RVI042 - max # of supported gw to gw vpn tunnels?
What is the number taken gw to gw vpn tunnels max supported? What would you recommend for the remote router - MD1 / 1 phone? Modem cable, most likely.
RV042 supports 50 Gw-2-Gw tunnels. With respect to the remote sites, you might consider WRV210 for its Wi - Fi, VPN and a lower cost. However, in a site remote using RV042 provides an option for redundant internet connection.
Tags: Cisco Support
Similar Questions
-
Cisco RV110W supports up to 1 VPN policies
Best regards
I use a router Cisco RV110W to 20 natoinwide of branches with a central site for interconnection, however, although VPN correctly between a branch and the central location it is not possible to add another tunnel in the RV110W to another secondary site (see photo)
In the data sheet RV110W it is said that this router supports up to 5 VPN tunnels, but apparently these 5 tunnels are supposed to establish via the software QuickVPN from a computer.
so: is there a real limit to VPN site to site (router to router) 1 with RV110W?
Thanks in advance for any help!
Please contact Cisco,
The RV110w supports only 1 site to tunnel
Of the data sheet:
1 tunnel IPSec Site to Site
The RV130W will allow 10 site to site tunnels, datasheet below:
http://www.Cisco.com/c/en/us/products/collateral/routers/small-business-...
Best regards
-
RV016 split support VPN tunnel?
I read a rumor that the RV016 does not support split VPN tunnels.
See here:
My understanding is that on my router RV042 VPN tunnels will send internet traffic to the local gateway and send the traffic through the VPN tunnel only if they are intended for the remote subnet. It is my understanding of the "split tunnel".
Is it not true with the RV016?
Your understanding on split tunnel is correct. RV016 behaves like RV042 in this regard.
-
Support for ASA5506X to VPN3020 VPN Tunnel
Hello
our client uses an old VPN3020 hub in their headquarters and several ASA 5505 in branches which maintain VPN tunnels to the hub. As the 5505 is EoS since 2013 they are seeking another feature for the new branches that will be able to work with the 3020. We wonder if ASA 5506 X would be a support. I couldn't find any reference that specifies this configuration being supported. If not, what would be an alternative care? (.. .and replacing the VPN3k is not an option ;-))
Thanks & best regards Frank.
The VPN3k uses IPsec IKEv1, which is supported by the ASA 5506.
The ASA 5505 is not yet EOS and also not EOL. For sure the 5506-X is a much better platform, but keeping a safety device (3 k) that * is * EOL and saw no updates for the years connected to the internet does not seem a really brilliant idea... ;-)
-
VPN tunnel upward, but no traffic?
I decided to take a Cisco 1800 series router and try to put in place. Up to now I can get out, and everything seems fine. I then tried to configure a VPN tunnel between this router and a sonicwall router secure.
Now the problem is the GUI of SonicWall and Cisco say that this tunnel is mounted. But I can't access internal networks...
So my cisco LAN is 192.168.11.0 255.255.255.0
and the Sonic Wall is 192.168.1.0 255.255.255.0
They can talk even if the tunnel is up. I was hitting my head, and running through the tutorials and just can not understand.
Here's proof that we have achieved at least the first phase:
inbound esp sas:
spi: 0xD1BC1B8E(3518765966)
transform: esp-256-aes esp-sha-hmac ,
in use settings ={Tunnel, }
conn id: 3003, flow_id: FPGA:3, crypto map: vpn
sa timing: remaining key lifetime (k/sec): (4541007/2298)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVEoutbound esp sas:
spi: 0xAE589C1E(2925042718)
transform: esp-256-aes esp-sha-hmac ,
in use settings ={Tunnel, }
conn id: 3004, flow_id: FPGA:4, crypto map: vpn
sa timing: remaining key lifetime (k/sec): (4541027/2297)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVE
So here's my config: (what Miss me?)
Current configuration : 3972 bytes
!
version 12.4 no service pad
service tcp-keepalives-in service tcp-keepalives-out
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname CompsysRouter
!
boot-start-marker
boot-end-marker
!
enable secret *****************
enable password ***********
!
aaa new-model
!
!
!
aaa session-id common
ip cef
!
!
!
