Private communication private VPN tunnel IP IP
I need plant communication between my local LAN segment and a segment of remote local network using private IP addresses. We currently have a VPN tunnel between two sites and we currently have NAT our private to a public IP traffic and send that to another public NAT at the remote site. I am unable to see traffic from the remote site via private IP and when I use packet tracer in the ASDM, the package is abandoned to the first statement "VPN". All I have to do different since I use a statement exempt from NAT?

Daniel,
You have changed your crypto ACL so that they understand as well private LAN?
At the moment, they are probably configured to use IP addresses public but what about the private sector?
If please check this and let us know what you find.
Thank you.
Raga
Tags: Cisco Security
Similar Questions
-
VPN Tunnel problem. external interface has private IP
Hi all
I don't know if it is wired or not!
When our ISP provide us an Internet connection our real IP is configured on the ethernet interface, while the serial interfaces have a private IP address.
The problem here is when I'm trying to configure a VPN tunnel to another router.
Anything in the configuration is smooth, except for the part where I put the serial interface is my outside.
The tunnel is still low coz the IP address will be my private (serial interface) during the configuration on the router counterpart is my public IP address.
So I am woundering is there a way I can force the VPN tunnel to take the IP address configured on the side LAN? Or any other work around?
Building configuration...
Current configuration: 2372 bytes
!
version 12.4
horodateurs service debug datetime msec
Log service timestamps datetime msec
no password encryption service
!
boot-start-marker
start the flash c1841-advsecurityk9 - mz.124 - 23.bin system
boot-end-marker
!
property intellectual auth-proxy max-nodata-& 3
property intellectual admission max-nodata-& 3
!
crypto ISAKMP policy 1
BA 3des
preshared authentication
Group 2
!
crypto ISAKMP policy 2
BA 3des
md5 hash
preshared authentication
Group 2
isakmp encryption key * address 144.254.x.y
!
!
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
!
map SDM_CMAP_1 1 ipsec-isakmp crypto
Description Tunnel to144.254.x.y
the value of 144.254.x.y peer
game of transformation-ESP-3DES-SHA
match address VPN_Traffic
!
!
!
interface FastEthernet0/0
address IP 10.55.218.1 255.255.255.0 secondary (My internal subnet)
IP address 196.219.a.b 255.255.255.224 (my public IP)
IP nat inside
IP virtual-reassembly
automatic duplex
automatic speed
No keepalive
!
interface FastEthernet0/1
no ip address
automatic duplex
automatic speed
!
interface Serial0/0/0
no ip address
frame relay IETF encapsulation
frame-relay lmi-type q933a
!
point-to-point interface Serial0/0/0.16
IP 172.16.133.2 255.255.255.252
NAT outside IP
IP virtual-reassembly
SNMP trap-the link status
dlci 16 frame relay interface
map SDM_CMAP_1 crypto
!
interface Serial0/0/1
no ip address
frame relay IETF encapsulation
ignore the dcd
frame-relay lmi-type q933a
!
point-to-point interface Serial0/0/1.16
IP 172.16.134.2 255.255.255.252
NAT outside IP
IP virtual-reassembly
SNMP trap-the link status
dlci 16 frame relay interface
map SDM_CMAP_1 crypto
!
IP forward-Protocol ND
IP route 0.0.0.0 0.0.0.0 Serial0/0/1.16
IP route 0.0.0.0 0.0.0.0 Serial0/0/0.16
!
VPN_Traffic extended IP access list
Note Protect traffic Local to any Destination subnet
Remark SDM_ACL = 4 category
IP 10.55.218.0 allow 0.0.0.255 any
!
Scheduler allocate 20000 1000
end
This should do the trick.
map SDM_CMAP_1 crypto local-address FastEthernet0/0
See you soon
-
Authentication of ACS in the VPN tunnel
We want to enable the ACS authentication to connect to different routers (Cisco 881 s) we have obtained who are communicating with our WAN via VPN tunnels. We want to avoid using public IP of the router to communicate and pass information to user/password with the ACS server and rely on the IP of the server private instead. The problem is that external interfaces of the router connect to the Internet using public IP addresses and when the router wishes to communicate with the ACS server it will use its IP of the interface to the public and which will fail. We can ping on the server of course when we set the source to the internal LAN IP.
The question is are there any way to have the router contact ACS through the VPN tunnel using a private IP address?
config is used and tested with success on local equipment:
AAA new-model
RADIUS-server host 10.x.x.x single-connection key xxxxxx
AAA authentication login Ganymede-local group local Ganymede
AAA authorization commands x Ganymede-local group Ganymede + if authenticated
AAA authorization exec Ganymede-local group Ganymede + authenticated if
See the establishment of privileges exec level x
line vty 0 4
Ganymede-local authentication login
authorization controls Ganymede-local x
-ACS ping to the router (WAN via VPN connection) when using public IP address of the router as the source address:
RT881 #ping 10.x.x.x
Type to abort escape sequence.
Send 5, echoes ICMP 100 bytes to 10.x.x.x, time-out is 2 seconds:
.....
Success rate is 0% (0/5)
-ACS ping to the router (WAN via VPN connection) when using IP private of the LAN as source address:
RT881 #ping source 10.x.x.1 10.x.x.x
Type to abort escape sequence.
Send 5, echoes ICMP 100 bytes to 10.x.x.x, time-out is 2 seconds:
Packet sent with a source address of 10.x.x.1
!!!!!
Success rate is 100 per cent (5/5), round-trip min/avg/max = 72/72/76 ms
Looking forward to your responses and suggestions.
Thanks, M.
Hey Maher,
You can use the command 'Ganymede-source interface ip' or 'RADIUS source-interface ip' for your scenario.
I hope this helps!
Kind regards
Assia
-
VPN connected, stream out of VPN tunnel
I mean that we have in place of the VPN Sites manage to sites with 2 RV042 router but it seams not as I wanted. Are you sure that each transfer of data through Router 2 will go into the VPN tunnel or it shuts down the VPN tunnel. I checked the routing table and saw that:
Sources mask Gateway Interface
2 1 or wan wan IP 255.255.255.0 ipsec0 private
By default 0.0.0.0 (ip wan 1 or 2) wan1 or wan2
.........
So what you think what sense data will pass through the line, it will go through the ipsec section or through wan1 or wan2. Ofcouse each data will pass through wan1 or wan2, but it can go inside the ipsec tunnel or ipsec outside tunnel. If she goes inside the ipsec tunnel, everything is ok, but if this isn't the case, transfer of unsecured data. I'm trying to access some website is not in private ip and it was outside ipsec tunnel go, I can capture and now that you have access.
Why with linksys have 2 work as draytek product even photos follow:
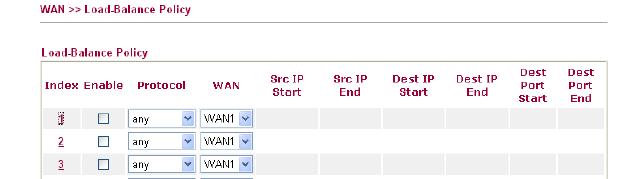
Can someone help me to answer this question, thank you for your attention
1. it depends on what the tunnels of your business allows. As I've written before, there are other protocols that allows you to route traffic through the VPN tunnel. Only IPSec cannot do this. For example, if your company uses GRE over IPSec then they can route traffic through their tunnels. Your RV does not support this.
