Cisco ISE: External RADIUS server
Hello
I send RADIUS of NHP NHP, another. I have already defined "External RADIUS servers".
So, how can I use this external RADIUS server to process my application?
Looking at the user guide, but did not find information on this parameter (for the rule after rule not simple)
Cela if anyone use this, please suggest me.
Thank you
Mathias
Please specify which version you are using. There were improvements to the functionality of the proxy in ISE 1.1.1
This can be used as follows:
-Define "External RADIUS server"
-Set the "Sequence of RADIUS server. This allows you to define a sequence of proxies that will send queries to until you get an answer
-In the authentication policy when the rules instead of the allowed protocols can select a "RADIUS server Sequence.
Tags: Cisco Security
Similar Questions
-
Hello
Given that roam JRS servers must be put into a sequence of Radius to the ISE server, which IP node address is supposed to be registered with JANET, PAN or each address IP of PSN. I would have thought that it's the PAN because all external RADIUS servers are configured on the PLATEAU, but thought I should ask just to be sure. Thank you
Yes, even if the configuration is on the PLATEAU, only ise nodes that have the political role of active service, will be used to transmit requests by using external radius proxy functionality.
-
Use an external radius server in a different ISE ISE
Hello
This is the scenario: three companies are part of a business, we want to authenticate users through 802.1 x, there are 3 Active Directory and Cisco 3 ISE.
Is not possible to join in a forest or 'connect' Active Directory.
This:
[email protected] / * / --> WLC company B--> EHT--> radius_connection --> ISE company B company has--> [email protected] / * /
Is this possible?
Thank you!
Yes, it is called radius proxy. You can create separate authentication rules, that match name field to your user name, and send the request to the appropriate server to ISE.
In ISE, it is the authentication policy and the sequence of radius server with which you work
-
Authentication (Windows Server 2013) AD Cisco ISE problem
Background:
Has deployed two Cisco ISE 1.1.3. ISE will be used to authenticate users wireless access admin WLC and switches. Database backend is Microsoft running on Windows Server 2012 AD. Existing Cisco ACS 4.2 still running and authenticate users. There are two Cisco WLCs version 7.2.111.3.
Wireless users authenticates to AD, through works of GBA 4.2. Access admin WLC and switches to the announcement through ISE works. Authentication with PEAP-MSCHAPv2 access and admin PAP/ASCII wireless.
Problem:
Wireless users cannot authenticate to the announcement through ISE. This is the error message '11051 RADIUS packet contains invalid state attribute' & '24444 Active Directory failed because of an error that is not specified in the ISE'.
Conducted a detailed test of the AD of the ISE. The test was a success and the result seems fine except for the below:
xxdc01.XX.com (10.21.3.1)
Ping: 0 Mins Ago
Status: down
xxdc02.XX.com (10.21.3.2)
Ping: 0 Mins Ago
Status: down
xxdc01.XX.com
Last success: Thu Jan 1 10:00 1970
March 11 failure: read 11:18:04 2013
Success: 0
Chess: 11006
xxdc02.XX.com
Last success: Fri Mar 11 09:43:31 2013
March 11 failure: read 11:18:04 2013
Success: 25
Chess: 11006
Domain controller: xxdc02.xx.com:389
Domain controller type: unknown functional level DC: 5
Domain name: xx.COM
IsGlobalCatalogReady: TRUE
DomainFunctionality: 2 = (DS_BEHAVIOR_WIN2003)
ForestFunctionality: 2 = (DS_BEHAVIOR_WIN2003)
Action taken:
Log Cisco ISE and WLC by using the credentials of the AD. This excludes the connection AD, clock and AAA shared secret as the problem.
(2) wireless authentication tested using EAP-FAST, but same problem occurs.
(3) detailed error message shows below. This excludes any authentication and authorization policies. Even before hitting the authentication policy, the AD search fails.