!
no ip domain lookup
ip domain name ********.local
ip inspect name myfw http timeout 3600 ip inspect name myfw tcp timeout 3600 ip inspect name myfw udp timeout 3600 ip inspect name myfw dns timeout 3600 ip auth-proxy max-nodata-conns 3 ip admission max-nodata-conns 3 !
!
crypto pki trustpoint TP-self-signed-1821875492 enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certificate-1821875492 revocation-check none
rsakeypair TP-self-signed-1821875492 !
!
crypto pki certificate chain TP-self-signed-1821875492 certificate self-signed 01 30820245 308201AE A0030201 02020101 300D0609 2A864886 F70D0101 04050030
31312F30 2D060355 04031326 494F532D 53656C66 2D536967 6E65642D 43657274
69666963 6174652D 31383231 38373534 3932301E 170D3130 31323130 32333433
35325A17 0D323030 31303130 30303030 305A3031 312F302D 06035504 03132649
4F532D53 656C662D 5369676E 65642D43 65727469 66696361 74652D31 38323138
37353439 3230819F 300D0609 2A864886 F70D0101 01050003 818D0030 81890281
8100CC57 E44AB177 3594C4C7 E88B1A4F CE4FD392 87CDB75C 2A6A6B1A 87D10791
0134F1FC 54A84BB6 08A40213 35B9DD0A FD813D2F 1C778D01 3F8EBEB0 C4793850
F52F7906 FDBC56A5 A4829AC5 4180DDA7 F54E3AAD DD1D4537 F1F19F11 9AE8A8A0
91C98934 233CF608 1447DA83 41B09E55 4A0FF674 8D060945 07D3F3F9 8EA7B412
5FD30203 010001A3 6D306B30 0F060355 1D130101 FF040530 030101FF 30180603
551D1104 11300F82 0D436F6D 70737973 526F7574 6572301F 0603551D 23041830
168014DC A9938F71 7CCF0E6D 8BC5DFA5 033DD7E4 0F605130 1D060355 1D0E0416
0414DCA9 938F717C CF0E6D8B C5DFA503 3DD7E40F 6051300D 06092A86 4886F70D
01010405 00038181 00148C2F AA7CA155 463B56F2 324FE1ED 3682E618 75E3048F
93E1EA61 3305767A FA93567B AA93B107 83A2F3D6 8F773779 E6BF0204 DC71879A
5F7FC07F 627D8444 48781289 7F8DC06A BC9057B1 4C72AE1F B64284BE 94C6059C
7B6B8A5D 83375B86 3054C760 961E8763 91767604 5E0E0CE3 3736133A E51ACF26
14F3C7C5 60E08BE3 88 quit
username jdixon secret 5 $*****************
!
!
ip ssh time-out 60 ip ssh authentication-retries 2 !
!
crypto isakmp policy 1 encr aes 256 authentication pre-share
group 2 lifetime 28800 crypto isakmp key address !
!
crypto ipsec transform-set compsys esp-aes 256 esp-sha-hmac
!
crypto map vpn 10 ipsec-isakmp
set peer set transform-set compsys
match address 101 !
!
!
interface FastEthernet0/0
ip address "LOCAL ROUTER OUTSIDE" 255.255.255.248 ip access-group Inbound in ip nat outside
ip inspect myfw out
ip virtual-reassembly
duplex auto
speed auto
no keepalive
crypto map vpn
!
interface FastEthernet0/1
ip address 192.168.11.1 255.255.255.0 ip nat inside
ip virtual-reassembly
duplex auto
speed auto
!
ip forward-protocol nd
ip route 0.0.0.0 0.0.0.0 !
!
ip http server
ip http authentication local
ip http secure-server
ip nat inside source list 1 interface FastEthernet0/0 overload
ip nat inside source static tcp 192.168.11.55 3389 interface FastEthernet0/0 9999 !
ip access-list extended Inbound
permit icmp any any
permit gre host "REMOTE ROUTER" host "LOCAL ROUTER" permit esp host "REMOTE ROUTER" host "LOCAL ROUTER" permit udp host "REMOTE ROUTER" host "LOCAL ROUTER" eq isakmp
permit ahp host "REMOTE ROUTER" host "LOCAL ROUTER" permit udp host "REMOTE ROUTER" host "LOCAL ROUTER" eq non500-isakmp
permit ip host "REMOTE ROUTER" any
permit tcp any host "LOCAL ROUTER" eq 22 !
access-list 1 permit 192.168.11.0 0.0.0.255 access-list 101 permit ip 192.168.11.0 0.0.0.255 192.168.1.0 0.0.0.255 !