2. If it's really plain IPSec then you cannot configure several subnets. You can try to implement the security group remote as a subnet more grand, such as 10.0.0.0/8. Of course the groups must match on both sides.
3. If you want to route all traffic through the tunnel, and then try to set the local/remote security to 0.0.0.0/0.0.0.0 group. Maybe it works.
The configuration of IPSec in the RV042 does not allow extremely complex configurations. It's mainly to connect two subnets between them.
-
I have read on several posts on the topic and still think I'm missing something, I'm looking for help.
Basically, I'm now implementing multiple VPN tunnels for external connections. We strive to keep the external "private addresses" our basic using NAT network.
I can get the Tunnel to work without problems using the ACL SHEEP; However, this technique requires that our internal network is aware of their external addresses "private." Our goal is to enter an address on the inside that is NAT to the external address 'private' and then shipped via the VPN tunnel. Basically to hide the external address 'private' of our internal systems that they would appear as thought the connection was one of our own networks.
The reverse is true coming from their external 'private' network. Any information of "their" private network external origin would result in our 'private' on arrival address space.
Is this possible? I am attaching a schema, which could help.
Hello
Yes, this should be possible. Lets say you allocate 10.112.2.250 as the address that you use to present the external server 192.168.10.10.
On your ASA device
public static 10.112.2.250 (exterior, Interior) 192.168.10.10 netmask 255.255.255.255
You will need to make sure that when the system tries to connect to 10.112.2.250 it is routed to the device of the SAA.
HTH
Jon
-
Creating a VPN Tunnel without RFC1918 subnets
Hi all
I was prompted to configure a Cisco router to one of our partners using a method with which I am familiar. That is why I hope someone here can guide me in the right direction. Essentially the establishment should be like this:
At one end there is a firewall with an IP address of 123.123.123.1 (all wrong FT). This must be the VPN endpoint. Behind this firewall is a server with a private IP 172.16.1.1. This private IP address is NAT due 123.123.123.2.
Now at the other end is a VPN router with an IP address of 234.234.234.1. It is another VPN endpoint. There is another internal server with the IP 10.0.0.1. I don't want to create an external NAT for this IP address that is internal if possible.
Essentially, I need to get 172.16.1.1 and 10.0.0.1 to communicate with each other via a VPN, but NOT to use their IP addresses in the VPN tunnel.
What is the best way to achieve this? Any help would be appreciated!
Craig
This configuration should do the trick for you...
-
Hello guys,.
I have an ASA 5505 firewall tries to create a VPN tunnel from site to site with a router of 2621 running Advanced IP services. The tunnel keeps do not and I don't know why. Below is the config.
!
hostname SeCuReWaLL
domain default.domain.invalid
activate 2KFQnbNIdI.2KYOU encrypted password
2KFQnbNIdI.2KYOU encrypted passwd
names of
name 192.168.2.0 outside
name 192.168.3.0 inside
!
interface Vlan1
Description of network links extended to outside of the
nameif outside
security-level 0
192.168.2.101 IP address 255.255.255.0
!
interface Vlan2
Description within a private network
nameif inside
security-level 100
address 192.168.3.1 IP 255.255.255.0
!
interface Ethernet0/0
!
interface Ethernet0/1
switchport access vlan 2
!
interface Ethernet0/2
Shutdown
!
interface Ethernet0/3
Shutdown
!
interface Ethernet0/4
Shutdown
!
interface Ethernet0/5
Shutdown
!
interface Ethernet0/6
Shutdown
!
interface Ethernet0/7
Shutdown
!
boot system Disk0: / asa822 - k8.bin
passive FTP mode
DNS server-group DefaultDNS
domain default.domain.invalid
allow inside_access_in to access extended list ip inside outside 255.255.255.0 255.255.255.0
outside_access_in list extended access permit icmp any any echo response
site_router to access extended list ip inside 255.255.255.0 allow 192.168.5.0 255.255.255.0
pager lines 24
Outside 1500 MTU
Within 1500 MTU
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 625.bin
don't allow no asdm history
ARP timeout 14400
Global 1 interface (outside)
NAT (inside) 0-list of access site_router
NAT (inside) 1 inside 255.255.255.0
Access-group outside_access_in in interface outside
Route outside 0.0.0.0 0.0.0.0 192.168.2.1 1
Outdoor 192.168.5.0 255.255.255.0 192.168.2.107 1
Timeout xlate 03:00
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-registration DfltAccessPolicy
Enable http server
HTTP inside 255.255.255.0 inside
No snmp server location
No snmp Server contact
Server enable SNMP traps snmp authentication linkup, linkdown cold start
Crypto ipsec transform-set esp-3des esp-sha-hmac secure_set
life crypto ipsec security association seconds 28800
Crypto ipsec kilobytes of life - safety 4608000 association
peer set card crypto ipsec_map 10 192.168.2.107
card crypto ipsec_map 10 transform-set secure_set
ipsec_map interface card crypto outside
crypto ISAKMP allow outside
crypto ISAKMP policy 10
preshared authentication
3des encryption
md5 hash
Group 5
lifetime 28800
Telnet timeout 5
SSH timeout 5
Console timeout 0
dhcpd dns 192.168.2.1
!
dhcpd address 192.168.3.10 - 192.168.3.40 inside
dhcpd allow inside
!a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
WebVPN
username admin privilege 15 encrypted password f3UhLvUj1QsXsuK7
tunnel-group 192.168.2.107 type ipsec-l2l
IPSec-attributes tunnel-group 192.168.2.107
pre-shared key *.
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the netbios
inspect the rsh
inspect the rtsp
inspect the skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect the tftp
inspect the sip
inspect xdmcp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
call-home
Profile of CiscoTAC-1
no active account
http https://tools.cisco.com/its/service/oddce/services/DDCEService destination address
email address of destination [email protected] / * /
destination-mode http transport
Subscribe to alert-group diagnosis
Subscribe to alert-group environment
Subscribe to alert-group monthly periodic inventory
monthly periodicals to subscribe to alert-group configuration
daily periodic subscribe to alert-group telemetry
Cryptochecksum:a6ffc4e9572dbee8e526c3013a96a510
: end!
InternetRouter hostname
!
boot-start-marker
boot-end-marker
!
!
No aaa new-model
no location network-clock-participate 1
No network-clock-participate wic 0
IP cef
!
!
!
!
no ip domain search
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
crypto ISAKMP policy 10
BA 3des
md5 hash
preshared authentication
Group 5
lifetime 28800
key cisco address 192.168.2.101 crypto ISAKMP xauth No.
!
!
Crypto ipsec transform-set esp-3des secure_set
!
ipsec_map 10 ipsec-isakmp crypto map
defined peer 192.168.2.101
Set transform-set secure_set
match the address router_site
!
!
!
!
interface Loopback0
192.168.5.1 IP address 255.255.255.0
!
interface FastEthernet0/0
IP 192.168.2.107 255.255.255.0
automatic duplex
automatic speed
ipsec_map card crypto
!
interface Serial0/0
no ip address
Shutdown
!
interface FastEthernet0/1
no ip address
Shutdown
automatic duplex
automatic speed
!
interface Serial0/1
no ip address
Shutdown
!
