Aggressive mode IKE on VPN3K
Hello
I have VPN 3005 with 4.7.2 OS (a last to this day). I am trying to turn off the Mode aggressive treatment (stick to the main Mode only) for VPN clients to remove. Please note that remote VPN clients and NOT the LAN-to-LAN connections.
So far I don't see how this can be done.
TAC engineer is not to come up with more good responses.
In any case has an idea?
Thank you!
David
I don't think you can do the Remoting on VPN
the hub works with the main mode, unless
you decide to use the certificate instead of
pre-shared key:
"The Cisco VPN client uses main mode and aggressive mode pre-shared keys are used when the public key (PKI) infrastructure is used in Phase 1 of the tunnel negotiations. After wearing the Internet Security Association and Key Management Protocol (ISAKMP Security Association) Association Security upward for secure communications, Cisco VPN 3000 Concentrator prompts the user to specify the credentials of the user. In this phase, also known under the name X-Auth or extended authentication, the VPN 3000 Concentrator valid user on the database of authentication configured. If authentication success, the Cisco Concentrator sends a message of successful customer authentication. After X-Auth, the Cisco VPN client application configuration settings such as the assigned IP address, the domain name system (DNS) server IP address and the IP address of the Server Windows Internet Naming Service (WINS). During this phase, called mode-config, the VPN 3000 Concentrator sends the settings configured at the client. The final step for a VPN tunnel successful is negotiating the parameters of Phase 2.
Tags: Cisco Security
Similar Questions
-
We used to use IPSEC VPN, but now Anyconnect SSL VPN. We have a third sweep our external firewall, and they recommend that we disable aggressive Mode IKE. This is only used for IPSec VPN? Is it safe to remove our configuration on our ASA 5505?
crypto isakmp identity address
crypto ISAKMP allow outside
crypto ISAKMP policy 10
preshared authentication
3des encryption
sha hash
Group 2
life 86400
Thank you.
Hi Bill,
Aggressive mode (3 pkt Exchange) is only used for remote access IPsec. The site to site VPN using main mode (6 pkt Exchange). If you don't have any VPN site to site, you can disable these commands but if you have VPN site to site then removing these will break them.
There was nothing called aggressive mode in Anyconnect. AnyConnect uses a totally different protocol called SSL (port 443 TCP/UDP).
Hope that answers your question.
Thank you
Vishnu Sharma
-
Tunnel of IOS Interface IKE aggressive mode
I had a pen test scan on a few of my routers and she claims that IKE aggressive Mode of operation are my IOS routers.
I'm having a problem to know how to disable this option in the version of IOS 12.4 (24) T. I can find it on other platforms, but not of IOS. Can someone tell me please in the right direction?
Thank you
You can turn off with
disable ISAKMP aggressive mode crypto
-
Need for visibility on the IPsec protocol: aggressive Mode
Hello
I have a few doubts about VPN. I already went through a large number of documents. Everybody says something I don't agree with. So please don't view this kind of material in your answer.
Aggressive mode: what I know, there are 3 Exchange for aggressive mode. Initiator in the first message sends the ID parameters, DH, HIS (IP address, domain name FULL). Then the answering machine (2nd MSG) reacts with the SA settings, DH, ID, HASH_R, then the initiator (3rd MSG) responds with HASH_I and PHASE 1 is established here.
As the initiator and the responder IDs are sent in clear text, so we say that aggressive mode is not course.
DH is used to exchange keys between peers. DH, negotiates and then generate a SECRET_KEY which in turn, is used to encrypt the symmetric key. We have SA parameters for encryption, hash, authentication.
Here are my questions:
(a) all of ITS parameters, IDs, DH traded first and second messages. The third message from the initiator is to send to HASH_I. Now, I don't see at all any use of DH in this mode, no encryption (payload ISAKAMP is not encrypted). A single phase 1 aims to build a secure layer of management so that the PHASE connection 2 (data connection) may establish under a secure layer (PHASE 1). Now, I see that in aggressive mode we are not able to achieve this secure layer. So, what's the point of having encryption algorithms and DH in PHASE 1 if they are never used? Instead of skip PHASE 1 and we can have the PFS in Phase 2 for serving as a DH and we were hashing algorithms, encryption too.
(b) the PRE SHARED KEY is actually shared via connect using the DH? Or just a HASH of PRE-SHARED-KEY is generated and sent on the connection for authentication?
(c) why the aggressive mode can be used for dynamic addressing and not the main mode?
If please answer queries and correct me if I am wrong somewhere.
Thank you
Rakesh Kumar
(a). theoretically, jumping Phase 1 and done everything in Phase 2 (for aggressive mode only) would probably be a good idea to make it safer. However, this would require a complete redesign of the IKE protocol. As you probably already know, aggressive mode is used by default only for VPN remote access, and I've never seen used for a site to any of the customers that I came in contact. In aggressive mode, in my opinion, would be used only in situations where a large number of VPN tunnels are built and demolished all the time (as with RA VPN) to save on material resources. But... It is what it is, not a very safe to use method.
(b) the pre-shared key is used to create a hash and this hash is sent to the remote peer. If the remote peer can create the same hash using its own pre-shared key, then peers know they share the same secrets. The problem with aggressive mode is that the hash is sent in plain text format, so if an attacker is able to capture these data they could preform a brute force offline attack.
(c). I think that this has to do with the fact that the aggressive mode sends its identity in text clear and not must therefore not be pre-configured as a peer answer as it does with tunnels with addresses static at both ends.
--
Please do not forget to select a correct answer and rate useful posts
-
Anyconnect Ikev2 uses aggressive Mode
Hello world
I'm trying to fix the IKE Aggressive mode with vulnerabilities PSK on our Cisco ASA that runs old IPsec and Ikev2 Anyconnect VPN.
When I run the command
Crypto isakmp HS her
User using IPSEC VPN
IKEv1 SAs:
HIS active: 25
Generate a new key SA: 0 (a tunnel report Active 1 and 1 to generate a new key during the generate a new key)
Total SA IKE: 251 peer IKE: 63.226.x.x
Type: user role: answering machine
Generate a new key: no State: AM_ACTIVEThen, he tells me that this VPN client is using aggressive mode right?
User using IKEV2 anyconnect
Crypto isakmp HS her
17 peer IKE: 192.206.x.x
Type: user role: answering machine
Generate a new key: no State: AM_ACTIVEIKEv2 SAs:
Session-id: 361, status: ACTIVE UP, IKE County: 1, number of CHILDREN: 1
Tunnel-id Local remote status role
x.x.x.x/4500 1696279645 192.206..x.x/33328 answering MACHINE READY
BA: AES - CBC, keysize: 256, Hash: SHA96, Grp:5 DH, Auth sign: RSA, Auth check: EAP
Duration of life/active: 86400/24756 sec
His child: local selector 0.0.0.0/0 - 255.255.255.255/65535
selector of distance 172.16..x.x.144/0 - 172.16.x.x/65535
SPI ESP/output: 0xa315b767/0xbec2f7ccNeed to know anyconnect ikev2 does not share any key of share pre then why the number of line 17 shows AM (aggressive mode)?
