Cisco easy VPN access Internet without Split Tunnel
Hey guys
IM wondering if anyone has a config that can help me get access to internet via an easy vpn tunnel on a cisco 877 router.
Basically, we are traveling to be users able to use the internet through vpn, rather than using split tunneling. The reason for this is that we have several sites that are attached by lists of external IP access for some services.
We hope that mobile users to interact with these sites through the central router and use external IP of access routers secure sites.
I hope that makes sense. I know that we can use a proxy but we also use other services of bases no proxy on these sites, it would be rather routed direct access.
Thank you
Luke
Hi Luke,.
Please use the installation of the client VPN (complete tunnel) link below.
Note the useful message.
Thank you
Kasi
Tags: Cisco Security
Similar Questions
-
PlayBook & cisco Easy VPN Server 831
I don't seem to be able to connect to my router 831 cisco easy vpn server is configured by using my Blackberry Playbook. Looking at the console of the router I can see Debugging but don't know what it means. I have attached debugging as well as glued my setup, if someone is able to help me at all it would be much appreciated. Thank you very much.
Current configuration: 2574 bytes
!
version 12.3
no service button
horodateurs service debug datetime msec
Log service timestamps datetime msec
no password encryption service
!
router host name
!
enable secret 5 $1$ FM71$ y4ejS2icnqX79b9gD92E81
enable password xxxx
!
username privilege 15 password 0 $1$ W1fA CRWS_Ritesh $ o1oSEpa163775446
username privilege 15 secret 5 shamilton wFLF $1$ $ 8eRxnrrgVHMXXC0bXdEGi1
AAA new-model
!
!
AAA authentication login default local
AAA authentication login ciscocp_vpn_xauth_ml_1 local
AAA authorization exec default local
AAA authorization ciscocp_vpn_group_ml_1 LAN
AAA - the id of the joint session
IP subnet zero
no ip Routing
!
!
audit of IP notify Journal
Max-events of po verification IP 100
No ftp server enable write
!
!
!
!
crypto ISAKMP policy 1
BA 3des
preshared authentication
Group 2
ISAKMP xauth timeout 15 crypto!
ISAKMP crypto client configuration group ciscogroup
(deleted) 0 key
DNS 172.16.60.246 172.16.60.237
pool SDM_POOL_3
ACL 100
Save-password
include-local-lan
!
!
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
!
crypto dynamic-map SDM_DYNMAP_1 1
game of transformation-ESP-3DES-SHA
market arriere-route
!
!
card crypto SDM_CMAP_1 client authentication list ciscocp_vpn_xauth_ml_1
map SDM_CMAP_1 isakmp authorization list ciscocp_vpn_group_ml_1 crypto
client configuration address map SDM_CMAP_1 crypto answer
map SDM_CMAP_1 65535-isakmp dynamic SDM_DYNMAP_1 ipsec crypto
!
!
!
!
interface Ethernet0
IP 172.16.60.241 255.255.255.0
IP nat inside
no ip route cache
!
interface Ethernet1
DHCP IP address
NAT outside IP
no ip route cache
automatic duplex
map SDM_CMAP_1 crypto
!
interface FastEthernet1
no ip address
Shutdown
automatic duplex
automatic speed
!
interface FastEthernet2
no ip address
Shutdown
automatic duplex
automatic speed
!
interface FastEthernet3
no ip address
Shutdown
automatic duplex
automatic speed
!
interface FastEthernet4
no ip address
automatic duplex
automatic speed
!
local IP SDM_POOL_1 172.16.60.190 pool 172.16.60.199
pool of local SDM_POOL_2 192.168.1.1 IP 192.168.1.100
local IP SDM_POOL_3 172.16.61.100 pool 172.16.61.150
IP nat inside source overload map route SDM_RMAP_1 interface Ethernet1
IP classless
!
IP http server
no ip http secure server
!