IP route 192.168.3.0 255.255.255.0 192.168.2.101
!
!
IP http server
no ip http secure server
!
router_site extended IP access list
ip licensing 192.168.5.0 0.0.0.255 192.168.3.0 0.0.0.255
!
!
!
!
control plan
!
!
!
Voice-port 1/0/0
!
Voice-port 1/0/1
!
Voice-port 1/1/0
!
Voice-port 1/1/1
!
!
!
!
!
!
!
!
Line con 0
exec-timeout 0 0
Synchronous recording
line to 0
line vty 0 4
opening of session
!
!
endInternetRouter #debug isakmp crypto
Crypto ISAKMP debug is on
InternetRouter #ping
Protocol [ip]:
Target IP address: 192.168.3.10
Number of repetitions [5]:
Size of datagram [100]:
Timeout in seconds [2]:
Extended commands [n]: y
Address source or interface: 192.168.5.1
Type of service [0]:
Set the DF bit in the IP header? [None]:
Validate the response data? [None]:
Data model [0xABCD]:
In bulk, Strict, Record, Timestamp, Verbose [no]:
Scan the range of sizes [n]:
Type to abort escape sequence.
Send 5, echoes ICMP 100 bytes to 192.168.3.10, time-out is 2 seconds:
Packet sent with the address source 192.168.5.1* 01:49:47.699 Mar 1: ISAKMP: ke received message (1/1)
* 01:49:47.699 Mar 1: ISAKMP: (0:0:N / A:0): THE application profile is (NULL)
* 01:49:47.699 Mar 1: ISAKMP: created a struct peer 192.168.2.101, peer port 500
* 01:49:47.699 Mar 1: ISAKMP: new created position = 0x8553C778 peer_handle = 0 x 80000013
* 01:49:47.699 Mar 1: ISAKMP: lock struct 0x8553C778, refcount IKE peer 1 for isakmp_initiator
* 01:49:47.699 Mar 1: ISAKMP: 500 local port, remote port 500
* 01:49:47.699 Mar 1: ISAKMP: set new node 0 to QM_IDLE
* 01:49:47.703 Mar 1: insert his with his 84074CC8 = success
* 01:49:47.703 Mar 1: ISAKMP: (0:0:N / A:0): cannot start aggressive mode, try the main mode.
* 01:49:47.703 Mar 1: ISAKMP: (0:0:N / A:0): found peer pre-shared key matching 192.168.2.101
* 01:49:47.703 Mar 1: ISAKMP: (0:0:N / A:0): built the seller-07 ID NAT - t
* 01:49:47.703 Mar 1: ISAKMP: (0:0:N / A:0): built of NAT - T of the seller-03 ID
* 01:49:47.703 Mar 1: ISAKMP: (0:0:N / A:0): built the seller-02 ID NAT - t
* 01:49:47.703 Mar 1: ISAKMP: (0:0:N / A:0): entry = IKE_MESG_FROM_IPSEC, IKE_SA_REQ_MM
* 01:49:47.707 Mar 1: ISAKMP: (0:0:N / A:0): former State = new State IKE_READY = IKE_I_MM1* 01:49:47.707 Mar 1: ISAKMP: (0:0:N / A:0): early changes of Main Mode
* 01:49:47.707 Mar 1: ISAKMP: (0:0:N / A:0): send package to 192.168.2.101 my_port 500 peer_port 500 (I) MM_NO_STATE
* 01:49:47.711 Mar 1: ISAKMP (0:0): packet received 192.168.2.101 dport 500 sport Global 500 (I) MM_NO_STATE
* 01:49:47.711 Mar 1: ISAKMP: (0:0:N / A:0): entry = IKE_MESG_FROM_PEER, IKE_MM_EXCH
* 01:49:47.711 Mar 1: ISAKMP: (0:0:N / A:0): former State = new State IKE_I_MM1 = IKE_I_MM2* 01:49:47.715 Mar 1: ISAKMP: (0:0:N / A:0): treatment ITS payload. Message ID = 0
* 01:49:47.715 Mar 1: ISAKMP: (0:0:N / A:0): load useful vendor id of treatment
* 01:49:47.715 Mar 1: ISAKMP: (0:0:N / A:0): supplier code seems the unit/DPD but major incompatibilite.123
* 01:49:47.715 Mar 1: ISAKMP: (0:0:N / A:0): provider ID is NAT - T v2
* 01:49:47.719 Mar 1: ISAKMP: (0:0:N / A:0): load useful vendor id of treatment
* 01:49:47.719 Mar 1: ISAKMP: (0:0:N / A:0): supplier code seems the unit/DPD but major incompatibility of 194
* 01:49:47.719 Mar 1: ISAKMP: (0:0:N / A:0): found peer pre-shared key matching 192.168.2.101
* 01:49:47.719 Mar 1: ISAKMP: (0:0:N / A:0): pre-shared key local found
* 01:49:47.719 Mar 1: ISAKMP: analysis of the profiles for xauth...
* 01:49:47.719 Mar 1: ISAKMP: (0:0:N / A:0): audit ISAKMP transform 1 against the policy of priority 10
* 01:49:47.719 Mar 1: ISAKMP: 3DES-CBC encryption
* 01:49:47.719 Mar 1: ISAKMP: MD5 hash
* 01:49:47.719 Mar 1: ISAKMP: group by default 5
* 01:49:47.719 Mar 1: ISAKMP: pre-shared key auth
* 01:49:47.723 Mar 1: ISAKMP: type of life in seconds
* 01:49:47.723 Mar 1: ISAKMP: life (basic) of 28800
* 01:49:47.723 Mar 1: ISAKMP: (0:0:N / A:0): atts are acceptable. Next payload is 0
* 1 Mar 01:49:48.119: ISAKMP:(0:1:SW:1): load useful vendor id of treatment
* 1 Mar 01:49:48.119: ISAKMP:(0:1:SW:1): vendor ID seems the unit/DPD but major incompatibility of 123
* 1 Mar 01:49:48.123: ISAKMP:(0:1:SW:1): vendor ID is NAT - T v2
* 1 Mar 01:49:48.123: ISAKMP:(0:1:SW:1): load useful vendor id of treatment
* 1 Mar 01:49:48.123: ISAKMP:(0:1:SW:1): vendor ID seems the unit/DPD but major incompatibility of 194
* 01:49:48.123 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE
* 01:49:48.123 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_I_MM2 = IKE_I_MM2* 1 Mar 01:49:48.127: ISAKMP:(0:1:SW:1): sending package to 192.168.2.101 my_port 500 peer_port 500 (I) MM_SA_SETUP
* 01:49:48.127 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE
* 01:49:.48.131 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_I_MM2 = IKE_I_MM3* 01:49:48.383 Mar 1: ISAKMP (0:134217729): packet received 192.168.2.101 dport 500 sport Global 500 (I) MM_SA_SETUP
* 01:49:48.383 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_FROM_PEER, IKE_MM_EXCH
* 01:49:48.383 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_I_MM3 = IKE_I_MM4* 1 Mar 01:49:48.387: ISAKMP:(0:1:SW:1): processing KE payload. Message ID = 0
* 1 Mar 01:49:48.887: ISAKMP:(0:1:SW:1): processing NONCE payload. Message ID = 0
* 01:49:48.887 Mar 1: ISAKMP: (0:1:SW:1): found peer pre-shared key matching 192.168.2.101
* 01:49:48.891 Mar 1: ISAKMP: (0:1:SW:1): SKEYID generated State
* 1 Mar 01:49:48.891: ISAKMP:(0:1:SW:1): load useful vendor id of treatment
* 1 Mar 01:49:48.891: ISAKMP:(0:1:SW:1): vendor ID is the unit
* 1 Mar 01:49:48.891: ISAKMP:(0:1:SW:1): load useful vendor id of treatment
* 1 Mar 01:49:48.891: ISAKMP:(0:1:SW:1): vendor ID seems the unit/DPD but major incompatibility of 145
* 1 Mar 01:49:48.891: ISAKMP:(0:1:SW:1): vendor ID is XAUTH
* 1 Mar 01:49:48.895: ISAKMP:(0:1:SW:1): load useful vendor id of treatment
* 1 Mar 01:49:48.895: ISAKMP:(0:1:SW:1): speaking to another box of IOS!
