Web server timeout setting
field SESSIONTIMEOUT of PSWEBPROFILE table has something to do with the websever time-out setting? If Yes, then in my case, change the values in the table doesn't have no effect or the time-out expires, or PIA setting!Wait times can be defined in many places.
Web profile
On the whitelists
Application server
to name a few...
http://docs.Oracle.com/CD/E38689_01/pt853pbr0/Eng/PT/tsvt/task_WebServerTimeouts-071144.html#WebServerTimeouts-071144__pt0020183
http://docs.Oracle.com/CD/E38689_01/pt853pbr0/Eng/PT/tsvt/task_PIATimeouts-07114a.html#portletsFrame
http://docs.Oracle.com/CD/E38689_01/pt853pbr0/Eng/PT/tsvt/task_ApplicationServerTimeouts-071147.html#portletsFrame
There are several types of wait times and you should read the documentation to understand how they interact together. I recommend leaving weblogic, only, unless specifically requested to change by the documentation. PeopleSoft will tell weblogic what to do.
Changing the value of update SQL is also not recommended. Change the web profile you use online, especially if you are not familiar with the options. If you're updating just SESSIONTIMEOUT you never change the pop-up warning that has a separate clock. Which can have a negative impact on users.
Delays of the web of PeopleSoft are JavaScript engine. If they are changed the web profile needs to be recharged. Restart the PIA after change of any web profile. Clear the cache of the browser and PIA as well. The JavaScript file defined in the code of timeout will be cached and sometimes after PIA restart the browser can be stubborn and always used the updated copy cached.
The JavaScript timeout is in the HTML PT_SAVEWARNINGSCRIPT object if you want to watch.
Tags: Oracle Applications
Similar Questions
-
Setting up Web server behind the WRT300N
I'm trying to set up a webserver behind a WRT300N. I followed the article Linksys at the bottom of this post, to the letter, but its still does not. I have a cable modem connected to the WRT300N comcast, and then I have my Web server connected to the internet through the WRT300N wireless. I assigned a static IP address to my web server (192.168.1.2), and I also put in place the router before port 80 to the web server (XP pro). However, when I type the public ip address in a web browser, it can't find my server. I know that the web server works because I seem to be my home page when I type http://localhost in the local web browser. Any ideas? What Miss me? http://www3.nohold.NET/noHoldCust56/Prod_6/KnowledgePortal/KPScripts/amsviewer.asp?docid=e86f4f1c3a98416abc78586d4f544132_KB3699_EN_070208_v1.XML&amsstatsid=4666791
Hello
Have you tried access you a public IP of someone elses PC, IE. a single step on your own network?
I had / have a problem try accessing one of my friends unless I have use someone elses internet connection. I could access only web interface of my modem otherwise.
dRdoS7
PS. don't know why this is the case, others may have an idea.
EDIT: What port no.. Do you use? They do like this:
'http://my_public_ip:access_port '?
Sorry, read your message again, try another port such as 8080 number
-
He was somehow set up my own Web server?
Hello community
I'm new in Web site development and I run a website called www.resthouse-wallis.com.
In fact, I can't run the Web site and I think that's not because of my hosting.
It is possible that with some changes in the Terminal (nginx, apache) that I am my own Web server running and have not configured it well?
Or is it possible that my hacked site?
One of my friends passed some photos through net2ftp.com
I'm really a new developer mac and need help to find the problem.
What does "I can't launch the website" mean exactly?
Can not go you on a browser?
What happens when you try?
It worked before?
FYI, the URL works fine for me, holiday home in the Canton of Valais.
OS X includes the Apache 2 web server that you can activate at any time. However this would be a web server local, and except if you have configured your router is not available outside your own network.
It has nothing to do with your site hosted elsewhere to have a local Web server.
Any Web site can be hacked, the real question is why would anyone? It takes time and effort to hack a site, and it usually requires a goal, the goal or the recovery. Why someone would want to hack into your Web site, and would be someone who takes the time to make it known?
-
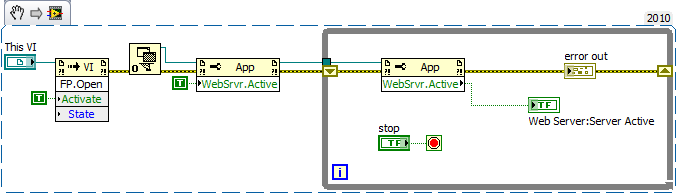
Cannot start web server on the executable file
Hello
We have a problem with a Web server - we cannot get to initialize the help of nodes of property or the ini on a compiled executable file.
As part of our application, we are starting the Web server to publish a status page to be read remotely. This works very well when we are running in the development environment and also when we run an executable a PC with installed development environment, however it will not boot on a PC with just the runtime installed.
I have attached some of the code that functionally does exactly the same thing in our main application. I used this as my Tester code and built in an exe while trying a lot of different things to fix.
When executing:
- The code will sit in the while loop until I press stop.
- Web server: Active Server = FALSE
- Out error = ERROR No.
In the full application the while loop waits a few seconds before throw an error if the server is not started. In this example, I can let the loop running for awhile without leave. Normally, the boot time is<50ms when="">
It's the ini file to the executable file:
[WebTest]
server.app.propertiesEnabled = True
Server.OLE.Enabled = True
server.tcp.serviceName = "My Server computer/VI"
server.vi.propertiesEnabled = True
WebServer.Enabled = True
WebServer.TcpAccess = "' + * '"
WebServer.ViAccess = "' + * '"
DebugServerEnabled = False
DebugServerWaitOnLaunch = FalseAnd it is the Web server configuration file:
ErrorLog "$LVSERVER_ROOT/logs/error.log".
LogLevel 3
The default server name
DocumentRoot "$LVSERVER_ROOT /... /.. '. "/ www".
Listen 8000
ThreadLimit 10
TypesConfig "$LVSERVER_ROOT/mime.types»
DirectoryIndex index.html
LoadModulePath "$LVSERVER_ROOT/modules '" $LVSERVER_ROOT/LVModules "" $LVSERVER_ROOT /... ".
LoadModule LVAuth lvauthmodule
LoadModule LVSnapshot lvsnapshotmodule
LoadModule LVRFP lvrfpmodule
LoadModule dir libdirModule
LoadModule copy libcopyModuleAddHandler LVAuthHandler
AddHandler LVSnapshotHandler .snap
AddHandler LVRFPHandlerAddHandler dirHandler
AddHandler copyHandler"CustomLog"$LVSERVER_ROOT/logs/access.log"'%%u %t \"%r\ hour' % > s %b.
KeepAlive on
KeepAliveTimeout 60
Timeout 60As can side note, anyone tell me where the $LVSERVER_ROOT variable is configured?