12304 extract EAP-response containing PEAP stimulus / response
11808 extracted EAP-response containing EAP - MSCHAP VERSION challenge response to the internal method and accepting of EAP - MSCHAP VERSION such as negotiated
Evaluate the politics of identity
15006 set default mapping rule
15013 selected identity Store - AD1
24430 Authenticating user in Active Directory
24444 active Directory operation failed because of an error that is not specified in the ISE
(4) enabled the registration of debugging AD and had a look at the logging. Nothing significant, and no clue about the problem.
(5) wireless tested on different mobile phones with the same error and laptos
(6) delete and add new customer/features of AAA Cisco ISE and WLC
(7) ISE services restarted
(8) join domain on Cisco ISE
(9) notes of verified version of ISE 1.1.3 and WLC 7.2.111.3 for any open caveats. Find anything related to this problem.
10) there are two ISE and two deployed WLC. Tested a different combination of ISE1 to WLC1, ISE1 to WLC2, etc. This excludes a hardware problem of WLC.
Other possibilities/action:
1) test it on another version WLC. Will have to wait for approval of the failure to upgrade the WLC software.
(2) incompatibility between Cisco ISE and AD running on Microsoft Windows Server 2012
Did he experienced something similar to have ideas on why what is happening?
Thank you.
Update:
(1) built an another Cisco ISE 1.1.3 sever in another data center that uses the same domain but other domain controller. Thai domain controller running Windows Server 2008. This work and successful authentication.
(2) my colleague tested in a lab environment Cisco ISE 1.1.2 with Windows Server 2012. He has had the same problem as described.
This leads me to think that there is a compatibility issue of Cisco ISE with Windows Server 2012.
Yes, it seems that 1.1.3 doesn't support Server 2012 as of yet.
External identity Source OS/Version
Microsoft Windows Active Directory 2003 R2 32-bit and 64-bit
Active Directory Microsoft Windows 2008 32-bit and 64-bit
Microsoft Windows Active Directory 2008 R2 64-bit only
Microsoft Windows Active Directory 2003 32-bit only
http://www.Cisco.com/en/us/docs/security/ISE/1.1/compatibility/ise_sdt.PDF
-
Hello!!
We are working on a mapping between a promoter Cisco ISE group and a user group in Active Directory, but the customer wants the mapping through a RADIUS SERVER, to avoid the ISE by querying directly activate Directory.
I know it is possible to use a RADIUS SERVER as source of external identity for ISE... but, is possible to use this RADIUS SERVER for this sponsor group manages?
Thank you and best regards!
Hi Rodrigo,
The answer is no. There is no way to integrate the portal Sponsor config with a RADIUS server. Your DB for authentication Portal Sponsor options;
AD
LDAP
User internal ISE DBSent by Cisco Support technique iPhone App
-
Cisco ISE and external syslog server
Hi Security Experts,
We start with deployment cisco ISE (Identity Services Engine) in our network. We have allocated 250 GB of space for the node (Admin + monitor) ISE.
I want to know if we can send tracking of nodes of external syslog server logs after a defined time interval.
For example, newspapers that are more than 10 days are for external syslog server. So basically our node monitoring will have the marbles which are the Max 9 days. Is this possible? Could you tell me some doc that explains the configuration of the same thing?
Thank you
Boudou
No this is not possible via syslog. What you need is database purge, so that the monitoring database is purged after a determined time interval. Here's a guide that will help shed some light on this:
http://www.Cisco.com/en/us/docs/security/ISE/1.1/user_guide/ise_mnt.html#wp1054328
Tarik Admani
* Please note the useful messages *. -
Cisco ISE comments Portal - DNS problem - External area
Hello
I have a client that has the following sceanrio:
In a wireless deployment and deployment Cisco ISE 1.1.3 with CWA, when the wireless client receives the URL ISE redictect (URL to access the portal of ISE comments), this URL is based on the ISE DNS name, not on its IP address. Thus, the PC cannot solve this problem by DNS name because there is no DNS in the external area (for the guets) or by using the addresses of servers DNS ISP provided by the DHCP server, and therefore it cannot access the portal comments at all;
I know that in an attempt to manually code the IP address - it doesn't (IE in the authorization profile CWA, the equivalent URL redirection via the pair av CISCO as follows:)
Cisco-AV-Paire = redirect url =https://10.10.10.10:8443/guestportal/gateway? sessionId = sessionIdValue & action = cwa,)
given that the sessionIdValue variable is not replaced by its real value when sending to the wireless client)
My question is: this question has been addressed in version 1.2 of Cisco of ISE - has anyone tried it if has been processed? If not in Cisco 1.2 - does anyone know iof this feature will become available?
