problem of ipsec ASA
Hello
During the configuration of ipsec between ASA and SRI 1811 tunnel, I have a few
negative questions:
PC host (192.168.56.1) <----->(in 192.168.56.56) ASA (excluding x.x.x.56)
<------->(off x.x.x.55) SRI (lo 192.168.55.55)
When I ping from SRI to ASA everyting is ok:
Source ip 192.168.56.1 SRI # ping 192.168.55.55
Type to abort escape sequence.
Send 5, echoes ICMP 100 bytes to 192.168.56.1, time-out is 2 seconds:
Packet sent with a source address of 192.168.55.55
.!!!!
ASA # sh isa his
ITS enabled: 1
Generate a new key SA: 0 (a tunnel report Active 1 and 1 to generate a new key during the generate a new key)
Total SA IKE: 1
1 peer IKE: x.x.x.55
Type: L2L role: answering machine
Generate a new key: no State: MM_ACTIVE
But in the vice versa ipsec tunnel is not established:
ASA # erase isa his
PC host # ping-c 2 192.168.55.55
PING 192.168.55.55 (192.168.55.55) 56 (84) bytes of data.
-192.168.55.55 - ping statistics
2 packets transmitted, 0 received, 100% packet loss, time 1010ms
and on the SAA, I saw track debugging messages:
Jun 02 03:18:07 [IKEv1]: unable to find political initiator IKE: Intf inside.
CBC: 192.168.56.1, Dst: 192.168.55.55
Jun 02 03:18:16 [IKEv1 DEBUG]: pitcher: received a message key acquisition, spi
0 x 0
Jun 02 03:18:16 [IKEv1]: unable to find political initiator IKE: Intf inside.
CBC: 192.168.56.1, Dst: 192.168.55.55
Jun 02 03:18:17 [IKEv1 DEBUG]: pitcher: received a message key acquisition, spi
0 x 0
Can someone help me with this problem?
Thank you.
Hello, I just noticed you are using a dynamic map, may I ask the reason for this?
I don't think you can be the "initiator" of a VPN session when using dynamic crypto maps, if you put the address of the remote peer, what benefit you earn using the dynamic encryption card?
Concerning
Farrukh
Tags: Cisco Security
Similar Questions
-
Strange problem in IPSec Tunnel - 8.4 NAT (2)
Helloo all,.
This must be the strangest question I've seen since the year last on my ASA.
I have an ASA 5540, who runs the code of 8.4 (2) without any problem until I ran into this problem last week and I spent sleepless nights with no resolution! Then, take a deep breath and here is a brief description of my setup and the problem:
A Simple IPSEC tunnel between my 8.4 (2) ASA 5540 and a Juniper SSG 140 6.3.0r9.0 (road OS based VPN) screen
The tunnel rises without any problem but the ASA refused to encrypt the traffic but it decrypts with GLORY!
Here are a few outputs debug, see the output and a package tracer output that also has an explanation of my problem of NAT WEIRD:
my setup - (I won't get into the details of encryption tunnel as my tunnel negotiations are perfect and returns from the outset when the ASA is configured as response only)
CISCO ASA - IPSec network details
LAN - 10.2.4.0/28
REMOTE NETWORK - 192.168.171.8/32
JUNIPER SSG 140 - IPSec networks details
ID OF THE PROXY:
LAN - 192.168.171.8/32
REMOTE NETWORK - 10.2.4.0/28
Name host # sh cry counterpart his ipsec
peer address:
Tag crypto map: outside_map, seq num: 5, local addr:
outside_cryptomap_4 to access extended list ip 10.2.4.0 allow 255.255.255.240 host 192.168.171.8
local ident (addr, mask, prot, port): (10.2.4.0/255.255.255.240/0/0)
Remote ident (addr, mask, prot, port): (192.168.171.8/255.255.255.255/0/0)
current_peer:
#pkts program: encrypt 0, #pkts: 0, #pkts digest: 0
#pkts decaps: 72, #pkts decrypt: 72, #pkts check: 72
compressed #pkts: 0, unzipped #pkts: 0
#pkts uncompressed: 0, comp #pkts failed: 0, #pkts Dang failed: 0
success #frag before: 0, failures before #frag: 0, #fragments created: 0
Sent #PMTUs: 0, #PMTUs rcvd: 0, reassembly: 20th century / of frgs #decapsulated: 0
#send errors: 0, #recv errors: 0
local crypto endpt. :
0, remote Start. crypto: 0 Path mtu 1500, fresh ipsec generals 58, media, mtu 1500
current outbound SPI: 5041C19F
current inbound SPI: 0EC13558
SAS of the esp on arrival:
SPI: 0x0EC13558 (247543128)
transform: esp-3des esp-sha-hmac no compression
running parameters = {L2L, Tunnel}
slot: 0, id_conn: 22040576, crypto-card: outside_map
calendar of his: service life remaining key (s): 3232
Size IV: 8 bytes
support for replay detection: Y
Anti-replay bitmap:
0xFFFFFFFF to 0xFFFFFFFF
outgoing esp sas:
SPI: 0x5041C19F (1346486687)
transform: esp-3des esp-sha-hmac no compression
running parameters = {L2L, Tunnel}
slot: 0, id_conn: 22040576, crypto-card: outside_map
calendar of his: service life remaining key (s): 3232
Size IV: 8 bytes
support for replay detection: Y
Anti-replay bitmap:
0x00000000 0x00000001
CONTEXTS for this IPSEC VPN tunnel:
# Sh asp table det vpn context host name
VPN CTX = 0x0742E6BC
By peer IP = 192.168.171.8
Pointer = 0x78C94BF8
State = upwards
Flags = BA + ESP
ITS = 0X9C28B633
SPI = 0x5041C19D
Group = 0
Pkts = 0
Pkts bad = 0
Incorrect SPI = 0
Parody = 0
Bad crypto = 0
Redial Pkt = 0
Call redial = 0
VPN = filter
VPN CTX = 0x07430D3C
By peer IP = 192.168.1.8
Pointer = 0x78F62018
State = upwards
Flags = DECR + ESP
ITS = 0X9C286E3D
SPI = 0x9B6910C5
Group = 1
Pkts = 297
Pkts bad = 0
Incorrect SPI = 0
Parody = 0
Bad crypto = 0
Redial Pkt = 0
Call redial = 0
VPN = filter
outside_cryptomap_4 to access extended list ip 10.2.4.0 allow 255.255.255.240 host 192.168.171.8
NAT (inside, outside) static source Ren - Ren - about destination static counterpart-host peer to route non-proxy-arp-search
network of the Ren - around object
subnet 10.2.4.0 255.255.255.240
network of the host object counterpart
Home 192.168.171.8
HS cry ipsec his
IKE Peer:
Type: L2L role: answering machine
Generate a new key: no State: MM_ACTIVE
output packet tracer extracted a packet transmitted by the network of 10.2.4.0/28 to 192.168.171.8 host
Phase: 7
Type: VPN
Subtype: encrypt
Result: ALLOW
Config:
Additional information:
Direct flow from returns search rule:
ID = 0x7789d788, priority = 70, domain = encrypt, deny = false
Hits = 2, user_data is0x742e6bc, cs_id = 0x7ba38680, reverse, flags = 0 x 0 = 0 protocol
IP/ID=10.2.4.0 SRC, mask is 255.255.255.240, port = 0
IP/ID=192.168.171.8 DST, mask is 255.255.255.255, port = 0, dscp = 0 x 0
input_ifc = none, output_ifc = external
VPN settings corresponding to the encrytpion + encapsulation and the hits here increment only when I run a test of tracer from my host on the remote peer inside package.