I tried the things:
- Copy a new default configuration file before the entry into force
- Writing a predefined file (encoded) before initializing config
- Definition to root before initializing directory (it actually generates an error because the server is not active...)
- Set WebServer.Active = TRUE several times inside the while loop
- Toggle the web server in the ini file
System:
- LabVIEW 2010
- PC with Windows 7 running
Thanks for any help, because it makes me crazy slow!
Ben
Hi Marco, thanks for the reply.
I have this guide was reviewed previously and had done all that he but a small section who gave me a hint of something to try and I have solved my problem, so thank you!
If anyone is interested, here's the problem:
The directive DocumentRoot folder in the config must exist or the Web server cannot be started. So basically, make sure that the file points to a folder that exists!
This leaves two small annoying problems if - you can't see if the file exists (and then create it) before starting the Web server, because you can not query the path to the folder without the Web server running.
AND
You can't really define the configuration programmatically file as parameters from the file are responsible for execution, not on the start Web server.
The result of this is that the config file and the folder root document should be created (and corresponding of course...) when the executable is built / installed on the system. Not a massive headache, but it means do not forget to put things in the build specification and do not rely on software to do the job at startup
-
Cannot access the Web server in the DMZ from the inside using IP global
Hi all
I hope it's a very simple question.
I'm running a PIX 515 firewall v6.3. I set up a Web server in my DMZ and use static NAT for re-branded it overall static IP address. Access from the outside of the demilitarized zone works remarkably well. I can access inside the interface Web site using the internal IP, but I can't access it from inside interface using the global IP are entrusted to him.
Is there a particular reason why this would not be allowed? My feeling was that the request would be forwarded via the external interface (as it is a global IP address) and then be bounced back by my sense of the ISP the request would come to the new external interface (as the static NAT is applied to the external interface).
However if I try and access the global IP from my inside interface, then the browser can not find the server.
can someone explain why this is so? Any information would be appreciated.
see you soon,
Wayne
---------------------------------
6.3 (3) version PIX
interface ethernet0 100full
interface ethernet1 100full
interface ethernet2 100full
ethernet0 nameif outside security0
nameif ethernet1 inside the security100
nameif dmz security50 ethernet2
hostname helmsdeep
domain p2h.com.sg
fixup protocol dns-length maximum 512
fixup protocol ftp 21
fixup protocol h323 h225 1720
fixup protocol h323 ras 1718-1719
fixup protocol http 80
fixup protocol they 389
no correction protocol rsh 514
fixup protocol rtsp 554
fixup protocol sip 5060
fixup protocol sip udp 5060
fixup protocol 2000 skinny
fixup protocol smtp 25
No fixup protocol sqlnet 1521
fixup protocol tftp 69
names of
acl_out list access permit tcp any host 203.169.113.110 eq www
access-list 90 allow the host tcp 10.1.1.27 all
pager lines 24
debug logging in buffered memory
Outside 1500 MTU
Within 1500 MTU
MTU 1500 dmz
IP address outside pppoe setroute
IP address inside 192.168.1.1 255.255.255.0
dmz 10.1.1.1 IP address 255.255.255.0
no failover
failover timeout 0:00:00
failover poll 15
No IP failover outdoors
No IP failover inside
no failover ip address dmz
location of PDM 202.164.169.42 255.255.255.255 inside
location of PDM 202.164.169.42 255.255.255.255 dmz
location of PDM 10.1.1.26 255.255.255.255 dmz
location of PDM 10.1.1.26 255.255.255.255 outside
location of PDM 172.16.16.20 255.255.255.255 outside
location of PDM 192.168.1.222 255.255.255.255 inside
history of PDM activate
ARP timeout 14400
Global 1 interface (outside)
Global (dmz) 1 10.1.1.101 - 10.1.1.125
NAT (inside) 1 0.0.0.0 0.0.0.0 0 0
NAT (dmz) 0-list of access 90
NAT (dmz) 1 0.0.0.0 0.0.0.0 0 0
static (dmz, external) 203.169.113.110 10.1.1.27 netmask 255.255.255.255 0 0
Access-group acl_out in interface outside
Timeout xlate 03:00
Timeout conn 01:00 half-closed 0:10:00 udp 0: CPP 02:00 0:10:00 01:00 h225
H323 timeout 0:05:00 mgcp 0: sip from 05:00 0:30:00 sip_media 0:02:00
Timeout, uauth 0:05:00 absolute
GANYMEDE + Protocol Ganymede + AAA-server
RADIUS Protocol RADIUS AAA server
AAA-server local LOCAL Protocol
Enable http server
http 192.168.1.222 255.255.255.255 inside
enable floodguard
string fragment 1
Console timeout 0
Terminal width 80
Code v6 pix or less don't let you have traffic "back" or return flow via the same interface on which it was sent. Having also your bounce back off of an external server traffic is never a good idea, because you won't be able to distinguish which and rogue attacks by spoofing someone outside your network.
Since you are using pix 6.3 code, you may be able to outside the NAT. Add this static to your config:
static (dmz, upside down) 203.169.113.110 10.1.1.27 netmask 255.255.255.255 0 0
You may need to run a clear xlate after adding the new static statement. Note that the interfaces: it's demilitarized zone, inside inside, dmz.
I would like to know if it works.
-
asa5512 V8.6 nat web server cannot access
Hi all
asa5512 V8.6 nat web server cannot access.
my home pc can access www.cisco.com, but external client cannot access my web server inside...
all of my config, I do not know what is wrong.
Thank youe help.
ciscoasa #.
See the ciscoasa # running
ciscoasa # show running-config
: Saved
:
ASA 1.0000 Version 2
!
ciscoasa hostname
activate 2KFQnbNIdI.2KYOU encrypted password
2KFQnbNIdI.2KYOU encrypted passwd
names of
!
interface GigabitEthernet0/0
nameif outside
security-level 0
address IP XXX1 255.255.255.240
!
interface GigabitEthernet0/1
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/2
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/3
Description link to 3560 G0/1
Speed 1000
full duplex
nameif inside
security-level 100
192.168.1.13 IP address 255.255.255.0
!
interface GigabitEthernet0/4
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/5
Shutdown
No nameif
no level of security
no ip address
!
interface Management0/0
nameif management
security-level 100
IP 192.168.100.1 address 255.255.255.0
!