* 1 Mar 01:49:48.895: ISAKMP:(0:1:SW:1): load useful vendor id of treatment
* 01:49:48.895 Mar 1: ISAKMP: (0:1:SW:1): supplier code seems the unit/DPD but hash mismatch
* 01:49:48.895 Mar 1: ISAKMP: receives the payload type 20
* 01:49:48.895 Mar 1: ISAKMP: receives the payload type 20
* 01:49:48.895 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE
* 01:49:48.899 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_I_MM4 = IKE_I_MM4* 01:49:48.899 Mar 1: ISAKMP: (0:1:SW:1): send initial contact
* 01:49:48.899 Mar 1: ISAKMP: (0:1:SW:1): ITS been pr.e using id ID_IPV4_ADDR type shared-key authentication
* 01:49:48.899 Mar 1: ISAKMP (0:134217729): payload ID
next payload: 8
type: 1
address: 192.168.2.107
Protocol: 17
Port: 500
Length: 12
* 01:49:48.903 Mar 1: ISAKMP: (0:1:SW:1): the total payload length: 12
* 1 Mar 01:49:48.903: ISAKMP:(0:1:SW:1): sending package to 192.168.2.101 my_port 500 peer_port 500 (I) MM_KEY_EXCH
* 01:49:48.907 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE
* 01:49:48.907 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_I_MM4 = IKE_I_MM5* 01:49:48.907 Mar 1: ISAKMP (0:134217729): packet received 192.168.2.101 dport 500 sport Global 500 (I) MM_KEY_EXCH
* 1 Mar 01:49:48.911: ISAKMP:(0:1:SW:1): payload ID for treatment. Message ID = 0
* 01:49:48.911 Mar 1: ISAKMP (0:134217729): payload ID
next payload: 8
type: 1
address: 192.168.2.101
Protocol: 17
Port: 0
Length: 12
* 1 Mar 01:49:48.911: ISAKMP:(0:1:SW:1): peer games * no * profiles
* 1 Mar 01:49:48.911: ISAKMP:(0:1:SW:1): HASH payload processing. Message ID = 0
* 01:49:48.915 Mar 1: ISAKMP: received payload type 17
* 1 Mar 01:49:48.915: ISAKMP:(0:1:SW:1): load useful vendor id of treatment
* 1 Mar 01:49:48.915: ISAKMP:(0:1:SW:1): vendor ID is DPD
* 01:49:48.915 Mar 1: ISAKMP: (0:1:SW:1): SA authentication status:
authenticated
* 01:49:48.915 Mar 1: ISAKMP: (0:1:SW:1): SA has been authenticated with 192.168.2.101
* 01:49:48.915 Mar 1: ISAKMP: attempts to insert a 192.168.2.107/192.168.2.101/500/ peer and inserted 8553 778 successfully.
* 01:49:48.919 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_FROM_PEER, IKE_MM_EXCH
* 01:49:48.919 Mar 1: ISAKMP: (0:1:SW:1.): O State of LD = new State IKE_I_MM5 = IKE_I_MM6* 01:49:48.919 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE
* 01:49:48.919 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_I_MM6 = IKE_I_MM6* 01:49:48.923 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE
* 01:49:48.923 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_I_MM6 = IKE_P1_COMPLETE* 01:49:48.927 Mar 1: ISAKMP: (0:1:SW:1): start Quick Mode Exchange, M - ID of 590019425
* 1 Mar 01:49:48.931: ISAKMP:(0:1:SW:1): sending package to 192.168.2.101 my_port 500 peer_port 500 (I) QM_IDLE
* 01:49:48.931 Mar 1: ISAKMP: (0:1:SW:1): entrance, node-590019425 = IKE_MESG_INTERNAL, IKE_INIT_QM
* 01:49:48.931 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_QM_READY = IKE_QM_I_QM1
* 01:49:48.931 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_INTERNAL, IKE_PHASE1_COMPLETE
* 01:49:48.935 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_P1_COMPLETE = IKE_P1_COMPLETE* 01:49:48.939 Mar 1: ISAKMP (0:134217729): packet received 192.168.2.101 dport 500 sport Global 500 (I) QM_IDLE
* 01:49:48.939 Mar 1: ISAKMP: node set 330122531 to QM_IDLE
* 1 Mar 01:49:48.943: ISAKMP:(0:1:SW:1): HASH payload processing. Message ID = 330122531
* 1 Mar 01:49:48.943: ISAKMP:(0:1:SW:1): treatment protocol NOTIFIER INVALID_ID_INFO 1
0, message ID SPI = 330122531, a = 84074CC8
* 01:49:48.943 Mar 1: ISAKMP: (0:1:SW:1): the peer is not paranoid KeepAlive.* 01:49:48.943 Mar 1: ISAKMP: (0:1:SW:1): remove the reason for HIS "fatal Recevied of information' State (I) QM_IDLE (ext. 192.168.2.101)
* 01:49:48.943 Mar 1: ISAKMP: (0:1:SW:1): remove error node 330122531 FALSE reason 'informational (en) st.
Success rate is 0% (0/5)
InternetRouter #ate 1 "
* 01:49:48.943 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY
* 01:49:48.947 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_P1_COMPLETE = IKE_P1_COMPLETE* 01:49:48.947 Mar 1: ISAKMP (0:134217729): packet received 192.168.2.101 dport 500 sport Global 500 (I) QM_IDLE
* 01:49:48.951 Mar 1: ISAKMP: node set-412204705 to QM_IDLE
* 1 Mar 01:49:48.951: ISAKMP:(0:1:SW:1): sending package to 192.168.2.101 my_port 500 peer_port 500 (I) QM_IDLE
* 01:49:48.951 Mar 1: ISAKMP: (0:1:SW:1): purge the node-412204705
* 01:49:48.955 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_INTERNAL, IKE_PHASE1_DEL
* 01:49:48.955 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_P1_COMPLETE = IKE_DEST_SA* 01:49:48.955 Mar 1: ISAKMP: (0:1:SW:1): removal of HIS State "No reason" why (I) QM_IDLE (ext. 192.168.2.101)
* 01:49:48.955 Mar 1: ISAKMP: Unlocking IKE struct 0x8553C778 for isadb_mark_sa_deleted(), count 0
* 01:49:48.959 Mar 1: ISAKMP: delete peer node by peer_reap for 192.168.2.101: 8553 778
* 01:49:48.959 Mar 1: ISAKMP: (0:1:SW:1): error in node-590019425 FALSE reason for deletion "deleted IKE."
