NEITHER Application Web server refuses to be activated
I am trying to deploy a web service in LabVIEW 2010 and it fails to deploy in saying that the Web of Application service OR work...
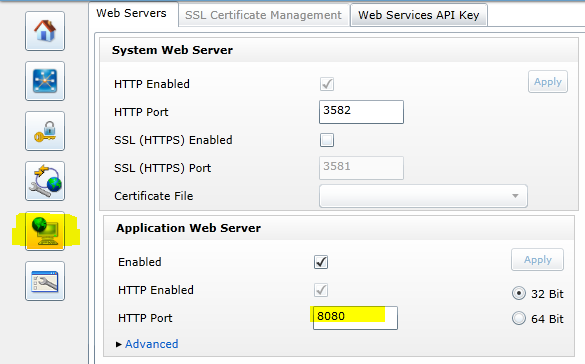
If I connect to http://localhost:3580, log in as Admin (empty password) and click on the page of web servers. I put the server to Application Web 8080 port, click on the check box turn on... then click apply - and the only thing that happens is that the browser displays the error on the page symbol in the status bar... There is not 'yes', showing next to the Enable checkbox for the web server of the system...
So - if I start again from zero and do the same thing, but also click the 32-bit option button before hitting the button apply - what is happening? Well, I get an error dialog box:
The service itself (32-bit, 64-bit is registered but not also started) runs according to the services control panel...
I'm stuck... If anyone knows what is missing here, is there something I am doing wrong, or something that must be done before activating the application service?
Uninstalling and reinstalling 32-bit LabVIEW 2010 on two different computers revealed that the problem appeared only on my Vista 64 bits - not the Windows 7 32-bit macine macine...
By looking at the services that are running on the machine with the problem that I could see that he was running the 32-bit version of the application Web server, had a 64-bit installed but disabled--but--only the latter has been fixed to depend on the Web Server service of NOR. This seemed a bit strange that the 32-bit version on the 32-bit computer was dependent on the Web server of OR...
So - I disabled the 32 bit Server Web Application service OR, turned on the 64-bit... and - I am now able to configure the Web application server to start.
Why so the 32 and 64-bit application Web services installed, with only 32 bit one running-, but not properly? This happens to everyone, but everyone arranges it by opting for the 64-bit version... or is there something that causes the installation get messed up?
Tags: NI Software
Similar Questions
-
Turn off NI Application Web Server
Does anyone know how to turn off the NI Application Web Server. It's hammering away on a port I need for an application. I opened up the .ini.default file and considered changing the default port (which is 8080). Would that result in issues? What about preventing it from starting up in bootup. I don't see it in my msconfig file.You can change the default port by using the Configuration Page of the Web server safely. Read the white paper in the section flags 'Web Services created by LabVIEW' to the location: http://www.ni.com/white-paper/12402/en/
The white paper says http://
: 5353 for the Web server configuration page, but the next Help topic now says http:// : 3582 to access the interface: http://zone.ni.com/reference/en-XX/help/371361L-01/lvhowto/ws_enable_web_server/ Then on the tab of the Web Server Configuration, you can set the port:
-
Activation of scripts on the Web server
I found this, but cannot locate Scripting on the Web Server: Configuration page
Activation of scripts on the Web server
To use the script with a Web service, you must enable the feature on the Web of LabVIEW server. In LabVIEW, select the script on the Web Server: Configuration page in the dialog box Options to enable the use of scripts on the Web server.
http://zone.NI.com/DevZone/CDA/tut/p/ID/7738
It seems that scripting is enabled automatically.
-
the difference between the Web application server and Web server?
What is the functional difference and the relationship between the Server Web applications and Web server, for example: Weblogic is the Application Web server, IIS is the Web server, Apache is the Web server and Oracle Application Server is the Application Web server? Someone said, Web Application Server is a Web server, but more functional superset, seems in this case, we can also use a server of web applications as a web server. For example, we can use Weblogic, but do not use IIS and Apache, please correct me?
Published by: user2571802 on February 28, 2010 18:51Hello
Have a read of http://www.javaworld.com/javaqa/2002-08/01-qa-0823-appvswebserver.html if all goes well it should give you a little more understanding.
See you soon
John
http://John-Goodwin.blogspot.com/Published by: JohnGoodwin on March 1, 2010 08:17
-
Not possible to activate the scripts on the Web server
Hello
I would like to create a page .html for Web with a bit of scripting ESP included - Services because now I understand just this:
<% for (i=0; i<3; i++) {
...some text...
} %>According to this document NOR, I first need to enable scripting:
To use the script with a Web service, you must enable the feature on the Web of LabVIEW server. In LabVIEW, select the script on the Web Server: Configuration page in the dialog box Options to enable the use of scripts on the Web server.
I activated the Web server and it works OK. But there is nothing called "Scripting" in the configuration page - and the script is executed (the code is just printed in the form of simple text).
Anyone know how to activate the ESP script?
Version: LV 2012.
Best regards, Jan
Hi Jan,
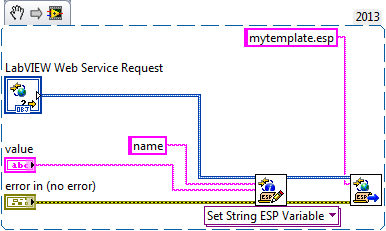
In fact, you use the ESP file instead of a static HTML file. For example, if we had the static html file:
Hello world
This file can be located at something like /MyWebService/HelloWorld.html.
If I then do something like have a page to say "Hello, Jan" or "Hello, Mark" I could use ESP. In this case, your code might look like:
<>
var xname = form ['name'];
%>
Hello, @@xname
The URL of such a web method is perhaps something like jan/MyWebService/Hellovar/Jan where Jan string literal passed to the terminal of a web method that can resemble
In this example, the string "Jan" is passed to the terminal of the value of the VI. What implementation of the Web method in the spec to build his signature might look like in /Hellovar /: value.
So, back to your original question. You embed not ESP breast and the HTML document. Instead, you embed HTML inside a document of ESP and the rendering of the document in HTML format when accessing the URL of the Web method. While the paper you mentioned earlier has an example project in that you can use as a reference
-
I sent the otainstall files in the IIS web server. I put for .cod mime types and
extensions at the server level .jad.
When I download the .cod from the server, it shows error of unsupported media type.
Any help would be much appreciated.
You open the JAD file in the browser BlackBerry or trying to load the COD file directly? You need to open the URL of the JAD file. Also make sure that the MIME types for JAD files have also bee configured.
MIME types required for a web server use BlackBerry smartphone applications
-
Web server on a DMZ and Active Directory
It is a question facing two part philosophical part technical.
If I have a new Win 2 k 3 web server that I put on my DMZ is stupid to allow him to join my AD domain by opening the appropriate ports for communication between the inside and DMZ AD interface interface?