The ikev2 Protocol has nothing to do with the aggressive mode or main at all.
If you do a 'sh crypto isa"it will show you the the ikev1 and his ikev2.
If you still see a flow in the table, maybe it's a stuck session.
To disable the aggressive mode, enter the following command:
Crypto ikev1 am - disable
For example:
HostName (config) # crypto ikev1 am - disable
-
Hello
Can someone tell me whatthe above message means and how to solve it.
Thank you
The command to disable connections inbound aggressive mode.
If you want, there is an option to disable connections inbound aggressive mode on the tunnel-group as well.
tunnel-group ipsec-attributes xxxxxx
ISAKMP am - disable
In this way you disable connections inbound aggressive mode to a specific peer.
If a peer tries to establish a connection in aggressive mode, you should see a message like this in the logs:
"Unable to initiate or respond to fashion aggressive while disabled"
This command prevents Easy VPN Virtual Private Network (easy) clients to connect if they use of pre-shared keys because the easy VPN (hardware and software) customers use aggressive mode.
Federico.
-
IPsec VPN Client - aggressive mode
Hi all
I just got got off the phone with the customer who underwent a check sweep of security from a third-party vendor. One of the vulnerebilities mentioned in the report is this:
I know that only the IPsec VPN client using aggressive mode to negotiate Phase I. So my question is how to convince my customer to continue to use the IPsec VPN? Is this what can I do to reduce the risk of the use of this type of access remotely. In addition, am I saw the same problem, if I use SSL based VPN Client?
Kind regards
Marty
Hello
Ikev1 HUB in aggressive mode sends his PSK hash in the second package as well as its public DH value.
It is indeed a weakness of slope Protocol.
To be able to act on this, U will be on the path to capture this stream in order to the brute force of the hash [which is not obvious - but not impossible.
This issue is seriously attenuated by activating XAUTH [authentication].
Xauth happens after the DH, so under encryption.
Assuming that the strong password policy is in use, it is so very very very difficult to find the right combination of username/password.
Ikev2 is much safer in this respect and this is the right way.
See you soon,.
Olivier
-
Tunnel VPN site to Site - aggressive Mode
I searched the community for answers to this and that you have not found quite what I was looking for (or what seems logical). I have an ASA 5510 to A site with one website VPN tunnel to a SonicWall to site B. Which works very well. I need to create a tunnel for site C to site a using a tunnel of aggressive mode. I'm not quite sure how to do this. Any suggestion would be great!
NOTE: I have included the parts of the running configuration that seem relevant to me. If I missed something please let me know.
ASA Version 8.2 (1)
interface Ethernet0/0
nameif outside
security-level 0
IP 1.2.3.4 255.255.255.248
!
10.5.2.0 IP Access-list extended site_B 255.255.255.0 allow 10.205.2.0 255.255.255.128
access extensive list ip 10.5.2.0 site_C allow 255.255.255.0 10.205.2.128 255.255.255.128
dynamic-access-policy-registration DfltAccessPolicy
Crypto ipsec transform-set ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ESP-DES-MD5 esp - esp-md5-hmac
Crypto ipsec transform-set ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ESP-AES-256-SHA 256 - aes - esp esp-sha-hmac
Crypto ipsec transform-set ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
Crypto ipsec transform-set ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set esp-3des esp-sha-hmac 3des-sha1
life crypto ipsec security association seconds 28800
Crypto ipsec kilobytes of life - safety 4608000 association
crypto VPN 30 card matches the address site_B
card crypto VPN 30 peer set 4.3.2.1
crypto VPN 30 the transform-set 3des-sha1 value card
card crypto VPN 40 corresponds to the address site_C
card crypto VPN. 40 set peer 8.7.6.5
crypto VPN. 40 the transform-set 3des-sha1 value card
crypto ISAKMP allow outside
crypto ISAKMP policy 10
preshared authentication
3des encryption
sha hash
Group 2
life 86400
Crypto isakmp nat-traversal 30
crypto ISAKMP ipsec-over-tcp port 10000
attributes of Group Policy DfltGrpPolicy
Protocol-tunnel-VPN IPSec l2tp ipsec svc webvpn
tunnel-group 4.3.2.1 type ipsec-l2l
4.3.2.1 tunnel-group ipsec-attributes
pre-shared-key *.
tunnel-group 8.7.6.5 type ipsec-l2l
IPSec-attributes tunnel-group 8.7.6.5
pre-shared-key *.
David,
Please try this:
clear crypto ipsec its peer site_c_IP
clear configure VPN 40 crypto card
card crypto VPN 10 corresponds to the address site_C
card crypto VPN 10 set peer 8.7.6.5
crypto VPN 10 the transform-set 3des-sha1 value card
debug logging in buffered memory
capture drop all circular asp type
capture capin interface inside the match ip 10.5.2.0 255.255.255.0 10.205.2.128 255.255.255.128
After generating the traffic and INTERNAL of the machine behind the ASA:
view Journal | 10.205.2 Inc.
See the fall of cap. 10.205.2 Inc.
view Cape capin
In case it does not work:
(a) show the crypto classic table ASP.
(b) details of vpn-framework for table ASP.
(c) show cry its site_c peer ipsec
(d) entry packet - trace within the icmp 10.5.2.15 8 0 10.205.2.130 detail
(e) see the crypto ipsec his
At the same time, please.
Let me know how it goes.
Thank you
Portu.
Please note all useful posts
-
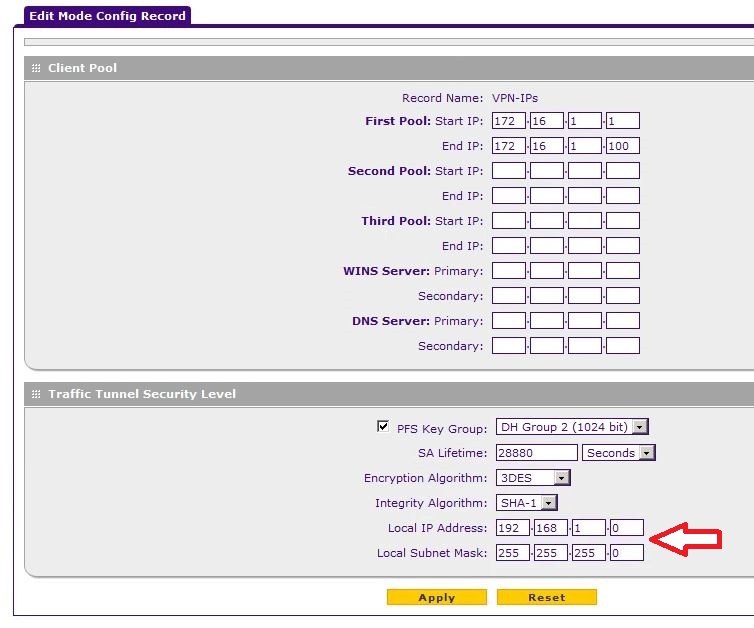
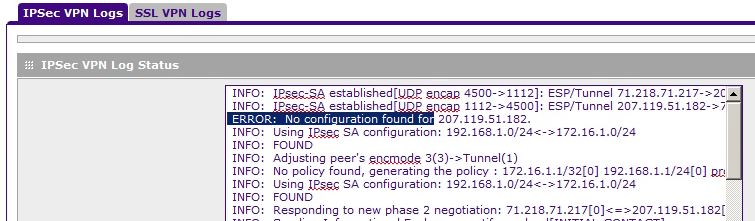
SRX5308 IPsec Config Mode - [IKE] ERROR: no configuration is found for...