!
time-range k3used
absolute starting 08:00 January 1, 2008
daily periodical 0:00 to 23:59
periodical daily 09:00-18:00
!
passive FTP mode
clock timezone BeiJing 8
network object obj - 192.168.1.0
subnet 192.168.1.0 255.255.255.0
network object obj - 192.168.200.0
192.168.200.0 subnet 255.255.255.0
network object obj - 192.168.1.2
host 192.168.1.2
network object obj - 192.168.1.2 - 01
host 192.168.1.2
network object obj - 192.168.1.19
Home 192.168.1.19
network object obj - 192.168.1.20
host 192.168.1.20
network object obj - 192.168.1.88
Home 192.168.1.88
network object obj - 192.168.1.1
host 192.168.1.1
network object obj - 192.168.1.2 - 02
host 192.168.1.2
network object obj - 192.168.1.6
host 192.168.1.6
object obj - X.X.X.3 network
Home X.X.X.3
object obj-tcp-source-eq-25 service
tcp source eq smtp service
obj-tcp-source-eq-110 service object
tcp source eq Microsoft pop3 service
object obj - X.X.X.10 network
Home X.X.X.10
obj-tcp-source-eq-8086 service object
tcp source eq 8086 service
obj-tcp-source-eq-80 service object
tcp source eq www service
network object obj - 192.168.1.1 - 01
host 192.168.1.1
obj-tcp-source-eq-3389 service object
source eq 3389 tcp service
obj-tcp-source-eq-9877 service object
tcp source eq 9877 service
obj-tcp-source-eq-21 service object
tcp source eq ftp service
object obj-tcp-source-eq-20 service
tcp source eq ftp service - data
network object obj - 192.168.2.88
Home 192.168.2.88
network object obj - 192.168.2.88 - 01
Home 192.168.2.88
network object obj - 192.168.2.88 - 02
Home 192.168.2.88
network object obj - 192.168.1.19 - 01
Home 192.168.1.19
network object obj - 192.168.2.2
host 192.168.2.2
network object obj - 192.168.2.2 - 01
host 192.168.2.2
network object obj - 192.168.2.2 - 02
host 192.168.2.2
network object obj - 192.168.3.2
host 192.168.3.2
network object obj - 192.168.3.2 - 01
host 192.168.3.2
network object obj - 192.168.3.2 - 02
host 192.168.3.2
object obj - X.X.X.9 network
Home X.X.X.9
obj-tcp-source-eq-8087 service object
tcp source eq 8087 service
network object obj - 192.168.1.200
host 192.168.1.200
network object obj - 192.168.1.200 - 01
host 192.168.1.200
network object obj - 192.168.1.30
host 192.168.1.30
network object obj - 192.168.1.30 - 01
host 192.168.1.30
network object obj - 192.168.1.1 - 02
host 192.168.1.1
object obj - X.X.X.6 network
Home X.X.X.6
obj-tcp-source-eq-8088 service object
tcp source eq 8088 service
network object obj - 192.168.3.5
Home 192.168.3.5
network object obj - 192.168.3.5 - 01
Home 192.168.3.5
network object obj - 192.168.3.5 - 02
Home 192.168.3.5
network object obj - 192.168.3.5 - 03
Home 192.168.3.5
network object obj - 192.168.3.5 - 04
Home 192.168.3.5
network object obj - 192.168.2.0
Subnet 192.168.2.0 255.255.255.0
network object obj - 192.168.3.0
subnet 192.168.3.0 255.255.255.0
network object obj - 192.168.4.0
subnet 192.168.4.0 255.255.255.0
network object obj - 192.168.5.0
192.168.5.0 subnet 255.255.255.0
network object obj - 192.168.6.0
192.168.6.0 subnet 255.255.255.0
network object obj - 192.168.7.0
192.168.7.0 subnet 255.255.255.0
network object obj - 192.168.8.0
192.168.8.0 subnet 255.255.255.0
vpn_list to access ip 192.168.1.0 scope list allow 255.255.255.0 192.168.200.0 255.255.255.0
vpn_list to access extended list ip 192.168.200.0 allow 255.255.255.0 192.168.1.0 255.255.255.0
access-list 101 extended deny ip any host 58.215.78.113
access-list 101 extended deny ip any host 61.139.126.81
access-list 101 extended deny ip any host 61.152.94.154
access-list 101 extended allow host ip 192.168.4.2 all
access-list 101 extended allow host ip 192.168.4.3 all
access-list 101 extended allow host ip 192.168.4.4 all
access-list 101 extended allow host ip 192.168.4.5 all
access-list 101 extended allow host ip 192.168.4.7 everything
access-list 101 extended permit ip host 192.168.4.8 all
access-list 101 extended permit ip host 192.168.4.9 all
access-list 101 extended permit ip host 192.168.4.10 all
access-list 101 extended allow host ip 192.168.4.11 all
access-list 101 extended allow host ip 192.168.4.12 all
access-list 101 extended allow host ip 192.168.4.13 all
access-list 101 extended allow host ip 192.168.4.14 all
access-list 101 extended allow host ip 192.168.4.15 all
access-list 101 extended allow host ip 192.168.4.16 all
access-list 101 extended allow host 192.168.4.18 ip everything
access-list 101 extended allow host ip 192.168.4.19 all
access-list 101 extended allow host ip 192.168.4.20 all
access-list 101 extended allow host ip 192.168.4.180 all
access-list 101 extended deny ip 192.168.4.0 255.255.255.0 any
access-list 101 extended allow host ip 192.168.2.176 all
access-list 101 extended allow icmp a whole
access-list 101 extended allow host ip 192.168.2.3 everything
access-list 101 extended allow host ip 192.168.2.164 all
access-list 101 extended allow host ip 192.168.2.171 all
access-list 101 extended allow host ip 192.168.2.142 all
access-list 101 extended allow host ip 192.168.2.180 all
access-list 101 extended allow host ip 192.168.2.149 all
access-list 101 extended allow host ip 192.168.2.201 all
access-list 101 extended allow host ip 192.168.2.170 all
access-list 101 extended allow host ip 192.168.2.168 all
access-list 101 extended allow host ip 192.168.2.103 everything
access-list 101 extended allow host ip 192.168.2.34 all
access-list 101 extended allow host ip 192.168.2.174 all
access-list 101 extended allow host ip 192.168.2.199 all
access-list 101 extended allow host ip 192.168.2.253 everything
access-list 101 extended allow host ip 192.168.2.236 all
access-list 101 extended allow host ip 192.168.2.214 all
access-list 101 extended allow host ip 192.168.2.110 everything
access-list 101 extended allow host ip 192.168.2.127 all
access-list 101 extended allow host ip 192.168.2.178 all
access-list 101 extended allow host ip 192.168.2.21 all
access-list 101 extended allow host ip 192.168.2.24 all
access-list 101 extended allow host ip 192.168.2.251 all
access-list 101 extended allow host ip 192.168.2.33 all
access-list 101 extended allow host ip 192.168.2.120 all
access-list 101 extended allow host ip 192.168.2.85 all
access-list 101 extended allow host ip 192.168.2.137 all
access-list 101 extended allow host ip 192.168.2.113 all
access-list 101 extended allow ip 192.168.2.20 host everything
access-list 101 extended allow host ip 192.168.2.101 everything
access-list 101 extended allow host ip 192.168.2.106 all
access-list 101 extended allow host ip 192.168.2.140 all
access-list 101 extended allow host ip 192.168.2.215 all
access-list 101 extended allow host ip 192.168.2.107 all
access-list 101 extended allow host ip 192.168.2.234 all
access-list 101 extended allow host ip 192.168.2.15 all
access-list 101 extended allow host ip 192.168.2.55 all
access-list 101 extended allow host ip 192.168.2.41 all
access-list 101 extended permit ip host 192.168.2.13 all
access-list 101 extended allow host ip 192.168.2.133 everything
access-list 101 extended allow host ip 192.168.2.73 all
access-list 101 extended allow host ip 192.168.2.172 all
access-list 101 extended allow host ip 192.168.2.175 all
access-list 101 extended allow host ip 192.168.2.88 all
access-list 101 extended allow host ip 192.168.2.188 all
access-list 101 extended allow host ip 192.168.2.136 all
access-list 101 extended allow host ip 192.168.2.74 all
access-list 101 extended allow host ip 192.168.2.12 everything
access-list 101 extended allow host ip 192.168.2.100 everything
access-list 101 extended allow host ip of 192.168.2.102 everything
access-list 101 extended allow host ip 192.168.2.152 all
access-list 101 extended allow ip 192.168.2.4 host everything
access-list 101 extended allow host ip 192.168.2.5 everything
access-list 101 extended allow host ip 192.168.2.6 everything