* 01:49:48.959 Mar 1: ISAKMP: (0:1:SW:1): node error 330122531 FALSE reason for deletion "removed IKE."
* 01:49:48.959 Mar 1: ISAKMP: (0:1:SW:1): entry = IKE_MESG_FROM_PEER, IKE_MM_EXCH
* 01:49:48.959 Mar 1: ISAKMP: (0:1:SW:1): former State = new State IKE_DEST_SA = IKE_DEST_SAHello
I gave a quick scan here for the configuration on both devices, found two or three commands are missing from the configuration of the ASA
ASA
---card crypto ipsec_map 10 correspondence address site_router
outside_access_in list extended access udp allowed any any eq 500
outside_access_in list extended access udp allowed any any eq 4500
outside_access_in list extended access allow esp a wholeI'm assuming pre shared key defined on ASA cisco is the same on router
On router
---------Try running the following commands: -.
No crypto ipsec transform-set esp-3des secure_set
Crypto ipsec transform-set esp-3des esp-sha-hmac secure_setAt the time of the opening of the tunnel, please gather at the debug crypto isa 127 output and debug crypto ipsec 127 of ASA
You can also check the configuration below document link
http://www.Cisco.com/en/us/products/ps6120/products_configuration_example09186a00805e8c80.shtml
Ignore the map route on router configuration contained in the above document *.
HTH...
Kind regards
Mohit -
Help with a VPN tunnel between ASA 5510 and Juniper SSG20
Hello
We have a customer wanting to configure a VPN Site to Site tunnel between a new purchased 5510 of ASA located in his direction with its Juniper SSG20 Office, located in the main office. We contacted HP and they send us a Cisco professional to do the job.
After 2 days from 16:00 to 22:00 and error and countless hours of research online and nunerous calls, we are still unable to get traffic from the network of agencies to enter the tunnel.
Main branch
1.1.1.2 1.1.1.1
----- -----------
192.168.8.0/24 | ASA|-----------------------------------| Juniper | 192.168.1.0/24
----- -----------
192.168.8.254 192.168.1.254According to Cisco professionals, the tunnel is now in place but no traffic through. We are unable to ping anything on the network on the other side (192.168.1.0/24). We receive timeout ping all the time. The Cisco professional told us it's a routing or NAT problem and he's working on a solution!
Through research, I came across a post on Experts-Exchange (here) [the 1st comment on the original post] which States "...". that both sides of the VPN must have a different class of LAN for the VPN to work... " Would that be our problem?
It has become a critical issue to the point that he had to replace the Cisco ASA with a temporary Juniper SSG5 on another subnet (192.168.7.0/24) to get the tunnel upward and through traffic until the ASA VPN issue is resolved and I didn't need to say that the client is killing us!
Help is very appreciated.
Thank you
1. Yes, ping package from the interface of the ASA is considered valuable traffic to the LAN of Juniper.
SAA, need you traffic from the interface source ASA's private, because interesting to determine by crypto ACL MYLIST traffic between 192.168.8.0/24 and 192.168.1.0/24.
You will also need to add the following configuration to be able to get the ping of the interface of the ASA:
management-private access
To initiate the ping of the private interface ASA:
ping 192.168.1.254 private
2. the default time before the next generation of new key is normally 28800 seconds, and if there is no interesting traffic flowing between 2 subnets, he'll tear the VPN tunnel down. As soon as there is interesting traffic, the VPN tunnel will be built automatically into the next generation of new key. However, if there is traffic before generating a new key, the new tunnel will be established, and VPN tunnel will remain standing and continue encrypt and decrypt traffic.
Currently, your configuration has been defined with ITS lifetime of 3600 seconds GOLD / 4608000 kilobytes of traffic before the next generate a new key (it will be either 3600 seconds, or 4608000 kilobytes period expires first). You can certainly change it by default to 28800 seconds without configuring kilobytes. SA life is negotiated between the ASA and Juniper, and whatever is the lowest value will be used.
Hope that helps.
-
Hello
My PIX is currently configured to allow all traffic IPSEC enter my network (sysopt permit-ipsec connection). I would like to change that so that I can define what traffic is permitted (and off).
My installation is simple (IMO). I only have the value default outside & inside interfaces. I guess I can control "outbound VPN traffic" in an incoming ACL inside interface.
But how can I control what traffic is allowed when entering the VPN tunnel? I don't have any interface to apply this since it is a VPN tunnel.
And I can't apply to the external interface, I think that, given that traffic arriving on this interface is ESP traffic, so encrypted and of course, I want to be able to define what is allowed in based on what looks like the decrypted packet.
Any thoughts anyone?
Thank you and best regards,
Kevin
IPSEC traffic is decrypted before going through the outdoor LCD. When you browse the ACL, the Source address and destination correspond to the real IPs. So to accomplish what you want is easy, just remove the sysopt permit-ipsec connection and change your external LCD, using the real IP as Source and Destination addresses.
For example, you have a vpn lan2lan with your inside network 10.10.10.0 24 and a remote control inside the 172.20.0.0/16 network and you want to give to this network access to a web server to the 10.10.10.33 just add a line
acl_out permit tcp 172.20.0.0 access list 255.255.0.0 host 10.10.10.33 eq 80
Access-group acl_out in interface outside
acl_out will end up with a mixture of address public and private Source and it is ok, the PIX don't care.
-
NAT before going on a VPN Tunnel Cisco ASA or SA520
I have a friend who asked me to try to help. We are established VPN site to site with a customer. Our camp is a Cisco sa520 and side there is a control point. The tunnel is up, we checked the phase 1 and 2 are good. The question is through the tunnel to traffic, our LAN ip address are private addresses 10.10.1.0/24 but the client says must have a public IP address for our local network in order to access that server on local network there. So, in all forums, I see that you cannot NAT before crossing the VPN tunnel, but our problem is that our site has only 6 assigned IP addresses and the comcast router, on the side of the firewall SA520 WAN. So we were wondering was there a way we can use the WAN on the SA520 interface or use another available 6 who were assigned to the NAT traffic and passes through the tunnel. That sounds confusing to you? Sorry, but it's rarely have I a customer say that I must have a public IP address on my side of the LAN. Now, I say this is a SA520 firewall, but if it is not possible to do with who he is a way were able with an ASA5505?
Help or direction would be very useful.
Hello
I guess I could quickly write a basic configuration. Can't be sure I remember all correctly. But should be the biggest part of it.
Some of the course settings may be different depending on the type of VPN L2L connection settings, you have chosen.
Naturally, there are also a lot of the basic configuration which is not mentioned below.
For example
- Configurations management and AAA
- DHCP for LAN
- Logging
- Interface "nonstop."
- etc.