A tracer complete package out for a packet of the 10.2.4.1 255.255.255.255 network to host 192.168.171.8:
Phase: 1
Type: ACCESS-LIST
Subtype:
Result: ALLOW
Config:
Implicit rule
Additional information:
Direct flow from returns search rule:
ID = 0x77ebd1b0, priority = 1, domain = allowed, deny = false
hits = 3037156, user_data = 0 x 0, cs_id = 0 x 0, l3_type = 0 x 8
Mac SRC = 0000.0000.0000, mask is 0000.0000.0000
DST = 0000.0000.0000 Mac, mask is 0100.0000.0000
input_ifc = output_ifc = any to inside,
Phase: 2
Type:-ROUTE SEARCH
Subtype: entry
Result: ALLOW
Config:
Additional information:
in 192.168.171.0 255.255.255.0 outside
Phase: 3
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional information:
Direct flow from returns search rule:
ID = 0x77ec1030, priority = 0, sector = inspect-ip-options, deny = true
hits = 212950, user_data = 0 x 0, cs_id = 0 x 0, reverse, flags = 0 x 0 = 0 protocol
IP/ID=0.0.0.0 SRC, mask is 0.0.0.0, port = 0
IP/ID=0.0.0.0 DST, mask is 0.0.0.0, port = 0, dscp = 0 x 0
input_ifc = output_ifc = any to inside,
Phase: 4
Type:
Subtype:
Result: ALLOW
Config:
Additional information:
Direct flow from returns search rule:
ID = 0x7c12cb18, priority = 18, area = import-export flows, deny = false
hits = 172188, user_data = 0x78b1f438, cs_id = 0 x 0, use_real_addr, flags = 0 x 0,
IP/ID=0.0.0.0 SRC, mask is 0.0.0.0, port = 0
IP/ID=0.0.0.0 DST, mask is 0.0.0.0, port = 0, dscp = 0 x 0
input_ifc = output_ifc = any to inside,
Phase: 5
Type: NAT
Subtype:
Result: ALLOW
Config:
NAT (inside, outside) static source Ren - Ren - about destination static counterpart-host peer to route non-proxy-arp-search
Additional information:
Definition of static 10.2.4.1/2700 to 10.2.4.1/2700
Direct flow from returns search rule:
ID = 0x77e0a878, priority = 6, area = nat, deny = false
hits = 9, user_data is 0x7b7360a8, cs_id = 0 x 0, use_real_addr, flags = 0 x 0, proto
IP/ID=10.2.4.1 SRC, mask is 255.255.255.240, port = 0
IP/ID=192.168.171.8 DST, mask is 255.255.255.255, port = 0, dscp = 0 x 0
input_ifc = inside, outside = output_ifc
(it's the weird NAT problem I see. I see the number of hits is increment only when I run the packet tracer understands even I have pings (traffic) the 192.168.171.8 constant welcomes the 10.2.4.1/28)-s'il please see the package I pasted after the capture section)
Phase: 6
Type: VPN
Subtype: encrypt
Result: ALLOW
Config:
Additional information:
Direct flow from returns search rule:
ID = 0x7b8751f8, priority = 70, domain = encrypt, deny = false
hits = 3, user_data = 0x7432b74, cs_id = 0x7ba38680, reverse, flags = 0 x 0, proto
IP/ID=10.2.4.1 SRC, mask is 255.255.255.240, port = 0
IP/ID=192.168.171.8 DST, mask is 255.255.255.255, port = 0, dscp = 0 x 0
input_ifc = none, output_ifc = external
Phase: 7
Type: VPN
Subtype: ipsec-tunnel-flow
Result: ALLOW
Config:
Additional information:
Reverse flow from returns search rule:
ID = 0x78b0c280, priority = 69 = ipsec-tunnel-flow area, deny = false
hits = 154, user_data is 0x7435f94, cs_id = 0 x 0, reverse, flags = 0 x 0 = 0 protocol
IP/ID=192.168.171.8 SRC, mask is 255.255.255.255, port = 0
IP/ID=10.2.4.1 DST, mask is 255.255.255.240, port = 0, dscp = 0 x 0
input_ifc = out, output_ifc = any
Phase: 8
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional information:
Reverse flow from returns search rule:
ID = 0x77e7a510, priority = 0, sector = inspect-ip-options, deny = true
hits = 184556, user_data = 0 x 0, cs_id = 0 x 0, reverse, flags = 0 x 0 = 0 protocol
IP/ID=0.0.0.0 SRC, mask is 0.0.0.0, port = 0
IP/ID=0.0.0.0 DST, mask is 0.0.0.0, port = 0, dscp = 0 x 0
input_ifc = out, output_ifc = any
Phase: 9
Type: CREATING STREAMS
Subtype:
Result: ALLOW
Config:
Additional information:
New workflow created with the 119880921 id, package sent to the next module
Information module for forward flow...