I have a real simple setup for Client-to-gateway VPN installation. Base tunnels seem to work fine, but when I try to install
a policy of Mode Config I get an error in the connection and cannot ping resources on the local VPN network.
The local IP address at the end of check-in Mode Config is 192.168.1.0. The manual says to leave the field empty and it will default to the address of the gateway, which is 192.168.1.1. If I leave the field blank this wrong address gets automatically enrolled and if I try to manually enter the right one I get an error saying it's an invaild address?
Then when I connect, I get the following error:
I think that is the question. How to work around this problem or do it properly? The manual is not any help and I googled my old brian dead.
Thanks for any idea that you can give me!
CC
Thanks for the reply okadis and thanks for the link to this site, it is very useful!
I was able to find a solution. Turns out that the works of very good firewall configuration. All I had to do was use the remote configuration of the CLIENT as the LAN address 192.168.1.0, and then everything worked.
Now, for me, it's 2 "bugs" in the SRX5308 of Mode Config record:
1 192.168.1.0 is not the address of the Local network subnet, it is 192.168.1.1; The manual says if left blank by default subnet LAN, which it isn't, it's default 192.168.1.0
2. it won't let you enter ANY ip address here. It must be left blank.
Maybe I'm missing something here, but it works perfectly after using what is there in the end customer.
Should have been simple. Well...
CC
-
iPsec gateway to gateway on LRT224, main mode?
Hi, I just got my new Linksys LRT224
I'm new to Linksys, but have used Netgear, D-Link and routers VPN Redfox.
About 20 minutes after conversion unboxing of the LRT224 I have an iPsec tunnel of aggressive mode between my Netgear SRX5308 and the LRT224 work, very impressive I think, well not my performance
 but the ease of LRT224. Very nice interface easy to understand and quick Web. However, I noticed two things so far, 1 I can open only my SRX to the LRT224 tunnel and not vice versa. 2nd I can't get aggressive mode working on LRT224? I do something wrong or does the LRT224 not support the main mode?
but the ease of LRT224. Very nice interface easy to understand and quick Web. However, I noticed two things so far, 1 I can open only my SRX to the LRT224 tunnel and not vice versa. 2nd I can't get aggressive mode working on LRT224? I do something wrong or does the LRT224 not support the main mode?Someone else who tried the main mode?
(there is no check box to select the main mode, but by selecting the name of domain + IP FQDN on local and remote in aggressive mode is not checked)
I normally set up routers like this:
SRX5308 Linksys *.
IKE:
General
Name of the policy = srx5308
Direction = Both
Change Mode = handLocal:
FULL DOMAIN NAME
XXXX.dyndns.orgDistance:
FULL DOMAIN NAME
yyyy.dyndns.orgIKE SA settings:
Encryption algorithm = 3DES
= SHA-1 authentication algorithm
= Pre-shared key authentication method
Pre-shared key = MySharedSecret
The Diffie-Hellman (DH) Group = group 2 (1024 bits)
HIS life (s) = 28800VPN strategy:
Name of the policy = srx5308
Remote endpoint point = yyyy.dyndns.orgSelection of traffic:
Beach = local IP address
Start IP 192.168.2.100 =
End IP = 192.168.2.200Beach = remote IP address
Start IP 192.168.1.100 =
End IP = 192.168.1.200Auto policy settings:
Life expectancy = 28800 seconds
Encryption algorithm = 3DES
= SHA-1 integrity algorithm
PFS = on
Key PFS = DH group 2 (1024 bits)
Selected IKE Policy = srx5308
****************************************************************Are looking for the forum and also my friend google, but so far have not found anything, so I'll keep looking.

Hi Ea > Br
You can try it. Set the parameter to LRT224.
As below:
Configuration of the remote control groups:
Remote security gateway type = IP + authentication with domain nameRemote IP Type group = IP by DNS resolved:
XXXX.dyndns.org
Domain name = xxxx.dyndns.org
The VPN tunnel will be working on the main mode, and you can open tunnel of LRT224 too.
-
Cisco RV220W IPSec VPN problem Local configuration for any config mode
Dear all,
I need help, I am currently evaluating RV220W for VPN usage but I'm stuck with the config somehow, it seems that there is a problem with the Mode-Config?
What needs to be changed or where is my fault?
I have installed IPSec according to the RV220W Administrator's Guide. Client's Mac with Mac Cisco IPSec VPN, I also tried NCP Secure Client.
I have 3 other sites where the config on my Mac works fine, but the Cisco VPN router is not.
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: remote for found identifier "remote.com" configuration
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: application received for the negotiation of the new phase 1: x.x.x.x [500]<=>2.206.0.67 [53056]
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: early aggressive mode.
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received unknown Vendor ID
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received Vendor ID: RFC 3947
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received unknown Vendor ID
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received unknown Vendor ID
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received unknown Vendor ID
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received unknown Vendor ID
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received unknown Vendor ID
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received unknown Vendor ID
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received unknown Vendor ID
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received unknown Vendor ID
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received Vendor ID: draft-ietf-ipsec-nat-t-ike-02
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received Vendor ID: draft-ietf-ipsra-isakmp-xauth-06.txt
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received Vendor ID: CISCO - UNITY
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: received Vendor ID: DPD
2013-03-07 01:55:49: [CiscoFirewall] [IKE] INFO: for 2.206.0.67 [53056], version selected NAT - T: RFC 39472013-03-07 01:55:50: [CiscoFirewall] [IKE] INFO: floating ports NAT - t with peer 2.206.0.67 [52149]
2013-03-07 01:55:50: [CiscoFirewall] [IKE] INFO: NAT - D payload is x.x.x.x [4500]
2013-03-07 01:55:50: [CiscoFirewall] [IKE] INFO: NAT - D payload does not match for 2.206.0.67 [52149]
2013-03-07 01:55:50: [CiscoFirewall] [IKE] INFO: NAT detected: Peer is behind a NAT device
2013-03-07 01:55:50: [CiscoFirewall] [IKE] INFO: request sending Xauth for 2.206.0.67 [52149]
2013-03-07 01:55:50: [CiscoFirewall] [IKE] INFO: ISAKMP Security Association established for x.x.x.x [4500] - 2.206.0.67 [52149] with spi: 1369a43b6dda8a7d:fd874108e09e207e
2013-03-07 01:55:50: [CiscoFirewall] [IKE] INFO: type of the attribute "ISAKMP_CFG_REPLY" from 2.206.0.67 [52149]
2013-03-07 01:55:50: [CiscoFirewall] [IKE] INFO: connection for the user "Testuser".
