Cisco ISE with GANYMEDE + and RADIUS both?
Hello
I'm wired opening of authentication on a network using Cisco ISE. I studied the conditions for this. I know that I need to enable the RADIUS on the Cisco switches on the network. The switches in the network are already programmed to GANYMEDE +. Anyone know if they can both operate on the same network at the same time?
Bob
I suppose that Ganymede is configured (with ACS 4.x or 5.x) for the peripheral administration via telnet/ssh, and now you need the RADIUS (radius) to authenticate 802. 1 x. Yes they can both work on the same network at the same time.
~ BR
Jatin kone
* Does the rate of useful messages *.
Tags: Cisco Security
Similar Questions
-
CIsco ISE with HP and Fortigate
Hello
I configured the switches HP 5820 X and 5130 for authentication radius AAA with Cisco ISE 2.0.0.306.
The switch receives the response from authorization successful; but unable to connect. What are the Advanced profile Radius authorization attributes in
ISE?
In addition, ISE supports Fotigate firewall?
Oh and Yes ISE supports any device using the RADIUS in accordance with rfc, it is usually only a question about this that av-pairs to send to that specific device, there is not really standard for this.
-
Interaction of Ganymede + and radius ACS 2.6 download PIX ACLs
We have ACS v2.6 running and control our connection to remote, routers and switches access. We are now looking to add support for a PIX firewall internal and want to use downloadable ACS ACL for the PIX. (to control outbound traffic through the PIX for authenticated users)
We have achieved this help attributes RADIUS of Cisco IOS/PIX
[009\001] cisco-av-pair on ACS. (and ACL restrictions of access on access to users)
However the problem we noticed is that any user is valid in our database of CiscoSecure or SecureID can authenticate and gain access to through the firewall, even if they are not allowed to do this (and as it is by default on PIX from inside to outside is allowed unlimited full access).
Was then imposed restrictions on network access on the CiscoSecure ACS for our PIX - to allow only access of corresponding user groups, but it did not work with RADIUS only GANYMEDE + (I guess that's because the RADIUS does not support approval).
We must work with GANYMEDE + and the passes of the ACS to the bottom of the ACL number/ID for the PIX for users allowed.
Question: We want to use downloadable s ACL of ACS for the PIX (for reasons of central support) is possible using GANYMEDE + and if yes how we re CiscoSecure ACS suitable for the ACL example below;
pix_int list access permit tcp any host 10.x.x.x eq 1022
pix_int list access permit tcp any host 10.x.x.x eq 1023
Thank you
Download ACL works only with the RADIUS, as described here:
http://www.Cisco.com/warp/public/110/atp52.html#new_per_user
You can continue to set the ACL on the PIX itself and simply pass the ACL via GANYMEDE number (as shown here: http://www.cisco.com/warp/public/110/atp52.html#access_list), but you can actually spend the entire ACL down via GANYMEDE, sorry.
-
Cisco ISE 2.0 and WLC 5508 with 7.6.130.0
I have looked on the release notes and compatibility n for ISE 2.0 and have not seen the answer to that. For the WLC 5508, the minimum AirOS is 7.0.116.0 but he limited the AAA authentication and support for comments. The recommended version of AirOS is 8.0.121.0.
http://www.Cisco.com/c/en/us/TD/docs/security/ISE/2-0/compatibility/ISE _...
What airos 7.6.130.0? I know that AirOS release works with 1.3 and 1.4, even if they show the same support for version 2.0. I'm just afraid that something may have changed with 2.0. I am concerned only about the AAA authentication and guest access. No BYOD, posture or MDM is necessary.
No change. Works well.
-
Cisco ISE 1.2 and the ad group
Hello
I have Cisco ISE installed on my EXSi server for my test pilot. I added several ad groups at ISE as well.
I created a condition of authorization policy, that is WIRELESS_DOT1X_USERS (see screenshot)
Basically, I just replicate the default Wireless_802.1X and added Network Access: EapAuthentication, Equals, EAP - TLS.My problem is, I have been unable to join the wireless network, if I added my ad group to the authorization strategy (see screenshot). The user I is a member of WLAN USERS. If I removed the authorization policy group, the use is able to join the wireless network.