snp_fp_tracer_drop
snp_fp_inspect_ip_options
snp_fp_tcp_normalizer
snp_fp_translate
snp_fp_adjacency
snp_fp_encrypt
snp_fp_fragment
snp_ifc_stat
Information for reverse flow...
snp_fp_tracer_drop
snp_fp_inspect_ip_options
snp_fp_ipsec_tunnel_flow
snp_fp_translate
snp_fp_tcp_normalizer
snp_fp_adjacency
snp_fp_fragment
snp_ifc_stat
Result:
input interface: inside
entry status: to the top
entry-line-status: to the top
output interface: outside
the status of the output: to the top
output-line-status: to the top
Action: allow
Hostname # sh Cap A1
8 packets captured
1: 12:26:53.376033 192.168.10.252 > 10.2.4.1: icmp: echo request
2: 12:26:53.376597 10.2.4.1 > 192.168.10.252: icmp: echo reply
3: 12:26:56.487905 192.168.171.8 > 10.2.4.1: icmp: echo request
4: 12:27:01.489217 192.168.171.8 > 10.2.4.1: icmp: echo request
5: 12:27:03.378245 192.168.10.252 > 10.2.4.1: icmp: echo request
6: 12:27:03.378825 10.2.4.1 > 192.168.10.252: icmp: echo reply
7: 12:27:06.491597 192.168.171.8 > 10.2.4.1: icmp: echo request
8: 12:27:11.491856 192.168.171.8 > 10.2.4.1: icmp: echo request
8 packets shown
As you can see, there is no echo response packet at all because the package may not be wrapped while he was sent to.
I'm Karen with it. In addition, he is a firewall multi-tenant live production with no problems at all outside this for a Juniper ipsec tunnel!
Also, the 192.168.10.0/24 is another remote network of IPSec tunnel to this network of 10.2.4.0/28 and this IPSEC tunnel has a similar Juniper SSG 140 screen os 6.3.0r9.0 at the remote end and this woks like a charm with no problems, but the 171 is not be encrypted by the ASA at all.
If someone could help me, that would be greatt and greatly appreciated!
Thanks heaps. !
Perfect! Now you must find something else inside for tomorrow--> forecast rain again
Please kindly marks the message as answered while others may learn from it. Thank you.
-
Problem with IPsec VPN between ASA and router Cisco - ping is not response
Hello
I don't know because the IPsec VPN does not work. This is my setup (IPsec VPN between ASA and R2):
my network topology data:
LAN 1 connect ASA - 1 (inside the LAN)
PC - 10.0.1.3 255.255.255.0 10.0.1.1
ASA - GigabitEthernet 1: 10.0.1.1 255.255.255.0
-----------------------------------------------------------------
ASA - 1 Connect (LAN outide) R1
ASA - GigabitEthernet 0: 172.30.1.2 255.255.255.252
R1 - FastEthernet 0/0: 172.30.1.1 255.255.255.252
---------------------------------------------------------------------
R1 R2 to connect
R1 - FastEthernet 0/1: 172.30.2.1 255.255.255.252
R2 - FastEthernet 0/1: 172.30.2.2 255.255.255.252
R2 for lan connection 2
--------------------------------------------------------------------
R2 to connect LAN2
R2 - FastEthernet 0/0: 10.0.2.1 255.255.255.0
PC - 10.0.2.3 255.255.255.0 10.0.2.1
ASA configuration:
1 GigabitEthernet interface
nameif inside
security-level 100
IP 10.0.1.1 255.255.255.0
no downtime
interface GigabitEthernet 0
nameif outside
security-level 0
IP 172.30.1.2 255.255.255.252
no downtime
Route outside 0.0.0.0 0.0.0.0 172.30.1.1------------------------------------------------------------
access-list scope LAN1 to LAN2 ip 10.0.1.0 allow 255.255.255.0 10.0.2.0 255.255.255.0
object obj LAN
subnet 10.0.1.0 255.255.255.0
object obj remote network
10.0.2.0 subnet 255.255.255.0
NAT (inside, outside) 1 static source obj-local obj-local destination obj-remote control remote obj non-proxy-arp static-----------------------------------------------------------
IKEv1 crypto policy 10
preshared authentication
aes encryption
sha hash
Group 2
life 3600
Crypto ikev1 allow outside
crypto isakmp identity address------------------------------------------------------------
tunnel-group 172.30.2.2 type ipsec-l2l
tunnel-group 172.30.2.2 ipsec-attributes
IKEv1 pre-shared-key cisco123
Crypto ipsec transform-set esp-aes-192 ASA1TS, esp-sha-hmac ikev1-------------------------------------------------------------
card crypto ASA1VPN 10 is the LAN1 to LAN2 address
card crypto ASA1VPN 10 set peer 172.30.2.2
card crypto ASA1VPN 10 set transform-set ASA1TS ikev1
card crypto ASA1VPN set 10 security-association life seconds 3600
ASA1VPN interface card crypto outsideR2 configuration:
interface fastEthernet 0/0
IP 10.0.2.1 255.255.255.0
no downtime
interface fastEthernet 0/1
IP 172.30.2.2 255.255.255.252
no downtime-----------------------------------------------------
router RIP
version 2
Network 10.0.2.0
network 172.30.2.0------------------------------------------------------
access-list 102 permit ahp 172.30.1.2 host 172.30.2.2
access-list 102 permit esp 172.30.1.2 host 172.30.2.2
access-list 102 permit udp host 172.30.1.2 host 172.30.2.2 eq isakmp
interface fastEthernet 0/1
IP access-group 102 to------------------------------------------------------
crypto ISAKMP policy 110
preshared authentication
aes encryption
sha hash
Group 2
life 42300------------------------------------------------------
ISAKMP crypto key cisco123 address 172.30.1.2-----------------------------------------------------
Crypto ipsec transform-set esp - aes 128 R2TS------------------------------------------------------
access-list 101 permit tcp 10.0.2.0 0.0.0.255 10.0.1.0 0.0.0.255
------------------------------------------------------
R2VPN 10 ipsec-isakmp crypto map
match address 101
defined by peer 172.30.1.2
PFS Group1 Set
R2TS transformation game
86400 seconds, life of security association set
interface fastEthernet 0/1
card crypto R2VPNI don't know what the problem
Thank you
If the RIP is not absolutely necessary for you, try adding the default route to R2:
IP route 0.0.0.0 0.0.0.0 172.16.2.1
If you want to use RIP much, add permissions ACL 102:
access-list 102 permit udp any any eq 520
-
Problem with IPSEC tunnel between Cisco PIX and Cisco ASA
Hi all!