access-list 101 extended allow host ip 192.168.2.14 all
access-list 101 extended allow host ip 192.168.2.19 all
access-list 101 extended permit ip host 192.168.2.16 all
access-list 101 extended allow host ip 192.168.2.17 all
access-list 101 extended allow host ip 192.168.2.18 all
access-list 101 extended allow host ip 192.168.2.22 all
access-list 101 extended allow host ip 192.168.2.23 all
access-list 101 extended allow host ip 192.168.2.115 all
access-list 101 extended allow host ip 192.168.2.116 all
access-list 101 extended allow host ip 192.168.2.117 all
access-list 101 extended allow host ip 192.168.2.118 all
access-list 101 extended allow host ip 192.168.2.119 all
access-list 101 extended allow host ip 192.168.2.150 all
access-list 101 extended allow host ip 192.168.2.128 all
access-list 101 extended deny ip 192.168.2.0 255.255.255.0 any
access-list 101 extended allow ip 192.168.3.2 host everything
access-list 101 extended allow host ip 192.168.3.3 everything
access-list 101 extended permit ip host 192.168.3.4 everything
access-list 101 extended allow host ip 192.168.3.5 all
access-list 101 extended allow host ip 192.168.3.6 all
access-list 101 extended allow host ip 192.168.3.7 all
access-list 101 extended allow host ip 192.168.3.8 all
access-list 101 extended allow host ip 192.168.3.9 all
access-list 101 extended allow host ip 192.168.3.10 everything
access-list 101 extended allow host ip 192.168.3.11 all
access-list 101 extended allow host ip 192.168.3.12 all
access-list 101 extended allow host ip 192.168.3.13 all
access-list 101 extended allow host ip 192.168.3.14 all
access-list 101 extended allow host ip 192.168.3.15 everything
access-list 101 extended allow host ip 192.168.3.16 all
access-list 101 extended allow host ip 192.168.3.17 everything
access-list 101 extended allow host ip 192.168.3.18 all
access-list 101 extended allow host ip 192.168.3.19 all
access-list 101 extended allow host ip 192.168.3.20 everything
access-list 101 extended permit ip host 192.168.3.21 all
access-list 101 extended allow host ip 192.168.3.22 all
access-list 101 extended allow host ip 192.168.3.23 all
access-list 101 extended allow host ip 192.168.3.24 everything
access-list 101 extended allow host ip 192.168.3.25 all
access-list 101 extended allow host ip 192.168.3.26 all
access-list 101 extended allow host ip 192.168.3.27 all
access-list 101 extended allow host ip 192.168.3.28 all
access-list 101 extended allow host ip 192.168.3.29 all
access-list 101 extended allow host ip 192.168.3.30 all
access-list 101 extended allow host ip 192.168.3.31 all
access-list 101 extended allow host ip 192.168.3.32 all
access-list 101 extended allow host ip 192.168.3.33 all
access-list 101 extended allow host ip 192.168.3.34 all
access-list 101 extended allow host ip 192.168.3.35 all
access-list 101 extended allow host ip 192.168.3.36 all
access-list 101 extended allow host ip 192.168.3.37 all
access-list 101 extended allow host ip 192.168.3.38 all
access-list 101 extended allow host ip 192.168.3.39 all
access-list 101 extended allow host ip 192.168.3.40 all
access-list 101 extended allow host ip 192.168.3.41 all
access-list 101 extended allow host ip 192.168.3.42 all
access-list 101 extended allow host ip 192.168.3.43 all
access-list 101 extended allow host ip 192.168.3.86 all
access-list 101 extended allow host ip 192.168.3.88 all
access-list 101 extended allow host ip 192.168.3.89 all
access-list 101 extended allow host ip 192.168.3.56 all
access-list 101 extended allow host ip 192.168.3.55 all
access-list 101 extended allow host ip 192.168.3.96 all
access-list 101 extended allow host ip 192.168.3.97 all
access-list 101 extended allow host ip 192.168.3.98 all
access-list 101 extended allow host ip 192.168.3.116 all
access-list 101 extended allow host ip 192.168.3.111 all
access-list 101 extended allow host ip 192.168.3.175 all
access-list 101 extended allow host ip 192.168.3.176 all
access-list 101 extended allow host ip 192.168.3.201 all
access-list 101 extended allow host ip 192.168.3.202 all
access-list 101 extended allow host ip 192.168.3.203 all
access-list 101 extended allow host ip 192.168.3.204 all
access-list 101 extended allow host ip 192.168.3.205 all
access-list 101 extended allow host ip 192.168.3.206 all
access-list 101 extended allow host ip 192.168.3.207 all
access-list 101 extended allow host ip 192.168.3.208 all
access-list 101 extended allow host ip 192.168.3.209 all
access-list 101 extended allow host ip 192.168.3.210 all
access-list 101 extended allow host ip 192.168.3.213 all
access-list 101 extended allow host ip 192.168.3.214 all
access-list 101 extended allow host ip 192.168.3.215 all
access-list 101 extended allow host ip 192.168.3.101 all
access-list 101 extended allow host ip 192.168.3.102 all
access-list 101 extended allow host ip 192.168.3.103 all
access-list 101 extended allow host ip 192.168.3.106 all
access-list 101 extended allow host ip 192.168.3.107 all
access-list 101 extended allow host ip 192.168.3.152 all
access-list 101 extended allow host ip 192.168.3.151 all
access-list 101 extended allow host ip 192.168.3.153 all
access-list 101 extended allow host ip 192.168.3.195 all
access-list 101 extended allow host ip 192.168.3.45 all
access-list 101 extended allow host ip 192.168.3.46 all
access-list 101 extended allow host ip 192.168.3.199 all
access-list 101 extended allow host ip 192.168.3.157 all
access-list 101 extended refuse 192.168.3.0 ip 255.255.255.0 any
access-list 101 extended allow tcp a whole
access list 101 scope ip allow a whole
vpnclient_splitTunnelAcl list standard access allowed 192.168.1.0 255.255.255.0
2 extended access-list permit ip 192.168.2.0 255.255.255.0 any
3 extended access-list allow ip 192.168.3.0 255.255.255.0 any
4 extended access-list allow ip 192.168.4.0 255.255.255.0 any
access-list extended 500 k permit ip host XXX1 everything
access-list extended 500 k allow icmp host XXX1 everything
access-list 102 extended allow host ip 192.168.1.6 everything
access-list extended 100 permit tcp any host 192.168.1.1 eq www
access-list extended 100 permit tcp any host 192.168.1.1 eq 8080
access-list extended 100 permit tcp any host X.X.X.4
access-list extended 100 permit ip any host X.X.X.4
access-list extended 100 permit icmp any host X.X.X.4
access-list extended 100 permit tcp any host 192.168.1.6 eq smtp
access-list extended 100 permit tcp any host 192.168.1.6 eq pop3
access-list extended 100 permit tcp any host 192.168.1.6 eq www
access-list extended 100 permit tcp any host 192.168.1.6
access-list 100 scope ip allow any host 192.168.1.6
access-list extended 100 permit icmp any host 192.168.1.6
access-list extended 100 permit tcp any host 192.168.1.19 eq 3389
access-list extended 100 permit tcp any host 192.168.1.20 eq 3389
access-list extended 100 permit tcp any host 192.168.1.88 eq 3389
access-list extended 100 permit tcp any host X.X.X.12
access-list extended 100 permit ip any host X.X.X.12
access-list extended 100 permit icmp any host X.X.X.12
access-list extended 100 permit tcp any host 192.168.1.6 eq 8086
access-list extended 100 permit tcp any host 192.168.1.1 eq 3389
access-list extended 100 permit tcp any host 192.168.1.6 eq 3389
access-list extended 100 permit tcp any host 192.168.1.6 eq ftp
access-list extended 100 permit tcp any host 192.168.1.6 eq ftp - data
access-list extended 100 permit tcp any host 192.168.2.88 eq 3389
access-list extended 100 permit tcp any host 192.168.2.88 eq 12172
access-list extended 100 permit tcp any host 192.168.2.2 eq 3389
access-list extended 100 permit tcp any host 192.168.2.2 eq 9116
access-list extended 100 permit tcp any host 192.168.3.2 eq 25243
access-list extended 100 permit tcp any host 192.168.3.2 eq 3389
access-list extended 100 permit tcp any host 192.168.1.200 eq www