I have attached the screenshot of ISE newspapers as well. I checked the ISE, AD/NPS, WLC, laptop computer time and date, and they are all in sync.
I also have the WLC added as NPS client on my network.
I checked the newspaper AD and I found it, it was the local management user WLCs trying to authenticate. It is supposed to be my wireless user Credential is not the WLC.
It's the paper I received from the AD/NPS
Access denied to user network policy server.
Contact the server administrator to strategy network for more information.
User:
Security ID: NULL SID
Account name: admin
Domain account: AAENG
Account name: AAENG\admin
Client computer:
Security ID: NULL SID
Account name: -.
Full account name: -.
OS version: -.
Called Station identifier: -.
Calling the Station identifier: -.
NAS:
NAS IPv4 address: 172.28.255.42
NAS IPv6 address: -.
NAS identifier: RK3W5508-01
NAS Port Type: -.
NAS Port: -
RADIUS client:
Friendly name of client: RK3W5508-01
The client IP address: 172.28.255.42
Information about authentication:
Connection request policy name: Windows authentication for all users use
The network policy name: -.
Authentication provider: Windows
Authentication server: WIN - RSTMIMB7F45.aaeng.local
Authentication type: PAP
EAP Type: -
Identifier for account: -.
Results of logging: Accounting Information was written in the local log file.
Reason code: 16
Reason: Authentication failed due to incompatibility of user credentials. The provided username is not mapped to an existing user account or the password is incorrect.
Hello
The problem is with what ISE name, it's choosing to search of the AD. If you look in the ISE newspapers down, you'll see the username that use ISE (firstname, lastname) to search for the AD.
In your certificate template see what attribute containst name AD (possibly the dns name or email or the name of principle of RFC 822 NT), go to your profile to authenticate cerificate and use this attribute for the user name.
Thank you
Tarik Admani
* Please note the useful messages *. -
Cisco ISE posture assessment and client provisioning
Hello
I have the Cisco ISE and Cisco IOS device. I configured the RADIUS between these devices.
Also, I configured RADIUSbetween ISE of Cisco and Cisco ASA. Now I want to know that how to posture assessment for these devices (ISE of Cisco and Cisco ASA or ISE Cisco Cisco IOS). Please give me the steps together for assesment for cisco ios device posture in Cisco ise.
In addition, please give me related to posture assessment and the provisioning client logs.
Thanks in advance.
You can go through the list link below to download a PDF link
Assessment of the posture with ISE.
http://www.Cisco.com/Web/CZ/expo2012/PDF/T_SECA4_ISE_Posture_Gorgy_Acs.PDF
~ BR
Jatin kone* Does the rate of useful messages *.
-
GANYMEDE + and RADIUS - don't either care hostname?
When first experimented with GANYMEDE + I remember to change the host name on a router and have it cause problems with authentication. Is this normal for GANYMEDE + to use a host name of devices as part of the authentication process? What is RADIUS?
Hello
Nope, neither for the AAA process, we use the host name of the appliance.
Only take care of the source (source IP address) interface, the shared secret and the ports used.
HTH,
Tiago--
If this helps you or answers to your question if it you please mark it as 'responded' or write it down, if other users can easily find it.
-
Integration of CISCO ISE with another controller wireless lan of the seller
Hi all!
I am currently working on an assignment and eager to integrate the identity service provider in the network. the only problem is that the deployed wireless network earlier of another provider I just need to know that either ISE has integration with the other controller feature wireless provider and can provide guest access control. The LDAP integration is also required.
Waiting for help!
Hello
According to my knowledge Yes, Cisco ISE can be integrated with another controller wireless LAN of the seller, but limited. (Aruba, Rukus) and if you want to add the external identity group to your network, then LDAP integration is required.
-
Hello
We run 3xWLC controller with 800 AP using ISE 1.2 for authentication wireless 802. 1 x. I was looking in the config of the ISE and notice of 400 edge cheating only 2x2960s are configured with 802. 1 x (ISE RADIUS config) and SNMP and only 2 of the port is 2 ap tie with swtich remaining ports.and the 3XWLC in network devices.