Have a strange problem with one of our tunnel ipsec for one of our customers, we can open the tunnel of the customers of the site, but not from our site, don't understand what's wrong, if it would be a configuration problem should can we not all up the tunnel.
On our side as initiator:
Jan 14 13:53:26 172.27.1.254% PIX-7-702208: ISAKMP Phase 1 Exchange started (local 1.1.1.1 (initiator), remote 2.2.2.2)
Jan 14 13:53:26 172.27.1.254% PIX-7-702210: Exchange of ISAKMP Phase 1 is complete (local 1.1.1.1 (initiator), remote 2.2.2.2)
Jan 14 13:53:26 172.27.1.254% 6-PIX-602202: ISAKMP connected session (local 1.1.1.1 (initiator), remote 2.2.2.2)
Jan 14 13:53:26 172.27.1.254% PIX-6-602201: Phase 1 ISAKMP Security Association created (local 1.1.1.1/500 (initiator), 2.2.2.2/500 remotely, authentication = pre-action, encryption = 3DES-CBC, hash = SHA, group = 2, life = 86400 s)
Jan 14 13:53:26 172.27.1.254% PIX-7-702209: ISAKMP Phase 2 Exchange started (local 1.1.1.1 (initiator), remote 2.2.2.2)
Jan 14 13:53:26 172.27.1.254% PIX-7-702201: ISAKMP Phase 1 delete received (local 1.1.1.1 (initiator), remote 2.2.2.2)
Jan 14 13:53:26 172.27.1.254% PIX-6-602203: ISAKMP disconnected session (local 1.1.1.1 (initiator), remote 2.2.2.2)
Jan 14 13:53:56 172.27.1.254% PIX-7-702303: sa_request, CBC (MSG key in English) = 1.1.1.1, dest = 2.2.2.2, src_proxy = 172.27.1.10/255.255.255.255/0/0 (type = 1), dest_proxy = 192.168.100.18/255.255.255.255/0/0 (type = 1), Protocol is ESP transform = lifedur hmac-sha-esp, esp-3des 28800 = s and 4608000 Ko, spi = 0 x 0 (0), id_conn = 0, keysize = 0, flags = 0 x 4004
The site of the customer like an answering machine:
14 jan 11:58:23 172.27.1.254% PIX-7-702208: ISAKMP Phase 1 Exchange started (local 1.1.1.1 (answering machine), 2.2.2.2 remote)
14 jan 11:58:23 172.27.1.254% PIX-7-702210: Exchange of ISAKMP Phase 1 is complete (local 1.1.1.1 (answering machine), 2.2.2.2 remote)
14 jan 11:58:23 172.27.1.254% 6-PIX-602202: ISAKMP connected session (local 1.1.1.1 (answering machine), 2.2.2.2 remote)
14 jan 11:58:23 172.27.1.254% PIX-6-602201: Phase 1 ISAKMP Security Association created (local 1.1.1.1/500 (answering machine), distance 2.2.2.2/500, authentication = pre-action, encryption = 3DES-CBC, hash = MD5, group = 1, life = 86400 s)
14 jan 11:58:23 172.27.1.254% PIX-7-702209: ISAKMP Phase 2 Exchange started (local 1.1.1.1 (answering machine), 2.2.2.2 remote)
14 jan 11:58:23 172.27.1.254% PIX-6-602301: its created, (his) sa_dest = 2.2.2.2, sa_prot = 50, sa_spi = 0x9de820bd (2649235645) sa_trans = sa_conn_id of hmac-sha-esp, esp-3des = 116
14 jan 11:58:23 172.27.1.254% PIX-7-702211: Exchange of ISAKMP Phase 2 is complete (local 1.1.1.1 (answering machine), 2.2.2.2 remote)
Jan 14 12:28:54 172.27.1.254% PIX-6-602302: SA deletion, (his) sa_dest = 2.2.2.2, sa_prot = 50, sa_spi = 0x9de820bd (2649235645), sa_trans = esp-3desesp-sha-hmac, sa_conn_id = 116
Kind regards
Johan
From my experience when a tunnel is launched on one side, but it is not on the other hand, that the problem is with an inconsistency of the isakmp and ipsec policies, mainly as ipsec policies change sets and corresponding address with ASA platform when a tunnel is not a statically defined encryption card he sometimes use the dynamic tag to allocate this vpn connection. To check if this is the case go ahead and make a "crypto ipsec to show his" when the tunnel is active on both sides, see on the SAA if the corresponding tunnel is the static encryption card set or if it presents the dynamic encryption card.
I advise you to go to the settings on both sides and ensure that they are both in the opposite direction.
-
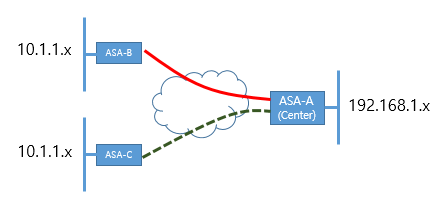
Currently, ASA - A (Center) and B has connected by VPN IPSec.
I would like a VPN establsh A ASA and ASA-C both.