access-list extended 100 permit tcp any host 192.168.1.200 eq 12001
access-list extended 100 permit tcp any host 192.168.1.30 eq 3389
access-list extended 100 permit tcp any host 192.168.3.5 eq 4160
access-list extended 100 permit tcp any host 192.168.3.5 eq 11111
access-list extended 100 permit tcp any host 192.168.3.5 eq 3389
access-list extended 100 permit tcp any host X.X.X.10
access-list extended 100 permit udp any host 192.168.2.88 eq 12172
access-list extended 100 permit udp any host 192.168.2.2 eq 9116
access-list extended 100 permit udp any host 192.168.3.2 eq 25243
access-list extended 100 permit udp any host 192.168.3.5 eq 4170
access-list extended 100 permit udp any host 192.168.3.5 eq 11111
access-list extended 100 permit ip any host X.X.X.10
access-list extended 100 permit tcp any host 192.168.1.6 eq 8087
access-list extended 100 permit tcp any host X.X.X.9
access-list extended 100 permit ip any host X.X.X.9
access-list extended 100 permit tcp any host 192.168.1.30 eq www
access-list extended 100 permit tcp any host X.X.X.5
access-list extended 100 permit ip any host X.X.X.5
access-list extended 100 permit icmp a whole
access-list extended 100 permit tcp any host 192.168.1.6 eq 8088
access-list extended 100 permit ip any host X.X.X.6
access-list extended 100 permit tcp any host X.X.X.6
access list extended 100 permit tcp host 61.186.169.129 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.129 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.129 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.129 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.129 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.186.169.130 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.130 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.130 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.130 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.130 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.186.169.131 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.131 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.131 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.131 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.131 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.186.169.132 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.132 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.132 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.132 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.132 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.186.169.133 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.133 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.133 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.133 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.133 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.129 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.130 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.131 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.132 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.133 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.129 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.130 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.131 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.132 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.133 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 183.64.106.194 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 183.64.106.194 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 183.64.106.194 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 183.64.106.194 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 183.64.106.194 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 183.64.106.194 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 183.64.106.194 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 183.64.106.195 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 183.64.106.195 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 183.64.106.195 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 183.64.106.195 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 183.64.106.195 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 183.64.106.195 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 183.64.106.195 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 14.107.162.32 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 14.107.162.32 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 14.107.162.32 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 14.107.162.32 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 14.107.162.32 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 14.107.162.32 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 14.107.162.32 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 14.107.247.121 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 14.107.247.121 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 14.107.247.121 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 14.107.247.121 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 14.107.247.121 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 14.107.247.121 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 14.107.247.121 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.128.208.106 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.128.208.106 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.128.208.106 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.128.208.106 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.128.208.106 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.128.208.106 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.128.208.106 X.X.X.2 time-range k3used
access-list 100 extended tcp refuse any host 192.168.1.2 eq 5872
access-list 100 extended tcp refuse any host 192.168.1.2 eq 8088
access-list 100 extended tcp refuse any host 192.168.1.2 eq 3389
access-list 100 extended tcp refuse any host 192.168.1.19 eq www
access-list 100 extended tcp refuse any host X.X.X.2
access-list extended 100 deny ip any host X.X.X.2
access-list extended 100 refuse icmp any host X.X.X.2
pager lines 24
Outside 1500 MTU
Within 1500 MTU
management of MTU 1500
IP local pool 192.168.200.1 - 192.168.200.20 mask 255.255.255.0 vpn_pool
ICMP unreachable rate-limit 1 burst-size 1
don't allow no asdm history
ARP timeout 14400
NAT (inside, all) source static obj - obj - 192.168.1.0 destination 192.168.1.0 static obj - 192.168.200.0 obj - 192.168.200.0 non-proxy-arp
NAT (inside, all) source static obj - 192.168.200.0 obj - 192.168.200.0 destination static obj - 192.168.1.0 obj - 192.168.1.0 non-proxy-arp
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.3 service obj-tcp-source-eq-25 obj-tcp-source-eq-25
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.3 service obj-tcp-source-eq-110 obj-tcp-source-eq-110
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.10 service obj-tcp-source-eq-8086 obj-tcp-source-eq-80
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.10 service obj-tcp-source-eq-3389 obj-tcp-source-eq-9877
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.10 service obj-tcp-source-eq-21 obj-tcp-source-eq-21
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.10 service obj-tcp-source-eq-20 obj-tcp-source-eq-20
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.9 service obj-tcp-source-eq-8087 obj-tcp-source-eq-80
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.6 service obj-tcp-source-eq-8088 obj-tcp-source-eq-80
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.3 service obj-tcp-source-eq-80 obj-tcp-source-eq-80
NAT (inside, outside) source dynamic obj - 192.168.1.6 obj - X.X.X.3
!