Remark SDM_ACL category of access list 1 = 2
access-list 1 permit 172.16.60.0 0.0.0.255
Note access-list 100 category CCP_ACL = 4
access-list 100 permit ip 172.16.60.0 0.0.0.255 any
public RO SNMP-server community
Enable SNMP-Server intercepts ATS
!
Line con 0
no activation of the modem
line to 0
line vty 0 4
exec-timeout 120 0
password xxxxx
length 0
!
max-task-time 5000 Planner
!
endStace,
*Mar 1 06:40:15.258: ISAKMP: transform 1, ESP_AES
*Mar 1 06:40:15.258: ISAKMP: attributes in transform:
*Mar 1 06:40:15.262: ISAKMP: SA life type in seconds
*Mar 1 06:40:15.262: ISAKMP: SA life duration (basic) of 10800
*Mar 1 06:40:15.262: ISAKMP: encaps is 61443
*Mar 1 06:40:15.262: ISAKMP: key length is 256
*Mar 1 06:40:15.262: ISAKMP: authenticator is HMAC-SHA
*Mar 1 06:40:15.262: ISAKMP (0:14): atts are acceptable.
*Mar 1 06:40:15.262: ISAKMP (0:14): IPSec policy invalidated proposal
*Mar 1 06:40:15.262: ISAKMP (0:14): phase 2 SA policy not acceptable! (local 14
The other end offers AES 256 and SHA IPSec transform set.
While you have configured:
crypto ipsec transform-set ESP-3DES-SHA esp-3des esp-sha-hmac
Suggestion:
Add a new set of transofrm and apply it under crypto map.
HTH,
Marcin
-
Internet access without split tunneling VPN PIX
I have a PIX 515E with code 6.31. I installed a VPN to allow access to the internal network from the Internet using the Cisco VPN client. It does not work properly. We have some sellers who demand that we come from our Internet IP range to allow us access to their database on the Internet. This works very well for our internal users, but I will allow users VPN for this also.
Is there a way to allow the user from the VPN client to use the Internet for business access to the internet instead of use the split tunneling to access the internet through their own connection? I would like users to vpn to be NAT would have réécrirait Internet and seeming come from our pool of Internet addresses. What I found references by using the split tunneling, but this won't work for me. Am I stuck getting a VPN concentrator to achieve?
Thank you
Josh
The PIX cannot route a package back on the same interface, he entered the, which includes a customer entering the interface external and routed VPN package back on the same interface.
A router or a VPN concentrator would be able to do this, but not a PIX, sorry.
-
Cannot access the internal network with Cisco easy vpn client RV320
I have a cisco RV320 (firmware v1.1.1.06) and created a tunnel easy vpn (= split tunnel tunnel mode), then I installed the cisco client vpn v5.0.07.0290 in Windows 7 64 bit, I can connect to the vpn, but I do not see the other pc ping nor them, no idea?
Thank you
Hello
1. is the firewall on the active Windows 7 computer? If so, please disable it
2. can you check that you get a correct IP address in the range of the POOL of IP configured?
3. When you perform the tracert command to access an internal server, it crosses the VPN¨?
4. is the tunnel of split giving you access to internal IP subnets defined?
5. on the RV320 you see the user connected and sending and receiving bytes?
Don t forget to rate and score as correct the helpful post!
David Castro,
Kind regards
-
ASA 5505 VPN works great but can't access internet via the tunnel to customers
We have an ASA 5505 ASA 8.2.1 running and using IPSec for Remote access clients in the main office. Remote access is a lot of work, with full access to network resources in the main office and the only thing I can't get to work is access to internet through the tunnel. I don't want to use split tunneling. I use ASDM 6.2.1 for configuration. Any help is appreciated. I'm probably missing something simple and it looked so much, I'm probably looking at right beyond the error. Thanks in advance for your time and help! Jim
Add a statement of nat for your segment of customer on the external interface
NAT (outside) - access list
then allow traffic routing back on the same interface, it is entered in the
permit same-security-traffic intra-interface
*
*
* more than information can be found here:
http://www.Cisco.com/en/us/products/ps6120/products_tech_note09186a00807...