But unfortunately, within the network range has same range B-ASA and ASA-C both. (10.1.1.x)
In this case, how can I connect IPSec VPN to ASA-B and C - ASA ASA - A at a time?
Thank you
Hello
You can go with policy subnet Nating ASA-C on another subnet on ASA - C (ex: 10.1.10.x) and use this as your ACL subnet subnet. It should work. Please search online for examples of configuration.
HTH
MS
-
Problems with ACL in config IPSec ASA-5504
I'm putting a tunnel IPSec between two ASA - 5540 s. There is a PC (SunMed_PC) behind the ASA-5540-B and a laptop (laptop-GHC) behind the ASA-5540-A. If the card encryption allows all IP, through the outside_cryptomap ACL, then the tunnel rises a FTP session is established.
But, when I restrict the following FTP, error message traffic is generated:
... Group = 164.72.1.147, IP = 164.72.1.147, IPSec tunnel rejecting: no entry for crypto for proxy card proxy remote 164.72.1.155/255.255.255.255/6/0 local 164.72.1.135/255.255.255.255/6/21 on the interface to the outside
Here's the configs giving only the relevant controls. I added the ACL 100 and "access-group 100 in the interface inside", but the error has not changed.
No idea what I'm missing?
CRO-ASA5540-A
names of
164.72.1.135 GHC_Laptop description name to test the VPN
164.72.1.155 SunMed_pc description name to test the VPN
!
interface GigabitEthernet0/0
nameif inside
security-level 100
IP 164.72.1.129 255.255.255.240
!
!
interface GigabitEthernet0/3
nameif outside
security-level 0
IP 164.72.1.145 255.255.255.248
!
passive FTP mode
DM_INLINE_TCP_1 tcp service object-group
port-object eq ftp
port-object eq ftp - data
access-list extended permits outside_cryptomap tcp ftp eq host GHC_Laptop host SunMed_pc object-group DM_INLINE_TCP_1
access-list 100 scope ip allow a whole
ASDM image disk0: / asdm - 603.bin
Access-group 100 in the interface inside
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
card crypto outside_map0 1 match address outside_cryptomap
outside_map0 card crypto 1jeu peer 164.72.1.147
outside_map0 card crypto 1jeu transform-set ESP-3DES-SHA
outside_map0 card crypto 1jeu nat-t-disable
outside_map0 interface card crypto outside
crypto ISAKMP allow outside
crypto ISAKMP policy 5
preshared authentication
3des encryption
sha hash
Group 2
life 86400
Group Policy Lan-2-Lan_only internal
attributes of Lan-2-Lan_only-group policy
VPN-filter no
Protocol-tunnel-VPN IPSec
tunnel-group 164.72.1.147 type ipsec-l2l
tunnel-group 164.72.1.147 General-attributes
Group Policy - by default-Lan-2-Lan_only
IPSec-attributes tunnel-group 164.72.1.147
pre-shared-key *.
!
: end
----------------------------------------------------------------------------------------------------------
ROC-ASA5540-B # sh run
ASA Version 8.0 (3)
!
names of
name 164.72.1.135 GHC_laptop
name 164.72.1.155 SunMed_PC
!
interface GigabitEthernet0/0
nameif inside
security-level 100
IP 164.72.1.153 255.255.255.248
!
interface GigabitEthernet0/3
nameif outside
security-level 0
IP 164.72.1.147 255.255.255.248
!
passive FTP mode
DM_INLINE_TCP_1 tcp service object-group
port-object eq ftp
port-object eq ftp - data
outside_cryptomap list extended access permit tcp host host SunMed_PC GHC_laptop object-group DM_INLINE_TCP_1
access-list 100 scope ip allow a whole
ASDM image disk0: / asdm - 603.bin
Access-group 100 in the interface inside
Route outside 164.72.1.128 255.255.255.240 GHC-Medical 1
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
card crypto outside_map0 1 match address outside_cryptomap
outside_map0 card crypto peer GHC-Medical 1jeu
outside_map0 card crypto 1jeu transform-set ESP-3DES-SHA
outside_map0 card crypto 1jeu nat-t-disable
outside_map0 interface card crypto outside
crypto ISAKMP allow outside
crypto ISAKMP policy 4
preshared authentication
3des encryption
sha hash
Group 2
life 86400
internal Lan-2-Lan group strategy
Lan Lan 2-strategy of group attributes
Protocol-tunnel-VPN IPSec
tunnel-group 164.72.1.145 type ipsec-l2l
tunnel-group 164.72.1.145 General-attributes
strategy-group-by default 2 Lan Lan
IPSec-attributes tunnel-group 164.72.1.145
pre-shared-key *.
: end
Your acl mapped on the card encryption is suspect on the first device:
access-list extended permits outside_cryptomap tcp ftp eq host GHC_Laptop host SunMed_pc object-group DM_INLINE_TCP_1
The source port should not be defined because it
is dynamic.
The second acl appears corrected:
outside_cryptomap list extended access permit tcp host host SunMed_PC GHC_laptop object-group DM_INLINE_TCP_1
-
Intercept-dhcp works to tunnel L2TP through IPsec ASA?
Hello
Is there anyone in the world operating a tunnel L2TP through IPsec on Cisco ASA for the native Windows clients and a Tunnel Split Configuration fully functional?