I do not understand how an access point is to do this work (802.1 x) because it is location on different site and people are connecting to various different locations. ISE almost run/do 11 876 profiled ends.
version 12.2
!
boot-start-marker
boot-end-marker
!
enable secret 5 $1$ fokm$ lesIWAaceFFs.SpNdJi7t.
!
Test-RADIUS username password 7 07233544471A1C5445415F
AAA new-model
Group AAA dot1x default authentication RADIUS
Group AAA authorization network default RADIUS
Group AAA authorization auth-proxy default RADIUS
start-stop radius group AAA accounting dot1x default
start-stop radius group AAA accounting system by default
!
!
!
!
AAA server RADIUS Dynamics-author
Client 10.178.5.152 server-key 7 151E1F040D392E
Client 10.178.5.153 server-key 7 060A1B29455D0C
!
AAA - the id of the joint session
switch 1 supply ws-c2960s-48 i/s-l
cooldown critical authentication 1000
!
!
IP dhcp snooping vlan 29,320,401
no ip dhcp snooping option information
IP dhcp snooping
no ip domain-lookup
analysis of IP device
!
logging of the EMP
!
Crypto pki trustpoint TP-self-signed-364377856
enrollment selfsigned
name of the object cn = IOS - Self - signed - certificate - 364377856
revocation checking no
rsakeypair TP-self-signed-364377856
!
!
TP-self-signed-364377856 crypto pki certificate chain
certificate self-signed 01
30820247 308201B 0 A0030201 02020101 300 D 0609 2A 864886 F70D0101 04050030
2 060355 04031325 494F532D 53656 C 66 2 AND 536967 6E65642D 43657274 30312E30
69666963 33363433 37373835 36301E17 393330 33303130 30303331 0D 6174652D
305A170D 2E302C06 1325494F 03550403 32303031 30313030 30303030 5A 303031
532D 5365 6C662D53 69676E65 642D 4365 72746966 69636174 652 3336 34333737
06092A 86 4886F70D 01010105 38353630 819F300D 00308189 02818100 0003818D
B09F8205 9DD44616 858B1F49 A27F94E4 9E9C3504 F56E18EB 6D1A1309 15C20A3D
31FCE168 5A8C610B 7F77E7FC D9AD3856 E4BABDD1 DFB28F54 6C24229D 97756ED4
975E2222 939CF878 48D7F894 618279CF 2F9C4AD5 4008AFBB 19733DDB 92BDF73E
B43E0071 C7DC51C6 B9A43C6A FF035C63 B53E26E2 C0522D40 3F850F0B 734DADED
02030100 01A 37130 03551 D 13 6F300F06 0101FF04 05300301 01FF301C 0603551D
11041530 13821150 5F494D2B 545F5374 61636B5F 322D312E 301F0603 551D 2304
18301680 1456F3D9 23759254 57BA0966 7C6C3A71 FFF07CE0 A2301D06 03551D0E
04160414 56F3D923 75925457 BA09667C 6C3A71FF F07CE0A2 2A 864886 300 D 0609
F70D0101 5B1CA52E B38AC231 E45F3AF6 12764661 04050003 81810062 819657B 5
F08D258E EAA2762F F90FBB7F F6E3AA8C 3EE98DB0 842E82E2 F88E60E0 80C1CF27
DE9D9AC7 04649AEA 51C49BD7 7BCE9C5A 67093FB5 09495971 926542 4 5A7C7022
8D9A8C2B 794D99B2 3B92B936 526216E0 79 D 80425 12B 33847 30F9A3F6 9CAC4D3C
7C96AA15 CC4CC1C0 5FAD3B
quit smoking
control-dot1x system-auth
dot1x critical eapol
!
pvst spanning-tree mode
spanning tree extend id-system
No vlan spanning tree 294-312,314-319,321-335,337-345,400,480,484-493,499,950
!
!