Or who simply goes against Smart Firewall? Can an attacker cross from outside intf in DMZ within intf?
If it's a wise thing to do, how to do? I guess just to open the ports that use MS as 135 137, netbios, 139, and 445 (I forgot everything?). Am I missing?
Thanks for any advice, technical or philosophical.
Marc
I would put it no doubt inside. In this era of virus, worms, software, spyware, p2p, etc., your users applications are often (in general not as malicious) also dangerous than the outside world. Use a DMZ for MS products is darn almost impossible, unless it is limited filtering (blocking access to users to SNMP, terminal services and other management fixed ports) in a position that allowed default value (rather than the general practices of firewall failure deny and selectively permit).
Because of the need for a relatively open between the clients and servers MS, I have a pretty aggressive policy of hardening, patching and antivirus.
If you try to put your DMZ, you can determine how your internal users could access it. If they are accessing the interface of http as well, it's good (some applications have two web interfaces as client binary packages well too big that use different, sometimes dynamic ports). You could then selectively allow access to the ip address of sql for ad servers only and open a ton it things. Yet, there is the risk that if this box has been compromised, it could be a conduit for other hosts. Because this kind of things MS is such a puzzle to the DMZ, I generally recommend people think about hardening the servers instead of trying to force the DMZ piece square into a round hole.
For IIS, look are the IISLockdown utility, which is a supplement on win2k/NT4 and perhaps be included out of the box on win2k3. It is menu-driven and can help you disable stuff you don't need. Hacking exposed Win2k is a great book to pick up. The NSA.gov has guidelines of security for most of the server MSFT products.
-
Configure the web server and application server deployment hangs in 11.1.2.2
Hi all
I want to install Hyperion 11.1.2.2 with Oracle 11.2.0.1 database. I installed all the modules successfully.
At configuration time, I set up the Foundation Hyperion Essbase, planning and reporting with success.
But the question, when try to configure HFM and FDM EMP Configurator crashes, in HFM Web server configuration and application Web of FDM configure FDM.
I installed IIS, Oracle 32-bit and 64-bit, the Clients, and also configured DCOM.
What comments can you do on this point, if any body faced the same question.
See you soon,.
Mady
Hi all
We reinstalled hyperion again
then it works fine.
Kind regards
Mady
-
storage of static content on the application server or Web server
Hello
Is it worth to separate the static content such as images, css on separate web server and application server.
We use version10.0 of Oracle weblogic server.
Please, share your experience.
Thank you
/ AshwaniDecision to store static content on the Application Server or Server Web is dependent mainly on below facts.
(1) total size of static content
(2) frequency of use of static content
(3) Machine accommodated for application server performance
(4) the network speed between the Web and application servers
(5) level of security of the information processing application and pages
(6) is static content created on demand?
(7) review delays in deployment and added additional efforts.Let me know, if you can understand this impact on decisions facts? another I'll spend the time to write more.
Thank you
Mahi -
How to separate the application server and web server on the level of physical servers?
I want to separate the application server and web server: locate on different hosts. Generally, we use Weblogic ACE. In the future maybe use Apache Tomcat as web server.
Example,
192.168.1.10 - as - Weblogic application server / module EJB
192.168.1.11 - as a Web server - Weblogic / WEB module (can be - Apache Tomcat)
Impossible to find examples and resources about it on google.
Thank you.So, if we're looking for a subject such as:
try { someEJB = context.lookup("ejb/Videotheek#model.logic.Videotheek"); } catch (NamingException e) { e.printStackTrace(); }If the EJB application is clustered in an object of type ' ClusterableRemoteRef (-4005477377232786958S: 172.31.0.107: [7003,7003,-1,-1,-1,-1,-1]: [8351443287261246917S:172.31.0.107:[7002,7002,-1,-1,-1,-1,-1]:ScriptDomain:VideotheekServer1/292])/289 172.31.0.107:ScriptDomain:VideotheekServer2 - 4005477377232786958S:172.31.0.107:[7003,7003,-1,-1,-1,-1,-1]:172.31.0.107:ScriptDomain:VideotheekServer2/289,-' is returned, which is part of the wlfullclient.jar.)
You can try using the EJB or the annotation of the resource (do not know with certainty if Tomcat is favorable). For annotations work, you must use version servlet 2.5 or later. JNDI research work in a general such as for example Tomcat servlet container.
-
Info general solution on Internet interface with active web server on microcontroller (Ethernet)
My intention is to have the on-Board Unit (ATMEGA32) located in a remote place, somewhere over the internet (connected via Ethernet) connected (via CANBUS) for the fuel cell system for the measurement data (current and the temperature of the fuel cell).
The end user and/or client must be able to display these data acquired via the browser on the internet. The main objective of this project is to prevent any pc dedicated as a simple web server, so I would like to know your general solutions.
(I noticed that I can't impelent a web server on this microcontroller, but how do I set the GUI to display data on the browser for users?-I want to say I'm not accurate if the designed GUI (LabVIEW or c SHARP) must be in the internet (solution host & domain) or there are better solutions for her.)If you have a solution for the web server on the microcontroller and are convinced that architecture will work, it seems that your question is how to write a client for data.
Some of the things you're talking about sounds like you want the web server on the microcontroller to respond to a fully functional GUI to any client. This may not be practical because of the computing power limited on the microcontroller and the difficulty of setting up and maintaining this type of server in a microcontroller environment.
A more common architecture that I've seen is just to serve the raw data and let the client user to interpret the data and display them as graphics, etc., this means that the user must Access the microcontroller of a computer running a client that you make.
You can use the communication/protocols/http client in labview palette or you can write a c# client that it is really a question of what data you need to acquire, and what language you are most comfortable in.
-
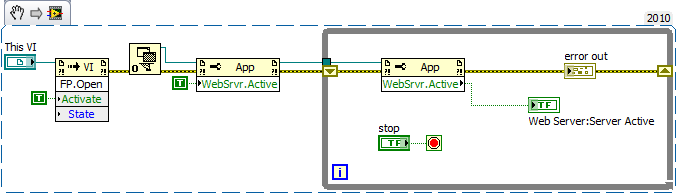
Cannot start web server on the executable file
Hello
We have a problem with a Web server - we cannot get to initialize the help of nodes of property or the ini on a compiled executable file.
As part of our application, we are starting the Web server to publish a status page to be read remotely. This works very well when we are running in the development environment and also when we run an executable a PC with installed development environment, however it will not boot on a PC with just the runtime installed.
I have attached some of the code that functionally does exactly the same thing in our main application. I used this as my Tester code and built in an exe while trying a lot of different things to fix.
When executing:
- The code will sit in the while loop until I press stop.
- Web server: Active Server = FALSE
- Out error = ERROR No.