Information for parameters below
- x.x.x.x = ASA 'outside' of the public IP interface
- y.y.y.y = ASA "outside" network mask
- z.z.z.z = ASA "outside" IP address of the default gateway
- a.a.a.a = the address of the remote site VPN L2L network
- b.b.b.b = mask of network to the remote site VPN L2L
- c.c.c.c = IP address of the public peer device VPN VPN L2L remote site
- PSK = The Pre Shared Key to connect VPN L2L
Interfaces - Default - Access-list Route
interface Vlan2
WAN description
nameif outside
security-level 0
Add IP x.x.x.x y.y.y.y
Route outside 0.0.0.0 0.0.0.0 z.z.z.z
interface Ethernet0
Description WAN access
switchport access vlan 2
- All interfaces are on default Vlan1 so their ' switchport access vlan x "will not need to be configured
interface Vlan1
LAN description
nameif inside
security-level 100
10.10.1.0 add IP 255.255.255.0
Note to access the INSIDE-IN list allow all local network traffic
access to the INTERIOR-IN ip 10.10.1.0 list allow 255.255.255.0 any
group-access INTERIOR-IN in the interface inside
Configuring NAT and VPN L2L - ASA 8.2 software and versions prior
Global 1 interface (outside)
NAT (inside) 1 10.10.1.0 255.255.255.0
Crypto ipsec transform-set AES-256 aes-256-esp esp-sha-hmac
crypto ISAKMP policy 10
preshared authentication
aes-256 encryption
sha hash
Group 2
lifetime 28800
L2L-VPN-CRYPTOMAP of the access list allow ip x.x.x.x a.a.a.a b.b.b.b host
card crypto WAN-CRYPTOMAP 10 matches L2L-VPN-CRYPTOMAP address
card crypto WAN-CRYPTOMAP 10 set peer c.c.c.c
card crypto WAN-CRYPTOMAP 10 the value transform-set AES-256
card crypto WAN-CRYPTOMAP 10 set security-association second life 3600
CRYPTOMAP WAN interface card crypto outside
crypto isakmp identity address
crypto ISAKMP allow outside
tunnel-group c.c.c.c type ipsec-l2l
tunnel-group c.c.c.c ipsec-attributes
pre-shared key, PSK
NAT and VPN L2L - ASA 8.3 software configuration and after
NAT source auto after (indoor, outdoor) dynamic one interface
Crypto ipsec transform-set ikev1 AES-256 aes-256-esp esp-sha-hmac
IKEv1 crypto policy 10
preshared authentication
aes-256 encryption
sha hash
Group 2
lifetime 28800
L2L-VPN-CRYPTOMAP of the access list allow ip x.x.x.x a.a.a.a b.b.b.b host
card crypto WAN-CRYPTOMAP 10 matches L2L-VPN-CRYPTOMAP address
card crypto WAN-CRYPTOMAP 10 set peer c.c.c.c
card crypto WAN-CRYPTOMAP 10 set transform-set AES-256 ikev1
card crypto WAN-CRYPTOMAP 10 set security-association second life 3600
CRYPTOMAP WAN interface card crypto outside
crypto isakmp identity address
Crypto ikev1 allow outside
tunnel-group c.c.c.c type ipsec-l2l
tunnel-group c.c.c.c ipsec-attributes
IKEv1 pre-shared key, PSK
I hope that the above information was useful please note if you found it useful
If it boils down to the configuration of the connection with the ASA5505 and does not cut the above configuration, feel free to ask for more
-Jouni
-
ISPS double and two redundant ASA 5520 VPN tunnels
Hi all
I have a requirement that looks like this:
-with two ISPs (of course public IP of different subnets), I have two firewalls that we have to do 2 l2l VPN tunnels.
Virtual private networks will be redundant to each other and in the case where one of the links is congested, traffic should pass through the other tunnel.
Did someone do something like that?
Thank you
Vlad
Hi Vlad,
To have redundant connections, I suggest the following link:
ASA/PIX 7.x: example of redundant Configuration or backup ISP links
To find out when the link is congested? I don't think it could be possible at all on the SAA, with a UDP IP SLA jitter, but I think that it is supported only on IOS routers.
Analysis of IP Service levels using the UDP IP SLA jitter operation
Thank you.
Portu.
Please note all messages that will be useful.
-
Cisco 1841 how vpn tunnels? default 100vpn?
Hi everyone, I have read the previous posts and I read that the cisco 1841 can manage up to 100 default VPN tunnels.
1. is this true? (I enclose my worm of show)
2. this version of IOS support SSL VPN tunnels as well?
SH ver
Cisco IOS Software, 1841 (C1841-ADVSECURITYK9-M), Version 12.4 (3i), VERSION of the SOFTWARE (fc2)
Technical support: http://www.cisco.com/techsupport
Copyright (c) 1986-2007 by Cisco Systems, Inc.
Updated Thursday 28 November 07 18:48 by stshenROM: System Bootstrap, Version 12.4 (13r) T, RELEASE SOFTWARE (fc1)
Uptime SPAREROUTER is 7 minutes
System to regain the power ROM
System image file is "flash: c1841-advsecurityk9 - mz.124 - 3i.bin".... Output omitted
Cisco 1841 (revision 7.0) with 234496 K/K 27648 bytes of memory.
Card processor ID FTX1151Y0BQ
2 FastEthernet interfaces
1 module of virtual private network (VPN)
Configuration of DRAM is 64 bits wide with disabled parity.
191K bytes of NVRAM memory.
62720K bytes of ATA CompactFlash (read/write)Configuration register is 0 x 2102
SPAREROUTER #.
Thank you
Randall
Hello
I guess that means that the total number of vpn ipsec tunnels taken in charge by the router of SSL VPN AIM is 800.
If you want only a SSL VPN without the AIM module can it be based on the license.
Kind regards
Anisha
P.S.: Please mark this thread as answered if you feel that your query is resolved. Note the useful messages.
-
SBS 2008 office1 Serv2008 Office 2 need to share assets between them via a site to site VPN tunnel
Hi all.
I really need help on this one.
The office 1 installer running SBS2008 Office 2 running Server 2008.
Each firm has its own FQDN Office 1 CompanyABC 2 A_B_C of the company office.
Each firm has its own internal IP address pool Office 1 192.168.69.xxx and office 192.168.20.xxx 2.
Site to site VPN tunnel between 2 office routers Netgear SRX5308 1 and 2 Netgear FVS318G Office established and working.
Each firm has its own DNS server and acts as a domain controller
How to configure the 2 networks to see each other and be able to use assets on every network (files, printers)?
Is it so simple that the addition of another pool internal IP for each DNS server?
Thanks in advance for your help.
Hello
Your Question is beyond the scope of this community.
I suggest that repost you your question in the Forums of SBS.
https://social.technet.Microsoft.com/forums/en-us/home?Forum=smallbusinessserver
"Windows Small Business Server 2011 Essentials online help"
https://msdn.Microsoft.com/en-us/library/home-client.aspx
TechNet Server forums.
http://social.technet.Microsoft.com/forums/WindowsServer/en-us/home?category=WindowsServer
See you soon.
-
routing of traffic between vpn tunnels
Hello
I have a scenario like that.