!
errdisable recovery cause Uni-directional
errdisable recovery cause bpduguard
errdisable recovery cause of security breach
errdisable recovery cause channel-misconfig (STP)
errdisable recovery cause pagp-flap
errdisable recovery cause dtp-flap
errdisable recovery cause link-flap
errdisable recovery cause FPS-config-incompatibility
errdisable recovery cause gbic-invalid
errdisable recovery cause psecure-violation
errdisable cause of port-mode-failure recovery
errdisable recovery cause dhcp-rate-limit
errdisable recovery cause pppoe-AI-rate-limit
errdisable recovery cause mac-limit
errdisable recovery cause vmps
errdisable recovery cause storm-control
errdisable recovery cause inline-power
errdisable recovery cause arp-inspection
errdisable recovery cause loopback
errdisable recovery cause small-frame
errdisable recovery cause psp
!
internal allocation policy of VLAN ascendant
!
!
interface GigabitEthernet1/0/10
switchport access vlan 320
switchport mode access
IP access-group ACL-LEAVE in
authentication event fail following action method
action of death server to authenticate the event permit
living action of the server reset the authentication event
multi-domain of host-mode authentication
open authentication
authentication order dot1x mab
authentication priority dot1x mab
Auto control of the port of authentication
periodic authentication
authentication violation replace
MAB
dot1x EAP authenticator
dot1x tx-time 10
spanning tree portfast
spanning tree enable bpduguardinterface GigabitEthernet1/0/16
switchport access vlan 320
switchport mode access
IP access-group ACL-LEAVE in
authentication event fail following action method
action of death server to authenticate the event permit
living action of the server reset the authentication event
multi-domain of host-mode authentication
open authentication
authentication order dot1x mab
authentication priority dot1x mab
Auto control of the port of authentication
periodic authentication
authentication violation replace
MAB
dot1x EAP authenticator
dot1x tx-time 10
spanning tree portfast
spanning tree enable bpduguard
interface GigabitEthernet1/0/24
switchport access vlan 320
switchport mode access
IP access-group ACL-LEAVE in
authentication event fail following action method
action of death server to authenticate the event permit
living action of the server reset the authentication event
multi-domain of host-mode authentication
open authentication
authentication order dot1x mab
authentication priority dot1x mab
Auto control of the port of authentication
periodic authentication
authentication violation replace
MAB
dot1x EAP authenticator
dot1x tx-time 10
spanning tree portfast
spanning tree enable bpduguard
!
interface GigabitEthernet1/0/33
switchport access vlan 320
switchport mode access
IP access-group ACL-LEAVE in
authentication event fail following action method
action of death server to authenticate the event permit
living action of the server reset the authentication event
multi-domain of host-mode authentication
open authentication
authentication order dot1x mab
authentication priority dot1x mab
Auto control of the port of authentication
periodic authentication
authentication violation replace
MAB
dot1x EAP authenticator
dot1x tx-time 10
spanning tree portfast
spanning tree enable bpduguard
interface GigabitEthernet1/0/34
switchport access vlan 320
switchport mode access
IP access-group ACL-LEAVE in
authentication event fail following action method
action of death server to authenticate the event permit
living action of the server reset the authentication event
multi-domain of host-mode authentication
open authentication
authentication order dot1x mab
authentication priority dot1x mab
Auto control of the port of authentication
periodic authentication
authentication violation replace
MAB
dot1x EAP authenticator
dot1x tx-time 10
spanning tree portfast
spanning tree enable bpduguard
!
interface GigabitEthernet1/0/44
switchport access vlan 320
switchport mode access
IP access-group ACL-LEAVE in
authentication event fail following action method
action of death server to authenticate the event permit
living action of the server reset the authentication event
multi-domain of host-mode authentication
open authentication
authentication order dot1x mab
authentication priority dot1x mab
Auto control of the port of authentication
periodic authentication
authentication violation replace
MAB
dot1x EAP authenticator
dot1x tx-time 10
spanning tree portfast
spanning tree enable bpduguard!