In the full application the while loop waits a few seconds before throw an error if the server is not started. In this example, I can let the loop running for awhile without leave. Normally, the boot time is<50ms when="">
It's the ini file to the executable file:
[WebTest]
server.app.propertiesEnabled = True
Server.OLE.Enabled = True
server.tcp.serviceName = "My Server computer/VI"
server.vi.propertiesEnabled = True
WebServer.Enabled = True
WebServer.TcpAccess = "' + * '"
WebServer.ViAccess = "' + * '"
DebugServerEnabled = False
DebugServerWaitOnLaunch = FalseAnd it is the Web server configuration file:
ErrorLog "$LVSERVER_ROOT/logs/error.log".
LogLevel 3
The default server name
DocumentRoot "$LVSERVER_ROOT /... /.. '. "/ www".
Listen 8000
ThreadLimit 10
TypesConfig "$LVSERVER_ROOT/mime.types»
DirectoryIndex index.html
LoadModulePath "$LVSERVER_ROOT/modules '" $LVSERVER_ROOT/LVModules "" $LVSERVER_ROOT /... ".
LoadModule LVAuth lvauthmodule
LoadModule LVSnapshot lvsnapshotmodule
LoadModule LVRFP lvrfpmodule
LoadModule dir libdirModule
LoadModule copy libcopyModuleAddHandler LVAuthHandler
AddHandler LVSnapshotHandler .snap
AddHandler LVRFPHandlerAddHandler dirHandler
AddHandler copyHandler"CustomLog"$LVSERVER_ROOT/logs/access.log"'%%u %t \"%r\ hour' % > s %b.
KeepAlive on
KeepAliveTimeout 60
Timeout 60As can side note, anyone tell me where the $LVSERVER_ROOT variable is configured?
I tried the things:
- Copy a new default configuration file before the entry into force
- Writing a predefined file (encoded) before initializing config
- Definition to root before initializing directory (it actually generates an error because the server is not active...)
- Set WebServer.Active = TRUE several times inside the while loop
- Toggle the web server in the ini file
System:
- LabVIEW 2010
- PC with Windows 7 running
Thanks for any help, because it makes me crazy slow!
Ben
Hi Marco, thanks for the reply.
I have this guide was reviewed previously and had done all that he but a small section who gave me a hint of something to try and I have solved my problem, so thank you!
If anyone is interested, here's the problem:
The directive DocumentRoot folder in the config must exist or the Web server cannot be started. So basically, make sure that the file points to a folder that exists!
This leaves two small annoying problems if - you can't see if the file exists (and then create it) before starting the Web server, because you can not query the path to the folder without the Web server running.
AND
You can't really define the configuration programmatically file as parameters from the file are responsible for execution, not on the start Web server.
The result of this is that the config file and the folder root document should be created (and corresponding of course...) when the executable is built / installed on the system. Not a massive headache, but it means do not forget to put things in the build specification and do not rely on software to do the job at startup
-
start the Web server in different folders
I developed a compiled VI (Smarts - Net .exe) that has been designed to operate in a specific folder (\Smarts-Net) and activated the Server Web page of Smarts - Net .html in the same folder. So far so good.
The application receives data in real time produced another of our programs and generates graphs to show "what happens".
My clients would like run multiple instances of my program for their customers, but want to isolate their customer 'A' customer 'B' so that they cannot display the data on the other. I can start my application using different IP ports so that I can have multiple views, but I want to further isolate the data of the customer in different folders.
I did a 'manager' program that will create a subfolder of the folder in my main application (\Smarts-Net) so that it would appear as "\Smarts-Net\JobA" and copy all the files in the main folder in the new subfolder. I then change the of Smarts - Net .ini file with the new pathname of the file and the new port like this number:
[Smarts-Net]
server.app.propertiesEnabled = True
Server.OLE.Enabled = True
Server.TCP.servic = "My Server computer/VI"
server.vi.propertiesEnabled = True
WebServer.DirectoryIndex = "index.htm"
WebServer.LogEnabled = True
WebServer.LogPath=C:\Smarts-Net\Logs\Smarts-Net.log
WebServer.MimeTypes = (a LOT of Mime types in here... I left aside for this post)
WebServer.Port = 9501
WebServer.Enabled = True
WebServer.RootPath=C:\Smarts-Net\JobA
WebServer.TcpAccess = "" + c * ' "
WebServer.ViAccess = "' + * '"
DebugServerEnabled = False
DebugServerWaitOnLaunch = FalseAfter you change the .ini file, I start the application (Smarts - Net .exe) to the new folder.
This is where I need help. If I try to display the VI from another computer using an address like http://snape:9600/JobA/Smarts-Net.html, I get an "HTTP 404 - File not found" error. But, if I try to http://snape:9600 / Smarts - Net .html, I get the VI Panel!
Thus, it seems that I can change the Port in the .ini file, but not the RootPath. Does anyone know how to get the html to load from a different folder from the one specified when I created the application code?
Hello Steve,.
From your description it looks that the web server is already doing what you say you need for.
There is a difference between the URL path, the path that is entered in the browser and the path of file system, the location of the file on the disk.
The WebServer.RootPath token specifies the directory of the file system that corresponds to the root directory, "/", in the URL. You have specified C:\Smarts-Net\JobA as root your path so all files in this directory will be the URL of the http://mycomputer:myport / myFile. If you want the URL of http://mycomputer:myport/Logan/myFile then you need to have your root C:\Smarts-Net\ directory.
Does make sense?
Nathan
-
asa5512 V8.6 nat web server cannot access
Hi all
asa5512 V8.6 nat web server cannot access.
my home pc can access www.cisco.com, but external client cannot access my web server inside...
all of my config, I do not know what is wrong.
Thank youe help.
ciscoasa #.
See the ciscoasa # running
ciscoasa # show running-config
: Saved
:
ASA 1.0000 Version 2
!
ciscoasa hostname
activate 2KFQnbNIdI.2KYOU encrypted password
2KFQnbNIdI.2KYOU encrypted passwd
names of
!
interface GigabitEthernet0/0
nameif outside
security-level 0
address IP XXX1 255.255.255.240
!
interface GigabitEthernet0/1
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/2
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/3
Description link to 3560 G0/1
Speed 1000
full duplex
nameif inside
security-level 100
192.168.1.13 IP address 255.255.255.0
!
interface GigabitEthernet0/4
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/5
Shutdown
No nameif
no level of security
no ip address
!
interface Management0/0
nameif management
security-level 100
IP 192.168.100.1 address 255.255.255.0
!