2013-03-07 01:55:50: [CiscoFirewall] [IKE] INFO: type of the attribute "ISAKMP_CFG_REQUEST" from 2.206.0.67 [52149]
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] WARNING: ignored attribute 5
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] WARNING: attribute ignored 28678
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] ERROR: local configuration for 2.206.0.67 [52149] has no config mode
2013-03-07 01:55:50: [CiscoFirewall] [IKE] WARNING: attribute ignored 28683
2013-03-07 01:56:07: [CiscoFirewall] [IKE] INFO: purged-with proto_id = ISAKMP and spi = 1369a43b6dda8a7d:fd874108e09e207e ISAKMP Security Association.
2013-03-07 01:56:08: [CiscoFirewall] [IKE] INFO: ISAKMP Security Association deleted for x.x.x.x [4500] - 2.206.0.67 [52149] with spi: 1369a43b6dda8a7d:fd874108e09e207e
Hi Mike, the built-in client for MAC does not work with the RV220W. The reason is, the MAC IPSec client is the same as the Cisco VPN 5.x client.
The reason that this is important is that the 5.x client work that on certain small business products include the SRP500 and SA500 series.
I would recommend that you search by using a client VPN as Greenbow or IPSecuritas.
-Tom
Please mark replied messages useful -
EzVPN between Cisco ASA 5505 (with NEM mode) and Ciscoo 881 Roure
Hi friends,
I configured the Cisco ASA 5505 and Cisco router with DMVPN 881. 3 offices works very well but one office remains failure. I did the same configuration for all facilities but this router does not work. Any ideas?
Please find below the exit of 881 router Cisco:
YF2_Tbilisi_router #.
* 4 August 09:31:26.793: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:31:26.793 4 August: ISAKMP (0): increment the count of errors on his, try 4 out 5: retransmit the phase 1
* 4 August 09:31:26.793: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:31:26.793: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:31:26.793 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:31:36.793: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:31:36.793 4 August: ISAKMP (0): increment the count of errors on his, try 5 of 5: retransmit the phase 1
* 4 August 09:31:36.793: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:31:36.793: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:31:36.793 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 09:31:44.929 4 August: ISAKMP: (0): serving SA., its is 88961 B 34, delme is 88961 B 34
* 4 August 09:31:46.793: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:31:46.793 4 August: ISAKMP: (0): the peer is not paranoid KeepAlive.* 09:31:46.793 4 August: ISAKMP: (0): removal of reason ITS status of 'Death by retransmission P1' (I) AG_INIT_EXCH (peer 1.1.1.1)
* 09:31:46.793 4 August: % CRYPTO-6-EZVPN_CONNECTION_DOWN: user (customer) = group = Youth_Facility_2 Server_public_addr = 1.1.1.1
* 4 August 09:31:46.793: ISAKMP:isadb_key_addr_delete: no key for address 1.1.1.1 (root NULL)
* 09:31:46.793 4 August: ISAKMP: (0): removal of reason ITS status of 'Death by retransmission P1' (I) AG_INIT_EXCH (peer 1.1.1.1)
* 09:31:46.793 4 August: ISAKMP: Unlocking counterpart struct 0x8AA90C50 for isadb_mark_sa_deleted(), count 0
* 09:31:46.793 4 August: ISAKMP: delete peer node by peer_reap for 1.1.1.1: 8AA90C50
* 09:31:46.793 4 August: ISAKMP: (0): entry = IKE_MESG_INTERNAL, IKE_PHASE1_DEL
* 09:31:46.793 4 August: ISAKMP: (0): former State = new State IKE_I_AM1 = IKE_DEST_SA* 4 August 09:31:47.805: del_node 2.2.2.2 src dst 1.1.1.1:500 fvrf 0 x 0, ivrf 0 x 0
* 09:31:47.805 4 August: ISAKMP: (0): the peer is not paranoid KeepAlive.* 4 August 09:31:47.805: ISAKMP: (0): profile of THE request is (NULL)
* 09:31:47.805 4 August: ISAKMP: created a struct peer 1.1.1.1, peer port 500
* 09:31:47.805 4 August: ISAKMP: new created position = 0x8AA90C50 peer_handle = 0 x 80004819
* 09:31:47.805 4 August: ISAKMP: lock struct 0x8AA90C50, refcount 1 to peer isakmp_initiator
* 09:31:47.805 4 August: ISAKMP: (0): client configuration parameters 87531228 adjustment
* 09:31:47.805 4 August: ISAKMP: 500 local port, remote port 500
* 09:31:47.805 4 August: ISAKMP: find a dup her to the tree during his B 88961, 34 = isadb_insert call BVA
* 4 August 09:31:47.805: ISAKMP: (0): set up client mode.