interface GigabitEthernet1/0/46
switchport access vlan 320
switchport mode access
IP access-group ACL-LEAVE in
authentication event fail following action method
action of death server to authenticate the event permit
living action of the server reset the authentication event
multi-domain of host-mode authentication
open authentication
authentication order dot1x mab
authentication priority dot1x mab
Auto control of the port of authentication
periodic authentication
authentication violation replace
MAB
dot1x EAP authenticator
dot1x tx-time 10
spanning tree portfast
spanning tree enable bpduguardinterface GigabitEthernet1/0/48
switchport access vlan 320
switchport mode access
IP access-group ACL-LEAVE in
authentication event fail following action method
action of death server to authenticate the event permit
living action of the server reset the authentication event
multi-domain of host-mode authentication
open authentication
authentication order dot1x mab
authentication priority dot1x mab
Auto control of the port of authentication
periodic authentication
authentication violation replace
MAB
dot1x EAP authenticator
dot1x tx-time 10
spanning tree portfast
spanning tree enable bpduguard
!
interface GigabitEthernet1/0/49
Description link GH
switchport trunk allowed vlan 1,2,320,350,351,401
switchport mode trunk
MLS qos trust dscp
IP dhcp snooping trust
!interface GigabitEthernet1/0/52
Description link CORE1
switchport trunk allowed vlan 1,2,29,277,278,314,320,401
switchport mode trunk
MLS qos trust dscp
IP dhcp snooping trust
!
!
interface Vlan320
IP 10.178.61.5 255.255.255.128
no ip-cache cef route
no ip route cache
!
default IP gateway - 10.178.61.1
IP http server
IP http secure server
IP http secure-active-session-modules no
active session modules IP http no
!
!
Access IP extended ACL-AGENT-REDIRECT list
deny udp any any domain eq bootps
permit tcp any any eq www
permit any any eq 443 tcp
IP extended ACL-ALLOW access list
allow an ip
IP access-list extended by DEFAULT ACL
allow udp any eq bootpc any eq bootps
allow udp any any eq field
allow icmp a whole
allow any host 10.178.5.152 eq 8443 tcp
permit tcp any host 10.178.5.152 eq 8905
allow any host 10.178.5.152 eq 8905 udp
permit tcp any host 10.178.5.152 eq 8906
allow any host 10.178.5.152 eq 8906 udp
allow any host 10.178.5.152 eq 8909 tcp
allow any host 10.178.5.152 eq 8909 udp
allow any host 10.178.5.153 eq 8443 tcp
permit tcp any host 10.178.5.153 eq 8905
allow any host 10.178.5.153 eq 8905 udp
permit tcp any host 10.178.5.153 eq 8906
allow any host 10.178.5.153 eq 8906 udp
allow any host 10.178.5.153 eq 8909 tcp
allow any host 10.178.5.153 eq 8909 udp
refuse an entire ip
Access IP extended ACL-WEBAUTH-REDIRECT list
deny ip any host 10.178.5.152
deny ip any host 10.178.5.153
permit tcp any any eq www
permit any any eq 443 tcpradius of the IP source-interface Vlan320
exploitation forest esm config
logging trap alerts
logging Source ip id
connection interface-source Vlan320
record 192.168.6.31
host 10.178.5.150 record transport udp port 20514
host 10.178.5.151 record transport udp port 20514
access-list 10 permit 10.178.5.117
access-list 10 permit 10.178.61.100
Server SNMP engineID local 800000090300000A8AF5F181
SNMP - server RO W143L355 community
w143l355 RW SNMP-server community
SNMP-Server RO community lthpublic
SNMP-Server RO community lthise
Server SNMP trap-source Vlan320
Server SNMP informed source-interface Vlan320
Server enable SNMP traps snmp authentication linkdown, linkup cold start
SNMP-Server enable traps cluster
config SNMP-server enable traps
entity of traps activate SNMP Server
Server enable SNMP traps ipsla
Server enable SNMP traps syslog
Server enable SNMP traps vtp
SNMP Server enable traps mac-notification change move threshold
Server SNMP enable traps belonging to a vlan
SNMP-server host 10.178.5.152 version 2 c lthise mac-notification
SNMP-server host 10.178.5.153 version 2 c lthise mac-notification
!
RADIUS attribute 6 sur-pour-login-auth server
Server RADIUS attribute 8 include-in-access-req
RADIUS attribute 25-application access server include
dead-criteria 5 tent 3 times RADIUS server
test the server RADIUS host 10.178.5.152 auth-port 1812 acct-port 1813 username test-RADIUS 7 key 03084F030F1C24
test the server RADIUS host 10.178.5.153 auth-port 1812 acct-port 1813 username test-RADIUS 7 key 141B060305172F
RADIUS vsa server send accounting
RADIUS vsa server send authenticationany help would be really appreciated.
