Cisco 4402 and LDAP
Here's my situation:
I try to connect a user through the 4402 wireless using an LDAP server for the SECURE network. VLAN for secure network is 102.
Security, LDAP (port 389) is authenticated and not anonymous.
Local wireless networks, (profile name) SECURE, no security layer 2, layer 3 is none, web strategy & authentication are checked. AAA Server LDAP Server tab listed under server 1 and only LDAP is listed under "used for authentication of the order.
Access point has a DHCP address, but the wireless still happens as without IP address limited connectivity.
Stuart,
This looks like a DHCP problem. What VLAN is the WLAN in? I want to make sure you say sure is 102, but then later about 112 and 131. That provides DHCP for the WIFI network? What do you see when you rang a client of debugging < client="" mac="" addres=""> ?
Tags: Cisco Wireless
Similar Questions
-
Cisco VCS and LDAP for authentication of users
I have a question about setting up LDAP for authentication of the user on the VCS. I want to have redundancy in my LDAP link. I believe that this is possible by setting a FULL domain name to the address of the LDAP server, then selecting a type of SRV resolution. What I'm not clear on is what the value for the server address would be if I used actually as SRV type of resolution. I should also add that I am looking to use TLS
To clarify, if my AD domain name is myad.netcraftsmen.net. I have set the field as server address:
myad.netcraftsmen.NET: assuming that VCS properly interrogate the DNS for the _service._proto correct parameters?
or would I need to create an SRV record to that effect and set the field server address with the address (including the fields of _service._proto)
or I need to specify one of the SRV records formats used by MS AD areas (there are several).
If the latter, then what SRV record for TLS. I don't see records with port 389 (non-secure).
My intuition tells me that this is probably the first option, but I could be far away.
Anyway, thanks in advance for any input.
Kind regards
Bill
Hi William,.
I just checked it on a X6.1 VCS, and it seems that VCS searches SRV _ldap._tcp.domain (where 'domain' has been entered as the server address), both when the encryption is set to 'None' and 'TLS '.
Hope this helps,
Andreas
-
AnyConnect user using the user certificate authentication and LDAP authentication
Hello
I'm trying to implement the Anyconnect VPN for my office. Now, I want the user to authenticate the user certificate based (which is install user local system are we) CN value and LDAP authentication. A help how to achieve this requirement. We install Certificate ROOT and INTERMEDIATE Godaddy and even already installed ASA. Also, we have the user certificate installed on each system user to authenticate the user.
Any help please.
Hi subhasisdutta,
This link will certainly help you with the configuration:
http://www.Cisco.com/c/en/us/support/docs/security/AnyConnect-secure-mob...
Hope this info helps!
Note If you help!
-JP-
-
Helps to configure a Cisco 4402 wireless controller
Hello
I need help setting up a Cisco 4402 Wireless Controller. I want to have users automatically connect to the wireless network, but not to have access to all the resources network until they open a web browser and provide their domain user name and password or a guest account provided by the receptionist.
I tried many different configurations but can't seem to make it work properly. More time then not when I put on the WIFI network security it causes my wireless network to disappear from the list of wireless avaialbe.
Here's my network configures:
1 - 4402 wireless LAN Controller
2 - Aironet 1130AG antennas
1 - 5510 cisco ASA
1 - 4503 core Router\Switch
8-2960G switches
Windows domain Server 2003 with RADIUS running on the domain controller.
Thanks in advance for the help.
Glad you got it working...
-
Cisco VCS and integration Lync2013
Hello!
Could you tell me please, when CISCO officially support Lync2013 - free new software for VCS - C and documentation on integration?
The main interest is the possibility of transferring video between CISCO/MCU and Lync endpoints on the H.264 Protocol, who hails from Lync2013.
Right now, I've got VCS - C and RTM Lync2013 X7.2. During the video call without AMGW appeal established as audio only.
When using with Lync2010, it worked on Protocol H.263 and CIF resolution.
Evgeniy salvation,
We are currently investigating the possibilities to achieve interoperability between Lync 2013, VCS and video devices on the side of the VCS standards-based, it is a work in progress and at this stage, it is to early to provide any factual information on when interop will be available.
In contrast to Lync 2010, Lync 2013 does not support H.263 for video and it so that will remove the OCS/Lync integration. I do however think that you should be able to make a two-way video between Lync 2013 and VCS-joined endpoints if you use an AMGW tried that yet?
Thank you
Andreas
-
Backdoor in Cisco routers and firewalls.
The more I read on the NSA scandal (and Yes, I apparently a scandal) less I trust corporations hardware and software. There is no reason for anyone to doubt that all Cisco equipment comes with a backdoor. Because these probable backdoors exist it's a matter of time before hackers discover and exploit them. It's happened to Microsoft a number of times and there is no reason that it could not happen to Cisco. It is no longer our trust Cisco equipment and have already started researching alternatives network.