* 4 August 09:31:47.805: ISAKMP: (0): built of NAT - T of the seller-rfc3947 ID
* 4 August 09:31:47.805: ISAKMP: (0): built the seller-07 ID NAT - t
* 4 August 09:31:47.805: ISAKMP: (0): built of NAT - T of the seller-03 ID
* 4 August 09:31:47.805: ISAKMP: (0): built the seller-02 ID NAT - t
* 4 August 09:31:47.805: ISKAMP: more send buffer from 1024 to 3072
* 09:31:47.805 4 August: ISAKMP: (0): ITS been pre-shared key and XAUTH authentication using id ID_KEY_ID type
* 09:31:47.805 4 August: ISAKMP (0): payload ID
next payload: 13
type: 11
Group ID: Youth_Facility_2
Protocol: 17
Port: 0
Length: 24
* 09:31:47.805 4 August: ISAKMP: (0): the total payload length: 24
* 09:31:47.809 4 August: ISAKMP: (0): entry = IKE_MESG_FROM_IPSEC, IKE_SA_REQ_AM
* 09:31:47.809 4 August: ISAKMP: (0): former State = new State IKE_READY = IKE_I_AM1* 4 August 09:31:47.809: ISAKMP: (0): Beginner aggressive Mode Exchange
* 4 August 09:31:47.809: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:31:47.809 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:31:57.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:31:57.809 4 August: ISAKMP (0): increment the count of errors on his, try 1 5: retransmit the phase 1
* 4 August 09:31:57.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:31:57.809: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:31:57.809 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:32:07.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:32:07.809 4 August: ISAKMP (0): increment the count of errors on his, try 2 of 5: retransmit the phase 1
* 4 August 09:32:07.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:32:07.809: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:32:07.809 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:32:17.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:32:17.809 4 August: ISAKMP (0): increment the count of errors on his, try 3 of 5: retransmit the phase 1
* 4 August 09:32:17.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:32:17.809: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:32:17.809 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:32:27.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:32:27.809 4 August: ISAKMP (0): increment the count of errors on his, try 4 out 5: retransmit the phase 1
* 4 August 09:32:27.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:32:27.809: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:32:27.809 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:32:37.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:32:37.809 4 August: ISAKMP (0): increment the count of errors on his, try 5 of 5: retransmit the phase 1
* 4 August 09:32:37.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:32:37.809: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:32:37.809 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 09:32:46.793 4 August: ISAKMP: (0): serving SA., his is 872E1504, delme is 872E1504
* 4 August 09:32:47.809: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:32:47.809 4 August: ISAKMP: (0): the peer is not paranoid KeepAlive.* 09:32:47.809 4 August: ISAKMP: (0): removal of reason ITS status of 'Death by retransmission P1' (I) AG_INIT_EXCH (peer 1.1.1.1)
* 09:32:47.809 4 August: % CRYPTO-6-EZVPN_CONNECTION_DOWN: user (customer) = group = Youth_Facility_2 Server_public_addr = 1.1.1.1
* 4 August 09:32:47.809: ISAKMP:isadb_key_addr_delete: no key for address 1.1.1.1 (root NULL)
* 09:32:47.809 4 August: ISAKMP: (0): removal of reason ITS status of 'Death by retransmission P1' (I) AG_INIT_EXCH (peer 1.1.1.1)
* 09:32:47.809 4 August: ISAKMP: Unlocking counterpart struct 0x8AA90C50 for isadb_mark_sa_deleted(), count 0
* 09:32:47.809 4 August: ISAKMP: delete peer node by peer_reap for 1.1.1.1: 8AA90C50
* 09:32:47.809 4 August: ISAKMP: (0): entry = IKE_MESG_INTERNAL, IKE_PHASE1_DEL
* 09:32:47.809 4 August: ISAKMP: (0): former State = new State IKE_I_AM1 = IKE_DEST_SA* 4 August 09:32:48.909: del_node src 2.2.2.2:500 dst 1.1.1.1:500 fvrf 0 x 0, ivrf 0 x 0
* 09:32:48.909 4 August: ISAKMP: (0): the peer is not paranoid KeepAlive.* 4 August 09:32:48.909: ISAKMP: (0): profile of THE request is (NULL)
* 09:32:48.909 4 August: ISAKMP: created a struct peer 1.1.1.1, peer port 500
* 09:32:48.909 4 August: ISAKMP: new created position = 0x8AA90C50 peer_handle = 0 x 80004818
* 09:32:48.909 4 August: ISAKMP: lock struct 0x8AA90C50, refcount 1 to peer isakmp_initiator
* 09:32:48.909 4 August: ISAKMP: (0): client setting Configuration parameters 88C05A48
* 09:32:48.909 4 August: ISAKMP: 500 local port, remote port 500
* 09:32:48.909 4 August: ISAKMP: find a dup her to the tree during the isadb_insert his 87B57D38 = call BVA
* 4 August 09:32:48.909: ISAKMP: (0): set up client mode.
* 4 August 09:32:48.909: ISAKMP: (0): built of NAT - T of the seller-rfc3947 ID
* 4 August 09:32:48.909: ISAKMP: (0): built the seller-07 ID NAT - t
* 4 August 09:32:48.909: ISAKMP: (0): built of NAT - T of the seller-03 ID
* 4 August 09:32:48.909: ISAKMP: (0): built the seller-02 ID NAT - t
* 4 August 09:32:48.909: ISKAMP: more send buffer from 1024 to 3072
* 09:32:48.913 4 August: ISAKMP: (0): ITS been pre-shared key and XAUTH authentication using id ID_KEY_ID type
* 09:32:48.913 4 August: ISAKMP (0): payload ID
next payload: 13
type: 11
Group ID: Youth_Facility_2
Protocol: 17
Port: 0
Length: 24
* 09:32:48.913 4 August: ISAKMP: (0): the total payload length: 24
* 09:32:48.913 4 August: ISAKMP: (0): entry = IKE_MESG_FROM_IPSEC, IKE_SA_REQ_AM
* 09:32:48.913 4 August: ISAKMP: (0): former State = new State IKE_READY = IKE_I_AM1* 4 August 09:32:48.913: ISAKMP: (0): Beginner aggressive Mode Exchange
* 4 August 09:32:48.913: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:32:48.913 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:32:58.913: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:32:58.913 4 August: ISAKMP (0): increment the count of errors on his, try 1 5: retransmit the phase 1
* 4 August 09:32:58.913: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:32:58.913: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:32:58.913 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:33:08.913: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:33:08.913 4 August: ISAKMP (0): increment the count of errors on his, try 2 of 5: retransmit the phase 1
* 4 August 09:33:08.913: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:33:08.913: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:33:08.913 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:33:18.913: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:33:18.913 4 August: ISAKMP (0): increment the count of errors on his, try 3 of 5: retransmit the phase 1
* 4 August 09:33:18.913: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:33:18.913: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:33:18.913 4 August: ISAKMP: (0): sending a packet IPv4 IKE.
* 4 August 09:33:28.913: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH...
* 09:33:28.913 4 August: ISAKMP (0): increment the count of errors on his, try 4 out 5: retransmit the phase 1
* 4 August 09:33:28.913: ISAKMP: (0): transmit phase 1 AG_INIT_EXCH
* 4 August 09:33:28.913: ISAKMP: (0): 1.1.1.1 package sending 500 peer_port 500 (I) my_port AG_INIT_EXCH
* 09:33:28.913 4 August: ISAKMP: (0): sending a packet IPv4 IKE.There is no DMVPN on the SAA. All that you have configured, is not compatible with the ASA or something another DMVPN then. At least debugging shows that there are some EzVPN involved.
The debug version, it seems that there is no communication on UDP/500 possible between devices. Maybe something is blocking who?
-
Hello world
He had to confirm IKE Phase 1
We use port UDP 500
IKE Phase 2, we use ports
ESP - 50
NAT - T UDP 4500
ESP TCP-1000-50
NAT - T UDP 4500
TCP-1000Concerning
Mahesh
IKE phase 1 (main mode/aggressive mode) is udp src and dst 500
Phase 2 of IKE could be:
- Protocol IP 50 (ESP)
- NAT - T is udp src (customer) ephemeral dst (server) udp 4500
- In former VPN clients tcp encapsulation was CBC (customer), ephemeral dst (server) tcp 10000 (10,000 in US) and 10,000 in most of the other countries
-
Pre shared keys used in IKE Phase 1
Hello world
Need to confirm if we use the buttons pre shared during IKE Phase 1 main mode and aggressive mode
Concerning
MAhesh
The pre-shared key is used in both modes of IKE Phase I. With pre-shared keys, the same preshared key is configured on each IPSec peer. IKE peers authenticate each other computer and sending a hash key data that includes the pre-shared key.
-
8.2 ASA failure phase2 ike ipsec
I used the wizard to access remote vpn, IPSEC on an ASA 5510 security + running os version 8.2.