!
!
!
control-plane
!
!
!
line con 0 line aux 0 line vty 0 4 !
scheduler allocate 20000 1000 endNAT exemption is where it is a failure.
Please kindly change to as follows:
access-list 150 deny ip 192.168.11.0 0.0.0.255 192.168.1.0 0.0.0.255
access-list 150 permit ip 192.168.11.0 0.0.0.255 any
IP nat inside source list 150 interface fastethernet0/0 overload
no nat ip within the source list 1 interface fastethernet0/0 overload
Hope that helps.
-
I need to establish a vpn connection between my office and a computer over the internet, allowing access to the internal of the outside lan. I have a problem with my router and I am looking for a new.
Can I use x 3500 to establish a pptp vpn tunnel or it can work only as vpn passthrough?
This modem/router supports VPN passthrough for IPSec, PPTP and L2TP only. Try VPN Linksys Gigabit routers like the series of the LRT.
-
RV042 VPN tunnel with Samsung Ubigate ibg2600 need help
Hi all, ok before I completely remove all of my hair, I thought stop by here and ask the volume for you all with the hope that someone can track down the problem.
In short I am configuring a 'Gateway to gateway' vpn tunnel between two sites, I don't have access to the config of the router from Samsung, but the ISPS making sure that they followed my setup - watching newspapers RV042, I don't however see the reason for the failure - im no expert vpn...
Sorry if the log file turns on a bit, I didn't know where the beginning and the end was stupid I know... any advice would be greatly welcomed lol.
System log
Current time: Fri Sep 2 03:37:52 2009 all THE Log Log Log Log VPN Firewall Access system
Time
Type of event Message
2 sep 03:36:01 2009 value of VPN Log [Tunnel negotiation Info] Inbound SPI = c3bdba08
2 sep 03:36:01 2009 value of outbound SPI VPN Log [Tunnel negotiation Info] = c664c1ca
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation Info] > initiator send fast Mode 3rd package
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation Info] Quick Mode Phase 2 SA established, IPSec Tunnel connected
2 sep 03:36:02 2009 VPN journal Dead Peer Detection start, DPD delay = timeout = 10 sec 10 sec timer
2 sep 03:36:02 2009 VPN received log delete SA payload: ISAKMP State #627 removal
2 sep 03:36:02 2009 VPN Log Main Mode initiator
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation Info] > Send main initiator Mode 1 package
2 sep 03:36:02 2009 charge of VPN journal received Vendor ID Type = [Dead Peer Detection]
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation of Info]< initiator="" received="" main="" mode="" 2nd="" packet="">
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation Info] > initiator send Mode main 3rd package
2 sep 03:36:03 2009 VPN Log [Tunnel negotiation of Info]< initiator="" received="" main="" mode="" 4th="" packet="">
2 sep 03:36:03 2009 Log [Tunnel negotiation Info] VPN > main initiator Mode to send 5 packs
2 sep 03:36:03 2009 Log [Tunnel negotiation Info] VPN > initiator receive hand Mode 6 Pack
2 sep 03:36:03 2009 log VPN main mode peer ID is ID_IPV4_ADDR: '87.85.xxx.xxx '.