!
time-range k3used
absolute starting 08:00 January 1, 2008
daily periodical 0:00 to 23:59
periodical daily 09:00-18:00
!
passive FTP mode
clock timezone BeiJing 8
network object obj - 192.168.1.0
subnet 192.168.1.0 255.255.255.0
network object obj - 192.168.200.0
192.168.200.0 subnet 255.255.255.0
network object obj - 192.168.1.2
host 192.168.1.2
network object obj - 192.168.1.2 - 01
host 192.168.1.2
network object obj - 192.168.1.19
Home 192.168.1.19
network object obj - 192.168.1.20
host 192.168.1.20
network object obj - 192.168.1.88
Home 192.168.1.88
network object obj - 192.168.1.1
host 192.168.1.1
network object obj - 192.168.1.2 - 02
host 192.168.1.2
network object obj - 192.168.1.6
host 192.168.1.6
object obj - X.X.X.3 network
Home X.X.X.3
object obj-tcp-source-eq-25 service
tcp source eq smtp service
obj-tcp-source-eq-110 service object
tcp source eq Microsoft pop3 service
object obj - X.X.X.10 network
Home X.X.X.10
obj-tcp-source-eq-8086 service object
tcp source eq 8086 service
obj-tcp-source-eq-80 service object
tcp source eq www service
network object obj - 192.168.1.1 - 01
host 192.168.1.1
obj-tcp-source-eq-3389 service object
source eq 3389 tcp service
obj-tcp-source-eq-9877 service object
tcp source eq 9877 service
obj-tcp-source-eq-21 service object
tcp source eq ftp service
object obj-tcp-source-eq-20 service
tcp source eq ftp service - data
network object obj - 192.168.2.88
Home 192.168.2.88
network object obj - 192.168.2.88 - 01
Home 192.168.2.88
network object obj - 192.168.2.88 - 02
Home 192.168.2.88
network object obj - 192.168.1.19 - 01
Home 192.168.1.19
network object obj - 192.168.2.2
host 192.168.2.2
network object obj - 192.168.2.2 - 01
host 192.168.2.2
network object obj - 192.168.2.2 - 02
host 192.168.2.2
network object obj - 192.168.3.2
host 192.168.3.2
network object obj - 192.168.3.2 - 01
host 192.168.3.2
network object obj - 192.168.3.2 - 02
host 192.168.3.2
object obj - X.X.X.9 network
Home X.X.X.9
obj-tcp-source-eq-8087 service object
tcp source eq 8087 service
network object obj - 192.168.1.200
host 192.168.1.200
network object obj - 192.168.1.200 - 01
host 192.168.1.200
network object obj - 192.168.1.30
host 192.168.1.30
network object obj - 192.168.1.30 - 01
host 192.168.1.30
network object obj - 192.168.1.1 - 02
host 192.168.1.1
object obj - X.X.X.6 network
Home X.X.X.6
obj-tcp-source-eq-8088 service object
tcp source eq 8088 service
network object obj - 192.168.3.5
Home 192.168.3.5
network object obj - 192.168.3.5 - 01
Home 192.168.3.5
network object obj - 192.168.3.5 - 02
Home 192.168.3.5
network object obj - 192.168.3.5 - 03
Home 192.168.3.5
network object obj - 192.168.3.5 - 04
Home 192.168.3.5
network object obj - 192.168.2.0
Subnet 192.168.2.0 255.255.255.0
network object obj - 192.168.3.0
subnet 192.168.3.0 255.255.255.0
network object obj - 192.168.4.0
subnet 192.168.4.0 255.255.255.0
network object obj - 192.168.5.0
192.168.5.0 subnet 255.255.255.0
network object obj - 192.168.6.0
192.168.6.0 subnet 255.255.255.0
network object obj - 192.168.7.0
192.168.7.0 subnet 255.255.255.0
network object obj - 192.168.8.0
192.168.8.0 subnet 255.255.255.0
vpn_list to access ip 192.168.1.0 scope list allow 255.255.255.0 192.168.200.0 255.255.255.0
vpn_list to access extended list ip 192.168.200.0 allow 255.255.255.0 192.168.1.0 255.255.255.0
access-list 101 extended deny ip any host 58.215.78.113
access-list 101 extended deny ip any host 61.139.126.81
access-list 101 extended deny ip any host 61.152.94.154
access-list 101 extended allow host ip 192.168.4.2 all
access-list 101 extended allow host ip 192.168.4.3 all
access-list 101 extended allow host ip 192.168.4.4 all
access-list 101 extended allow host ip 192.168.4.5 all
access-list 101 extended allow host ip 192.168.4.7 everything
access-list 101 extended permit ip host 192.168.4.8 all
access-list 101 extended permit ip host 192.168.4.9 all
access-list 101 extended permit ip host 192.168.4.10 all
access-list 101 extended allow host ip 192.168.4.11 all
access-list 101 extended allow host ip 192.168.4.12 all
access-list 101 extended allow host ip 192.168.4.13 all
access-list 101 extended allow host ip 192.168.4.14 all
access-list 101 extended allow host ip 192.168.4.15 all
access-list 101 extended allow host ip 192.168.4.16 all
access-list 101 extended allow host 192.168.4.18 ip everything
access-list 101 extended allow host ip 192.168.4.19 all
access-list 101 extended allow host ip 192.168.4.20 all
access-list 101 extended allow host ip 192.168.4.180 all
access-list 101 extended deny ip 192.168.4.0 255.255.255.0 any
access-list 101 extended allow host ip 192.168.2.176 all
access-list 101 extended allow icmp a whole
access-list 101 extended allow host ip 192.168.2.3 everything
access-list 101 extended allow host ip 192.168.2.164 all
access-list 101 extended allow host ip 192.168.2.171 all
access-list 101 extended allow host ip 192.168.2.142 all
access-list 101 extended allow host ip 192.168.2.180 all
access-list 101 extended allow host ip 192.168.2.149 all
access-list 101 extended allow host ip 192.168.2.201 all
access-list 101 extended allow host ip 192.168.2.170 all
access-list 101 extended allow host ip 192.168.2.168 all
access-list 101 extended allow host ip 192.168.2.103 everything
access-list 101 extended allow host ip 192.168.2.34 all
access-list 101 extended allow host ip 192.168.2.174 all
access-list 101 extended allow host ip 192.168.2.199 all
access-list 101 extended allow host ip 192.168.2.253 everything
access-list 101 extended allow host ip 192.168.2.236 all
access-list 101 extended allow host ip 192.168.2.214 all
access-list 101 extended allow host ip 192.168.2.110 everything
access-list 101 extended allow host ip 192.168.2.127 all
access-list 101 extended allow host ip 192.168.2.178 all
access-list 101 extended allow host ip 192.168.2.21 all
access-list 101 extended allow host ip 192.168.2.24 all
access-list 101 extended allow host ip 192.168.2.251 all
access-list 101 extended allow host ip 192.168.2.33 all
access-list 101 extended allow host ip 192.168.2.120 all
access-list 101 extended allow host ip 192.168.2.85 all
access-list 101 extended allow host ip 192.168.2.137 all
access-list 101 extended allow host ip 192.168.2.113 all
access-list 101 extended allow ip 192.168.2.20 host everything
access-list 101 extended allow host ip 192.168.2.101 everything
access-list 101 extended allow host ip 192.168.2.106 all
access-list 101 extended allow host ip 192.168.2.140 all
access-list 101 extended allow host ip 192.168.2.215 all
access-list 101 extended allow host ip 192.168.2.107 all
access-list 101 extended allow host ip 192.168.2.234 all
access-list 101 extended allow host ip 192.168.2.15 all
access-list 101 extended allow host ip 192.168.2.55 all
access-list 101 extended allow host ip 192.168.2.41 all
access-list 101 extended permit ip host 192.168.2.13 all
access-list 101 extended allow host ip 192.168.2.133 everything
access-list 101 extended allow host ip 192.168.2.73 all
access-list 101 extended allow host ip 192.168.2.172 all
access-list 101 extended allow host ip 192.168.2.175 all
access-list 101 extended allow host ip 192.168.2.88 all
access-list 101 extended allow host ip 192.168.2.188 all
access-list 101 extended allow host ip 192.168.2.136 all
access-list 101 extended allow host ip 192.168.2.74 all
access-list 101 extended allow host ip 192.168.2.12 everything
access-list 101 extended allow host ip 192.168.2.100 everything
access-list 101 extended allow host ip of 192.168.2.102 everything
access-list 101 extended allow host ip 192.168.2.152 all
access-list 101 extended allow ip 192.168.2.4 host everything
access-list 101 extended allow host ip 192.168.2.5 everything
access-list 101 extended allow host ip 192.168.2.6 everything
access-list 101 extended allow host ip 192.168.2.14 all