Group: adminsbbs
User: adminuser
When connecting using the client, it says «fixing communications...» "and then it flashes and it is disconnected. Hoping the following debug output to help you will help me, so I didn't enter the config.
What seems to be the cause of failure of the phase 2 of IKE?
Since the ASA device:
asa01 # 29 dec 18:54:16 [IKEv1 DEBUG]: IP = 3.4.249.124, IKE Peer included IKE fragmentation capability flags: Main Mode: real aggressive Mode: false
29 Dec 18:54: 16 [IKEv1]: IP = 3.4.249.124, connection landed on tunnel_group adminsbbs
29 Dec 18:54: 16 [IKEv1 DEBUG]: Group = adminsbbs, IP = 3.4.249.124, IKE SA proposal # 1, transform # 10 entry overall IKE acceptable matches # 1
29 Dec 18:54: 16 [IKEv1]: Group = adminsbbs, IP = 3.4.249.124, status of automatic NAT detection: remote endpoint IS behind a NAT device this end is NOT behind a NAT device
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, (adminuser) user authenticated.
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, transaction mode attribute unhandled received: 5
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs, name of user = adminuser, IP = 3.4.249.124, Type of Client: Mac OS X Client Application Version: 4.9.01 (0100)
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, assigned private IP 172.16.20.1 remote user address
29 Dec 18:54: 26 [IKEv1 DEBUG]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, fast Mode resumed treatment, Cert/Trans Exch/RM IDDM completed
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, PHASE 1 COMPLETED
29 Dec 18:54: 26 [IKEv1]: IP = 3.4.249.124, Keep-alive type for this connection: DPD
29 Dec 18:54: 26 [IKEv1 DEBUG]: Group = adminsbbs, name of user = adminuser, IP = 3.4.249.124, timer to generate a new key to start P1: 82080 seconds.
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, data received in payload ID remote Proxy Host: address 172.16.20.1, protocol 0, Port 0
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs, username = adminuser, IP = 3.4.249.124, received data IP Proxy local subnet in payload ID: address 0.0.0.0 Mask 0.0.0.0, protocol 0, Port 0
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs, name of user = adminuser, IP = 3.4.249.124, QM IsRekeyed its not found old addr
29 Dec 18:54: 26 [IKEv1 DEBUG]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, only Tunnel UDP-encapsulated and UDP-encapsulated-Transport mode NAT-Traversal-defined selection
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, remote peer IKE configured crypto card: outside_dyn_map
29 Dec 18:54: 26 [IKEv1 DEBUG]: Group = adminsbbs, name of user = adminuser, IP = 3.4.249.124, ITS processing IPSec payload
29 Dec 18:54: 26 [IKEv1]: Phase 2 failed: Mismatched types of class attributes Mode of Encapsulation: RRs would be: UDP Tunnel(NAT-T) Cfg would be: Transport UDP
29 Dec 18:54: 26 [IKEv1]: Phase 2 failed: Mismatched types of class attributes Mode of Encapsulation: RRs would be: UDP Tunnel(NAT-T) Cfg would be: Transport UDP
29 Dec 18:54: 26 [IKEv1]: Phase 2 failed: Mismatched types of class attributes Mode of Encapsulation: RRs would be: UDP Tunnel(NAT-T) Cfg would be: Transport UDP
29 Dec 18:54: 26 [IKEv1]: Phase 2 failed: Mismatched types of class attributes Mode of Encapsulation: RRs would be: UDP Tunnel(NAT-T) Cfg would be: Transport UDP
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs, username = adminuser, IP = 3.4.249.124, IPSec security association proposals found unacceptable.
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs, name of user = adminuser, IP = 3.4.249.124, error QM WSF (P2 struct & 0xcca2f140, mess id 0x374db953).
29 Dec 18:54: 26 [IKEv1 DEBUG]: Group = adminsbbs, name of user = adminuser, IP = 3.4.249.124, case of mistaken IKE responder QM WSF (struct & 0xcca2f140)
, : QM_DONE EV_ERROR--> QM_BLD_MSG2 EV_NEGO_SA--> QM_BLD_MSG2, EV_IS_REKEY--> QM_BLD_MSG2, EV_CONFIRM_SA--> QM_BLD_MSG2, EV_PROC_MSG--> QM_BLD_MSG2, EV_HASH_OK--> QM_BLD_MSG2, NullEvent--> QM_BLD_MSG2 EV_COMP_HASH 29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, Removing counterpart of table Correlator has failed, no match!
29 Dec 18:54: 26 [IKEv1]: Group = adminsbbs username = adminuser, IP = 3.4.249.124, Session is be demolished. Reason: Phase 2
29 Dec 18:54: 26 [IKEv1]: ignoring msg SA brand with Iddm 102400 dead because ITS removal
29 Dec 18:54: 26 [IKEv1]: IP = 3.4.249.124, encrypted packet received with any HIS correspondent, drop
The client connection:
Cisco Systems VPN Client Version 4.9.01 (0100)
Copyright (C) 1998-2006 Cisco Systems, Inc. All rights reserved.
Type of client: Mac OS X
Running: Darwin Darwin Kernel Version 10.5.0 10.5.0: Fri Nov 5 23:20:39 PDT 2010. root:XNU-1504.9.17~1/RELEASE_I386 i386
365 19:09:13.384 29/12/2010 Sev = Info/4 CM / 0 x 43100002
Start the login process
366 19:09:13.385 29/12/2010 Sev = WARNING/2 CVPND / 0 x 83400011
Send error - 28 package. ADR DST: 0xAC10D5FF, ADR Src: 0xAC10D501 (DRVIFACE:1158).
367 19:09:13.385 29/12/2010 Sev = WARNING/2 CVPND / 0 x 83400011
Send error - 28 package. ADR DST: 0xAC107FFF, ADR Src: 0xAC107F01 (DRVIFACE:1158).
368 19:09:13.385 29/12/2010 Sev = Info/4 CM / 0 x 43100004
Establish a connection using Ethernet
369 19:09:13.385 12/29/2010 Sev = Info/4 CM / 0 x 43100024
Attempt to connect with the server "1.2.0.14".
370 19:09:13.385 12/29/2010 Sev = Info/4 CVPND / 0 x 43400019
Separation of privileges: binding to the port: (500).
371 19:09:13.387 29/12/2010 Sev = Info/4 CVPND / 0 x 43400019
Separation of privileges: binding to the port: (4500).
372 19:09:13.387 29/12/2010 Sev = Info/6 IKE/0x4300003B
Attempts to establish a connection with 1.2.0.14.