2 sep 03:36:03 2009 Log [Tunnel negotiation Info] VPN Mode main Phase 1 SA established
2 sep 03:36:03 2009 log VPN [Tunnel negotiation Info] initiator Cookies = c527 d584 595 c 2c3b
2 sep 03:36:03 2009 log VPN [Tunnel negotiation Info] responder Cookies = b62c ca31 1a5f 673f
2 sep 03:36:03 2009 log quick launch Mode PSK VPN + TUNNEL + PFS
2 sep 03:36:03 2009 Log [Tunnel negotiation Info] VPN > initiator send fast Mode 1 package
2 sep 03:36:04 2009 VPN Log [Tunnel negotiation of Info]< initiator="" received="" quick="" mode="" 2nd="" packet="">
2 sep 03:36:04 2009 value of VPN Log [Tunnel negotiation Info] Inbound SPI = c3bdba09
2 sep 03:36:04 2009 value of outbound SPI VPN Log [Tunnel negotiation Info] = e3da1469
2 sep 03:36:04 2009 VPN Log [Tunnel negotiation Info] > initiator send fast Mode 3rd package
2 sep 03:36:04 2009 VPN Log [Tunnel negotiation Info] Quick Mode Phase 2 SA established, IPSec Tunnel connected
2 sep 03:36:04 2009 VPN journal Dead Peer Detection start, DPD delay = timeout = 10 sec 10 sec timer
2 sep 03:36:05 2009 VPN received log delete SA payload: ISAKMP State #629 removalPFS - off on tada and linksys router does not support the samsung lol! connected!

-
VPN connected, stream out of VPN tunnel
I mean that we have in place of the VPN Sites manage to sites with 2 RV042 router but it seams not as I wanted. Are you sure that each transfer of data through Router 2 will go into the VPN tunnel or it shuts down the VPN tunnel. I checked the routing table and saw that:
Sources mask Gateway Interface
2 1 or wan wan IP 255.255.255.0 ipsec0 private
By default 0.0.0.0 (ip wan 1 or 2) wan1 or wan2
.........
So what you think what sense data will pass through the line, it will go through the ipsec section or through wan1 or wan2. Ofcouse each data will pass through wan1 or wan2, but it can go inside the ipsec tunnel or ipsec outside tunnel. If she goes inside the ipsec tunnel, everything is ok, but if this isn't the case, transfer of unsecured data. I'm trying to access some website is not in private ip and it was outside ipsec tunnel go, I can capture and now that you have access.
Why with linksys have 2 work as draytek product even photos follow:
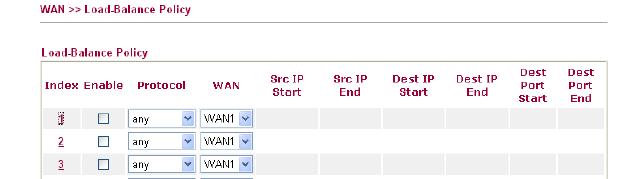
Can someone help me to answer this question, thank you for your attention
1. it depends on what the tunnels of your business allows. As I've written before, there are other protocols that allows you to route traffic through the VPN tunnel. Only IPSec cannot do this. For example, if your company uses GRE over IPSec then they can route traffic through their tunnels. Your RV does not support this.
2. If it's really plain IPSec then you cannot configure several subnets. You can try to implement the security group remote as a subnet more grand, such as 10.0.0.0/8. Of course the groups must match on both sides.
3. If you want to route all traffic through the tunnel, and then try to set the local/remote security to 0.0.0.0/0.0.0.0 group. Maybe it works.
The configuration of IPSec in the RV042 does not allow extremely complex configurations. It's mainly to connect two subnets between them.
-
Routing access to Internet through an IPSec VPN Tunnel
Hello
I installed a VPN IPSec tunnel for a friend's business. At his desk at home, I installed a Cisco SA520 and at it is remote from the site I have a Cisco RVS4000. The IPSec VPN tunnel works very well. The remote site, it can hit all of its workstations and peripheral. I configured the RVS4000 working in router mode as opposed to the bridge. In the Home Office subnet is 192.168.1.0/24 while the subnet to the remote site is 192.168.2.0/24. The SA520 is configured as Internet gateway for the headquarters to 192.168.1.1. The remote desktop has a gateway 192.168.2.1.
I need to configure the remote site so that all Internet traffic will be routed via the Home Office. I have to make sure that whatever it is plugged into the Ethernet on the RVS4000 port will have its Internet traffic routed through the Internet connection on the SA520. Currently I can ping any device on the headquarters of the remote desktop, but I can't ping anything beyond the gateway (192.168.1.1) in the Home Office.
Any help would be greatly appreciated.
Thank you.
Hi William, the rvs4000 does not support the tunnel or esp transfer wild-card.
-
RV110W replaces WRV210. IPsec VPN tunnel between them?