access-list 101 extended allow host ip 192.168.2.19 all
access-list 101 extended permit ip host 192.168.2.16 all
access-list 101 extended allow host ip 192.168.2.17 all
access-list 101 extended allow host ip 192.168.2.18 all
access-list 101 extended allow host ip 192.168.2.22 all
access-list 101 extended allow host ip 192.168.2.23 all
access-list 101 extended allow host ip 192.168.2.115 all
access-list 101 extended allow host ip 192.168.2.116 all
access-list 101 extended allow host ip 192.168.2.117 all
access-list 101 extended allow host ip 192.168.2.118 all
access-list 101 extended allow host ip 192.168.2.119 all
access-list 101 extended allow host ip 192.168.2.150 all
access-list 101 extended allow host ip 192.168.2.128 all
access-list 101 extended deny ip 192.168.2.0 255.255.255.0 any
access-list 101 extended allow ip 192.168.3.2 host everything
access-list 101 extended allow host ip 192.168.3.3 everything
access-list 101 extended permit ip host 192.168.3.4 everything
access-list 101 extended allow host ip 192.168.3.5 all
access-list 101 extended allow host ip 192.168.3.6 all
access-list 101 extended allow host ip 192.168.3.7 all
access-list 101 extended allow host ip 192.168.3.8 all
access-list 101 extended allow host ip 192.168.3.9 all
access-list 101 extended allow host ip 192.168.3.10 everything
access-list 101 extended allow host ip 192.168.3.11 all
access-list 101 extended allow host ip 192.168.3.12 all
access-list 101 extended allow host ip 192.168.3.13 all
access-list 101 extended allow host ip 192.168.3.14 all
access-list 101 extended allow host ip 192.168.3.15 everything
access-list 101 extended allow host ip 192.168.3.16 all
access-list 101 extended allow host ip 192.168.3.17 everything
access-list 101 extended allow host ip 192.168.3.18 all
access-list 101 extended allow host ip 192.168.3.19 all
access-list 101 extended allow host ip 192.168.3.20 everything
access-list 101 extended permit ip host 192.168.3.21 all
access-list 101 extended allow host ip 192.168.3.22 all
access-list 101 extended allow host ip 192.168.3.23 all
access-list 101 extended allow host ip 192.168.3.24 everything
access-list 101 extended allow host ip 192.168.3.25 all
access-list 101 extended allow host ip 192.168.3.26 all
access-list 101 extended allow host ip 192.168.3.27 all
access-list 101 extended allow host ip 192.168.3.28 all
access-list 101 extended allow host ip 192.168.3.29 all
access-list 101 extended allow host ip 192.168.3.30 all
access-list 101 extended allow host ip 192.168.3.31 all
access-list 101 extended allow host ip 192.168.3.32 all
access-list 101 extended allow host ip 192.168.3.33 all
access-list 101 extended allow host ip 192.168.3.34 all
access-list 101 extended allow host ip 192.168.3.35 all
access-list 101 extended allow host ip 192.168.3.36 all
access-list 101 extended allow host ip 192.168.3.37 all
access-list 101 extended allow host ip 192.168.3.38 all
access-list 101 extended allow host ip 192.168.3.39 all
access-list 101 extended allow host ip 192.168.3.40 all
access-list 101 extended allow host ip 192.168.3.41 all
access-list 101 extended allow host ip 192.168.3.42 all
access-list 101 extended allow host ip 192.168.3.43 all
access-list 101 extended allow host ip 192.168.3.86 all
access-list 101 extended allow host ip 192.168.3.88 all
access-list 101 extended allow host ip 192.168.3.89 all
access-list 101 extended allow host ip 192.168.3.56 all
access-list 101 extended allow host ip 192.168.3.55 all
access-list 101 extended allow host ip 192.168.3.96 all
access-list 101 extended allow host ip 192.168.3.97 all
access-list 101 extended allow host ip 192.168.3.98 all
access-list 101 extended allow host ip 192.168.3.116 all
access-list 101 extended allow host ip 192.168.3.111 all
access-list 101 extended allow host ip 192.168.3.175 all
access-list 101 extended allow host ip 192.168.3.176 all
access-list 101 extended allow host ip 192.168.3.201 all
access-list 101 extended allow host ip 192.168.3.202 all
access-list 101 extended allow host ip 192.168.3.203 all
access-list 101 extended allow host ip 192.168.3.204 all
access-list 101 extended allow host ip 192.168.3.205 all
access-list 101 extended allow host ip 192.168.3.206 all
access-list 101 extended allow host ip 192.168.3.207 all
access-list 101 extended allow host ip 192.168.3.208 all
access-list 101 extended allow host ip 192.168.3.209 all
access-list 101 extended allow host ip 192.168.3.210 all
access-list 101 extended allow host ip 192.168.3.213 all
access-list 101 extended allow host ip 192.168.3.214 all
access-list 101 extended allow host ip 192.168.3.215 all
access-list 101 extended allow host ip 192.168.3.101 all
access-list 101 extended allow host ip 192.168.3.102 all
access-list 101 extended allow host ip 192.168.3.103 all
access-list 101 extended allow host ip 192.168.3.106 all
access-list 101 extended allow host ip 192.168.3.107 all
access-list 101 extended allow host ip 192.168.3.152 all
access-list 101 extended allow host ip 192.168.3.151 all
access-list 101 extended allow host ip 192.168.3.153 all
access-list 101 extended allow host ip 192.168.3.195 all
access-list 101 extended allow host ip 192.168.3.45 all
access-list 101 extended allow host ip 192.168.3.46 all
access-list 101 extended allow host ip 192.168.3.199 all
access-list 101 extended allow host ip 192.168.3.157 all
access-list 101 extended refuse 192.168.3.0 ip 255.255.255.0 any
access-list 101 extended allow tcp a whole
access list 101 scope ip allow a whole
vpnclient_splitTunnelAcl list standard access allowed 192.168.1.0 255.255.255.0
2 extended access-list permit ip 192.168.2.0 255.255.255.0 any
3 extended access-list allow ip 192.168.3.0 255.255.255.0 any
4 extended access-list allow ip 192.168.4.0 255.255.255.0 any
access-list extended 500 k permit ip host XXX1 everything
access-list extended 500 k allow icmp host XXX1 everything
access-list 102 extended allow host ip 192.168.1.6 everything
access-list extended 100 permit tcp any host 192.168.1.1 eq www
access-list extended 100 permit tcp any host 192.168.1.1 eq 8080
access-list extended 100 permit tcp any host X.X.X.4
access-list extended 100 permit ip any host X.X.X.4
access-list extended 100 permit icmp any host X.X.X.4
access-list extended 100 permit tcp any host 192.168.1.6 eq smtp
access-list extended 100 permit tcp any host 192.168.1.6 eq pop3
access-list extended 100 permit tcp any host 192.168.1.6 eq www
access-list extended 100 permit tcp any host 192.168.1.6
access-list 100 scope ip allow any host 192.168.1.6
access-list extended 100 permit icmp any host 192.168.1.6
access-list extended 100 permit tcp any host 192.168.1.19 eq 3389
access-list extended 100 permit tcp any host 192.168.1.20 eq 3389
access-list extended 100 permit tcp any host 192.168.1.88 eq 3389
access-list extended 100 permit tcp any host X.X.X.12
access-list extended 100 permit ip any host X.X.X.12
access-list extended 100 permit icmp any host X.X.X.12
access-list extended 100 permit tcp any host 192.168.1.6 eq 8086
access-list extended 100 permit tcp any host 192.168.1.1 eq 3389
access-list extended 100 permit tcp any host 192.168.1.6 eq 3389
access-list extended 100 permit tcp any host 192.168.1.6 eq ftp
access-list extended 100 permit tcp any host 192.168.1.6 eq ftp - data
access-list extended 100 permit tcp any host 192.168.2.88 eq 3389
access-list extended 100 permit tcp any host 192.168.2.88 eq 12172
access-list extended 100 permit tcp any host 192.168.2.2 eq 3389
access-list extended 100 permit tcp any host 192.168.2.2 eq 9116
access-list extended 100 permit tcp any host 192.168.3.2 eq 25243
access-list extended 100 permit tcp any host 192.168.3.2 eq 3389
access-list extended 100 permit tcp any host 192.168.1.200 eq www
access-list extended 100 permit tcp any host 192.168.1.200 eq 12001
access-list extended 100 permit tcp any host 192.168.1.30 eq 3389