I'm not sure that completely understand the question; But if LSE is only political wireless, then none of the wired switches need any configuration of ISE.
Access points tunnel all wireless traffic to the WLC on CAPWAP (unless you use FlexConnect). This is the configuration 802. 1 x on the WLC that implements policies defined in ISE.
Switches wired never need to act as an access network (n) device and so do not need to be defined in ISE unless or until you want to apply policies of ISE for wired devices...
-
Cisco ISE - eap-peap and eap - tls
Hello
Does anyone have an example of a policy of ISE, where from a WLC authentication requests can be processed by TLS and PEAP?
I don't seem to get that working, I however do the accident of ISE application with my config that is not the idea.
If peap uses this identity source, if tls uses 'this profile of authentication certificate '.
THX
Don't need to do in politics
Can create a sequence identity and understand that it contains a certificate OmniPass profile and identity store
Administration > identity management > identity Source sequences
Can then select and define the Certfiicate authentication profile for OmniPass based certificate and a list of authentication search
-
Access VPN ASA and cisco ISE Admin
Hello
Currently I'm deployment anyconnect VPN Solution for my client on ASA 9.2 (3). We use the ISE 1.3 to authenticate remote users.
In the policy stipulates the conditions, I put the condition as below.
Policy name: Anyconnect
Condition: DEVICE: Device Type Device Type #All Device Types #Dial - in access EQUALS AND
RADIUS: NAS-Port-Type is equal to virtualI'm authenticating users against the AD.
I am also restrict users based on group membership in authorization policies by using the OU attributes.
This works as expected for remote users.
We also use the ISE to authenticate administrators to connect to the firewall. Now what happens is, Cisco ASA valid also against policy, administrators and their default name Anyconnect.
Now the question is, how to set up different political requirement for access network admin and users the same Firewall VPN.
Any suggestions on this would be a great help.
See you soon,.
Sri
You can get some ideas from this article of mine:
http://ltlnetworker.WordPress.com/2014/08/31/using-Cisco-ISE-as-a-generic-RADIUS-server/
-
Authentication (Windows Server 2013) AD Cisco ISE problem
Background:
Has deployed two Cisco ISE 1.1.3. ISE will be used to authenticate users wireless access admin WLC and switches. Database backend is Microsoft running on Windows Server 2012 AD. Existing Cisco ACS 4.2 still running and authenticate users. There are two Cisco WLCs version 7.2.111.3.
Wireless users authenticates to AD, through works of GBA 4.2. Access admin WLC and switches to the announcement through ISE works. Authentication with PEAP-MSCHAPv2 access and admin PAP/ASCII wireless.
Problem:
Wireless users cannot authenticate to the announcement through ISE. This is the error message '11051 RADIUS packet contains invalid state attribute' & '24444 Active Directory failed because of an error that is not specified in the ISE'.
Conducted a detailed test of the AD of the ISE. The test was a success and the result seems fine except for the below:
xxdc01.XX.com (10.21.3.1)
Ping: 0 Mins Ago
Status: down
xxdc02.XX.com (10.21.3.2)
Ping: 0 Mins Ago
Status: down
xxdc01.XX.com
Last success: Thu Jan 1 10:00 1970
March 11 failure: read 11:18:04 2013
Success: 0
Chess: 11006
xxdc02.XX.com
Last success: Fri Mar 11 09:43:31 2013
March 11 failure: read 11:18:04 2013
Success: 25
Chess: 11006
Domain controller: xxdc02.xx.com:389
Domain controller type: unknown functional level DC: 5
Domain name: xx.COM
IsGlobalCatalogReady: TRUE
DomainFunctionality: 2 = (DS_BEHAVIOR_WIN2003)
ForestFunctionality: 2 = (DS_BEHAVIOR_WIN2003)
Action taken:
Log Cisco ISE and WLC by using the credentials of the AD. This excludes the connection AD, clock and AAA shared secret as the problem.
(2) wireless authentication tested using EAP-FAST, but same problem occurs.