It is more a crazy conspiracy theory, that is the reality.
In all liklihood, we use a series of firewall to further isolate our network against intrusions. To reduce costs, we can keep our existing in this topology Cisco equipment, but we will replace hardware Cisco when it breaks down or needs to be upgraded. I do the same thing with my home network.
In the last months, we already moved all of our e-mail to secure servers overseas and changed all our McAfee, AVG and Avast antivirus software. We are also researching Linux distributions to replace Microsoft.
If Cisco wants to protect their brand, they need to take a stand or see their market share continue to erode. There must be a CEO to a U.S. company that will take this position and be a hero rather that continue to be a lap dog.
Hello
use open-source based linux firewalls and routers.
and check the source cod
-
Cisco show and share to publish on the internet
Dear Experts
We have new deployment for Cisco SNS, and we publish SNS on the internet. I need help to do it and any recommendations, please.
Thank you
Richard
Hi Richard
Solve you your problem? I have to make sure of the following.
1. you can access external SNS internally.
2-natting is ok between IP Public & private.
3. for the DNS record, make sure that the name must be the same on the inside & outside. For example internlly vod.bnp.med.ca and create a record public vod.bnp.med.ca should be the same FQDN, otherwise your SNS will never work. For authentication, you must publish the DMM.
Note: your question this internal FQDN differs from the external FQDN of the SNS.
Thank you
Please note all relevant information
-
I am very new to Cisco ISE and Meraki. I try to get the Radius configuration for wireless authentication. When I do a test of the Meraki to ISE, it passes.
When I try to connect from my laptop, I look at the logs of the Radius and it passes; However, it does not connect me to good policy. I keep hitting the default policy. I have my Meraki police above the default policy in the strategy defined in article. I have attached what looks like my strategy game.
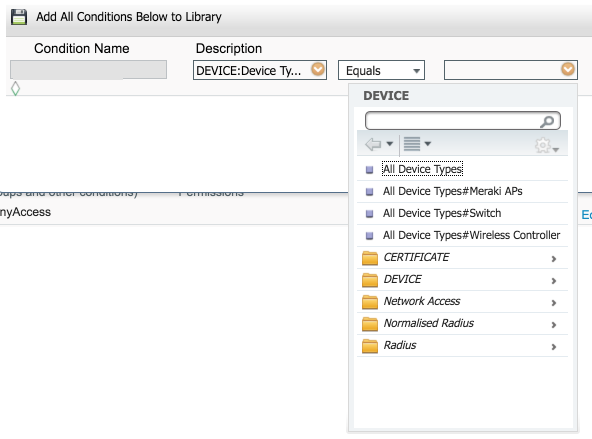
Devices does not really matter. Here is what I see when I create a device group (where you add the access point to this group), and then create the condition:
And here is where I create the condition of strategy game and you should be able to select the Meraki access points:
This will give you the condition similar to what I posted above. This is perhaps why you aren't hit that is not matching the condition for this game.
-
Cisco ACS GANYMEDE + AAA can be activated for telnet to Cisco 600 and 700 routers?
Unfortunately you can not configure radius AAA or Ganymede in routers series 600 or 700.
-
The traffic load between the power of Cisco ASA and FireSight Management Center fire
Hi all
I have a stupid question to ask.
Can I know what is the traffic load and the e/s flow between firepower Cisco ASA and FireSight Management Center?
Currently working on a project, client require such information to adapt to their network. Tried to find in the document from Cisco, but no luck.
Maybe you all have no idea to provide.
It varies depending on the number of events reported from the module to the CSP. No event = only health controls and policy changes are exchanged. 10,000 events per second = much more traffic.
Generally it is not a heavy load, however.
-
Configure to integrate Cisco ASA and JOINT
Hello
We have Cisco ASA and JOINT, need assistance on the integration of the same thing; Please email me so that I'll share the details of the architecture.
Thank you best regards &,.
REDA
Hi reda,.
If I correctly your diagram, you do not want to send any traffic from the external switch to the JOINT with a SPAN port and all traffic from your DMZ interfaces with another.
Is this correct?
If so, can you tell me why you want to inspect the traffic before it goes through the firewall? As I said in my original answer, we generally advise putting IP addresses after the firewall.
Not to mention that in your case, I guess that some traffic will be inspected twice so you will need to assign a different virtual sensors to each JOINT internal interfaces to ensure that the same instance does not see the traffic of several times.
Kind regards
Nicolas
-
What is the difference between Cisco NAC and ACS?