On Wednesday, 27 January 2010, at 23:12, jimcanova
-
Hello everyone
I have setup a VPN connection, which I can connect to. For all customers of connection, I want to give them an IP (from a subnet maybe) and let them use this IP address for all that they do.
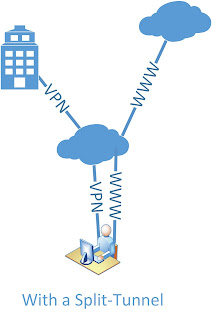
Therefore, this:
and not current:
My inside is 192.168.1.0
My VPN IP pool is 192.168.30.5 - 200
My server (DNS, files, Web site) is 192.168.1.222Here's my setup. I scored what I thought might have something to do with it:
ASA Version 9.2 (1)
!
ciscoasa hostname
activate 8Ry2YjIyt7RRXU24 encrypted password
volatile xlate deny tcp any4 any4
volatile xlate deny tcp any4 any6
volatile xlate deny tcp any6 any4
volatile xlate deny tcp any6 any6
volatile xlate deny udp any4 any4 eq field
volatile xlate deny udp any4 any6 eq field
volatile xlate deny udp any6 any4 eq field
volatile xlate deny udp any6 any6 eq field
2KFQnbNIdI.2KYOU encrypted passwd
names of
pool of IP local IP-pool 192.168.30.5 - 192.168.30.200 mask 255.255.255.0
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
IP 192.168.1.253 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
IP address dhcp setroute
!
boot system Disk0: / asa921 - k8.bin
passive FTP mode
permit same-security-traffic intra-interface
network obj_any object
subnet 0.0.0.0 0.0.0.0
network of the object Server-25
Home 192.168.1.222
Description of the test server
network of the object server-80
Home 192.168.1.222
Description of the test server
network of the object server-443
Home 192.168.1.222
Description of the test server
network of the object server-2525
Home 192.168.1.222
Description of the test server
network of the object server-993
Home 192.168.1.222
Description of the test server
network of the object server-6001
Home 192.168.1.222
Description of the test server
network of the object server-6002
Home 192.168.1.222
Description of the test server
network of the object server-6003
Home 192.168.1.222
Description of the test server
network of the object server-6004
Home 192.168.1.222
Description of the test server
network of the VPN HOST object
192.168.30.0 subnet 255.255.255.0
the object to the Interior-net network
host 192.168.1.0
the VPN server object network
Home 192.168.1.222
outside_access_in list extended access permit tcp any object Server-25 eq smtp
outside_access_in list extended access permit tcp any object server-2525 2525 eq
outside_access_in list extended access permit tcp any object server-80 eq www
outside_access_in list extended access permit tcp any object server-443 https eq
outside_access_in list extended access permit tcp any object server-993 993 eq
outside_access_in list extended access permit tcp any object server-6001 eq 6001
outside_access_in list extended access permit tcp any object server-6002 6002 eq
outside_access_in list extended access permit tcp any object server-6003 eq 6003
outside_access_in list extended access permit tcp any object server-6004 eq 6004
outside_access_in to access ip 192.168.1.0 scope list allow 255.255.255.0 192.168.30.0 255.255.255.0
permit access-list Split-Tunnel-ACL standard 192.168.30.0 255.255.255.0
no pager
Enable logging
asdm of logging of information
Within 1500 MTU
Outside 1500 MTU
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 721.bin
don't allow no asdm history
ARP timeout 14400
no permit-nonconnected arp
NAT (indoor, outdoor) Interior-net Interior-NET static source static destination HOST-VPN-VPN-HOST
NAT VPN VPN-server destination (indoor, outdoor) static static source HOST-VPN-VPN-HOST
!