373 19:09:13.471 29/12/2010 Sev = Info/4 IKE / 0 x 43000013
SEND to > ISAKMP OAK AG (SA, KE, NO, ID, VID (Xauth), VID (dpd), VID (Frag), VID(Nat-T), VID (Unity)) at 1.2.0.14
374 19:09:13.538 29/12/2010 Sev = Info/5 IKE/0x4300002F
Received packet of ISAKMP: peer = 1.2.0.14
375 19:09:13.538 29/12/2010 Sev = Info/4 IKE / 0 x 43000014
RECEIVING< isakmp="" oak="" ag="" (sa,="" ke,="" non,="" id,="" hash,="" vid(unity),="" vid(xauth),="" vid(dpd),="" vid(nat-t),="" nat-d,="" nat-d,="" vid(frag),="" vid(?))="" from="">
376 19:09:13.538 29/12/2010 Sev = Info/5 IKE / 0 x 43000001
Peer is a compatible peer Cisco-Unity
377 19:09:13.538 29/12/2010 Sev = Info/5 IKE / 0 x 43000001
Peer supports XAUTH
378 19:09:13.539 29/12/2010 Sev = Info/5 IKE / 0 x 43000001
Peer supports the DPD
379 19:09:13.539 29/12/2010 Sev = Info/5 IKE / 0 x 43000001
Peer supports NAT - T
380 19:09:13.539 29/12/2010 Sev = Info/5 IKE / 0 x 43000001
Peer supports fragmentation IKE payloads
381 19:09:13.622 29/12/2010 Sev = Info/6 IKE / 0 x 43000001
IOS Vendor ID successful construction
382 19:09:13.622 29/12/2010 Sev = Info/4 IKE / 0 x 43000013
SENDING > ISAKMP OAK AG * (HASH, NOTIFY: NAT - D, NAT - D, VID (?), STATUS_INITIAL_CONTACT, VID (Unity)) at 1.2.0.14
383 19:09:13.623 12/29/2010 Sev = Info/6 IKE / 0 x 43000055
Sent a keepalive on the IPSec Security Association
384 19:09:13.623 29/12/2010 Sev = Info/4 IKE / 0 x 43000083
IKE port in use - Local Port = 0 x 1194, Remote Port = 0 x 1194
385 19:09:13.623 29/12/2010 Sev = Info/5 IKE / 0 x 43000072
Automatic NAT detection status:
Remote endpoint is NOT behind a NAT device
This effect is behind a NAT device
386 19:09:13.623 29/12/2010 Sev = Info/4 CM/0x4310000E
ITS established Phase 1. 1 crypto IKE Active SA, 0 IKE SA authenticated user in the system
387 19:09:13.639 29/12/2010 Sev = Info/5 IKE/0x4300002F
Received packet of ISAKMP: peer = 1.2.0.14
388 19:09:13.639 29/12/2010 Sev = Info/4 IKE / 0 x 43000014
RECEIVING< isakmp="" oak="" trans="" *(hash,="" attr)="" from="">
389 19:09:13.639 12/29/2010 Sev = Info/4 CM / 0 x 43100015
Launch application xAuth
390 19:09:13.825 12/29/2010 Sev = Info/4 IPSEC / 0 x 43700008
IPSec driver started successfully
391 19:09:13.825 29/12/2010 Sev = Info/4 IPSEC / 0 x 43700014
Remove all keys
392 19:09:16.465 29/12/2010 Sev = Info/4 CM / 0 x 43100017
xAuth application returned
393 19:09:16.465 29/12/2010 Sev = Info/4 IKE / 0 x 43000013
SEND to > ISAKMP OAK TRANS *(HASH, ATTR) to 1.2.0.14
394 19:09:16.480 29/12/2010 Sev = Info/5 IKE/0x4300002F
Received packet of ISAKMP: peer = 1.2.0.14
395 19:09:16.480 29/12/2010 Sev = Info/4 IKE / 0 x 43000014
RECEIVING< isakmp="" oak="" trans="" *(hash,="" attr)="" from="">
396 19:09:16.481 29/12/2010 Sev = Info/4 IKE / 0 x 43000013
SEND to > ISAKMP OAK TRANS *(HASH, ATTR) to 1.2.0.14
397 19:09:16.481 29/12/2010 Sev = Info/4 CM/0x4310000E
ITS established Phase 1. 1 crypto IKE Active SA, 1 IKE SA authenticated user in the system
398 19:09:16.482 29/12/2010 Sev = Info/4 IKE / 0 x 43000013
SEND to > ISAKMP OAK TRANS *(HASH, ATTR) to 1.2.0.14
399 19:09:16.498 29/12/2010 Sev = Info/5 IKE/0x4300002F
Received packet of ISAKMP: peer = 1.2.0.14
400 19:09:16.498 12/29/2010 Sev = Info/4 IKE / 0 x 43000014
RECEIVING< isakmp="" oak="" trans="" *(hash,="" attr)="" from="">
401 19:09:16.498 29/12/2010 Sev = Info/5 IKE / 0 x 43000010
MODE_CFG_REPLY: Attribute = INTERNAL_IPV4_ADDRESS:, value = 172.16.20.1
402 19:09:16.498 29/12/2010 Sev = Info/5 IKE / 0 x 43000010
MODE_CFG_REPLY: Attribute = INTERNAL_IPV4_NETMASK:, value = 255.255.255.0
403 19:09:16.498 29/12/2010 Sev = Info/5 IKE / 0 x 43000010
MODE_CFG_REPLY: Attribute = INTERNAL_IPV4_DNS (1):, value = 1.2.2.2
404 19:09:16.498 29/12/2010 Sev = Info/5 IKE / 0 x 43000010
MODE_CFG_REPLY: Attribute = INTERNAL_IPV4_DNS (2):, value = 1.2.2.22
405 19:09:16.498 29/12/2010 Sev = Info/5 IKE/0x4300000D
MODE_CFG_REPLY: Attribute = MODECFG_UNITY_SAVEPWD:, value = 0x00000000
406 19:09:16.498 29/12/2010 Sev = Info/5 IKE/0x4300000D
MODE_CFG_REPLY: Attribute = MODECFG_UNITY_SPLIT_INCLUDE (# of split_nets), value = 0 x 00000003
407 19:09:16.498 12/29/2010 Sev = Info/5 IKE/0x4300000F
SPLIT_NET #1
subnet 10.10.10.0 =
mask = 255.255.255.0
Protocol = 0
SRC port = 0
port dest = 0
408 19:09:16.498 29/12/2010 Sev = Info/5 IKE/0x4300000F
SPLIT_NET #2
subnet = 1.2.31.0
mask = 255.255.255.0
Protocol = 0
SRC port = 0
port dest = 0
409 19:09:16.498 29/12/2010 Sev = Info/5 IKE/0x4300000F
SPLIT_NET #3
subnet = 1.2.8.0
mask = 255.255.255.0
Protocol = 0
SRC port = 0
port dest = 0
410 19:09:16.498 29/12/2010 Sev = Info/5 IKE/0x4300000D
MODE_CFG_REPLY: Attribute = MODECFG_UNITY_PFS:, value = 0x00000000
411 19:09:16.499 29/12/2010 Sev = Info/5 IKE/0x4300000E
MODE_CFG_REPLY: Attribute = APPLICATION_VERSION, value = Cisco Systems, Inc. ASA5510 Version 8.2 (2) built by manufacturers on Tuesday, January 11, 10 14:19
412 19:09:16.499 29/12/2010 Sev = Info/5 IKE/0x4300000D
MODE_CFG_REPLY: Attribute = received and by using the NAT - T port number, value = 0 x 00001194
413 19:09:16.499 29/12/2010 Sev = Info/4 CM / 0 x 43100019
Data in mode Config received
414 19:09:16.500 29/12/2010 Sev = Info/4 IKE / 0 x 43000056
Received a request from key driver: local IP = 192.168.0.103, GW IP = 1.2.0.14, Remote IP = 0.0.0.0
415 19:09:16.500 2010-12-29 Sev = Info/4 IKE / 0 x 43000013
