iPad App AnyConnect and Webproxy without Split Tunneling
Hello
Is it possible to use a web proxy server to make iPad VPN SSL connections to use an internal navigation proxy server when connected. Split tunneling is not allowed, but I want to allow users to be able to browse the internet through our internal proxy.
Is there a solution for this?
Thank you
You can look in the Internet EXPLORER on the SAA proxy feature which will allow you to set values of dynamic proxy for AnyConnect connection customers. This feature was originally designed for IE but has been tested to work with the iPhone and iPod Touch 4.1.
Todd
Tags: Cisco Security
Similar Questions
-
Hello everyone
I have setup a VPN connection, which I can connect to. For all customers of connection, I want to give them an IP (from a subnet maybe) and let them use this IP address for all that they do.
Therefore, this:
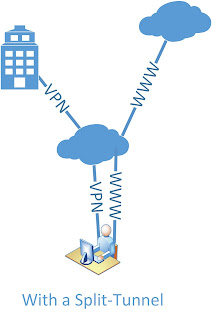
and not current:
My inside is 192.168.1.0
My VPN IP pool is 192.168.30.5 - 200
My server (DNS, files, Web site) is 192.168.1.222Here's my setup. I scored what I thought might have something to do with it:
ASA Version 9.2 (1)
!
ciscoasa hostname
activate 8Ry2YjIyt7RRXU24 encrypted password
volatile xlate deny tcp any4 any4
volatile xlate deny tcp any4 any6
volatile xlate deny tcp any6 any4
volatile xlate deny tcp any6 any6
volatile xlate deny udp any4 any4 eq field
volatile xlate deny udp any4 any6 eq field
volatile xlate deny udp any6 any4 eq field
volatile xlate deny udp any6 any6 eq field
2KFQnbNIdI.2KYOU encrypted passwd
names of
pool of IP local IP-pool 192.168.30.5 - 192.168.30.200 mask 255.255.255.0
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
IP 192.168.1.253 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
IP address dhcp setroute
!
boot system Disk0: / asa921 - k8.bin
passive FTP mode
permit same-security-traffic intra-interface
network obj_any object
subnet 0.0.0.0 0.0.0.0
network of the object Server-25
Home 192.168.1.222
Description of the test server
network of the object server-80
Home 192.168.1.222
Description of the test server
network of the object server-443
Home 192.168.1.222
Description of the test server
network of the object server-2525
Home 192.168.1.222
Description of the test server
network of the object server-993
Home 192.168.1.222
Description of the test server
network of the object server-6001
Home 192.168.1.222
Description of the test server
network of the object server-6002
Home 192.168.1.222
Description of the test server
network of the object server-6003
Home 192.168.1.222
Description of the test server
network of the object server-6004
Home 192.168.1.222
Description of the test server
network of the VPN HOST object
192.168.30.0 subnet 255.255.255.0
the object to the Interior-net network
host 192.168.1.0
the VPN server object network
Home 192.168.1.222
outside_access_in list extended access permit tcp any object Server-25 eq smtp
outside_access_in list extended access permit tcp any object server-2525 2525 eq
outside_access_in list extended access permit tcp any object server-80 eq www
outside_access_in list extended access permit tcp any object server-443 https eq
outside_access_in list extended access permit tcp any object server-993 993 eq
outside_access_in list extended access permit tcp any object server-6001 eq 6001
outside_access_in list extended access permit tcp any object server-6002 6002 eq
outside_access_in list extended access permit tcp any object server-6003 eq 6003
outside_access_in list extended access permit tcp any object server-6004 eq 6004
outside_access_in to access ip 192.168.1.0 scope list allow 255.255.255.0 192.168.30.0 255.255.255.0
permit access-list Split-Tunnel-ACL standard 192.168.30.0 255.255.255.0
no pager
Enable logging
asdm of logging of information
Within 1500 MTU
Outside 1500 MTU
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 721.bin
don't allow no asdm history
ARP timeout 14400
no permit-nonconnected arp
NAT (indoor, outdoor) Interior-net Interior-NET static source static destination HOST-VPN-VPN-HOST
NAT VPN VPN-server destination (indoor, outdoor) static static source HOST-VPN-VPN-HOST
!