Thanks in advance for your answers.
Robert C.
Robert,
Manual assignment has been made available in version 1.2 of the ISE.
M.

-
Setup
Cisco Catalyst 2960-S running 15.0.2 - SE8
Under Centos freeRadius 6.4 RADIUS server
Client (supplicant) running Windows 7
When Windows client is connected to the port (port 12 in my setup) with authentication of 802. 1 x active switch, show of Wireshark that catalyst sends ask EAP and the client responds with EAP response. But it made not the request to the Radius server. The RADIUS test utility 'aaa RADIUS testuser password new-code test group' works.
Here is my config running. Any advice would be greatly appreciated.
#show running mySwitch-
mySwitch #show running-config
Building configuration...Current configuration: 2094 bytes
!
version 12.2
no service button
horodateurs service debug datetime msec
Log service timestamps datetime msec
no password encryption service
!
hostname myswitch
!
boot-start-marker
boot-end-marker
!
activate the password secret 5 $1$ Z1z6$ kqvVYRQdVRZ0h8aDTV5DR0 enable password!
!
!
AAA new-model
!
!
AAA dot1x group group radius aaa accounting dot1x default start-stop radius authentication group!
!
!
AAA - the id of the joint session
1 supply ws-c2960s-24ts-l switch
!
!
!
!
!
control-dot1x system-auth
pvst spanning-tree mode
spanning tree extend id-system
!
!
!
!
internal allocation policy of VLAN no ascendant interface FastEthernet0 no stop ip address!
GigabitEthernet1/0/1 interface
!
interface GigabitEthernet1/0/2
!
interface GigabitEthernet1/0/3
!
interface GigabitEthernet1/0/4
!
interface GigabitEthernet1/0/5
!
interface GigabitEthernet1/0/6
!
interface GigabitEthernet1/0/7
!
interface GigabitEthernet1/0/8
!
interface GigabitEthernet1/0/9
!
interface GigabitEthernet1/0/10
!
interface GigabitEthernet1/0/11
!
interface GigabitEthernet1/0/12
switchport mode access
Auto control of the port of authentication
dot1x EAP authenticator
!
interface GigabitEthernet1/0/13
!
interface GigabitEthernet1/0/14
!
interface GigabitEthernet1/0/15
!
interface GigabitEthernet1/0/16
!
interface GigabitEthernet1/0/17
!
interface GigabitEthernet1/0/18
!
interface GigabitEthernet1/0/19
!
interface GigabitEthernet1/0/20
!
interface GigabitEthernet1/0/21
!
interface GigabitEthernet1/0/22
!
interface GigabitEthernet1/0/23
!
interface GigabitEthernet1/0/24
!
interface GigabitEthernet1/0/25
!
interface GigabitEthernet1/0/26
!
interface GigabitEthernet1/0/27
!
interface GigabitEthernet1/0/28
!
interface Vlan1
IP 10.1.2.12 255.255.255.0
!
IP http server
IP http secure server
activate the IP sla response alerts
recording of debug trap
10.1.2.1 host connection tcp port 514 RADIUS-server host 10.1.2.1 transport auth-port 1812 acct-port 1646 timeout 3 retransmit testing123 key 3.
Line con 0
line vty 0 4
password password
line vty 5 15
password password
!
endinterface GigabitEthernet1/0/16
!
interface GigabitEthernet1/0/17
!
interface GigabitEthernet1/0/18
!
interface GigabitEthernet1/0/19
!
interface GigabitEthernet1/0/20Have you run wireshark on the server because the request to switch? If so you make sure that there is a response from the server? For Windows network POLICY Server (I've never tried Centos), you must ensure that the request is related to a policy which then authenticates, or denies access. Usually, it is a matter of such attributes and the seller.