SEND to > ISAKMP OAK QM * (HASH, SA, NO, ID, ID) to 1.2.0.14
416 19:09:16.517 29/12/2010 Sev = Info/5 IKE/0x4300002F
Received packet of ISAKMP: peer = 1.2.0.14
417 19:09:16.517 29/12/2010 Sev = Info/4 IKE / 0 x 43000014
RECEIVING< isakmp="" oak="" info="" *(hash,="" notify:status_resp_lifetime)="" from="">
418 19:09:16.517 29/12/2010 Sev = Info/5 IKE / 0 x 43000045
Answering MACHINE-LIFE notify has value of 86400 seconds
419 19:09:16.517 29/12/2010 Sev = Info/5 IKE / 0 x 43000047
This SA has been alive for 3 seconds, affecting seconds expired 86397 now
420 19:09:16.518 12/29/2010 Sev = Info/5 IKE/0x4300002F
Received packet of ISAKMP: peer = 1.2.0.14
421 19:09:16.518 12/29/2010 Sev = Info/4 IKE / 0 x 43000014
RECEIVING< isakmp="" oak="" info="" *(hash,="" notify:no_proposal_chosen)="" from="">
422 19:09:16.518 29/12/2010 Sev = Info/4 IKE / 0 x 43000013
SEND to > ISAKMP OAK INFO *(HASH, DEL) to 1.2.0.14
423 19:09:16.518 29/12/2010 Sev = Info/4 IKE / 0 x 43000049
IPsec security association negotiation made scrapped, MsgID = FCB95275
424 19:09:16.518 29/12/2010 Sev = Info/4 IKE / 0 x 43000017
Marking of IKE SA delete (I_Cookie = 4BEBFA4F685D02E9 R_Cookie = 6A6CB439CD58F148) reason = DEL_REASON_IKE_NEG_FAILED
425 19:09:16.520 29/12/2010 Sev = Info/5 IKE/0x4300002F
Received packet of ISAKMP: peer = 1.2.0.14
426 19:09:16.520 29/12/2010 Sev = Info/4 IKE / 0 x 43000058
Received an ISAKMP for a SA message no assets, I_Cookie = 4BEBFA4F685D02E9 R_Cookie = 6A6CB439CD58F148
427 19:09:16.520 29/12/2010 Sev = Info/4 IKE / 0 x 43000014
RECEIVING< isakmp="" oak="" info="" *(dropped)="" from="">
428 19:09:17.217 29/12/2010 Sev = Info/4 IPSEC / 0 x 43700014
Remove all keys
429 19:09:19.719 29/12/2010 Sev = Info/4 IKE/0x4300004B
IKE negotiation to throw HIS (I_Cookie = 4BEBFA4F685D02E9 R_Cookie = 6A6CB439CD58F148) reason = DEL_REASON_IKE_NEG_FAILED
430 19:09:19.719 29/12/2010 Sev = Info/4 CM / 0 x 43100012
ITS phase 1 deleted before first Phase 2 SA is caused by "DEL_REASON_IKE_NEG_FAILED". Crypto 0 Active IKE SA, 0 IKE SA authenticated user in the system
431 19:09:19.719 29/12/2010 Sev = Info/5 CM / 0 x 43100025
Initializing CVPNDrv
432 19:09:19.719 29/12/2010 Sev = Info/4 CVPND/0x4340001F
Separation of privileges: restore MTU on the main interface.
433 19:09:19.719 29/12/2010 Sev = Info/4 IKE / 0 x 43000001
Signal received IKE to complete the VPN connection
434 19:09:20.719 29/12/2010 Sev = Info/4 IPSEC / 0 x 43700014
Remove all keys
435 19:09:20.719 29/12/2010 Sev = Info/4 IPSEC / 0 x 43700014
Remove all keys
436 19:09:20.719 29/12/2010 Sev = Info/4 IPSEC / 0 x 43700014
Remove all keys
437 19:09:20.719 29/12/2010 Sev = Info/4 IPSEC/0x4370000A
IPSec driver successfully stopped
Hello 3moloz123,
Crypto ipsec transform-set esp-3des esp-md5-hmac TRANS_ESP_3DES_MD5
Crypto ipsec transform-set transit mode TRANS_ESP_3DES_MD5
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
1. the reason why the VPN remote access (RA) couldn't form with success before the passage of TRANS_ESP_3DES_MD5 to ESP_3DES_MD5 is the mode of transport is not supported for RA VPN. You must use Tunnel mode for the processing of IPSec together we must maintain the IP header inside so that, once the package is decapsules and decrypted at the head of IPSec end we can transfer the package.
In the newspapers, you can see this failure
29 Dec 18:54: 26 [IKEv1]: Phase 2 failed: Mismatched types of class attributes Mode of Encapsulation: RRs would be: UDP Tunnel(NAT - T) Cfg had: UDP Transport
Repeat x 4
RRS of transformation all sent by the RA Client. Cfg would be is that the dynamic encryption card supports.
2. the isakmp policy change was unnecessary, the Phase 1 session came fine ISAKMP indicating worked. Phase 2 begins only after a successful Phase 1 (session ISAKMP).
After failing to build Phase 2 (child SA) we drop the ISAKMP Security Association since it is not used.
I hope that answers your questions.
Kind regards
Craig
Maybe you are looking for
-
a few days ago he has updated Firefox to update on my computer. Since then, I was in the options to try to change the settings for a number of things. There is no apply / save button in the options pages. In addition, the tab options remains open - i
-
Hi, I am writing a program that needs a break in the loop for. However, I'm using Labview 7.1, and is not a conditional release. If anyone can give me some suggestions, I would appreciate it. Derek
-
ERROR 8, required component (5,0,0)
Help! I get this error continually, the required component is missing or improperly installed. Reinstall the HP Photosmart software that came with your device and try to scan the image. HP Officejet L7680 on Windows XP (wireless connection) 1. I unin
-
Is BlackBerry Z10 possible to sync Outlook Notes?
Hello world We are using Exchange 2003 and BB10 tests at the moment. I got the active BB10 and configuring activesync correctly. Email, calendar, tasks, contacts are working properly, but only the Notes could not be in sync to the BB10. Im not sure
-
Large enough string - what is the best way to apply
Hi guys,. I have user agreement which is about 1300 characters, could someone please tell me the best way to store and retrieve? and also view it. I don't want to cramp, the memory of the blackberry. I build on the JDE version 4.5. Thanks in advance.