I have a VPN between two locations using WRV210s at the end of work. Now, I want to replace a 210 with a new RV110W. Can I get both to work together? The config is quite different.
Rod, the rv110w must be on the latest version of the software. The original version firmware did not support site to site vpn.
Site of the tunnel to the other, simply to match the parameters. If you need help with this, you can call the support center, make sure you have access to the pages of each router configuration.
-Tom
Please evaluate the useful messages -
VPN Tunnel problem. external interface has private IP
Hi all
I don't know if it is wired or not!
When our ISP provide us an Internet connection our real IP is configured on the ethernet interface, while the serial interfaces have a private IP address.
The problem here is when I'm trying to configure a VPN tunnel to another router.
Anything in the configuration is smooth, except for the part where I put the serial interface is my outside.
The tunnel is still low coz the IP address will be my private (serial interface) during the configuration on the router counterpart is my public IP address.
So I am woundering is there a way I can force the VPN tunnel to take the IP address configured on the side LAN? Or any other work around?
Building configuration...
Current configuration: 2372 bytes
!
version 12.4
horodateurs service debug datetime msec
Log service timestamps datetime msec
no password encryption service
!
boot-start-marker
start the flash c1841-advsecurityk9 - mz.124 - 23.bin system
boot-end-marker
!
property intellectual auth-proxy max-nodata-& 3
property intellectual admission max-nodata-& 3
!
crypto ISAKMP policy 1
BA 3des
preshared authentication
Group 2
!
crypto ISAKMP policy 2
BA 3des
md5 hash
preshared authentication
Group 2
isakmp encryption key * address 144.254.x.y
!
!
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
!
map SDM_CMAP_1 1 ipsec-isakmp crypto
Description Tunnel to144.254.x.y
the value of 144.254.x.y peer
game of transformation-ESP-3DES-SHA
match address VPN_Traffic
!
!
!
interface FastEthernet0/0
address IP 10.55.218.1 255.255.255.0 secondary (My internal subnet)
IP address 196.219.a.b 255.255.255.224 (my public IP)
IP nat inside
IP virtual-reassembly
automatic duplex
automatic speed
No keepalive
!
interface FastEthernet0/1
no ip address
automatic duplex
automatic speed
!
interface Serial0/0/0
no ip address
frame relay IETF encapsulation
frame-relay lmi-type q933a
!
point-to-point interface Serial0/0/0.16
IP 172.16.133.2 255.255.255.252
NAT outside IP
IP virtual-reassembly
SNMP trap-the link status
dlci 16 frame relay interface
map SDM_CMAP_1 crypto
!
interface Serial0/0/1
no ip address
frame relay IETF encapsulation
ignore the dcd
frame-relay lmi-type q933a
!
point-to-point interface Serial0/0/1.16
IP 172.16.134.2 255.255.255.252
NAT outside IP
IP virtual-reassembly
SNMP trap-the link status
dlci 16 frame relay interface
map SDM_CMAP_1 crypto
!
IP forward-Protocol ND
IP route 0.0.0.0 0.0.0.0 Serial0/0/1.16
IP route 0.0.0.0 0.0.0.0 Serial0/0/0.16
!
VPN_Traffic extended IP access list
Note Protect traffic Local to any Destination subnet
Remark SDM_ACL = 4 category
IP 10.55.218.0 allow 0.0.0.255 any
!
Scheduler allocate 20000 1000
end
This should do the trick.
map SDM_CMAP_1 crypto local-address FastEthernet0/0
See you soon
-
2 separated on same ASA VPN tunnels can communicate with each other
Here's the scenario that I have a VPN tunnel with one of my remote locations. I also have a VPN Tunnel with a provider that supports the equipment for my organization. I need to have my supplier able to communicate with equipment that live in my other VPN tunnel. The two Tunnels are on the same ASA5540.
1 is it Possible?
2 How set it up?
Thank you
Follow this link for example. Enhanced spoke-to-spoke VPN, allows the two tunnels ending to your asa5540 to connect, using parameter permit intra-interface with configuration accless-list permits traffic of each endpoint of the tunnel.