network obj_any object
NAT dynamic interface (indoor, outdoor)
network of the object Server-25
NAT (inside, outside) interface static tcp smtp smtp service
network of the object server-80
NAT (inside, outside) interface static tcp www www service
network of the object server-443
NAT (inside, outside) interface static tcp https https service
network of the object server-2525
NAT (inside, outside) interface static 2525 2525 tcp service
network of the object server-993
NAT (inside, outside) interface static tcp 993 993 service
network of the object server-6001
NAT (inside, outside) interface static tcp 6001 6001 service
network of the object server-6002
NAT (inside, outside) interface static tcp 6002 6002 service
network of the object server-6003
NAT (inside, outside) interface static 6003 6003 tcp service
network of the object server-6004
NAT (inside, outside) interface static service tcp 6004 6004
Access-group outside_access_in in interface outside
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
RADIUS AAA server HSS-auth-server protocol
allow only
AAA-server HSS-auth-server (inside) host 192.168.1.222
Timeout 5
key *.
identity of the user by default-domain LOCAL
Enable http server
http 192.168.1.0 255.255.255.0 inside
No snmp server location
No snmp Server contact
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec pmtu aging infinite - the security association
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 define ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
outside_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
outside_map interface card crypto outside
trustpool crypto ca policy
Crypto isakmp nat-traversal 30
Crypto ikev1 allow outside
IKEv1 crypto policy 10
authentication crack
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 20
authentication rsa - sig
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 30
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 40
authentication crack
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 50
authentication rsa - sig
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 60
preshared authentication
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 70
authentication crack
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 80
authentication rsa - sig
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 90
preshared authentication
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 100
authentication crack
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 110
authentication rsa - sig
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 120
preshared authentication
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 130
authentication crack
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 140
authentication rsa - sig
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 150
preshared authentication
the Encryption
sha hash
Group 2
life 86400
Telnet timeout 5
SSH stricthostkeycheck
SSH timeout 5
SSH group dh-Group1-sha1 key exchange
Console timeout 0interface ID client DHCP-client to the outside
dhcpd outside auto_config
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
internal HSSvpn group strategy
attributes of Group Policy HSSvpn
value of server WINS 192.168.1.222
value of server DNS 192.168.1.222
Ikev1 VPN-tunnel-Protocol
Split-tunnel-policy tunnelall
Split-tunnel-network-list value Split-Tunnel-ACL
HSS.dk value by default-field
activate dns split-tunnel-all
type tunnel-group HSSvpn remote access
attributes global-tunnel-group HSSvpn
address IP-pool pool
HSS-auth-server authentication-server-group
Group Policy - by default-HSSvpn
password-management
IPSec-attributes tunnel-group HSSvpn
IKEv1 pre-shared-key *.
tunnel-group HSSvpn ppp-attributes
No chap authentication
no authentication ms-chap-v1
ms-chap-v2 authentication
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:c85ff8bf61669bef56b4dad704a4930a
: endHello
Change Split Tunnel VPN in full Tunnel VPN, you have really do much in your configuration.
Seems that have already changed you the 'tunnelspecified' 'tunnelall' in configurations of the 'group policy' . You can delete the setup but that defines the ACL of Split Tunnel
attributes of Group Policy HSSvpn
No split-tunnel-network-list value Split-Tunnel-ACLSeems that you use an internal AAA server to manage authentication rather than on the SAA. I guess if you want to assign a specific IP address for VPN user/username, then it must be done on the side Server?
If you had the "username" on the SAA configurations you can set it up under its framework which "username" IP address gets when he or she connects with the VPN Client.
As naturally as you start using the complete Tunnel and all traffic from the VPN Client starts to get in the tunnel to the ASA you will need a NAT for VPN Client users Internet traffic. You can configure this NAT like this for example:
network of the VPN-POOL object
192.168.30.0 subnet 255.255.255.0interface of VPN-POOL dynamic NAT (outside, outside) after auto source
Note that this is a manual of NAT / double NAT statement real "nat" IS NOT inserted under the 'object' , but the 'object' is rather created it can be used in the "nat" command. I see that your other dynamic PAT configurations are configured with NAT Auto / object NAT network. You can do this like that too if you wish. Personally I do like that.
But as I said before, it seems that you have already configured the VPN to be full of Tunnel. It is perhaps not as it is? While it is connected with VPN, you should be able to check the secure routes (or something like that) section to see if it says "0.0.0.0" If Yes, then it should be tunneling all traffic.