I created a tunnel L2TP through IPsec on the ASA 5520 9.1 (6) Version of the software running. My configuration is:
mask 172.23.32.1 - 172.23.33.255 255.255.252.0 IP local pool VPN_Users
ROUTING_SPLIT list standard access allowed 192.168.0.0 255.255.0.0
ROUTING_SPLIT list standard access allowed 172.16.0.0 255.248.0.0Crypto ipsec transform-set esp-aes-256 WIN10, esp-sha-hmac ikev1
transport mode encryption ipsec transform-set WIN10 ikev1
Crypto ipsec transform-set esp-3des esp-sha-hmac WIN7 ikev1
Crypto ipsec transform-set transport WIN7 using ikev1
Dynamic crypto map DYNMAP 10 set transform-set WIN10 WIN7 ikev1
Crypto dynamic-map DYNMAP 10 the value reverse-road
card crypto CMAP 99-isakmp dynamic ipsec DYNMAP
CMAP interface ipsec crypto mapCrypto isakmp nat-traversal 29
crypto ISAKMP disconnect - notify
Ikev1 enable ipsec crypto
IKEv1 crypto policy 10
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400
output
IKEv1 crypto policy 20
preshared authentication
3des encryption
sha hash
Group 2
life 86400
outputinternal EIK_USERS_RA group policy
EIK_USERS_RA group policy attributes
value of 12.34.56.7 DNS Server 12.34.56.8
VPN - connections 2
L2TP ipsec VPN-tunnel-Protocol ikev1
disable the password-storage
enable IP-comp
enable PFS
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list ROUTING_SPLIT
ad.NYME.Hu value by default-field
Intercept-dhcp enable
the authentication of the user activation
the address value VPN_Users pools
outputattributes global-tunnel-group DefaultRAGroup
authentication-server-group challenger
accounting-server-group challenger
Group Policy - by default-EIK_USERS_RA
IPSec-attributes tunnel-group DefaultRAGroup
IKEv1 pre-shared-key *.
tunnel-group DefaultRAGroup ppp-attributes
No chap authentication
no authentication ms-chap-v1
ms-chap-v2 authentication
outputNow, the native Windows clients can connect using this group of tunnel:
our - asa # show remote vpn-sessiondb
Session type: IKEv1 IPsec
User name: w10vpn Index: 1
Assigned IP: 172.23.32.2 public IP address: 12.34.56.9
Protocol: IKEv1 IPsecOverNatT L2TPOverIPsecOverNatT
License: Another VPN
Encryption: IKEv1: (1) 3DES IPsecOverNatT: (1) L2TPOverIPsecOverNatT AES256: (1) no
Hash: IKEv1: (1) IPsecOverNatT SHA1: (1) L2TPOverIPsecOverNatT SHA1: (1) no
TX Bytes: 1233 bytes Rx: 10698
Group Policy: Group EIK_USERS_RA Tunnel: DefaultRAGroup
Connect time: 15:12:29 UTC Friday, April 8, 2016
Duration: 0: 00: 01:00
Inactivity: 0 h: 00 m: 00s
Result of the NAC: unknown
Map VLANS: VLAN n/a: noHowever, real communication takes place above the tunnel if I 'Gateway on remote network use default'. If I disable this option among the preferences of the IPv4 of the virtual interface of VPN in Control Panel as described in the section 'Configuration of Tunnel of Split' of This DOCUMENT then Windows sends all packets through the channel, because it fails to extract from the ASA routing table. Split routing works perfectly when using legacy Cisco VPN Client with the same group policy, but does not work with L2TP over IPsec.
As far as I can see, the 'intercept-dhcp' option is inefficient somehow. I even managed to intercept packets of the PPP virtual machine Windows XP interface, and I saw that windows sends its DHCP INFORM requests, but the ASA does not. My question is why?
-J' made a mistake in the above configuration?
-Can there be one option somewhere else in my config running that defuses intercept-dhcp?
- Or is there a software bug in my version of firmware ASA? (BTW, I tried with several versions of different software without success?
Hi, I have the same problem you have, but I was lucky enough to be able to install version 9.2 (4) on which this feature works very well. I'm suspecting that it is a bug, but I need to dig a little deeper. If I find something interesting I'll share it here.
-
"ITS creation failed" problem for IPSec VPN
An ASA 5100 is used to provide VPN access for my business. The configuration was made by a permeable man who has been missing for some time, and the configuration used to be OK until this morning. This morning, some users reported that their VPN would have fallen once got connected. I checked the ASA and ASDM, I see every time when user deletes, it IPSec tunnel is always action. Furthermore, I faked the problem and got the newspaper of errors such as:
1 11:14:45.898 12/06/07 Sev = WARNING/3 IKE/0xE3000065 could not find an IKE SA for 10.2.1.8. Abandoned KEY_REQ.
2 11:14:45.898 12/06/07 Sev = WARNING/2 IKE/0xE3000099 could not open the P2 generate a new key: error detected(Initiate:176)
3 11:14:45.898 12/06/07 Sev = WARNING/2 IKE/0xE3000099 cannot open the QM (IKE_MAIN:458)
On the side of the AS I did "debug crypto isakmp" and 'debug crypto ipsec' and I got the following errors:
iscoasa # ERROR IPSEC: expiration of the timer of the asynchronous operation, SPI: 0x114CA5B6, user: roeladmin, peer: 202.x.x.70, time: 2 seconds, ctm_ipsec_create_sa:856
IPSEC ERROR: Material outside ITS create command failed, SPI: 0x114CA5B6, error code: 0 x 17
IPSEC ERROR: Asynchronous Operation timeout expired, SPI: 0x61BE2022, user: roeladmin, peer: 202.x.x.70, time: 2 seconds, ctm_ipsec_create_sa:856
IPSEC ERROR: Cannot add a user auth, SPI input: 0x61BE2022, user: roeladmin, peer: 202.172.62.70
IPSEC ERROR: Cannot create an inbound SA SPI: 0x61BE2022 document
IPSEC ERROR: Unable to complete the command of IKE UPDATE
12 June at 14:25:13 [IKEv1]: Group = LANWORKS, Username = roeladmin, IP = 202.172.62.70, error QM WSF (P2 struct & 0 x 4699058, mess id 0xf37ec6f4).
12 June at 14:25:13 [IKEv1]: Group = LANWORKS, Username = roeladmin, IP = 202.172.62.70, peer table correlator Removing failed, no match!
IPSEC ERROR: Material Inbound ITS create command failed, SPI: 0x61BE2022, error code: 0 x 17
It shows that ITS creation has failed. But I can't find the problem with the configuration. Can someone help me on this? Thank you
Outgoing material ITS create command failed, SPI: 0x114CA5B6, error code: 0 x 17
It is a hardware problem, reset the firewall and it will work, I saw 4 times in different ASAs
Please hate the post if help.