-
Authentication of ACS in the VPN tunnel
We want to enable the ACS authentication to connect to different routers (Cisco 881 s) we have obtained who are communicating with our WAN via VPN tunnels. We want to avoid using public IP of the router to communicate and pass information to user/password with the ACS server and rely on the IP of the server private instead. The problem is that external interfaces of the router connect to the Internet using public IP addresses and when the router wishes to communicate with the ACS server it will use its IP of the interface to the public and which will fail. We can ping on the server of course when we set the source to the internal LAN IP.
The question is are there any way to have the router contact ACS through the VPN tunnel using a private IP address?
config is used and tested with success on local equipment:
AAA new-model
RADIUS-server host 10.x.x.x single-connection key xxxxxx
AAA authentication login Ganymede-local group local Ganymede
AAA authorization commands x Ganymede-local group Ganymede + if authenticated
AAA authorization exec Ganymede-local group Ganymede + authenticated if
See the establishment of privileges exec level x
line vty 0 4
Ganymede-local authentication login
authorization controls Ganymede-local x
-ACS ping to the router (WAN via VPN connection) when using public IP address of the router as the source address:
RT881 #ping 10.x.x.x
Type to abort escape sequence.
Send 5, echoes ICMP 100 bytes to 10.x.x.x, time-out is 2 seconds:
.....
Success rate is 0% (0/5)
-ACS ping to the router (WAN via VPN connection) when using IP private of the LAN as source address:
RT881 #ping source 10.x.x.1 10.x.x.x
Type to abort escape sequence.
Send 5, echoes ICMP 100 bytes to 10.x.x.x, time-out is 2 seconds:
Packet sent with a source address of 10.x.x.1
!!!!!
Success rate is 100 per cent (5/5), round-trip min/avg/max = 72/72/76 ms
Looking forward to your responses and suggestions.
Thanks, M.
Hey Maher,
You can use the command 'Ganymede-source interface ip' or 'RADIUS source-interface ip' for your scenario.
I hope this helps!
Kind regards
Assia
-
IPSEC VPN tunnel on issue of Zonebased Firewall
Help, please!
I'm trying to configure a router lab ISR1921 to build the VPN tunnel with vmware vshield edge. The configuration of the 1921 is pasted below. There is not a lot of adjustment on the side of vshield really and I'm sure both sides are adapting to phase 1 & 2.
The question I have: the tunnel can be built correctly and I also see from show crypto ipsec release encap and decap counters. However the devices on each side can communicate. That said, I can ping from 1921 to the IP of the internal interface of the vshield with IP source specified. But just no communication part and other...
I did debugs and only "error" messages are:
01:58:03.193 20 February: ISAKMP: (1001): error suppression node 1656104565 FALSE reason 'informational (in) State d1.
...
01:58:03.193 20 February: ISAKMP: (1001): purge the node-1657220080
I hope that I did a stupid thing to configure error, but I spent too much time on it. It is supposed to be a really simple installation... Please help!
!
version 15.4
horodateurs service debug datetime msec
Log service timestamps datetime msec
no password encryption service
!
Lab-1900 host name
!
boot-start-marker
boot system flash: c1900-universalk9-mz. Spa. 154 - 1.T1.bin
boot system flash: c1900-universalk9-mz. Spa. 151 - 4.M7.bin
boot system flash: c1900-universalk9-mz. Spa. 150 - 1.M4.bin
boot-end-marker
!
AAA new-model
!
AAA authentication login default local
authorization AAA console
AAA authorization exec default local
!
AAA - the id of the joint session
clock timezone AST - 4 0
clock to summer time recurring ADT 3 Sun Mar 2 Sun Nov 02:00 02:00
!
DHCP excluded-address IP 192.168.100.1 192.168.100.40
!
dhcp DHCPPOOL IP pool
import all
network 192.168.100.0 255.255.255.0
LAB domain name
DNS 8.8.8.8 Server 4.2.2.2
default router 192.168.100.1
4 rental
!