(3) detailed error message shows below. This excludes any authentication and authorization policies. Even before hitting the authentication policy, the AD search fails.
12304 extract EAP-response containing PEAP stimulus / response
11808 extracted EAP-response containing EAP - MSCHAP VERSION challenge response to the internal method and accepting of EAP - MSCHAP VERSION such as negotiated
Evaluate the politics of identity
15006 set default mapping rule
15013 selected identity Store - AD1
24430 Authenticating user in Active Directory
24444 active Directory operation failed because of an error that is not specified in the ISE
(4) enabled the registration of debugging AD and had a look at the logging. Nothing significant, and no clue about the problem.
(5) wireless tested on different mobile phones with the same error and laptos
(6) delete and add new customer/features of AAA Cisco ISE and WLC
(7) ISE services restarted
(8) join domain on Cisco ISE
(9) notes of verified version of ISE 1.1.3 and WLC 7.2.111.3 for any open caveats. Find anything related to this problem.
10) there are two ISE and two deployed WLC. Tested a different combination of ISE1 to WLC1, ISE1 to WLC2, etc. This excludes a hardware problem of WLC.
Other possibilities/action:
1) test it on another version WLC. Will have to wait for approval of the failure to upgrade the WLC software.
(2) incompatibility between Cisco ISE and AD running on Microsoft Windows Server 2012
Did he experienced something similar to have ideas on why what is happening?
Thank you.
Update:
(1) built an another Cisco ISE 1.1.3 sever in another data center that uses the same domain but other domain controller. Thai domain controller running Windows Server 2008. This work and successful authentication.
(2) my colleague tested in a lab environment Cisco ISE 1.1.2 with Windows Server 2012. He has had the same problem as described.
This leads me to think that there is a compatibility issue of Cisco ISE with Windows Server 2012.
Yes, it seems that 1.1.3 doesn't support Server 2012 as of yet.
External identity Source OS/Version
Microsoft Windows Active Directory 2003 R2 32-bit and 64-bit
Active Directory Microsoft Windows 2008 32-bit and 64-bit
Microsoft Windows Active Directory 2008 R2 64-bit only
Microsoft Windows Active Directory 2003 32-bit only
http://www.Cisco.com/en/us/docs/security/ISE/1.1/compatibility/ise_sdt.PDF
-
I am very new to Cisco ISE and Meraki. I try to get the Radius configuration for wireless authentication. When I do a test of the Meraki to ISE, it passes.
When I try to connect from my laptop, I look at the logs of the Radius and it passes; However, it does not connect me to good policy. I keep hitting the default policy. I have my Meraki police above the default policy in the strategy defined in article. I have attached what looks like my strategy game.
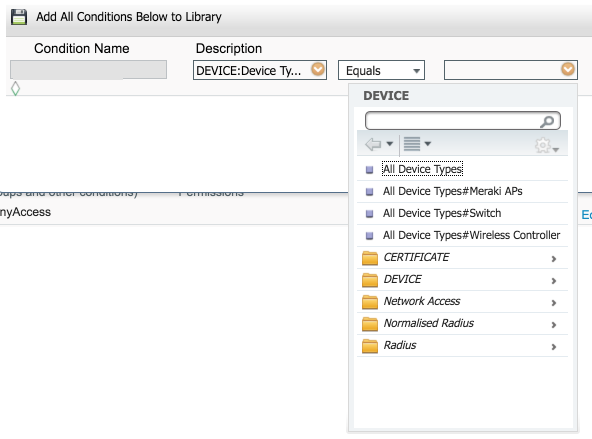
Devices does not really matter. Here is what I see when I create a device group (where you add the access point to this group), and then create the condition:
And here is where I create the condition of strategy game and you should be able to select the Meraki access points:
This will give you the condition similar to what I posted above. This is perhaps why you aren't hit that is not matching the condition for this game.
-
Hello!!
We are working on a mapping between a promoter Cisco ISE group and a user group in Active Directory, but the customer wants the mapping through a RADIUS SERVER, to avoid the ISE by querying directly activate Directory.
I know it is possible to use a RADIUS SERVER as source of external identity for ISE... but, is possible to use this RADIUS SERVER for this sponsor group manages?