network obj_any object
NAT dynamic interface (indoor, outdoor)
network of the object Server-25
NAT (inside, outside) interface static tcp smtp smtp service
network of the object server-80
NAT (inside, outside) interface static tcp www www service
network of the object server-443
NAT (inside, outside) interface static tcp https https service
network of the object server-2525
NAT (inside, outside) interface static 2525 2525 tcp service
network of the object server-993
NAT (inside, outside) interface static tcp 993 993 service
network of the object server-6001
NAT (inside, outside) interface static tcp 6001 6001 service
network of the object server-6002
NAT (inside, outside) interface static tcp 6002 6002 service
network of the object server-6003
NAT (inside, outside) interface static 6003 6003 tcp service
network of the object server-6004
NAT (inside, outside) interface static service tcp 6004 6004
Access-group outside_access_in in interface outside
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
RADIUS AAA server HSS-auth-server protocol
allow only
AAA-server HSS-auth-server (inside) host 192.168.1.222
Timeout 5
key *.
identity of the user by default-domain LOCAL
Enable http server
http 192.168.1.0 255.255.255.0 inside
No snmp server location
No snmp Server contact
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec pmtu aging infinite - the security association
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 define ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
outside_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
outside_map interface card crypto outside
trustpool crypto ca policy
Crypto isakmp nat-traversal 30
Crypto ikev1 allow outside
IKEv1 crypto policy 10
authentication crack
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 20
authentication rsa - sig
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 30
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 40
authentication crack
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 50
authentication rsa - sig
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 60
preshared authentication
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 70
authentication crack
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 80
authentication rsa - sig
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 90
preshared authentication
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 100
authentication crack
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 110
authentication rsa - sig
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 120
preshared authentication
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 130
authentication crack
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 140
authentication rsa - sig
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 150
preshared authentication
the Encryption
sha hash
Group 2
life 86400
Telnet timeout 5
SSH stricthostkeycheck
SSH timeout 5
SSH group dh-Group1-sha1 key exchange
Console timeout 0interface ID client DHCP-client to the outside
dhcpd outside auto_config
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
internal HSSvpn group strategy
attributes of Group Policy HSSvpn
value of server WINS 192.168.1.222
value of server DNS 192.168.1.222
Ikev1 VPN-tunnel-Protocol
Split-tunnel-policy tunnelall
Split-tunnel-network-list value Split-Tunnel-ACL
HSS.dk value by default-field
activate dns split-tunnel-all
type tunnel-group HSSvpn remote access
attributes global-tunnel-group HSSvpn
address IP-pool pool
HSS-auth-server authentication-server-group
Group Policy - by default-HSSvpn
password-management
IPSec-attributes tunnel-group HSSvpn
IKEv1 pre-shared-key *.
tunnel-group HSSvpn ppp-attributes
No chap authentication
no authentication ms-chap-v1
ms-chap-v2 authentication
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:c85ff8bf61669bef56b4dad704a4930a
: endHello
Change Split Tunnel VPN in full Tunnel VPN, you have really do much in your configuration.
Seems that have already changed you the 'tunnelspecified' 'tunnelall' in configurations of the 'group policy' . You can delete the setup but that defines the ACL of Split Tunnel
attributes of Group Policy HSSvpn
No split-tunnel-network-list value Split-Tunnel-ACLSeems that you use an internal AAA server to manage authentication rather than on the SAA. I guess if you want to assign a specific IP address for VPN user/username, then it must be done on the side Server?
If you had the "username" on the SAA configurations you can set it up under its framework which "username" IP address gets when he or she connects with the VPN Client.
As naturally as you start using the complete Tunnel and all traffic from the VPN Client starts to get in the tunnel to the ASA you will need a NAT for VPN Client users Internet traffic. You can configure this NAT like this for example:
network of the VPN-POOL object
192.168.30.0 subnet 255.255.255.0interface of VPN-POOL dynamic NAT (outside, outside) after auto source
Note that this is a manual of NAT / double NAT statement real "nat" IS NOT inserted under the 'object' , but the 'object' is rather created it can be used in the "nat" command. I see that your other dynamic PAT configurations are configured with NAT Auto / object NAT network. You can do this like that too if you wish. Personally I do like that.