network object obj - 192.168.1.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.200.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.1.2
NAT (inside, outside) Static X.X.X.2 5872 5872 tcp service
network object obj - 192.168.1.2 - 01
NAT (inside, outside) Static X.X.X.2 8088 8088 tcp service
network object obj - 192.168.1.19
NAT (inside, outside) Static X.X.X.12 tcp 3389 8001 service
network object obj - 192.168.1.20
NAT (inside, outside) Static X.X.X.12 tcp 3389 8002 service
network object obj - 192.168.1.88
NAT (inside, outside) Static X.X.X.12 tcp 3389 12345 service
network object obj - 192.168.1.1
NAT (inside, outside) Static X.X.X.4 tcp www www service
network object obj - 192.168.1.2 - 02
NAT (inside, outside) Static X.X.X.2 service tcp 3389 8005
network object obj - 192.168.1.1 - 01
NAT (inside, outside) Static X.X.X.10 tcp 3389 9876 service
network object obj - 192.168.2.88
NAT (inside, outside) Static X.X.X.10 tcp 3389 3129 service
network object obj - 192.168.2.88 - 01
NAT (inside, outside) Static X.X.X.10 12172 12172 tcp service
network object obj - 192.168.2.88 - 02
NAT (inside, outside) Static X.X.X.10 service udp 12172 12172
network object obj - 192.168.1.19 - 01
NAT (inside, outside) Static X.X.X.2 service tcp www 8056
network object obj - 192.168.2.2
NAT (inside, outside) Static X.X.X.10 3389 3128 tcp service
network object obj - 192.168.2.2 - 01
NAT (inside, outside) Static X.X.X.10 9116 9116 tcp service
network object obj - 192.168.2.2 - 02
NAT (inside, outside) Static X.X.X.10 service udp 9116 9116
network object obj - 192.168.3.2
NAT (inside, outside) Static X.X.X.10 25243 25243 tcp service
network object obj - 192.168.3.2 - 01
NAT (inside, outside) Static X.X.X.10 service udp 25243 25243
network object obj - 192.168.3.2 - 02
NAT (inside, outside) Static X.X.X.10 tcp 3389 3130 service
network object obj - 192.168.1.200
NAT (inside, outside) Static X.X.X.10 service tcp www 1114
network object obj - 192.168.1.200 - 01
NAT (inside, outside) Static X.X.X.10 12001 12001 tcp service
network object obj - 192.168.1.30
NAT (inside, outside) Static X.X.X.5 tcp www www service
network object obj - 192.168.1.30 - 01
NAT (inside, outside) Static X.X.X.10 tcp 3389 9878 service
network object obj - 192.168.1.1 - 02
NAT (inside, outside) Static X.X.X.4 8080 8080 tcp service
network object obj - 192.168.3.5
NAT (inside, outside) Static X.X.X.10 4160 4160 tcp service
network object obj - 192.168.3.5 - 01
NAT (inside, outside) Static X.X.X.10 service udp 4170 4170
network object obj - 192.168.3.5 - 02
NAT (inside, outside) Static X.X.X.10 11111 11111 tcp service
network object obj - 192.168.3.5 - 03
NAT (inside, outside) Static X.X.X.10 tcp 3389 3127 service
network object obj - 192.168.3.5 - 04
NAT (inside, outside) Static X.X.X.10 11111 11111 udp service
network object obj - 192.168.2.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.3.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.4.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.5.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.6.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.7.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.8.0
NAT dynamic interface (indoor, outdoor)
Access-group 100 in external interface
Access-group 101 in the interface inside
Route outside 0.0.0.0 0.0.0.0 X.X.X.14 1
Route inside 192.168.2.0 255.255.255.0 192.168.1.12 1
Route inside 192.168.3.0 255.255.255.0 192.168.1.12 1
Route inside 192.168.4.0 255.255.255.0 192.168.1.12 1
Route inside 192.168.5.0 255.255.255.0 192.168.1.12 1
Route inside 192.168.6.0 255.255.255.0 192.168.1.12 1
Timeout xlate 03:00
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
identity of the user by default-domain LOCAL
Enable http server
No snmp server location
No snmp Server contact
Server enable SNMP traps snmp authentication linkup, linkdown warmstart of cold start
Crypto ipsec transform-set esp - esp-md5-hmac ikev1 vpn_set
Crypto-map dynamic vpn_map 10 set transform-set vpn_set ikev1
Crypto-map dynamic vpn_map 10 the value reverse-road
vpnmap 10 card crypto ipsec-isakmp dynamic vpn_map
vpnmap interface card crypto outside
Crypto ikev1 allow outside
IKEv1 crypto policy 1
preshared authentication
the Encryption
md5 hash
Group 2
life 86400
IKEv1 crypto policy 65535
preshared authentication
3des encryption
sha hash
Group 2
life 86400
Telnet 0.0.0.0 0.0.0.0 inside
Telnet 192.168.1.0 255.255.255.0 inside
Telnet timeout 5
SSH 0.0.0.0 0.0.0.0 outdoors
SSH timeout 30
SSH version 1
Console timeout 0
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
Server NTP 192.43.244.18
internal group vpnclient strategy
vpnclient group policy attributes
value of server DNS 61.128.128.68
Ikev1 VPN-tunnel-Protocol
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list vpnclient_splitTunnelAcl
cisco 3USUcOPFUiMCO4Jk encrypted password username
type tunnel-group vpn_group remote access
tunnel-group vpn_group General-attributes
address vpn_pool pool
Group Policy - by default-vpnclient
vpn_group group of tunnel ipsec-attributes
IKEv1 pre-shared-key *.