Laboratory of IP domain name
8.8.8.8 IP name-server
IP-server names 4.2.2.2
inspect the IP log drop-pkt
IP cef
No ipv6 cef
!
type of parameter-card inspect global
Select a dropped packet newspapers
Max-incomplete 18000 low
20000 high Max-incomplete
Authenticated MultiLink bundle-name Panel
!
redundancy
!
property intellectual ssh version 2
!
type of class-card inspect entire game ESP_CMAP
match the name of group-access ESP_ACL
type of class-card inspect the correspondence SDM_GRE_CMAP
match the name of group-access GRE_ACL
type of class-card inspect entire game PAC-cls-icmp-access
match icmp Protocol
tcp protocol match
udp Protocol game
type of class-card inspect correspondence sdm-cls-VPNOutsideToInside-13
game group-access 154
class-card type check ALLOW-VPN-TRAFFIC-OUT match-all
match the ALLOW-VPN-TRAFFIC-OUT access group name
type of class-card inspect entire game PAC-cls-insp-traffic
match Protocol pptp
dns protocol game
ftp protocol game
https protocol game
match icmp Protocol
match the imap Protocol
pop3 Protocol game
netshow Protocol game
Protocol shell game
match Protocol realmedia
match rtsp Protocol
smtp Protocol game
sql-net Protocol game
streamworks Protocol game
tftp Protocol game
vdolive Protocol game
tcp protocol match
udp Protocol game
http protocol game
type of class-card inspect entire game AH_CMAP
match the name of group-access AH_ACL
inspect the class-map match ALLOW VPN TRAFFIC type
match the ALLOW-VPN-TRAFFIC-OUT access group name
type of class-card inspect correspondence ccp-invalid-src
game group-access 126
type of class-card inspect entire game PAC-insp-traffic
corresponds to the class-map PAC-cls-insp-traffic
type of class-card inspect entire game SDM_VPN_TRAFFIC
match Protocol isakmp
match Protocol ipsec-msft
corresponds to the AH_CMAP class-map
corresponds to the ESP_CMAP class-map
type of class-card inspect correspondence ccp-icmp-access
corresponds to the class-ccp-cls-icmp-access card
type of class-card inspect the correspondence SDM_VPN_PT
game group-access 137
corresponds to the SDM_VPN_TRAFFIC class-map
!
type of policy-card inspect self-out-pmap
class type inspect PCB-icmp-access
inspect
class class by default
Pass
policy-card type check out-self-pmap
class type inspect SDM_VPN_PT
Pass
class class by default
Drop newspaper
policy-card type check out-pmap
class type inspect PCB-invalid-src
Drop newspaper
class type inspect ALLOW VPN TRAFFIC OUT
inspect
class type inspect PCB-insp-traffic
inspect
class class by default
Drop newspaper
policy-card type check out in pmap
class type inspect sdm-cls-VPNOutsideToInside-13
inspect
class class by default
Drop newspaper
!
security of the area outside the area
safety zone-to-zone
safety zone-pair zp-self-out source destination outside zone auto
type of service-strategy inspect self-out-pmap
safety zone-pair zp-out-to source out-area destination in the area
type of service-strategy check out in pmap
safety zone-pair zp-in-out source in the area of destination outside the area
type of service-strategy inspect outside-pmap
source of zp-out-auto security area outside zone destination auto pair
type of service-strategy check out-self-pmap
!
crypto ISAKMP policy 1
BA 3des
preshared authentication
Group 2
ISAKMP crypto key iL9rY483fF address 172.24.92.103
!
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
tunnel mode
!
IPSEC_MAP 1 ipsec-isakmp crypto map
Tunnel Sandbox2 description
defined by peer 172.24.92.103
Set security-association second life 28800
game of transformation-ESP-3DES-SHA
PFS group2 Set
match address 150
!
the Embedded-Service-Engine0/0 interface
no ip address
Shutdown
!
interface GigabitEthernet0/0
WAN description
IP 172.24.92.18 255.255.255.0
NAT outside IP
No virtual-reassembly in ip
outside the area of security of Member's area
automatic duplex
automatic speed
No mop enabled
card crypto IPSEC_MAP
Crypto ipsec df - bit clear
!
interface GigabitEthernet0/1
LAN description
IP 192.168.100.1 address 255.255.255.0
IP nat inside
IP virtual-reassembly in
Security members in the box area
automatic duplex
automatic speed
!
IP forward-Protocol ND
!
IP http server
access-class 2 IP http
local IP http authentication
IP http secure server
!