But as I said before, it seems that you have already configured the VPN to be full of Tunnel. It is perhaps not as it is? While it is connected with VPN, you should be able to check the secure routes (or something like that) section to see if it says "0.0.0.0" If Yes, then it should be tunneling all traffic.
Hope this helps :)
-Jouni
-
iPad App AnyConnect and Webproxy without Split Tunneling
Hello
Is it possible to use a web proxy server to make iPad VPN SSL connections to use an internal navigation proxy server when connected. Split tunneling is not allowed, but I want to allow users to be able to browse the internet through our internal proxy.
Is there a solution for this?
Thank you
You can look in the Internet EXPLORER on the SAA proxy feature which will allow you to set values of dynamic proxy for AnyConnect connection customers. This feature was originally designed for IE but has been tested to work with the iPhone and iPod Touch 4.1.
Todd
-
access list of split tunneling
Hello
I have some problems on ASA 5520 split tunneling configuration.
Here's the scenario:
Number of remote users connects ipsec with ASA 5520 (in central) using ubuntu vpnc-client.
Split tunneling is used, in order to allow remote users to surf the Internet using their ISP.
The goal is to remove the possibility for ssh/telnet servers within the local enterprise network for remote users.
Here is a part of the config:
internal REMOTE_gp group strategy
attributes of Group Policy REMOTE_gp
VPN-idle-timeout no
Protocol-tunnel-VPN IPSec
Group-lock no
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list REMOTE_splittunnel-group type REMOTE access remotely
tunnel-group REMOTE General attributes
authentication-server-group RADIUSGR
Group Policy - by default-REMOTE_gp
REMOTE tunnel-group ipsec-attributes
pre-shared-key *.
ISAKMP keepalive retry threshold 15 10
RADIUS protocol AAA-server RADIUSGR
AAA-server RADIUSGR (INSIDE_LAN) 192.168.0.244
REMOTE_split list extended access deny tcp 192.168.0.0 255.255.255.0 ssh telnet rank everything
permit access ip 192.168.0.0 scope list REMOTE_split 255.255.255.0 192.168.100.0 255.255.255.0
ip subnet ##192.168.100.0/24 - where from Radius Server to allocate ip addresses to remote users.
INSIDE_LAN_in list extended access deny tcp 192.168.0.0 255.255.255.0 eq ssh 192.168.100.0 255.255.255.0
INSIDE_LAN_in list extended access deny tcp 192.168.0.0 255.255.255.0 eq telnet 192.168.100.0 255.255.255.0
permit access ip 192.168.0.0 scope list INSIDE_LAN_in 255.255.255.0 any
It has nat enabled on the interface, but there is a special instruction in nat0 ACL for 192.168.100.0 subnet
permit access ip 192.168.0.0 scope list INSIDE_LAN_nat0_outbound 255.255.255.0 192.168.100.0 255.255.255.0
The problem is that the remote users can easily ssh and telnet servers in network INSIDE_LAN. Everything I put in INSIDE_LAN_in ACL, remote users still have full access to this network. Restrictions in the REMOTE_split ACL do not work either.
You must configure vpn-filter rather to block telnet and ssh access as follows:
Remote filter access list deny tcp 192.168.100.0 255.255.255.0 192.168.0.0 255.255.255.0 eq 22
Remote filter access list deny tcp 192.168.100.0 255.255.255.0 192.168.0.0 255.255.255.0 eq 23
distance-filter 192.168.100.0 ip access list allow 255.255.255.0 192.168.0.0 255.255.255.0
attributes of Group Policy REMOTE_gp
VPN-value filter-remote control
Split tunnel acl has the following statement and it should be extended to standard ACLs instead of:
REMOTE_split list of permitted access 192.168.0.0 255.255.255.0
Hope that helps.