There are two branch office vpn tunnels to the headquarters. I want to load balance the traffic on this two links using EIGRP.
in this way, another branch offic is also connected to the head office. now, I want to ensure the communication between two branch of the office through seat over these vpn tunnels.
Concerning
skrao
Hello
Here is a great link that describes a similar setup to yours:
http://www.Cisco.com/en/us/Tech/tk583/TK372/technologies_configuration_example09186a008009438e.shtml
Good reading and after return if there is anything that you are not clear.
PLS, don't forget to rate messages.
Paresh
-
Cisco ASA 5515 two asa firewall ipsec vpn tunnel is not coming
HelloW everyone.
I configured ipsec vpn tunnel between Singapore and Malaysia with asa firewall.
but the vpn does not come to the top. can someone tell me what can be the root cause?
Here is the configuration of twa asa: (I changed the ip address all the)
Singapore:
See the race
ASA 2.0000 Version 4
!
ASA5515-SSG520M hostname
activate the encrypted password of PVSASRJovmamnVkD
names of
!
interface GigabitEthernet0/0
nameif inside
security-level 100
IP 192.168.15.4 255.255.255.0
!
interface GigabitEthernet0/1
nameif DMZ
security-level 50
IP 192.168.5.3 255.255.255.0
!
interface GigabitEthernet0/2
nameif outside
security-level 0
IP 160.83.172.8 255.255.255.224
<--- more="" ---="">
!
<--- more="" ---="">
interface GigabitEthernet0/3
<--- more="" ---="">
Shutdown
<--- more="" ---="">
No nameif
<--- more="" ---="">
no level of security
<--- more="" ---="">
no ip address
!
interface GigabitEthernet0/4
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/5
nameif test
security-level 100
IP 192.168.168.219 255.255.255.0
!
interface Management0/0
management only
nameif management
security-level 100
IP 192.168.1.1 255.255.255.0
!
connection of the banner ^ C please disconnect if you are unauthorized access ^ C
connection of the banner please disconnect if you are unauthorized access
boot system Disk0: / asa922-4-smp - k8.bin
passive FTP mode
network of the SG object
<--- more="" ---="">
192.168.15.0 subnet 255.255.255.0
network of the MK object
192.168.6.0 subnet 255.255.255.0
service of the TCP_5938 object
Service tcp destination eq 5938
Team Viewer description
service tcp_3306 object
Service tcp destination eq 3306
service tcp_465 object
tcp destination eq 465 service
service tcp_587 object
Service tcp destination eq 587
service tcp_995 object
tcp destination eq 995 service
service of the TCP_9000 object
tcp destination eq 9000 service
network of the Inside_host object
Home 192.168.15.202
service tcp_1111 object
Service tcp destination eq 1111
service tcp_7878 object
Service tcp destination eq 7878
service tcp_5060 object
SIP, service tcp destination eq
<--- more="" ---="">
service tcp_5080 object
Service tcp destination eq 5080
network of the NETWORK_OBJ_192.168.15.0_24 object
192.168.15.0 subnet 255.255.255.0
inside_access_in list extended access allowed object SG ip everything
OUTSIDE_IN list extended access permit tcp any newspaper EQ 9000 Inside_host object
access extensive list ip 192.168.15.0 outside_cryptomap allow 255.255.255.0 object MK
pager lines 24
Enable logging
timestamp of the record
exploitation forest-size of the buffer of 30000
debug logging in buffered memory
recording of debug trap
debugging in the history record
asdm of logging of information
host test 192.168.168.231 record
host test 192.168.168.203 record
Within 1500 MTU
MTU 1500 DMZ
Outside 1500 MTU
test MTU 1500
management of MTU 1500
no failover
<--- more="" ---="">
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 7221.bin
don't allow no asdm history
ARP timeout 14400
no permit-nonconnected arp
NAT (inside, outside) static source SG SG static destination MK MK non-proxy-arp-search to itinerary
!
network of the SG object
NAT dynamic interface (indoor, outdoor)
network of the Inside_host object
NAT (inside, outside) interface static 9000 9000 tcp service
inside_access_in access to the interface inside group
Access-group OUTSIDE_IN in interface outside
Route outside 0.0.0.0 0.0.0.0 160.83.172.x 1
Route inside 10.0.1.0 255.255.255.0 192.168.15.199 1
Route inside 10.0.2.0 255.255.255.0 192.168.15.199 1
Route inside 10.0.11.0 255.255.255.0 192.168.15.199 1
Route inside 10.1.0.0 255.255.0.0 192.168.15.199 1
Route inside 10.8.0.0 255.255.0.0 192.168.15.199 1
Route inside 10.104.0.0 255.255.0.0 192.168.15.199 1
Route inside 192.168.8.0 255.255.255.0 192.168.15.199 1
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
<--- more="" ---="">
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
identity of the user by default-domain LOCAL
the ssh LOCAL console AAA authentication
Enable http serverCommunity trap SNMP-server host test 192.168.168.231 *.
No snmp server location
No snmp Server contact
Server enable SNMP traps syslog
Crypto ipsec transform-set ikev1 VPN-TRANSFORM esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
<--- more="" ---="">
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA-TRANS-aes - esp esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-128-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-TRANS-aes - esp esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-128-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA-TRANS esp-aes-192 esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-192-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5-TRANS esp-aes-192 esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-192-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA-TRANS esp-aes-256 esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-256-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5-TRANS esp-aes-256 esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-256-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-SHA-TRANS esp-3des esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-3DES-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-TRANS esp-3des esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-3DES-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
<--- more="" ---="">
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA-TRANS esp - esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-DES-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-DES-MD5-TRANS esp - esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-DES-MD5-TRANS mode transit
Crypto ipsec pmtu aging infinite - the security association
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 define ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
crypto CRYPTO - map 2 map corresponds to the address outside_cryptomap
card crypto CRYPTO-map 2 set peer 103.246.3.54
card crypto CRYPTO-map 2 set ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
card crypto CRYPTO-map 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
CRYPTO-card interface card crypto outside
trustpool crypto ca policy
Crypto ikev1 allow outside
IKEv1 crypto policy 10
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400Console timeout 0
management of 192.168.1.2 - dhcpd address 192.168.1.254
enable dhcpd management
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
SSL encryption rc4-aes128-sha1 aes256-3des-sha1 sha1 sha1
internal GroupPolicy1 group strategy
attributes of Group Policy GroupPolicy1
Ikev1 VPN-tunnel-Protocol
username, password admin eY/fQXw7Ure8Qrz7 encrypted privilege 15
username gmsadmin password HS/VyK0jtJ/PANQT encrypted privilege 15
tunnel-group 143.216.30.7 type ipsec-l2l
tunnel-group 143.216.30.7 General-attributes
Group Policy - by default-GroupPolicy1
<--- more="" ---="">
IPSec-attributes tunnel-group 143.216.30.7
IKEv1 pre-shared-key *.