IP nat inside source map route RMAP_4_PAT interface GigabitEthernet0/0 overload
IP route 0.0.0.0 0.0.0.0 172.24.92.254
!
AH_ACL extended IP access list
allow a whole ahp
ALLOW-VPN-TRAFFIC-OUT extended IP access list
IP 192.168.100.0 allow 0.0.0.255 192.168.1.0 0.0.0.255
ESP_ACL extended IP access list
allow an esp
TELNET_ACL extended IP access list
permit tcp any any eq telnet
!
allowed RMAP_4_PAT 1 route map
corresponds to the IP 108
!
1snmp2use RO SNMP-server community
access-list 108 deny ip 192.168.100.0 0.0.0.255 192.168.1.0 0.0.0.255
access-list 108 allow ip 192.168.100.0 0.0.0.255 any
access-list 126 allow the ip 255.255.255.255 host everything
access-list 126 allow ip 127.0.0.0 0.255.255.255 everything
access-list 137 allow ip 172.24.92.0 0.0.0.255 any
access-list 150 permit ip 192.168.100.0 0.0.0.255 192.168.1.0 0.0.0.255
access-list 154 allow ip 192.168.1.0 0.0.0.255 192.168.100.0 0.0.0.255
!
control plan
!
Line con 0
exec-timeout 0 0
Synchronous recording
line to 0
line 2
no activation-character
No exec
preferred no transport
transport output pad rlogin lapb - your MOP v120 udptn ssh telnet
StopBits 1
line vty 0 4
access-class TELNET_ACL in
exec-timeout 0 0
Synchronous recording
transport of entry all
line vty 5 15
access-class TELNET_ACL in
exec-timeout 0 0
Synchronous recording
transport of entry all
!
Scheduler allocate 20000 1000
0.ca.pool.ntp.org server NTP prefer
1.ca.pool.ntp.org NTP server
!
end
NAT looks fine.
Please create an ACL with bidirecctional ACEs and add it as a group of access to the interface of penetration:
IP access-list extended 180
IP 192.168.100.0 allow 0.0.0.255 192.168.1.0 0.0.0.255 connect
ip permit 192.168.1.0 0.0.0.255 192.168.100.0 0.0.0.255 connect
allow an ip
interface GigabitEthernet0/1
IP access-group 180 to
IP access-group out 180
Generer generate traffic, then run the command display 180 access lists .
Also, if possible activate debug ip icmp at the same time.
Share the results.
Thank you
-
Hello again,
can you please answer me a few questions that burned my head these days
1 can I connect ASA5505 a WRT54GL router in a VPN tunnel so that the WRT54GL is the endpoint that connects to the ASA?
2. If Yes can you tell me please which firmware should I use and the steps that will follow.
3 if not can you me say what router should I use so that the VPN tunnel can be done.
Thank you!
Hi Svetoslav,
I understand that you ask if you can establish a VPN site to site between an ASA 5505 and Linksys WRT54GL. Unfortunately, the WRT54GL doesn't support VPN endpoint. If you don't want to spend money on another ASA 5505 (which I recommend), you can watch the line Cisco Small Business firewall-lights/roads, like the RV320.
http://www.Cisco.com/en/us/products/ps11997/index.html
Kind regards
Mike
Maybe you are looking for
-
How do you know which disk to defragment and which can help to solve any problems and you can upgrade the memory on a Pavilion 20-b013w all in one pc
-
Someone at-s\u0026 Crash issues in Creative Suite of Adobe Illustrator using El Capitan?
Have graphics problems when using Creative Suite. Accidents of continuous... Any help is appreciated...
-
Delete individual rhythms in a project
Hi all, another small question: Is it possible to erase the beats in Garage Band? The scenario: I have a track where there is half of a missing bar in the transition between the chorus and the intro to guitar 4-bar for the next verse; so the County i
-
Structure of the event does not not at the exit of a Btn dialog box
Hi all I have here a simple VI. I want to blow a One button in the user dialog box. I want VI to wait until the user clicks on the OK"" button. When we click on the OK button the VI should pop another dialogue a button and stops when you press the Ok
-
How can I remove the frame private on a folder in Windows XP?
I scored a private folder and now I want to cancel this setting. The screen sharing and security I cannot uncheck the box 'make private' - it is gray and inaccessible.