I am currently part of a new construction project and my Cisco account manager and sales engineer recommend Cisco NAC for our new MDF. I'm confused because I don't clearly know the difference between a Cisco ACS and the NAC. What is the difference?
Thank you
Chris
Chris,
The two are completely different, maybe the sales rep could present you with more information and application. Each offers a variety of services tailored to the specific needs. I think that we need to read more in depth on the proceeds of the NAC. NAC seems an excellent solution for authentication authorization but other regulatory compliance.
When you see ask your representative to sales for more information/demo.
ACS is more widely use as a central point to access control to network devices routers, an example is for acs accounting management and the authority to order on all devices on the network using acs as RADIUS server. Considering that the NAC is over a central point of safety inspection on earlier systems of access to your network by via LAN or outside, an example of these respected regulatory defined could be inspections could be virus definition checks before getting lan access thus preventing access to the LAN if the system does not have regulatory compliance defined in NAC access is denied. Another example could be the unknown local host connections etc... So, it seems that NAC is a much broader product that provides endpoint security internal, not only the authentication authorization as acs... ACS has been there for a long time, NAC is rather new product.
NAC
http://www.Cisco.com/en/us/NetSol/ns466/networking_solutions_package.html
ACS
http://www.Cisco.com/en/us/products/sw/secursw/ps5338/index.html
Rgds
Jorge
-
Turn on the mtu on cisco switch and cisco user server
Hi all
someone got bad luck turning on the mtu on their cisco switch? I guess I need to turn it on for all because the command is for all ports on cisco catalyst and my server switch is nearby to my user of switches and a broadband bandwidth 6 G or 6 ports, I need to turn it on for all user ports?
Thanks for any comments, that you can add.
I assume you mean Jumbo frame support! You shouldn't have any problems with that. Please take a look at for example http://www.cisco.com/en/US/products/hw/switches/ps700/products_configuration_example09186a008010edab.shtml for more details and the configuration of the different switches. According to the model, the parameters are for dedicated ports only or the entire switch. In the case of the switch everything you will need to reload (reboot) switch, so be careful.
André
-
Hello
Is it possible to integrate companies to lower COSTS and LDAP?
There may be samples of it?
Thank you in advance,
Kioshin10
Hello and sorry for the delay.
It is possible to integrate companies low-cost with LDAP, but we do not have a concrete example of how to do it. You must use external authentication API and we have a few examples of how to create a valid authentication given a username token and a unique id.
Basically, it is the case:
-your client authenticates in your LDAP system on your back-end server (via a HTML form or a Flash application that interacts with your server).
-Once authenticated, you take a 'unique identifier' your LDAP "record" (the uid, gid/uid or possibly unique name but I wouldn't recommend that) and the user name and use it to generate a token for a specific session authentication in a room.
-and then send you the token to your Flash/Flex client or to start a Flash/Flex client that will connect to the specified room and authenticate with this token.
In general, ACC does not require strict integration with your authentication system. Log into your system and then generate a signed token that tells companies to lower COSTS that the user 'exploit' this token is a valid user who was allowed access to a specific room.
Anyway, please check the documentation and samples for external authentication and if you have any specific questions, or you enter the implementation details and need more help, feel free to ask here.
-
ISE of Cisco protocols for ldap and Windows wireless client
Only protocols below are supported by ise in combination with ldap identity sources.
EAP - GTC, PAP, EAP - TLS, PEAP-TLS.
Peripheral Mac OS appear to be able to use these, but Windows users seem to have problems. How windows users must connect with ise that only uses the ldap Protocol?
You can use the anyconnect Network Access Manager. Just out of curiosity why ldap on join ise to AD?
Sent by Cisco Support technique Android app
Maybe you are looking for
-
Lately, the trackpad is not getting detected on my MacBook Air power. I don't see the pointer of the trackpad. Sometimes I have to turn off and then turn on one or two times for the trackpad pointer appears on the display. Can someone guide me to sol
-
How can I change the default start in 32-bit mode mode
This is the message I get when I try to download my music to Musicnotesorder: Sorry, this plugin requires that your browser run in 32-bit mode. To change the startup by default Firefox 32 bit mode, click on the screen and select the menu item: "Show
-
How can I access the toolbar which includes "file, print" etc.? How can I change the font size of my hotmail home page? It used to be using "display".
-
The Task Manager shows only the connection information of network with no menu - how to fix?
I when I try to open the task manager of the only information that appears is the news of network connections. There is no menu, and when I right click the only option is to close.
-
How will I know that my hard drive is when it starts to work by itself?
I'm going to step away from my computer for a while, maybe just to read for half an hour, and then I noticed that the drive works. How will I know what he does? I want to really just to ensure that some spyware or something malicious does not on my