!
class-map 500 k
matches the access list 500 k
class-map inspection_default
match default-inspection-traffic
class-map 2
matches the access list 2
PAM-class 3
matches the access list 3
class-map 4
corresponds to the list of access-4
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
Review the ip options
inspect the netbios
inspect the rsh
inspect the rtsp
inspect the skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect the tftp
inspect the sip
inspect xdmcp
Policy-map 500 k
500 k class
Policy-map 2
class 2
class 3
class 4
!
global service-policy global_policy
context of prompt hostname
remote anonymous reporting call invites 2
call-home
Profile of CiscoTAC-1
no active account
http https://tools.cisco.com/its/service/oddce/services/DDCEService destination address
email address of destination [email protected] / * /
destination-mode http transport
Subscribe to alert-group diagnosis
Subscribe to alert-group environment
Subscribe to alert-Group 13 monthly periodic inventory
Subscribe to alert-group configuration periodic monthly 13
daily periodic subscribe to alert-group telemetry
Cryptochecksum:ecead54d7c85807eb47c7cdaf7d7e82a
: end
ciscoasa# $
ciscoasa #.
ciscoasa #.
Hello
You have changed the source IP address of the order I suggested?
There is no reason to use the 192.168.1.1 IP address as the source of this command "packet - trace" that the source will NEVER be this IP address, because it is a private IP not routable on the public Internet.
Then you can try with the order I suggested.
entry Packet-trace out tcp 1.1.1.1 12345 61.186.236.4 80
I guess that the above command / test failed because you were using the real server IP address as the IP source for the test.
-Jouni
-
We run our site Web of the College on ColdFusion 9.0. We wrote a program ColdFusion that takes submissions of user on a form and submits it to a database and sending them by e-mail.
People are faced with a problem where if they take too much time to submit the form, then it expires and they lose all their comments.
Business owners want to know how long this timeout period is so that they can adequately inform their audience.
Honestly, I don't know if this is controlled by ColdFusion, IIS, or a combination of both, but of course, there is a timeout setting somewhere that can be changed. Can someone point me in the right direction so that I can tell how long they must fill out a form of people?
Thank you!
ColdFusion by default is set for the session and set deadlines for applications on ColdFusion Administrator-> server-> memory Variables page settings.
Out of the box, the sessions are by default for applications in 2 hours and 20 minutes.
You can customize these values in your code as you. SessionTimeOut and applicationTimeOut values can be set either with a tag
OR "thie" property values in an Application.cfc file. Subject to the maximum time allowed for these properties configured in the memory page Variables mentioned above. -
Cannot connect to the integrated Web server
I have a HP p1606dn printer I need to change the IP address. I can't connect to SAP by using the IP address of the printer configuration page. I also tried on a work of the same model printer and cannot connect. I can't understand what I'm doing wrong. I type in xxx.xxx.xx.xxx in the address bar in Internet Explorer which is supposed to be an approved browser. Thank you!
If the Web integrated printer server does not load when the IP address is entered, then means generally is not a direct path between the printer and the computer is trying to access.
You mentioned that you must change the IP address. What is the reason for this change? The network IP addressing scheme changed so that the PC and the printer may appear as on different networks?
I don't know if it will work in your particular situation, because it depends on whether or not it has access to an Ethernet connection. You could try the connected printer to an Ethernet port which would be on the same network as the PC and then access it by IP addressed assigned to the Ethernet address. Once the integrated Web server load, you can manually set the wifi information and then return to the wifi.
-
Info general solution on Internet interface with active web server on microcontroller (Ethernet)
My intention is to have the on-Board Unit (ATMEGA32) located in a remote place, somewhere over the internet (connected via Ethernet) connected (via CANBUS) for the fuel cell system for the measurement data (current and the temperature of the fuel cell).
The end user and/or client must be able to display these data acquired via the browser on the internet. The main objective of this project is to prevent any pc dedicated as a simple web server, so I would like to know your general solutions.
(I noticed that I can't impelent a web server on this microcontroller, but how do I set the GUI to display data on the browser for users?-I want to say I'm not accurate if the designed GUI (LabVIEW or c SHARP) must be in the internet (solution host & domain) or there are better solutions for her.)If you have a solution for the web server on the microcontroller and are convinced that architecture will work, it seems that your question is how to write a client for data.
Some of the things you're talking about sounds like you want the web server on the microcontroller to respond to a fully functional GUI to any client. This may not be practical because of the computing power limited on the microcontroller and the difficulty of setting up and maintaining this type of server in a microcontroller environment.
A more common architecture that I've seen is just to serve the raw data and let the client user to interpret the data and display them as graphics, etc., this means that the user must Access the microcontroller of a computer running a client that you make.
You can use the communication/protocols/http client in labview palette or you can write a c# client that it is really a question of what data you need to acquire, and what language you are most comfortable in.
-
We try to remotely administer printers HP OfficeJet Pro 8500 A909g Wireless
M/N: CB023A
They print and scan very well, and we can access the home page of each printer EWS.
We have been asked to make a few changes and cannot go beyond the EWS username and password authentication request.
In my view, it has been defined by a previous administrator, but him documented names of user and password we have on file do not work.
How do reset us the EWS password?
I havethe default value is EMPTY, but if not, that would be the default password after reset? SOLVED!
Then I got a job to another printer HP OfficeJet 8 X 00-
All you have to do is RESTORE network defaults on the front control panel - this will reset the default value:(1) requirement for access password turned OFF
(2) default user name is ADMIN
(3) password is EMPTY
then, on command before Panel set your IP network information, and you will then be able to access the built-in Web server and see all / manage all settings, including resetting the password to the web server integrated EWS.
WITH THE SUPPORT OF HP NO.
-
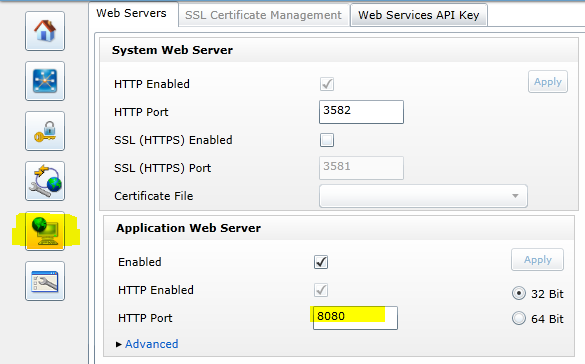
Turn off NI Application Web Server
Does anyone know how to turn off the NI Application Web Server. It's hammering away on a port I need for an application. I opened up the .ini.default file and considered changing the default port (which is 8080). Would that result in issues? What about preventing it from starting up in bootup. I don't see it in my msconfig file.You can change the default port by using the Configuration Page of the Web server safely. Read the white paper in the section flags 'Web Services created by LabVIEW' to the location: http://www.ni.com/white-paper/12402/en/
The white paper says http://
: 5353 for the Web server configuration page, but the next Help topic now says http:// : 3582 to access the interface: http://zone.ni.com/reference/en-XX/help/371361L-01/lvhowto/ws_enable_web_server/ Then on the tab of the Web Server Configuration, you can set the port:
-
System Web Server error: don't overload - no free workers
Has deployed several panels of remote façade on via LV 2015 CRIO-9067. Connection works fine, but after some time, connecting to files html becomes generally intermittent and eventually completely impossible to access. The error is 503 - Server overload error. Went to dig into log files and found the following in /var/local/natinst/log/SystemWebServer.log:
AppWeb: error: no free workers. Increase ThreadLimit. (County of 10 out of 10)
Any thoughts? Could spread free workers in SystemWebServer.conf but unsure of other impacts.