Regarding the configuration, it seems a bit out of the AAA. Try to remove the:
line "aaa dot1x group service radius authentication" and this by using instead:
"aaa dot1x default radius authentication group". After the dot1x word you are supposed to provide a list of the authentication or the default Word if you do not want to use a list.
-
Cisco ISE with GANYMEDE + and RADIUS both?
Hello
I'm wired opening of authentication on a network using Cisco ISE. I studied the conditions for this. I know that I need to enable the RADIUS on the Cisco switches on the network. The switches in the network are already programmed to GANYMEDE +. Anyone know if they can both operate on the same network at the same time?
Bob
I suppose that Ganymede is configured (with ACS 4.x or 5.x) for the peripheral administration via telnet/ssh, and now you need the RADIUS (radius) to authenticate 802. 1 x. Yes they can both work on the same network at the same time.
~ BR
Jatin kone* Does the rate of useful messages *.
-
I am very new to Cisco ISE and Meraki. I try to get the Radius configuration for wireless authentication. When I do a test of the Meraki to ISE, it passes.
When I try to connect from my laptop, I look at the logs of the Radius and it passes; However, it does not connect me to good policy. I keep hitting the default policy. I have my Meraki police above the default policy in the strategy defined in article. I have attached what looks like my strategy game.
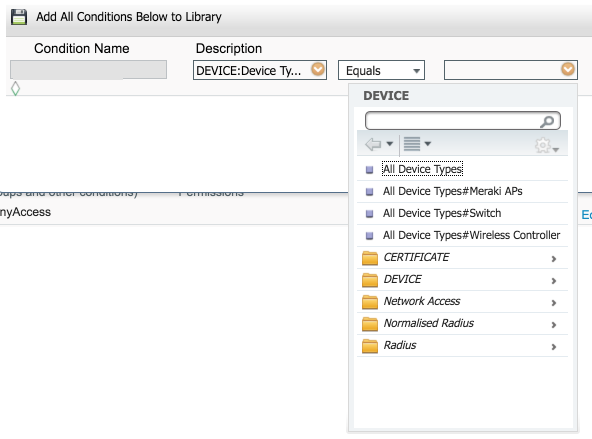
Devices does not really matter. Here is what I see when I create a device group (where you add the access point to this group), and then create the condition:
And here is where I create the condition of strategy game and you should be able to select the Meraki access points:
This will give you the condition similar to what I posted above. This is perhaps why you aren't hit that is not matching the condition for this game.
-
RADIUS server two in 1 Cisco router
Hello
Just need to know if it is possible to use two RADIUS server in 1 Cisco router. The first server RADIUS authenticate remote users to access our internal LAN while the other RADIUS server will authenticate users who will have access to routers. The reason why we cannot use the same RADIUS server to authenticate remote users and users of router is due to our contract with our supplier (long story!).
in any case, if it's possible, could someone help me how to do or give me the link to the documentation.
Thank you
Yes, it's the way to do it. This gives you two different methods, the user.
connection key radius-server 1.1.1.1
RADIUS - 2.2.2.2 key server logon
3.3.3.3 RADIUS server remote key
4.4.4.4 RADIUS server remote key
RADIUS AAA server telnet protocol group
Server 1.1.1.1
2.2.2.2 Server
AAA-server group remoteaccess radius Protocol
3.3.3.3 Server
Server 4.4.4.4
AAA authentication login default group remoteaccess
AAA authentication connection group telnet
line vty 0 4
SUCH connection authentication
Line con 0
authentication of SUCH loging
This is an example which will allow your access telnet to the router to use a server group
while allowing your users to remote access use other radius servers.
-Jesse
-
How to account for the Radius Server cisco vpn client
Hello
I would like to realize vpn cisco customers
My config is:
AAA authentication login default local radius group
RADIUS AAA authentication login aaa_radius local group
RADIUS group AAA authorization exec default authenticated if
AAA authorization vpn LAN
failure to exec AAA accounting
action-type market / stop
RADIUS group
!