Thank you and best regards!
Hi Rodrigo,
The answer is no. There is no way to integrate the portal Sponsor config with a RADIUS server. Your DB for authentication Portal Sponsor options;
AD
LDAP
User internal ISE DBSent by Cisco Support technique iPhone App
-
ISE license consumption and freeing licenses [RADIUS]
Hi people EHT,.
There are a lot of questions of ISE issued by me in the last time. And guess what - another here.
I wonder how the ISE license consumption and freeing licenses actually works. At least I have not find any good document or post on it.
From what I understand, a license (no matter if basic, plus, apex whatever) is consumed based on RADIUS accounting messages.
Example:
An endpoint is authenticating and allowed successfully with 802. 1 X without profiling or posture or whatever (simple). The ISE knows that this endpoint must use a base license and basic license consumption is increased by one.
As soon as the client is disconnected from the network, the n (switch, WLC) sends an accounting stop message to the ISE and the ISE again releases the base license.
(am I right so far?)
Assuming that I am just using the example above:
RADIUS is not say that really reliable. No matter that it uses UDP (which is unreliable), RAY has a mechanism of recognition built in (Accouting request / respone). But this mechanism gives up after a few attempts. Suppose that a client is disconnected, but the message of stop RADIUS is not received by the ISE.
Fact the endpoint stay forever in the State of the current session and therefore to consume a license forever? (Assume that there is no timer of dot1x re-authentication).
Or is it a mechanism of 'time-out' for endpoint licences?
Kind of a side story here:
I wrote a simple wrapper for the freeradius tool 'eapol_test '. Go Linux applications unique command line EAP (e.g., EAP - TLS) can be issued to a RADIUS server. If the Linux client acts as "supplicant" X 802.1 and authenticator. It's cool to quickly test the availability of the service of an authentication server.
My simple wrapper for "eapol_test" performs a ping 'EAP' at the time of convergence of measurement and measurement of authentications per second in a lab environment. The wrapper can also change endpoint of each session of RAY MAC. When I do ping EAP in a laboratory of my number of licenses on the ISE exploded, because eapol_test does not deliver messages from accounting RADIUS to EHT :)
Johannes has soon
Hi Johannes-
You're right about the consumption of license:
Licenses are counted against concurrent, active sessions. An active session is one for which a RADIUS Accounting Start is received but RADIUS Accounting Stop has not yet been received.
However, in addition to this:Note Sessions without RADIUS activity are automatically purged from Active Session list every 5 days or if the endpoint is deleted from the system.
This information used in the documentation of ISE 1.x, but for some reason, he is not :) in the 2.x here's the info from 1.2: http://www.cisco.com/c/en/us/td/docs/security/ise/1-2/installation_guide/ise_ig/ise_app_d_man_license.pdf I hope this helps! Thank you for the useful job evaluation!
Maybe you are looking for
-
Problems of updating Flash from Adobe
I constantly get popups saying "firefox has prevented the obsolete plugin adobe flash of opening", but I can't seem to update the plugin. I tried to go through firefox for the website https://www.mozilla.org/en-US/plugincheck/ , but all I get is a sp
-
Hello I use Mid 2014 Macbook Pro retina 15' Always work off OS X 10.9.5 Logic Pro X 10.2.2 IO: Avid Fast Track Duo KRK Rokit 5 and low KRK subwoofer So whenever I use logical just to do everything which, in perhaps the second time all my audio coming
-
How can I know what power adapter is mine since we both have the same for macbook pro 2013?
I mixed my adapter upward with my friend and we both have the same adapter for macbook pro and mine is almost more recent than its adapter. I need to know how can I know who is mine?
-
Option of film available, but does not work
When you choose a view in any folder with photos, I can choose "film". Until very recently, it worked well. Now, it seems, however, the preview pane is missing and all my pictures form a long horizontal "thumbnail" view top (similar to what is usuall
-
Pavilion dv7 - 4263cl: hard drive problems
Long story short, OS could not start windows with a missing BOOTMGR message, recovery disc, not work, ordered new HP recovery disks. To cover, I ordered a new hard drive to replace it, with the same characteristics but a 1 Toshiba to. OK, installed