN_Subnet interface of nat (outside, outside) the after-service automatic dynamic source
With respect,
Safwan
Maybe you are looking for
-
How to convert the string to a full decimal point and left shift
Hey guys I tried to convert gps string to an integer, like this A string that is 2467.8976 and I need to convert it to a similar integer as point of this 2467.8979 so that I can shift the decimal point to the left (24.678979) which i coudnt do it wit
-
KB2686509 cannot install with error 0x8007F0F4
I tried to update the KB2686509 but fails with ErrorCode 0x8007F0F4
-
HP PSC 1610 all in one printer Scanner Copier
Seen the documents problem scanning. Receipt of message is 'no scan options '. Where can I get software to 'device '. searched for the PC using HP Image Zone and can't find it.
-
I can't read ods odt files in vista 32 and
I can't read ODS ODT FILES AND IT IS COMING AS SYMBOLS AND SIGNS, HOW can I GET MY WORK I'M BACK with the HELP of VISTA 32
-
My mom has a Dell computer and its toolbars took a good deal of space in the top of the screen. I went to the icon VIEW and clicking full screen display. Now, I can't search toolbars of icons or no way for her to save, or anything. All this happens i