access-list extended 100 permit tcp any host 192.168.3.5 eq 4160
access-list extended 100 permit tcp any host 192.168.3.5 eq 11111
access-list extended 100 permit tcp any host 192.168.3.5 eq 3389
access-list extended 100 permit tcp any host X.X.X.10
access-list extended 100 permit udp any host 192.168.2.88 eq 12172
access-list extended 100 permit udp any host 192.168.2.2 eq 9116
access-list extended 100 permit udp any host 192.168.3.2 eq 25243
access-list extended 100 permit udp any host 192.168.3.5 eq 4170
access-list extended 100 permit udp any host 192.168.3.5 eq 11111
access-list extended 100 permit ip any host X.X.X.10
access-list extended 100 permit tcp any host 192.168.1.6 eq 8087
access-list extended 100 permit tcp any host X.X.X.9
access-list extended 100 permit ip any host X.X.X.9
access-list extended 100 permit tcp any host 192.168.1.30 eq www
access-list extended 100 permit tcp any host X.X.X.5
access-list extended 100 permit ip any host X.X.X.5
access-list extended 100 permit icmp a whole
access-list extended 100 permit tcp any host 192.168.1.6 eq 8088
access-list extended 100 permit ip any host X.X.X.6
access-list extended 100 permit tcp any host X.X.X.6
access list extended 100 permit tcp host 61.186.169.129 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.129 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.129 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.129 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.129 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.186.169.130 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.130 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.130 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.130 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.130 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.186.169.131 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.131 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.131 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.131 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.131 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.186.169.132 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.132 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.132 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.132 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.132 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.186.169.133 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.186.169.133 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.186.169.133 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.186.169.133 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.186.169.133 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.129 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.130 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.131 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.132 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.186.169.133 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.129 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.130 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.131 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.132 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.186.169.133 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 183.64.106.194 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 183.64.106.194 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 183.64.106.194 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 183.64.106.194 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 183.64.106.194 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 183.64.106.194 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 183.64.106.194 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 183.64.106.195 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 183.64.106.195 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 183.64.106.195 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 183.64.106.195 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 183.64.106.195 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 183.64.106.195 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 183.64.106.195 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 14.107.162.32 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 14.107.162.32 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 14.107.162.32 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 14.107.162.32 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 14.107.162.32 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 14.107.162.32 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 14.107.162.32 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 14.107.247.121 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 14.107.247.121 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 14.107.247.121 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 14.107.247.121 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 14.107.247.121 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 14.107.247.121 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 14.107.247.121 X.X.X.2 time-range k3used
access list extended 100 permit tcp host 61.128.208.106 host 192.168.1.2 eq 5872 times-range k3used
access list extended 100 permit tcp host 61.128.208.106 host 192.168.1.2 eq 8088 times-range k3used
access list extended 100 permit tcp host 61.128.208.106 host 192.168.1.2 eq 3389 times-range k3used
allowed extended access list 100 tcp host 61.128.208.106 host 192.168.1.19 eq www time-range k3used
access-list extended 100 permit tcp host 61.128.208.106 X.X.X.2 time-range k3used
access-list extended 100 permit ip host 61.128.208.106 X.X.X.2 time-range k3used
access-list extended 100 permit icmp host 61.128.208.106 X.X.X.2 time-range k3used
access-list 100 extended tcp refuse any host 192.168.1.2 eq 5872
access-list 100 extended tcp refuse any host 192.168.1.2 eq 8088
access-list 100 extended tcp refuse any host 192.168.1.2 eq 3389
access-list 100 extended tcp refuse any host 192.168.1.19 eq www
access-list 100 extended tcp refuse any host X.X.X.2
access-list extended 100 deny ip any host X.X.X.2
access-list extended 100 refuse icmp any host X.X.X.2
pager lines 24
Outside 1500 MTU
Within 1500 MTU
management of MTU 1500
IP local pool 192.168.200.1 - 192.168.200.20 mask 255.255.255.0 vpn_pool
ICMP unreachable rate-limit 1 burst-size 1
don't allow no asdm history
ARP timeout 14400
NAT (inside, all) source static obj - obj - 192.168.1.0 destination 192.168.1.0 static obj - 192.168.200.0 obj - 192.168.200.0 non-proxy-arp
NAT (inside, all) source static obj - 192.168.200.0 obj - 192.168.200.0 destination static obj - 192.168.1.0 obj - 192.168.1.0 non-proxy-arp
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.3 service obj-tcp-source-eq-25 obj-tcp-source-eq-25
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.3 service obj-tcp-source-eq-110 obj-tcp-source-eq-110
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.10 service obj-tcp-source-eq-8086 obj-tcp-source-eq-80
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.10 service obj-tcp-source-eq-3389 obj-tcp-source-eq-9877
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.10 service obj-tcp-source-eq-21 obj-tcp-source-eq-21
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.10 service obj-tcp-source-eq-20 obj-tcp-source-eq-20
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.9 service obj-tcp-source-eq-8087 obj-tcp-source-eq-80
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.6 service obj-tcp-source-eq-8088 obj-tcp-source-eq-80
NAT (inside, outside) source static obj - 192.168.1.6 obj - X.X.X.3 service obj-tcp-source-eq-80 obj-tcp-source-eq-80
NAT (inside, outside) source dynamic obj - 192.168.1.6 obj - X.X.X.3
!