AAA accounting network aaa_radius
action-type market / stop
RADIUS groupRADIUS-server host x.x.x.x auth-port 1812 acct-port 1813 key xxxxx
No package of accounitng is sent to the server radius, only the packages autthetication
RADIUS server is freeradius
Thank you
Pet
Hello!
The sequence of commands you add to your configuration:
1. in the case of former card crypto
crypto-NAME of the customer accounting card card list aaa_radius
2. in the case of isakmp profiles
Profile of crypto isakmp PROFILE NAME
accounting aaa_radius
When the NAME of the map and the PROFILE NAME real names for you profile crypto map or isakmp respectively.
I hope this helps.
Best regards.
-
Cisco 1812 no contact to the Radius Server
Hi guys,.
IM pretty new to cisco and plays with an 1812 products... I am trying set up an easy VPN server, with the support of ray and I can see that I did everything right, but there is a problem, because the router do not contact the RADIUS server and the RADIUS server has been tested ok.
Anyone who can see what I'm missing? Worked with this problem for 3 days now.
Here is my CONF.
Current configuration: 9170 bytes
!
! Last modification of the configuration to 13:44:49 UTC Tuesday, October 12, 2010
!
version 15.1
horodateurs service debug datetime msec
Log service timestamps datetime msec
no password encryption service
!
router host name
!
boot-start-marker
boot-end-marker
!
!
no set record in buffered memory
!
AAA new-model
!
!
AAA server radius sdm-vpn-server-group 1 group
auth-port 1645 90.0.0.245 Server acct-port 1646
!
AAA authentication login default local
AAA authentication login sdm_vpn_xauth_ml_1-passwd-expiry group sdm-vpn-server-group 1
AAA authorization exec default local
AAA authorization sdm_vpn_group_ml_1 LAN
!
!
!
!
!
AAA - the id of the joint session
!
Crypto pki token removal timeout default 0
!
Crypto pki trustpoint TP-self-signed-250973313
enrollment selfsigned
name of the object cn = IOS - Self - signed - certificate - 250973313
revocation checking no
!
!
TP-self-signed-250973313 crypto pki certificate chain
certificate self-signed 01
308201A 5 A0030201 02020101 3082023C 300 D 0609 2A 864886 F70D0101 04050030
2 040355 04031325 494F532D 53656 C 66 2 AND 536967 6E65642D 43657274 30312E30
69666963 32353039 37333331 33301E17 313031 30313230 39343333 0D 6174652D
395A170D 2E302C06 1325494F 03540403 32303031 30313030 30303030 5A 303031
532D 5365 6C662D53 69676E65 4365 72746966 69636174 652 3235 30393733 642D
06092A 86 4886F70D 01010105 33313330 819F300D 00308189 02818100 0003818D
BCF94FB0 77240E92 B703CE70 556D5D22 A57823E5 DD4CD4C4 12D639DE 5E97DB2D
81FBB304 9FA677A6 CAD84F96 9734081B F8F8FAAE 000B02FB AEF7C7B1 73AFA44B
7D27E112 8991F03B 3D4FD484 34E2EA9F BD426F73 48778F2A AD35AAD6 EC00805D
249B 8702 D545AEEA 40670DFD 3E6BEC29 EE48A0C6 CB7694FD 722D1A62 3A499CC5
02030100 01A 36630 03551 D 13 64300F06 0101FF04 05300301 01FF3011 0603551D
11040A 30 08820652 6F757465 72301F06 23 04183016 801462CB F6BD12F6 03551D
080C8A89 F9FBBDCE 9751528A FFFD301D 0603551D 0E041604 1462CBF6 BD12F608
0C8A89F9 FBBDCE97 51528AFF FD300D06 092 HAS 8648 01040500 03818100 86F70D01
ACA87977 CF 55225 6 9147E57E 8B5A8CA8 46348CAF 801D11C6 9DA57C69 14FA5076
6844F0CC 4CBEB541 136A483A 69F7B7F0 E44474E8 14DC2E80 CC04F840 B 3531, 884
F08A492D 8C3902C0 725EE93D AC83A29F 799AAE0F 5795484B B3D02F84 911DB135
5 189766 C30DA111 6B9B4E46 E999DA5B 202 21B0B9D4 HAS 6900 07A93D8D 41C7FD21
quit smoking
dot11 syslog
IP source-route
!