Hope this helps :)
-Jouni
-
Internet access without split tunneling VPN PIX
I have a PIX 515E with code 6.31. I installed a VPN to allow access to the internal network from the Internet using the Cisco VPN client. It does not work properly. We have some sellers who demand that we come from our Internet IP range to allow us access to their database on the Internet. This works very well for our internal users, but I will allow users VPN for this also.
Is there a way to allow the user from the VPN client to use the Internet for business access to the internet instead of use the split tunneling to access the internet through their own connection? I would like users to vpn to be NAT would have réécrirait Internet and seeming come from our pool of Internet addresses. What I found references by using the split tunneling, but this won't work for me. Am I stuck getting a VPN concentrator to achieve?
Thank you
Josh
The PIX cannot route a package back on the same interface, he entered the, which includes a customer entering the interface external and routed VPN package back on the same interface.
A router or a VPN concentrator would be able to do this, but not a PIX, sorry.
-
Cisco easy VPN access Internet without Split Tunnel
Hey guys
IM wondering if anyone has a config that can help me get access to internet via an easy vpn tunnel on a cisco 877 router.
Basically, we are traveling to be users able to use the internet through vpn, rather than using split tunneling. The reason for this is that we have several sites that are attached by lists of external IP access for some services.
We hope that mobile users to interact with these sites through the central router and use external IP of access routers secure sites.
I hope that makes sense. I know that we can use a proxy but we also use other services of bases no proxy on these sites, it would be rather routed direct access.
Thank you
Luke
Hi Luke,.
Please use the installation of the client VPN (complete tunnel) link below.
Note the useful message.
Thank you
Kasi
-
Client AnyConnect and connections without client hang for two users
ASA 5525, v.19 9.1 (5)
AnyConnect client 3.1.02026
I have two users who are unable to connect through the AC client or no client via the web portal. The use of the client, it will get stuck in a loop of "check updates". On the portal, the connection will proceed to point "Cisco Secure Desktop validated successfully... Success... Reloading... Please wait. "Then it crashes here.
This problem occurs for the user, no matter which company laptop it connects to. A help desk technician can use his laptop computer and connect properly, but she could not connect on his own laptop computer or on another laptop. (Same for the other user.) So the question does not appear to be linked to his laptop or the installation of the CA. (Helpdesk reimage her machine early in the process of solving problems before they realized that the question seems to follow the user.)
I've updated the hostscan - no change in the results file. Client and clientless connections seem to work for all users. We are puzzled. Suggestions, anyone? Thank you!
The LDAP protocol must be people - Active Directory server. Chances are the one who manages the SAA should have access at least to look at Active Directory to look that up. If they are not they need.
Of course, I don't know a lot about what you use the devices, but if you use ISE, there should be a type of device MNT (monitoring and troubleshooting) - collecting newspapers and, hopefully, they are sent to a certain type of overall collection of syslog (splunk?) tool.
Otherwise, there should be a device called a CAM (Clean Access Manager) who collects newspapers - which can also be spread to a global tool for syslog - but with cam, you can pull reports from the output in a file delimited by commas (.csv) and pass through them that way.
-The thing that annoys me, is he gets to two users any computer, they try to connect to any network to which they connect, and other users can authenticate and access network on these same devices.
-That is why it is rather confused. Pretty much saying, there must be something with:
-the pool of intellectual property that they get an IP of
-their powers AD
-user name
-something in this sense, if the information provided is accurate.
-
Hi guys,.
I wonder if remote access VPN with split tunnel is using the home user or the corporate to surf internet connection own internet connection?
Any help will be greatly appreciated.
Thank you
Lake
Dear Lakeram,
Split tunneling allows you to access certain resources through the tunnel and all other traffic will be sent to your local proxy.
VPN traffic is defined by the VPN endpoint, for example:
192.168.1.0/24---Internet---ADSL ASA VPN client-
You can have the ASA push the network 192.168.1.0/24 to the customer. Once connected if the client tries to access everything that comes out of the scope of the network, this traffic will be sent to the LAN...
Here's an example with ASA and router.