network object obj - 192.168.1.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.200.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.1.2
NAT (inside, outside) Static X.X.X.2 5872 5872 tcp service
network object obj - 192.168.1.2 - 01
NAT (inside, outside) Static X.X.X.2 8088 8088 tcp service
network object obj - 192.168.1.19
NAT (inside, outside) Static X.X.X.12 tcp 3389 8001 service
network object obj - 192.168.1.20
NAT (inside, outside) Static X.X.X.12 tcp 3389 8002 service
network object obj - 192.168.1.88
NAT (inside, outside) Static X.X.X.12 tcp 3389 12345 service
network object obj - 192.168.1.1
NAT (inside, outside) Static X.X.X.4 tcp www www service
network object obj - 192.168.1.2 - 02
NAT (inside, outside) Static X.X.X.2 service tcp 3389 8005
network object obj - 192.168.1.1 - 01
NAT (inside, outside) Static X.X.X.10 tcp 3389 9876 service
network object obj - 192.168.2.88
NAT (inside, outside) Static X.X.X.10 tcp 3389 3129 service
network object obj - 192.168.2.88 - 01
NAT (inside, outside) Static X.X.X.10 12172 12172 tcp service
network object obj - 192.168.2.88 - 02
NAT (inside, outside) Static X.X.X.10 service udp 12172 12172
network object obj - 192.168.1.19 - 01
NAT (inside, outside) Static X.X.X.2 service tcp www 8056
network object obj - 192.168.2.2
NAT (inside, outside) Static X.X.X.10 3389 3128 tcp service
network object obj - 192.168.2.2 - 01
NAT (inside, outside) Static X.X.X.10 9116 9116 tcp service
network object obj - 192.168.2.2 - 02
NAT (inside, outside) Static X.X.X.10 service udp 9116 9116
network object obj - 192.168.3.2
NAT (inside, outside) Static X.X.X.10 25243 25243 tcp service
network object obj - 192.168.3.2 - 01
NAT (inside, outside) Static X.X.X.10 service udp 25243 25243
network object obj - 192.168.3.2 - 02
NAT (inside, outside) Static X.X.X.10 tcp 3389 3130 service
network object obj - 192.168.1.200
NAT (inside, outside) Static X.X.X.10 service tcp www 1114
network object obj - 192.168.1.200 - 01
NAT (inside, outside) Static X.X.X.10 12001 12001 tcp service
network object obj - 192.168.1.30
NAT (inside, outside) Static X.X.X.5 tcp www www service
network object obj - 192.168.1.30 - 01
NAT (inside, outside) Static X.X.X.10 tcp 3389 9878 service
network object obj - 192.168.1.1 - 02
NAT (inside, outside) Static X.X.X.4 8080 8080 tcp service
network object obj - 192.168.3.5
NAT (inside, outside) Static X.X.X.10 4160 4160 tcp service
network object obj - 192.168.3.5 - 01
NAT (inside, outside) Static X.X.X.10 service udp 4170 4170
network object obj - 192.168.3.5 - 02
NAT (inside, outside) Static X.X.X.10 11111 11111 tcp service
network object obj - 192.168.3.5 - 03
NAT (inside, outside) Static X.X.X.10 tcp 3389 3127 service
network object obj - 192.168.3.5 - 04
NAT (inside, outside) Static X.X.X.10 11111 11111 udp service
network object obj - 192.168.2.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.3.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.4.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.5.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.6.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.7.0
NAT dynamic interface (indoor, outdoor)
network object obj - 192.168.8.0
NAT dynamic interface (indoor, outdoor)
Access-group 100 in external interface
Access-group 101 in the interface inside
Route outside 0.0.0.0 0.0.0.0 X.X.X.14 1
Route inside 192.168.2.0 255.255.255.0 192.168.1.12 1
Route inside 192.168.3.0 255.255.255.0 192.168.1.12 1
Route inside 192.168.4.0 255.255.255.0 192.168.1.12 1
Route inside 192.168.5.0 255.255.255.0 192.168.1.12 1
Route inside 192.168.6.0 255.255.255.0 192.168.1.12 1
Timeout xlate 03:00
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
identity of the user by default-domain LOCAL
Enable http server
No snmp server location
No snmp Server contact
Server enable SNMP traps snmp authentication linkup, linkdown warmstart of cold start
Crypto ipsec transform-set esp - esp-md5-hmac ikev1 vpn_set
Crypto-map dynamic vpn_map 10 set transform-set vpn_set ikev1
Crypto-map dynamic vpn_map 10 the value reverse-road
vpnmap 10 card crypto ipsec-isakmp dynamic vpn_map
vpnmap interface card crypto outside
Crypto ikev1 allow outside
IKEv1 crypto policy 1
preshared authentication
the Encryption
md5 hash
Group 2
life 86400
IKEv1 crypto policy 65535
preshared authentication
3des encryption
sha hash
Group 2
life 86400
Telnet 0.0.0.0 0.0.0.0 inside
Telnet 192.168.1.0 255.255.255.0 inside
Telnet timeout 5
SSH 0.0.0.0 0.0.0.0 outdoors
SSH timeout 30
SSH version 1
Console timeout 0
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
Server NTP 192.43.244.18
internal group vpnclient strategy
vpnclient group policy attributes
value of server DNS 61.128.128.68
Ikev1 VPN-tunnel-Protocol
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list vpnclient_splitTunnelAcl
cisco 3USUcOPFUiMCO4Jk encrypted password username
type tunnel-group vpn_group remote access
tunnel-group vpn_group General-attributes
address vpn_pool pool
Group Policy - by default-vpnclient
vpn_group group of tunnel ipsec-attributes
IKEv1 pre-shared-key *.