Hi BDA_VAN1,
I couldn't find a way to complete the connections, but the Web server should terminate connections when they reach the time-out limit (which I believe is of 60 seconds by default).
You can go into the NISystemWebServer.conf file and increase the number of allowed connections. There is an article in the knowledge base that works through this process. This can be used to see the error, but it can also give other connections that have been implemented a chance to timeout.
-
How can I send a HTTP request to a web server using TCP?
I'm writing a HTTP string to activate a script CGI, server of our company. It seems that the OPEN TCP CONNECTION works. Can I just use the TCP WRITE function to send the HTTP request string to the server?
Thank you
TimI know that I probably would have finished faster if I had the Internet Toolbox, but the solution ends up being pretty simple with just the TCP features.
Here is the solution, I came with yesterday (in the case where someone else needs) after searching Protocols TCP as suggested by "Laboratory Viewer" and examine details in the riding of developer. It ends up being only a string of 4 line.GET HTTP://proxyserver/path/file.asp?id=test HTTP/1.1
HOME roxyserver
roxyserverThe first line of the string is made up of three things:
(1) the GET command
(2) the URL of the program target (in this case an ASP program that distributes a message preset)
NOTE that in this case, the URL contained "HTTP://proxyserver" and not only the path to the file. If your not using a proxy server, you can probably omit the name of the server of the URL, but you must always the name of the host server to the second line.
(3) the HTTP version usedThe second line is the host server.
The last two lines are empty, but the two are apparently necessary to properly close the TCP request.
Vi uses an OPEN TCP CONNECTION to connect to port 80, then the 4 line string is sent with a WRITING of TCP and the connection is closed with a NARROW CONNECTION of TCP.
In my application, when the piece of equipment monitored by LabVIEW begins to enter a dangerous to use, LabVIEW uses this vi to send the HTTP request through the TCP connection and a program of target ASP on the company's web server. The ASP reads the message ID (? id = test) and sends the message page and the text messaging appropriate to maintenance and engineering personnel. People warned by text pagers are supposed to respond immediately.
Our DSI wrote the ASP that allows you to set the ID of multiple message with different distribution lists. Each message is triggered with a different ID of the virtual instrument according to the gravity of the situation.
Thanks to other amateurs who have published their questions and their answers. Hope someone else finds this useful.
-
Hello
I assumed it would be easy, but I'm not having any luck here... I would create a VI to read each of the .cvs file located on a local web server (see imagesfor more details). Any suggections?
Thank you
Pete
PJackson wrote:
I can stick this same path in the Open box of excel and the data loads perfectly...
This is because Excel does some fancy way, analysis, sees the URL and load the file on the web rather than from the local disk. It is in no way standard behavior (although perhaps, it will be in a few years). Until then, you can not treat a URL - an address for a file on a remote web server - as a local file. RavensFan suggestion might work if you set the sharing of files on the remote computer, but then you do file sharing, do not download from the web. To download a file on the web, use the HTTP screw or a Datasocket Read, which is probably the easiest option here. For Datasocket Read, provide the URL (http://10...) as well as the connection to the wire one string empty type. You will have the entire file as a string on the output data, which you can subscribe to the channel of spreadsheet in table for a table.
-
Here's a question I'll get lucky with. I have a VI, set to be reentrant, broadcast via the web server. The main instance of the VI is never worked with: it's a clone whenever someone accesses the correct URL, and the user interacts with the newly created clone (never the main forum). A clone is able to configure and calling instrument VI when good IDs are entered, which translates to browser popups that are controllable on the end of the user (even if only one user ever does both. To clarify, many clones can be opened simultaneously for connection purposes, but that a user never interacts with the instruments that are not themselves reentrant).
If the user clicks on my Logout button in their browser, it is trivial to close these instruments other, independent and properly clean. But if the user simply click on the red X in their browser, it is non-stop and the instruments that the clone called stay open on the server, when they close.
My experience so far:
No close panel? event seems to be triggered in the clone. The clone simply cease to be.
The remote_panel_connections property doesn't seem to work properly in this case (I have not had luck so far), since it is possible that more than a clone to be active and that the main parent who is spawning clones stays running, but is not interacted with in some way.
What I need:
One way for the clone of VI recognize that the user has closed his browser and communicate that it closes all the assets of VI before ending.
--------------
I would like to avoid forcing the instruments that the clone call to constantly query to see if the VI clone is present on the network. If there is no other solution, but this, I would appreciate a suggestion as to the intensive way less code and resources to implement this type of interrogation, as the instruments are really designed to be totally independent after they are called, rather than under vi.
Thanks for all comments, let me know if you need more information.
MTdev wrote:
One way for the clone of VI recognize that the user has closed his browser and communicate that it closes all the assets of VI before ending.
When a VI stops running, any reference as a queue is also cancelled. You can make use of this fact. If your original clone VI could launch a second reentrant VI, which remains active, you could channel all communications to the instruments via VI second using a queue created in the first. When the first VI disappears, it will trigger an error waiting waiting VI in the second (no vote office is involved). The second VI can take all the necessary measures.
Maybe you are looking for
-
10.11.4 update hangs and does not restart
How you can install this update because it seems to corrupt the computer hangs after that it will restart
-
Re: Satellite A350 - subwoofer issues
Hello My laptop is a year and a bit old. It's a Satellite a350. About 5 months ago my sister played music at a volume very important and this resulted as a crackling and popping sound coming from the speakers all the time except when the mute. I just
-
I have windows xp pro sp3 and since I installed the fix wmp 11 Report Center that my disc is not readable in spite, I can play cds/dvds.and data also Impossible to install wmp! so the fix Center report as nero burning plugin causes wmp to crash or do
-
Windows Vista does not boot, black screen after "windows loading files...". »
I have a laptop HP Pavilion dv2000, it came with windows vista, so I don't have a boot disk. When I try to start it, it will say "windows loading files...". "with a bar, once the bar is loaded it will say microsoft Corp. (with the copyright symbol) a
-
I have 10 windows, my child has windows 7. How can I get family safety to work?
The subject says most of it. I have used parental controls to set up parental controls Web site, however, it is said that it applies only to the windows 10. My child's computer to Windows 7. I tried to connect from his machine to implement control