!
!
!
!
IP cef
No ipv6 cef
!
Authenticated MultiLink bundle-name Panel
!
!
!
license udi pid CISCO1812/K9 sn FCZ10232108
username admin privilege 15 secret 5 P677 $1$ $ Rggfdgt8MeD8letZDL08d.
!
!
!
type of class-card inspect correspondence sdm-nat-smtp-1
game group-access 101
smtp Protocol game
type of class-card inspect entire game SDM_AH
match the name of group-access SDM_AH
type of class-card inspect all sdm-cls-insp-traffic game
match Protocol cuseeme
dns protocol game
ftp protocol game
h323 Protocol game
https protocol game
match icmp Protocol
match the imap Protocol
pop3 Protocol game
netshow Protocol game
Protocol shell game
match Protocol realmedia
match rtsp Protocol
smtp Protocol game
sql-net Protocol game
streamworks Protocol game
tftp Protocol game
vdolive Protocol game
tcp protocol match
udp Protocol game
inspect the class-map match sdm-insp-traffic type
corresponds to the class-map sdm-cls-insp-traffic
type of class-card inspect all SDM-voice-enabled game
h323 Protocol game
Skinny Protocol game
sip protocol game
type of class-card inspect entire game SDM_IP
match the name of group-access SDM_IP
type of class-card inspect entire game SDM_ESP
match the name of group-access SDM_ESP
type of class-card inspect entire game SDM_EASY_VPN_SERVER_TRAFFIC
match Protocol isakmp
match Protocol ipsec-msft
corresponds to the SDM_AH class-map
corresponds to the SDM_ESP class-map
type of class-card inspect the correspondence SDM_EASY_VPN_SERVER_PT
corresponds to the SDM_EASY_VPN_SERVER_TRAFFIC class-map
type of class-card inspect all match sdm-cls-icmp-access
match icmp Protocol
tcp protocol match
udp Protocol game
type of class-card inspect correspondence sdm-invalid-src
game group-access 100
type of class-card inspect correspondence sdm-icmp-access
corresponds to the class-map sdm-cls-icmp-access
type of class-card inspect correspondence sdm-Protocol-http
http protocol game
!
!
type of policy-card inspect sdm-permits-icmpreply
class type inspect sdm-icmp-access
inspect
class class by default
Pass
type of policy-card inspect sdm-pol-NATOutsideToInside-1
class type inspect sdm-nat-smtp-1
inspect
class class by default
drop
type of policy-map inspect sdm - inspect
class type inspect sdm-invalid-src
Drop newspaper
class type inspect sdm-insp-traffic
inspect
class type inspect sdm-Protocol-http
inspect
class type inspect SDM-voice-enabled
inspect
class class by default
Pass
type of policy-card inspect sdm-enabled
class type inspect SDM_EASY_VPN_SERVER_PT
Pass
class class by default
drop
type of policy-card inspect sdm-license-ip
class type inspect SDM_IP
Pass
class class by default
Drop newspaper
!
security of the area outside the area
safety zone-to-zone
ezvpn-safe area of zone
safety zone-pair sdm-zp-self-out source destination outside zone auto
type of service-strategy inspect sdm-permits-icmpreply
source of sdm-zp-out-auto security area outside zone destination auto pair
type of service-strategy inspect sdm-enabled
safety zone-pair sdm-zp-in-out source in the area of destination outside the area
type of service-strategy inspect sdm - inspect
sdm-zp-NATOutsideToInside-1 zone-pair security source outside the area of destination in the area
type of service-strategy inspect sdm-pol-NATOutsideToInside-1
in the destination box source sdm-zp-in-ezvpn1 ezvpn-pairs area security
type of service-strategy inspect sdm-license-ip
source of sdm-zp-out-ezpn1 of security area outside zone ezvpn-zone time pair of destination
type of service-strategy inspect sdm-license-ip
safety zone-pair sdm-zp-ezvpn-out1-source ezvpn-zone of destination outside the area
type of service-strategy inspect sdm-license-ip
safety zone-pair source sdm-zp-ezvpn-in1 ezvpn-area destination in the area
type of service-strategy inspect sdm-license-ip
!