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
Overall description
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
<--- more="" ---="">
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:ccce9a600b491c8db30143590825c01d
: endMalaysia:
:
ASA 2.0000 Version 4
!
hostname ASA5515-SSG5-MK
activate the encrypted password of PVSASRJovmamnVkD
names of
!
interface GigabitEthernet0/0
nameif inside
security-level 100
IP 192.168.6.70 255.255.255.0
!
interface GigabitEthernet0/1
nameif DMZ
security-level 50
IP 192.168.12.2 255.255.255.0
!
interface GigabitEthernet0/2
nameif outside
security-level 0
IP 143.216.30.7 255.255.255.248
<--- more="" ---="">
!
interface GigabitEthernet0/3
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/4
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/5
nameif test
security-level 100
IP 192.168.168.218 255.255.255.0
!
interface Management0/0
management only
nameif management
security-level 100
IP 192.168.1.1 255.255.255.0
!
<--- more="" ---="">
Interface Port - Channel 1
No nameif
no level of security
IP 1.1.1.1 255.255.255.0
!
boot system Disk0: / asa922-4-smp - k8.bin
passive FTP mode
clock timezone GMT + 8 8
network of the SG object
192.168.15.0 subnet 255.255.255.0
network of the MK object
192.168.6.0 subnet 255.255.255.0
service of the TCP_5938 object
Service tcp destination eq 5938
Team Viewer description
service tcp_3306 object
Service tcp destination eq 3306
service tcp_465 object
tcp destination eq 465 service
service tcp_587 object
Service tcp destination eq 587
service tcp_995 object
tcp destination eq 995 service
service of the TCP_9000 object
<--- more="" ---="">
tcp destination eq 9000 service
network of the Inside_host object
Home 192.168.6.23
service tcp_1111 object
Service tcp destination eq 1111
service tcp_7878 object
Service tcp destination eq 7878
service tcp_5060 object
SIP, service tcp destination eq
service tcp_5080 object
Service tcp destination eq 5080
network of the NETWORK_OBJ_192.168.2.0_24 object
192.168.6.0 subnet 255.255.255.0
inside_access_in list extended access allowed object SG ip everything
VPN-INTERESTING-TRAFFIC extended access list permit ip object MK SG
OUTSIDE_IN list extended access permit tcp any newspaper EQ 9000 Inside_host object
outside_cryptomap to access extended list ip 192.168.6.0 allow 255.255.255.0 object SG
pager lines 24
Enable logging
timestamp of the record
exploitation forest-size of the buffer of 30000
debug logging in buffered memory
recording of debug trap
asdm of logging of information
<--- more="" ---="">
host test 192.168.168.231 record
host test 192.168.168.203 record
Within 1500 MTU
MTU 1500 DMZ
Outside 1500 MTU
test MTU 1500
management of MTU 1500
reverse IP check management interface path
no failover
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 7221.bin
don't allow no asdm history
ARP timeout 14400
no permit-nonconnected arp
NAT (inside, outside) static source MK MK static destination SG SG route no-proxy-arp-search
NAT (inside, outside) static source NETWORK_OBJ_192.168.2.0_24 NETWORK_OBJ_192.168.2.0_24 static destination SG SG route no-proxy-arp-search
!
network of the MK object
NAT dynamic interface (indoor, outdoor)
network of the Inside_host object
NAT (inside, outside) interface static 9000 9000 tcp service
inside_access_in access to the interface inside group
Access-group OUTSIDE_IN in interface outside
Route outside 0.0.0.0 0.0.0.0 143.216.30.x 1
<--- more="" ---="">
Route inside 10.2.0.0 255.255.0.0 192.168.6.200 1
Route inside 10.6.0.0 255.255.0.0 192.168.6.200 1
Route inside 192.168.254.0 255.255.255.0 192.168.6.200 1
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
identity of the user by default-domain LOCAL
AAA authentication http LOCAL console
the ssh LOCAL console AAA authentication
Enable http serverNo snmp server location
No snmp Server contact
Crypto ipsec transform-set ikev1 VPN-TRANSFORM esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
<--- more="" ---="">
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA-TRANS-aes - esp esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-128-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-TRANS-aes - esp esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-128-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA-TRANS esp-aes-192 esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-192-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5-TRANS esp-aes-192 esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-192-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA-TRANS esp-aes-256 esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-256-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5-TRANS esp-aes-256 esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-256-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-SHA-TRANS esp-3des esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-3DES-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-TRANS esp-3des esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-3DES-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
<--- more="" ---="">
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA-TRANS esp - esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-DES-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-DES-MD5-TRANS esp - esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-DES-MD5-TRANS mode transit
Crypto ipsec pmtu aging infinite - the security association
crypto CRYPTO - map 2 map corresponds to the address outside_cryptomap
card crypto CRYPTO-map 2 set peer 160.83.172.8
card crypto CRYPTO-map 2 set ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
CRYPTO-card interface card crypto outside
trustpool crypto ca policy
Crypto ikev1 allow outside
IKEv1 crypto policy 10
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400
SSH timeout 60
SSH group dh-Group1-sha1 key exchange
Console timeout 0
management of 192.168.1.2 - dhcpd address 192.168.1.254
enable dhcpd management
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
SSL encryption rc4-aes128-sha1 aes256-3des-sha1 sha1 sha1
attributes of Group Policy DfltGrpPolicy
Ikev1 VPN-tunnel-Protocol l2tp ipsec without ssl-client
internal GroupPolicy1 group strategy
attributes of Group Policy GroupPolicy1
Ikev1 VPN-tunnel-Protocol
username, password admin eY/fQXw7Ure8Qrz7 encrypted privilege 15
username gmsadmin password HS/VyK0jtJ/PANQT encrypted privilege 15
<--- more="" ---="">
tunnel-group MK SG type ipsec-l2l
IPSec-attributes tunnel-group MK-to-SG
IKEv1 pre-shared-key *.
tunnel-group 160.83.172.8 type ipsec-l2l
tunnel-group 160.83.172.8 General-attributes
Group Policy - by default-GroupPolicy1
IPSec-attributes tunnel-group 160.83.172.8
IKEv1 pre-shared-key *.
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
<--- more="" ---="">
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:d41d8cd98f00b204e9800998ecf8427e
: endGood news, that VPN has been implemented!
According to the ping problem, my suggestion is to check, if some type of firewall based on host computers on both sides block ICMP requests.
Anyway, you can still use the capture of packets on the inside of the interfaces of the two ASAs, to check if the ICMP traffic is to reach the ASA.
In addition, you can try to enable ICMP inspection:
Policy-map global_policy
class inspection_defaultinspect the icmp
inspect the icmp error
Maybe you are looking for
-
my ipod fell in the pool and ive put in the rice, but it does not turn when I put load response by heating but the screen is black and nothing happens.
-
missing applications after iOS 9.3
I upgraded my iPhone 6 IOS 9.2.1 to 9.3, and now the applications YouTube and Nike + running are missing. Please tell us how to bring back, thank you.
-
Hello, after updating my hdr-as15 wifi connection does not work because the password that is installed in the camera is invallid, can someone help me please I would like to communicate with my phone, congratulations michael
-
Remove iCloud locally cached document reader
Hello. I want to remove some documents offline cached locally to my iCloud drive app iPhone, without deleting icloud. How can I do? Thank you.
-
Update Windows SP3 and DVD will not work.
I show a history of update of. NETFramwork 3.5 and Service packs 3 dating back to May 2010. At the same time, I lost the use of the DVD +-RW. While I got the update automatic running, even when I try a download of express update, the system always