-
VPN router to the problem of the ASA
Hello world.
I am doing a VPN between a router and a series of ASA5500 and difficulties.
The router part is 100% correct because it is a daily task, but miss me something on the side of the ASA of the things.
The ASA also has remote via IPsec tunnels clients as you'll see below, so I have to make sure that continues to work!
It is a fairly urgent question. So any help or advice can be provided, it would be very appreciated!
Here is the router part:
!
crypto ISAKMP policy 1
BA 3des
preshared authentication
Group 2
isakmp encryption key * ASA-PUBLIC-IP address
ISAKMP crypto keepalive 100
!
!
Crypto ipsec transform-set transform-set esp-3des esp-md5-hmac
!
10 customers map ipsec-isakmp crypto
defined ASA-PUBLIC-IP peer
transform-set transform-Set
match address 102
QoS before filing
!
!
Access-list 100 remark [== NAT control ==]
access-list 100 deny ip 192.168.2.0 0.0.0.255 10.1.1.0 0.0.0.255
access-list 100 permit ip 192.168.2.0 0.0.0.255 any
Access-list 102 remark == [VPN access LISTS] ==
access-list 102 permit ip 192.168.2.0 0.0.0.255 10.1.1.0 0.0.0.255
Access-list 102 remark
(Crypto card has been applied to the corresponding interface)
SIDE OF THE ASA:
permit inside_nat0_outbound to access extended list ip 10.1.1.0 255.255.255.0 10.1.1.192 255.255.255.224
prevpn_splitTunnelAcl list standard access allowed 10.1.1.0 255.255.255.0
access-list Interior-access-in extended permit ip 10.1.1.0 255.255.255.0 any
access-list Interior-access-in extended permit icmp 10.1.1.0 255.255.255.0 any
access list for distance-extended permitted ip network 10.1.1.0 255.255.255.0 192.168.2.0 255.255.255.0
Global (outside) 1 ASA-PUBLIC-IP
NAT (inside) 0-list of access inside_nat0_outbound
NAT (inside) 1 10.1.1.0 255.255.255.0
NAT (inside) 0 192.168.2.0 255.255.255.0
Crypto ipsec transform-set ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto-map dynamic outside_dyn_map 20 the transform-set ESP-3DES-MD5 value
card crypto outside_map 40 match remote-network address
card crypto outside_map 40 game peers REMOTE-router-IP
outside_map card crypto 40 the transform-set ESP-3DES-MD5 value
map outside_map 65535-isakmp ipsec crypto dynamic outside_dyn_map
outside_map interface card crypto outside
ISAKMP allows outside
part of pre authentication ISAKMP policy 10
ISAKMP policy 10 3des encryption
ISAKMP policy 10 md5 hash
10 2 ISAKMP policy group
ISAKMP life duration strategy 10 86400
tunnel-group prevpn type ipsec-ra
tunnel-group prevpn General-attributes
address pool VPN-pool
Group Policy - by default-prevpn
prevpn group of tunnel ipsec-attributes
pre-shared-key *.
tunnel-group REMOTE-router-IP type ipsec-l2l
REMOTE-router-IP tunnel-group ipsec-attributes
pre-shared-key *.
Hi Chris
first on the router make this change to littil than u ned to add md5 as hashing whil employees u th in the asa and the router u did not, so the default is sha!
do
crypto ISAKMP policy 1
md5 hash
now on the SAA as I see that there is a problem in nat0 you line l2l tunnel
so that you need to look like:
permit inside_nat0_outbound to access extended list ip 10.1.1.0 255.255.255.0 192.168.2.0 255.255.255.0
You also need a permit for the ipsec traffic, the following command will allow all ipsec traffic if you want to filter traffic not to use this command and use rather ACLs on the external interface, but following that to allow all traffic to your L2L and remote vpn access:
Permitted connection ipsec sysopt
so, please:
clear xlate and reload the ASA then attempt to leave the expmtion NAT new effects
Good luck
If useful rates
-
How to configure bandwidth allowed on the VPN IPSec ASA tunnels?
ASA 5505 8.2.1
ASA 5520 8.4
We currently have a tunnel set up between 2 ASAs
is 1 - possible to assign 1.5 Mbps of Bandwidth (BW) to this tunnel? Then if Tunnel number 2 is set up I could assign 2 Mbit to this one for example?
I'm not talking to prioritize certain type of traffic on the IPsec tunnel, I'm talking about Tunnel 1 to 1.5 Mbps of BW guaranteed for all traffic that passes through it. Same for tunnel 2
Then
2-How do to control the quantity of biological weapons in an IPsec tunnel?
Please provide documentation possible
Thank you
Johnny
Hello! Please consult this document:
https://supportforums.Cisco.com/docs/doc-1230
___
HTH. Please rate this post if this has been helpful. If it solves your problem, please mark this message as "right answer".
-
Need help, a problem with IPSec and NAT - T
We had a successful between a Cisco remote access client and the ASA connection. The connection is more data transfer, but the Phase I and Phase II complete successfully. There are several sections between separate networks for the remote user to the ASA, including hotlines of Verizon and Verizon's ISP.
Troubleshooting Cisco guides strongly suggests, it is a problem of NAT - T, but when I turn on debugging 254 isakmp and debug ipsec 254, I get only a modest messages on NAT - T, which is "Recieved NAT-Traversal version 02 VID. This message and connections, are when I disabled it on the ASA of NAT - T.
If I enable NAT - T on the SAA, the remote client cannot establish Phase I or II; I was not able to gather debugs on this scenerio yet.
The customer has a second laptop, both of them experience the same problem. We have ensured that the Tunneling, UPD 4500 is activated.
I suspect that an intermediary device or Verizon, changed something.
What should be my next troubleshooting (unfortunately, I can't post the configs)?
Kind regards
j
From my very limited experience, both sides must have the NAT - T enabled, otherwise the side who did not need NAT - t won't be able to read the part of the IP header because it is encrypted.
Good luck!
Pedro
-
VPN IPSEC ASA with counterpart with dynamic IP and certificates
Hello!