ASA/PIX: Allow the tunneling split for the VPN Clients on the example of Configuration of ASA
http://www.Cisco.com/en/us/products/ps6120/products_configuration_example09186a0080702999.shtml
ASA 8.x: allow the tunneling split for AnyConnect VPN Client on the example of Configuration of ASA
http://www.Cisco.com/en/us/products/ps6120/products_configuration_example09186a0080975e83.shtml
Router allows the VPN Clients to connect to IPsec and Internet using Split Tunneling Configuration example
I hope it helps.
Thank you.
-
I can fix on my ipad apps in alphabetical order without doing one at a time?
N °
-
Eloqua Engage (sales) for Custom iPad App
Is it possible to take the current Eloqua for iPad app sales and customize it? We think that repackage or points in our current application for our sales team.
If so, are there companies you can recommend to work with? and someone has already done it?
Hi Aziz.
I was informed by Eloqua supported that version iPad committed is removed and will not be updated.
If you want to use hired him on a device, you must use your browser on your device of your choice.Best regards
Thorbjørn
-
Before and after the split-screen view
Its possible for itself before and after without split-screen? Just pass before and after.
Not to be confused with the key slash?
-
iPad App doesn't work do not since upgrading to iOS 6
I'm working on an iPad app development and today I updated our iPad 3 iOS iOS 6 and the application opens. I installed App's track of newspaper on the iPad and got the following warning: "LaunchServices: could not store file lsd-identifiers ' we use Adobe AIR 3.1 to compile the application. The application worked before with iOS 5.1
3.4 AIR was the first version to support iOS properly 6. Can you start using that? It's nicer than 3.1!
-
Even after the "split-tunnel-policy tunnelspecified" specification with "split-tunnel-network-list value TUNNEL of SPLITTING" and denying all traffic to the public IP address of the ASA, I'm still not able to SSH in the firewall. Everything else seems to work OK, but I have to be able to handle the ASA from the public interface. In fact, I expect little given the mean one sa is the installer for the tunnel, and it would seem that a deny statement would be ignored, but perhaps there is a way around this. Thank you.
If you want to connect to your home IP through the tunnel, you must specify 'inside access management:
http://www.Cisco.com/en/us/docs/security/ASA/asa82/configuration/guide/a...
Best regards, Karsten
Sent by Cisco Support technique iPad App
-
L2TP Windows 7, split and site-to-site tunnel
Hi all
I'm going to this interesting problem that drives me crazy all day. I have ASA 5505 (ver 9) where I set up VPN site-to-site to another router and it works. Then I configured L2TP IPsec VPN on SAA with split tunneling, and I can reach my local network. The problem is when I am trying to reach this remote network that is behind this site-to-site VPN. Whatever I do, I'm not able to reach the network. This exact same setup works on different ASA with AnyConnect VPN.
So that's what I did:
(1) adds VPN subnet as ITS 2nd to the existing site-to-site VPN
(2) exemption from NAT configured for subnet VPN when you go to the remote subnet
(3) published the remote subnet to VPN client.
This should do the trick as it does when AnyConnect is in question.
I'll paste some commands concerning:
local pool VPN_POOL 192.168.255.100 - 192.168.255.235 255.255.255.0 IP mask
network of the L2TP-VPN-sub-network object
192.168.255.0 subnet 255.255.255.0access extensive list ip 192.168.17.0 outside_cryptomap allow 255.255.255.0 Site object - 172.16.17.0
outside_cryptomap to access extended list ip 192.168.255.0 allow 255.255.255.0 Site object - 172.16.17.0
Split-Tunnel-ACL access-allowed list standard 192.168.17.0 255.255.255.0
Split-Tunnel-ACL access-allowed list standard 172.16.17.0 255.255.255.0NAT (inside, outside) static source to the inside network inside-network destination Site - 172.16.17.0 of azure - static non-proxy-arp 172.16.17.0
NAT (inside, outside) static source to the inside network inside-network destination static L2TP-VPN-sub-network L2TP-VPN-slot-network non-proxy-arp-search directions
NAT (inside, outside) static source L2TP VPN sub network L2TP-VPN-sub-network static destination Site - 172.16.17.0 Site - 172.16.17.0 no-proxy-arp-search to itineraryinternal VPN_L2TP_IPSEC group policy
VPN_L2TP_IPSEC group policy attributes
value of server DNS 172.16.17.4
Protocol-tunnel-VPN l2tp ipsec
Split-tunnel-policy tunnelspecified
Split-tunnel-network-list value Split-Tunnel-ACL
value by default-field * *.com
Split-dns value * *.com
enable dhcp Intercept 255.255.255.0attributes global-tunnel-group DefaultRAGroup
address VPN_POOL pool
Group Policy - by default-VPN_L2TP_IPSEC
IPSec-attributes tunnel-group DefaultRAGroup
IKEv1 pre-shared-key *.
tunnel-group DefaultRAGroup ppp-attributes
ms-chap-v2 authenticationSomeone at - he managed to get this configuration works? I guess I'm missing some details here, but I don't see that. Perhaps it does not work with L2TP?