!
class-map 500 k
matches the access list 500 k
class-map inspection_default
match default-inspection-traffic
class-map 2
matches the access list 2
PAM-class 3
matches the access list 3
class-map 4
corresponds to the list of access-4
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
Review the ip options
inspect the netbios
inspect the rsh
inspect the rtsp
inspect the skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect the tftp
inspect the sip
inspect xdmcp
Policy-map 500 k
500 k class
Policy-map 2
class 2
class 3
class 4
!
global service-policy global_policy
context of prompt hostname
remote anonymous reporting call invites 2
call-home
Profile of CiscoTAC-1
no active account
http https://tools.cisco.com/its/service/oddce/services/DDCEService destination address
email address of destination [email protected] / * /
destination-mode http transport
Subscribe to alert-group diagnosis
Subscribe to alert-group environment
Subscribe to alert-Group 13 monthly periodic inventory
Subscribe to alert-group configuration periodic monthly 13
daily periodic subscribe to alert-group telemetry
Cryptochecksum:ecead54d7c85807eb47c7cdaf7d7e82a
: end
ciscoasa# $
ciscoasa #.
ciscoasa #.
Hello
You have changed the source IP address of the order I suggested?
There is no reason to use the 192.168.1.1 IP address as the source of this command "packet - trace" that the source will NEVER be this IP address, because it is a private IP not routable on the public Internet.
Then you can try with the order I suggested.
entry Packet-trace out tcp 1.1.1.1 12345 61.186.236.4 80
I guess that the above command / test failed because you were using the real server IP address as the IP source for the test.
-Jouni
-
Make the remote web server accessible via VPN Site to website
We have two test sites that are connected by a tunnel IPSEC VPN site-to-site (hosted on a SAA each site) over the Internet. We are trying to set up an environment to test two web applications running side by side. Two web servers are running on the Site of Test 1. We don't have the same public IP available at each site.
To address the public site 1 unique IP address restriction, we try to install ACL and NAT rules to have 2 Site accept traffic from the internet and send it on the site to the other tunnel. So 1 Web server would accept the ASA 1 internet traffic and Web Server 2 accept traffic from ASA 2 to the other site. Here's a network diagram:

We have difficulties to get this configuration works correctly. Please note that the network 192.168.3.0/24 clients are able to access the servers Web1 and Web2. This question seems to be due to our NAT configuration. This is the type of error, we see on the two firewalls:
Asymmetrical NAT rules matched for flows forward and backward; Connection for tcp src outside:4.4.4.4/443 dst outside:192.168.1.10/443 refused due to path failure reverse that of NAT
Our situation seems similar to this post: https://supportforums.cisco.com/thread/2242230
Any help would be appreciated.
Hello
What Karsten said above is true. While it is possible and works, it also means that the configuration is a little more complex to manage. I have done no such features in a real-life network environment and have always used additional public IP addresses on the local site when a server is hosted.
If you want to continue to move forward with this so here's a few points to consider and the configurations that you need.
First off it seems to me that the other server will be organized by the local Site 1 so a simple static PAT (Port Forward) must manage the Site 1.
network of the WEB-HTTP object
host 192.168.1.10
NAT (inside, outside) interface static tcp 443 443 service
And if you need TCP/80 also then you will need
network of the HTTPS WEB object
host 192.168.1.10
NAT (inside, outside) interface static service tcp 80 80
Now, 2 Site will naturally a little different that the server is hosted on the Site 1 and Site 2 is the public IP address used to publish the server on the external network.
Essentially, you will need to configure NAT that both makes dynamic PAT for the addresses of the source of the connection to your server Web 2, but also makes the static PAT (Port Forward) for the IP address of the Web Server 2. Additionally, you have to set the area of encryption on the Site 1 and Site 2 to match this new addition to the L2L VPN connection.
Unless of course you use an existing IP address on the field of encryption in the dynamic translation of PAT for the source address. In this case, it would take no change VPN L2L. I'll use that in the example below.
The NAT configuration might look like this
service object WWW
destination eq 80 tcp service
service object HTTPS
destination eq 443 tcp service
the object SOURCE-PAT-IP network
host 192.168.3.254
network of the WEB-SERVER-2-SITE1 object
host 192.168.1.11
NAT (outside, outside) 1 dynamic source no matter what static SOURCE-PAT-IP destination interface WEB-SERVER-2-SITE1 service WWW WWW
NAT (outdoors, outdoor), 2 dynamic source no matter what static SOURCE-PAT-IP destination interface WEB-SERVER-2-SITE1 service HTTPS HTTPS
So, essentially, NAT configurations above should ake 'all' traffic coming from behind 'outside' interface intended to "outside" "interface" IP address and translate the source to ' SOURCE-PAT-IP ' address and untranslate destination to "WEB-SERVER-2-SITE1".
Make sure that the IP address chosen (in this case 192.168.3.254) is not used on any device. If she is then replace it with something that is not currently used in the network. Otherwise, configure an IP address of some other subnet and include in the L2L VPN configurations on both sites.
Unless you already have it, you also have this configuration command to activate the traffic to make a U-turn/pin on the ' outside ' of the Site 2 ASA interface
permit same-security-traffic intra-interface
Hope this helps
Remember to mark a reply as the answer if it answered your question.
Feel free to ask more if necessary.
-Jouni
Maybe you are looking for
-
How to display only icons on the personal bar?
In the bookmarks toolbar, I have a lot of Favorites and do not want to see titles unless I hover over the icon.Is this possible?I saw a suite called = add (Smart bookmarks Menu"but he said he was abandoned and not put to update to the latest version
-
How to create the default recovery disc factory with OneKey Recovery 4.0
I have a K430 and before I use it (as with any machine, I bought) I wanted to make my recovery disks. Throughout this site there are guides to do this with version 7, but this desktop computer has version 4.0 of OKR I can record an image of my partit
-
DEXT with MOTOblur - provider Telefonica When I configured my DEXT for the first time I imported contacts from the SIM card by mistake. the contact list created by MOTOblur now connects the contacts of my company Exchange Server with Google, Facebook
-
LabVIEW compatible capture card
Hello A few weeks ago, I ordered a PCI 4 x 4 of the German company Phytec acquisition card. When they were not yet convinced me to buy the thing, they told me how this card works with LabVIEW and that there are many example of screw when I tried to u
-
Windows Installer is no longer on my computer... How can I reinstall it?
I can't follow the suggestions to reinstall Windows Installer , because it no longer appears in my '' programs. '' How can I reinstall Windows Installer without this program? I followed several methods of Microsoft, but my computer cannot continue