!
crypto ISAKMP policy 1
BA 3des
preshared authentication
Group 2
!
Configuration group Sindby crypto isakmp client
key TheSommerOf03
90.0.0.240 DNS 8.8.8.8
win 90.0.0.240
SBYNET field
pool SDM_POOL_2
Max-users 15
netmask 255.255.255.0
ISAKMP crypto sdm-ike-profile-1 profile
identity Sindby group match
client authentication list sdm_vpn_xauth_ml_1
ISAKMP authorization list sdm_vpn_group_ml_1
client configuration address respond
virtual-model 1
!
!
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
Crypto ipsec transform-set ESP-3DES-SHA1 esp-3des esp-sha-hmac
Crypto ipsec transform-set esp-SHA2-ESP-3DES-3des esp-sha-hmac
Crypto ipsec transform-set esp-3des SHA3-ESP-3DES esp-sha-hmac
Crypto ipsec transform-set esp-3des SHA4-ESP-3DES esp-sha-hmac
Crypto ipsec transform-set esp-3des SHA5-ESP-3DES esp-sha-hmac
Crypto ipsec transform-set esp-3des SHA6-ESP-3DES esp-sha-hmac
Crypto ipsec transform-set esp-3des SHA7-ESP-3DES esp-sha-hmac
Crypto ipsec transform-set esp-3des SHA8-ESP-3DES esp-sha-hmac
Crypto ipsec transform-set esp-3des SHA9-ESP-3DES esp-sha-hmac
Crypto ipsec transform-set esp-3des SHA10-ESP-3DES esp-sha-hmac
!
Profile of crypto ipsec SDM_Profile1
game of transformation-ESP-3DES-SHA10
isakmp-profile sdm-ike-profile-1 game
!
!
!
!
!
!
interface BRI0
no ip address
encapsulation hdlc
Shutdown
!
interface FastEthernet0
Description $FW_OUTSIDE$
IP address 93.166.xxx.xxx 255.255.255.248
NAT outside IP
IP virtual-reassembly in
outside the area of security of Member's area
automatic duplex
automatic speed
!
interface FastEthernet1
no ip address
Shutdown
automatic duplex
automatic speed
!
interface FastEthernet2
!
interface FastEthernet3
!
interface FastEthernet4
!
interface FastEthernet5
!
FastEthernet6 interface
!
interface FastEthernet7
!
interface FastEthernet8
!
interface FastEthernet9
!
type of interface virtual-Template1 tunnel
IP unnumbered FastEthernet0
ezvpn-safe area of Member's area
ipv4 ipsec tunnel mode
Tunnel SDM_Profile1 ipsec protection profile
!
interface Vlan1
Description $FW_INSIDE$
IP 90.0.0.190 255.255.255.0
IP nat inside
IP virtual-reassembly in
Security members in the box area
!
local IP SDM_POOL_1 90.0.0.25 pool 90.0.0.29
local IP SDM_POOL_2 90.0.0.75 pool 90.0.0.90
IP forward-Protocol ND
IP http server
local IP http authentication
IP http secure server
IP http timeout policy inactive 600 life 86400 request 10000
!
!
IP nat inside source static tcp 192.168.1.200 25 interface FastEthernet0 25
the IP nat inside source 1 interface FastEthernet0 overload list
IP route 0.0.0.0 0.0.0.0 93.166.xxx.xxx
!