-
Cisco easy VPN + loopback interface. static ip address for the client
Good day people.
I have a couple a question and answer on which I can't google for a period. BTW I maybe simly use bad aproach to choose keywords.
Thus,.
(1) is it possible to assign the same IP to the same customer every time that it authenticated, preferably without using DHCP? Definely im sure it is possible, but can't find match configuration examples (my camera's 1921 Cisco IOS 15.0.1).
(2) is it possible to assign the dynamic crypto map to the loopback interface (to make EASY VPN Server accessible through two interfaces - maybe you recommend another approach instead?) - that I move the map workingcrypto of int phy loopback - I can not connect with reason "SA Phace1 policy proposal" not accepted
Hello
(1) you can attach to the same IP to the same username using RADIUS
(2) If you have 2 outside interfaces
Then, you would use
mymap-address loop0 crypto card
int gig0/0
crypto mymap map
int g0/1
cryptp map mymap
By doing so, the local address would actually be the loop0 but Cryptography card HAS to be applied on physical output interfaces
See you soon
OLivier
-
CISCO easy VPN & local subnets
Easyvpn Installer based on http://www.cisco.com/en/US/products/sw/secursw/ps5318/products_configuration_example09186a00806ad10e.shtml
core1 #sh passage int fa0/0
Building configuration...
Current configuration: 303 bytes
!
interface FastEthernet0/0
Description _WAN_INTERFACE_
004f.620a.8771 Mac address
IP 10.74.17.254 255.255.240.0
no ip redirection
no ip unreachable
no ip proxy-arp
NAT outside IP
IP virtual-reassembly
route IP cache flow
automatic duplex
automatic speed
No cdp enable
card crypto VPNMAP1
end
#sh core1 run int fa0/1.1
Building configuration...
Current configuration: 294 bytes
!
interface FastEthernet0/1.1
Description Native_VLAN_1
encapsulation dot1Q 1 native
IP 192.168.40.101 255.255.255.0
IP helper 192.168.40.210
NBAR IP protocol discovery
IP nat inside
IP virtual-reassembly
no ip mroute-cache
entry of service-policy DROP_ONLINE_MOVIES
end
#sh core1 run int fa0/1.50
Building configuration...
Current configuration: 137 bytes
!
interface FastEthernet0/1.50
encapsulation dot1Q 50
192.168.50.1 IP address 255.255.255.0
IP nat inside
IP virtual-reassembly
end
core1 #sh ip int br | UNAs Exc
Interface IP-Address OK? Method State Protocol
FastEthernet0/0 10.74.17.254 YES NVRAM up up
FastEthernet0/1.1 192.168.40.101 YES NVRAM up up
FastEthernet0/1.20 192.168.20.1 YES NVRAM up up
FastEthernet0/1.50 192.168.50.1 YES NVRAM up up
FastEthernet0/1.82 192.168.82.1 YES NVRAM up up
Gateway of last resort is 10.74.16.254 to network 0.0.0.0
C 192.168.40.0/24 is directly connected, FastEthernet0/1.1
192.168.80.0/32 is divided into subnets, subnets 1
S 192.168.80.5 [1/0] via 195.212.29.188
C 192.168.20.0 is directly connected, FastEthernet0/1.20
10.0.0.0/8 is variably divided into subnets, 3 subnets, 3 masks
S 10.10.1.0/31 is directly connected, FastEthernet0/1.1
C 10.10.10.0/24 is directly connected, FastEthernet0/1.10
C 10.74.16.0/20 is directly connected, FastEthernet0/0
S 192.168.0.0/24 is directly connected, FastEthernet0/1.1
C 192.168.50.0/24 is directly connected, FastEthernet0/1.50
S * 0.0.0.0/0 [1/0] via 10.74.16.254
VPNPOOL1 192.168.80.1 192.168.80.5
CUSTOMER
Linux machine using vpnc
cat /etc/vpnc/e_vpn.conf
Xxxxxx gateway IPSec
VPN IPSec ID
IPSec secret xxxxx
IKE psk Authmode
Xauth username yyyyy
Xauth password xxxxx