Someone please give me config the work of the ASA for ASA Site to Site IPSEC VPN with counterpart with dynamic IP and authentication certificates.
He works with PSK authentication. But the connection landed at DefaultRAGroup instead of DefaultL2LGroup with certificate
authentication.
Should what special config I ask a DefaultRAGroup to activate the connection?
Thank you!
The ASA uses parts of the client cert DN to perform a tunnel-group lookup to place the user in a group. When "peer-id-validate req" is defined the ASA also tries to compare the IKE ID (cert DN) with the actual cert DN (also received in IKE negotiation), if the comparison fails the connection fails. know you could set "peer-id-validate cert" for the time being and the ASA will try to compare the values but allow the connection if it cannot.
In general I would suggest using option "cert."
With nocheck, we are simply not strict on IKE ID matchin the certificate, which is normally not a problem of security :-)
-
Here's the scenario...
I have a client site with a network of VPN Cisco ASA 5505 with one IPSec tunnel to a VPN HQ.
I would like to introduce a 2nd tunnel from the customer site to another location of HQ who announces the same set of routes.
An ASA VPN point of view, what is the best way to do it?
Charge or a balancing approach active / standby will be acceptable.
IM curious to know how 2 static VPN tunnels will work side by side with the same cryptographic cards? It will even work?
I can it influence the use of good old routing mode?
Help! : P
Thank you!
D
Yes, that's where the second pair must be added.
-
Hello
I have a requirement to terminate VPN site-to-site on ASA5545 unit such as IPsec on a stick and the road through the Internet router (2911) within the network and vice versa. For now, router Internet is with all the ACL and nat for the company. Sooner or later, all the ACL and nat must be migrated to the new ASA unit.
Anyone can share ideas on that?
Thank you
.
Hello
Yes... I agree with your proposed... design rather crossed and do all the workaround solution, this would be the right method that will make things much simpler...
Even if it would be better if you bring ASA between router and switch basis... I mean internet side by side (outside) interface of ASA will face to router and LAN (inside) interface will connect to the router base... then you can make site to site and anyconnect configured on the SAA itself and you can make the router just do routing to the internet... But based on your current production and the impact you can decide how you want to migrate...
Concerning
Knockaert
-
VPN IPSec ASA with two ISP active
Hi ALL!
I have a question.
So I have ASA with 9.2 (1) SW connected to ISP with active SLA.
I need to configure redundant IPSec VPN via ISP2, while all other traffic must go through isps1. In case if one of the ISP goes down all including VPN traffic must be routed via ISP alive.
I have configured SLA and it works.
ciscoasa # display route performance
Route 0.0.0.0 isps1 0.0.0.0 10.175.2.5 5 track 1
Route isp2 0.0.0.0 0.0.0.0 10.175.3.5 10 track 2
Route isp2 172.22.10.5 255.255.255.255 10.175.3.5 1 excerpt 2Here we can see if isps1 and ISP2 are RISING, all traffic passes through isps1, but traffic intended for the remote peer IPSec 172.22.10.5 passes by ISP2.
This configuration works just at the moment when isps1 or isp2 is down or if a static route for 172.22.10.5 deleted. Where two Internet service providers are increasing to ASA does not send the next remote IPSec datagrams.
ciscoasa # display running nat
NAT (inside, isp2) source static obj-INSIDE_LAN obj-INSIDE_LAN destination static obj-REMOTE_LAN obj-REMOTE_LAN no-proxy-arp-search to itinerary
NAT (inside isps1) source static obj-INSIDE_LAN obj-INSIDE_LAN destination static obj-REMOTE_LAN obj-REMOTE_LAN no-proxy-arp-search to itineraryCrypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec pmtu aging infinite - the security association
card crypto cm_vpnc 10 correspondence address acl_vpn
card crypto cm_vpnc 10 set pfs
peer set card crypto cm_vpnc 10 172.22.10.5
card crypto cm_vpnc 10 set transform-set ESP-AES-256-SHA ikev1
86400 seconds, duration of life card crypto cm_vpnc 10 set - the security association
card crypto cm_vpnc interface isps1
cm_vpnc interface isp2 crypto card
trustpool crypto ca policy
isps1 enable ikev1 crypto
isp2 enable ikev1 crypto
IKEv1 crypto policy 1
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400ciscoasa # show ip
System of IP addresses:
Subnet mask IP address name interface method
Vlan1 in 192.168.2.1 255.255.255.0 CONFIG
Isps1 Vlan2 10.175.2.10 255.255.255.0 CONFIG
Isp2 Vlan3 10.175.3.10 255.255.255.0 CONFIGThe main question why?
Thank you in advance,
Anton
Hi anton,.
If you check the log message on your ASA R301-IS , he's trying to build the tunnel VPN with both IP and it receives packets of asymmetrically your distance ciscoasa.
TO avoid this asymmetrical connection, point your IP from peers as primary & secondary on your R301-EAST
set peer 10.175.3.10 10.175.2.10
Delete the track on your routing entries
Route isp2 172.22.10.5 255.255.255.255 10.175.3.5
This should work for you.
Similalry lower your ISP 2, you should see VPN tunnel is mounted with isps1 one.
HTH
Sandy
Maybe you are looking for
-
How to customize the 3 buttons on the front of the Portege R400?
I wonder if it is possible to customize the function of the three buttons on the front of my R400? For the moment, they seem to do nothing. I would use both of them as PgUp and PgDn display documents in tablet mode. Using the program "Toshiba button
-
I am looking to buy a new iMac in the near future and I wanted to know how slow 5400 RPM? I heard of some, the startup time is extremely slow and then I heard that there are no slow start of time at all and 5400 RPM is quite good for a student like m
-
computer not turns off after installing thinkpoint
-
to install important updates, but it keeps error643
I have norton already have it installed on my laptop but microsoft says it is mandatory to install the important updates? When I try this it keeps 634 ERROR being a future pensioner I do not understand what to do?
-
HP mini computer: Reset bios password
My hp mini is locked. Enter in password is the error. Help, please. Machine no is CNU9379KWL.