SDM_AH extended IP access list
Remark SDM_ACL = 1 category
allow a whole ahp
SDM_ESP extended IP access list
Remark SDM_ACL = 1 category
allow an esp
SDM_IP extended IP access list
Remark SDM_ACL = 1 category
allow an ip
!
exploitation forest esm config
access-list 1 permit 90.0.0.0 0.0.0.255
Access-list 100 = 128 SDM_ACL category note
access-list 100 permit ip 255.255.255.255 host everything
access-list 100 permit ip 127.0.0.0 0.255.255.255 everything
access-list 100 permit ip 93.166.xxx.xxx 0.0.0.7 everything
Remark SDM_ACL category of access list 101 = 0
IP access-list 101 permit any host 192.168.1.200
!
!
!
!
!
!
RADIUS-server host 90.0.0.245 auth-port 1645 acct-port 1646
!
control plan
!
!
Line con 0
line to 0
line vty 0 4
transport input telnet ssh
!
end
Hello
Looks like you're missing the key from the radius server configuration "RADIUS-server host 90.0.0.245 auth-port 1645 1646 key your_keyacct-port»
Thank you
Wen
-
Cisco ISE synchronization and NTP server
I am currently implementing Cisco ISE to our customer.
But having a little problem Cisco ISE cannot synchronize with NTP server.
Keep in mind, NTP servers in AD.
Currently, Cisco ISE synchronize just at the local level.
Cisco ISE implemented distributed mode, when there are two Cisco ISE installed on VMware (Administration & monitoring primary & secondary node), and another is the device (political Service node).
As a result of it might not sync server NTP and the ISE of Cisco, Cisco ISE often OUT-OF-SYN.
Is there a solution for this problem?
Gandhi,
This is a known issue, I have crossed upwards and have not read that you use AD as your NTP server, there have been problems with integration of the ISE and ACS with AD as their ntp source, please use another device like sources ntp, for example a router.
Thank you
Tarik Admani
* Please note the useful messages *. -
Access VPN ASA and cisco ISE Admin
Hello
Currently I'm deployment anyconnect VPN Solution for my client on ASA 9.2 (3). We use the ISE 1.3 to authenticate remote users.
In the policy stipulates the conditions, I put the condition as below.
Policy name: Anyconnect
Condition: DEVICE: Device Type Device Type #All Device Types #Dial - in access EQUALS AND
RADIUS: NAS-Port-Type is equal to virtualI'm authenticating users against the AD.
I am also restrict users based on group membership in authorization policies by using the OU attributes.
This works as expected for remote users.
We also use the ISE to authenticate administrators to connect to the firewall. Now what happens is, Cisco ASA valid also against policy, administrators and their default name Anyconnect.
Now the question is, how to set up different political requirement for access network admin and users the same Firewall VPN.
Any suggestions on this would be a great help.
See you soon,.
Sri
You can get some ideas from this article of mine:
http://ltlnetworker.WordPress.com/2014/08/31/using-Cisco-ISE-as-a-generic-RADIUS-server/
Maybe you are looking for
-
Compressor doesn't recognize no updates of project FCPX
When I recently sent a FCPX project to the compressor, I noticed that he needed to sharpen after that he had done his work. I went back to FCPX and redesigned some of the clips and sent to compressor again. He spat that is exactly the same result as
-
cannot switch between iPhoto libraries
Just recently, my mac made me create a new library for iPhoto. I don't know why, maybe my first one was overloaded, because I have a LOT of photos and videos and we used only. But after that there is a new one (which is of course empty), it won't let
-
My m9650f has two eSATA ports that work properly. The card has port multiplier cabability to know, so I can add a multiplier with success?
-
Since yesterday I couldn't send emails from OE6 (can receive without problem) the error message is An unknown error has occurred. ' Subject 'Thank you!', account: 'pop3.hosts.co.uk', server: 'smtp.namesco.net', Protocol: SMTP, server response: ' 550
-
original title: connection to a network PC 2 I use Windows XP, when I try to install 2 network connection on a PC, AAQMS has stopped working, but if I disable the secand connection quite well. 1 connected directly to the AAQMS system for the Air moni