Target 192.168.50.0/24 192.168.40.0/24 networks
Route - n
Kernel IP routing table
Destination Gateway Genmask Flags metric Ref use Iface
192.168.40.101 0.0.0.0 255.255.255.255 UH 0 0 0 tun0
_VPN_ 9.158.166.129 UGH 255.255.255.255 0 0 0 eth0
9.158.166.129 0.0.0.0 255.255.255.255 UH 0 0 0 eth0
9.0.136.50 9.158.166.129 UGH 255.255.255.255 0 0 0 eth0
192.168.220.0 0.0.0.0 255.255.255.240 U 0 0 0 virbr4
192.100.100.0 0.0.0.0 255.255.255.128 U 0 0 0 virbr5
9.158.166.128 0.0.0.0 255.255.255.128 U 0 0 0 eth0
192.168.80.0 0.0.0.0 255.255.255.0 U 0 0 0 tun0
192.168.40.0 0.0.0.0 255.255.255.0 U 0 0 0 tun0
192.168.50.0 0.0.0.0 255.255.255.0 U 0 0 0 tun0
0.0.0.0 9.158.166.129 0.0.0.0 UG 0 0 0 eth0
Ping - c1 192.168.50.1
PING 192.168.50.1 (192.168.50.1) 56 (84) bytes of data.
-ping 192.168.50.1 - statistics
1 packets transmitted, 0 received, 100% packet loss, time 0ms s
Did I miss something in the config... or something is wrong?
Follow these steps:
101 extended IP access list
1 deny ip any 192.168.80.0 0.0.0.255
!
Renumber list of access IP 101 10 10
Thank you.
Please note all useful posts
-
Issue of Cisco AnyConnect VPN access
We have configured a Cisco ASA 5505 with access AnyConnect. It works very well. However, these users can't ping on the private network devices. We have configured all devices on the network with an address 10.10.10.0/24 space. The inside interface of the ASA I 10.10.10.1/24 and the VPN return addresses are 10.10.10.50 - 10.10.10.65/24.
They users can use SSH and Oracle or MySQL calls but can't ping. Obviously, I'm looking for something.
Thank you.
Dwane
Hi Sylvie,.
Most likely, your ASA missing no. - nat between inside the interface and remote vpn-pool address range.
Quick Trobule shooting, thanks for posting your config and do not forget to remove the config security information.
What version of your ASA?
Thank you
Rizwan James
-
Problems: Access to the internet. 2. right of PC, for example, clock, Favorites, etc. does not appear on the screen while booting.
3. cannot access the Micro password
Error message: «Windows cannot access the path specified...» »
When I'm online through the icon help & Support, still cannot access all the other icons; needs access to sites through links.
First of all, there is problem when I played the game on 'brightness (MySpace link); PC seems to crash and the problem has continued since then.
I have no idea what to do and I'm a bit of a novice. In addition, have physical difficulties which slows me down or interferes with the ability to work through problems.
Applications and links of Facebook can be very dangerous. Please start with the basics to ensure that you are working from a clean base. You will need to obtain the tools of a different, known-clean computer with access to the Internet and put them on a USB stick to transfer to the affected machine.
http://www.elephantboycomputers.com/page2.html#Removing_Malware
If you can't do the work yourself (and there is no shame in admitting this isn't your cup of tea), take the machine to a professional computer repair shop (not your local equivalent of BigComputerStore/GeekSquad). If possible, have all your data backed up before taking the machine into a shop.
MS - MVP - Elephant Boy computers - don't panic!
-
Access Internet without IPv4 but Ipv6 connectivity is OK
I bought a laptop with IE10 a Windows 8 installed. When I try to log into WiFi, Ipv4 access does not work but the Ipv6 access works.
I can navigate only in a few pages.