Hello, Damir Reic.
What do you use NAT for L2TP-VPN? Split tunneling is help your users internet direcrly so you don't need to use NAT. It can be a source of problem as NAT works before VPN site to site. If your remote users traffic could be changed to NAT and IP traffic that wi source address will be different. And for this reason, it is not rules hiting your site-to-site VPN.
-
Restrictions of ASA Anyconnect for Split Tunneling network list
Hello
I have a question. We use Cisco ASA 5520 9.1.1 firmware version with configure SSL VPN Anyconnect(Anyconnect client version 2.5.605).)
We use the big Split Tunneling access-list with 200 ACEs.
If I add more than 200 entries in the list of access and then I connect to the VPN, and after that, we will see that only 200 entries have been added to the routing table.
So my question is... There is a limit for Split Tunneling ACL when you use the Anyconnect client?
Thank you
Hello
This is very well document in one of internal bug at Cisco . Unfortunately, as it is internal I will not be able to share the same with you. The only workaround available as of now is to combine your networks and make the list as small as possible covering all the required network you need which is less than or equal to 200
Thank you
Jeet Kumar
-
How can I transform my ipad app within an app that works for the iPad and iPhone?
I built an ipad with the DPS application. But now my client wants to have the same content on iphone. How can I transform my ipad app within an app that works for the iPad and iPhone? Is this possible without creating a new application App Builder? Thanks for your replies.
You must create a new instance of the DPS App Builder application. Select iPhone and iPad. If you use the same mobileprovision files (or mobile layout updated of the files of the bases on the same ID App), it is considered that a version update of the application itself.
You will need create sheets separated for the iPhone. folios iPad do not appear in the library of iPhone. See Digital Publishing Suite help | Creating content DPS for iPhones.
-
My iPad will not normally charge. I tried different cables and Chargers. I plugged the iPad to iTunes and reset a DFU. After only a few hours the iPad finished reloading all software and reloaded new apps, it had also charged the battery but the problem remains, I still can't load the iPad normally. Any help out there?
There are very few things that keep loading an iPad. Some of these (other charger plugged into a good outlet, different cable) you have already tried. Others are:
1 dirt, lint or fuzz in the port of loading of the charger or the iPad. Check and clean carefully if necessary.
2. a software failure. Reset the iPad. Press and hold the Home button and the sleep/wake button until the Apple logo appears. Then release the button and let the appliance restarts. You lose no data by doing this. It's like a restart of the computer.
3. failure. Make an appointment at an Apple store to have a technician look at your device. Or contact the Apple Support.
Maybe you are looking for
-
change the model fades into the track edit window
Let me repost with corrected language I opened to the top of track editing window for a track of the model. (audio) I can see in the editing window track fades, but when I try to edit them in any way it does not work. Logic does strange things at th
-
I bought a watch on eBay, the former owner has not extinguished obviously locking activation. When I try to turn it on, it says to update to the latest ios, then when I try to do what it the screen said, update checking and nothing else happens, it's
-
Satellite L300 - 12K - Skype disconnects when surfing and using Java
Hello! I always have problems when I use Skype when you surf in particular using java and don't know why.When I start a conversation on Skype, I m always disconnected from the internet. No more connection for 1 or 2 minutes. Only when you use Skype.
-
Laptop was stolen and have been returned, but have the password on the bios please help me RE051ST? Ive treid many passwords and it returns error code 75237870 can you help me please?
-
Intermittent visa BFFF0011 with viOpen error
I'm contacting a 2700 Keithey DMM via TCP/IP, and very occasionally, when I call viOpen, it will fail with BFFF0011 error code. Everyone knows that before and if so, what was the cause? I checked the patch ethernet lead and in any case (I think) it h