Hi Francisco,.Thanks for posting the question on Microsoft Community Forums.As we hear of publication description, Ipv4 does not work when connecting by Wifi.
We will try to help you solve the problem.If you could answer a few questions that would help us resolve this problem:1. do you get an error message?2. you are on a domain network?Here are some steps that you can follow:Step 1: Clear the cache of DNS resolution.
(a) move the mouse to the lower left corner of the screen and right click on the Start and selection
"Command Prompt (Admin).(b) type ipconfig/flushdns, and then press ENTER.Step 2: Manually configure TCP/IP settingsFollow the steps to reset TCP/IP.
one) starts at the desktop view.(b) open the command prompt, right-click in the corner when the start window appears, select command prompt (admin).(c) at the command prompt, copy and paste (or type) the following command and then press ENTER:
netsh int ip reset c:\resetlog.txt
Note: If you do not specify a path of the directory for the log file, use the following command:
netsh int ip reset resetlog.txt(d) restart the computer.You can read this article on the problems of network connection for assistance.
http://Windows.Microsoft.com/en-us/Windows-8/cant-connect-to-a-networkHope this solves the problem. If the problem persists, you can write back to us and we will be happy to help you further.
-
Ipad Cisco ipsec VPN connects but not access to the local network
Hi guys,.
I am trying to connect our ipads to vpn to access network resources. IPSec cisco ipad connects but not lan access and cannot ping anything not even not the interfaces of the router.
If I configure the vpn from cisco on a laptop, it works perfectly, I can ping all and can access resources on the local network if my guess is that the traffic is not going in the tunnel vpn between ipad and desktop.
Cisco 877.
My config is attached.
Any ideas?
Thank you
Build-in iPad-client is not useful to your configuration.
You have three options:
(1) remove the ACL of your vpn group. Without split tunneling client will work.
2) migrate legacy config crypto-map style. Here, you can use split tunneling
3) migrate AnyConnect.
The root of the problem is that the iPad Gets the split tunneling-information. But instead of control with routing traffic should pass through the window / the tunnel and which traffic is allowed without the VPN of the iPad tries to build a set of SAs for each line in your split-tunnel-ACL. But with the model-virtual, SA only is allowed.
-
Even IOS VPN Interface Internet Access issue
Hi all
I was wondering if there was any equivalent to these orders of ASA 5510 to put on a cisco IOS router 2811.
Split-tunnel-policy excludespecified
value of Split-tunnel-network-list LOCAL_LAN_ACCESS
What I want to achieve is to give internet access to my vpn users without creating a split tunnel, which means the vpn user turns off the Internet on the same interface on that their vpn router ends.
Is a 2811 for this there docs? I could not find the doc for it...
TIA,
-Fred
Try this link
Public Internet on a stick
Rgds
Jorge
Maybe you are looking for
-
The most recent update of installed Firefox yesterday. Since then, I have not been able to open new tabs manually by using the sign on the tabs or the file, command new Tab.
-
Hello, I want the YIG oscilloscope with the portable interface so first of all I have to do?
Hello If I'm portable computer interface with oscilloscope yig so first I have to do? What type of probe is beneficial for me
-
Screen reader works but see window empty when you open a Word document
Original title: I am currently setting up my screen reader, Windows Vista Home Edition and have successfully by reading everything except the content of windows. Example, you open a word document and I see the text, but the screen reader sees an empt
-
Updated in date dated 13/01/2016 has been auto installed I lost sound
Windows 7 update as of 13/01/2016 has been auto installed, I lost his (missing sound) did a restore system recovered from his. To check the widows 7 is upgrading its system has again been lost. Y at - it a fixed? OT: The window update
-
Smartphones blackBerry BIS does not mail for the last 1 - 2w?
BlackBerry 9000, Rogers. Mail server is an IMAP server that I run, running cyrus IMAPd. At least a good year, he pushed email instantly to my BB. My server supports IMAP IDLE, and the BIS connection seemed to take advantage of this. Deliver the e-mai