VPN Tunnel, routing
Hello
We had the following problem:
One of our customers is connected through the VPN Client software. Our counterpart is a hub. We use IP addresses in the range of 172.28.0.0 to 172.32.255.255.
The client uses IPs 172.16.0.0/13.
When the customer uses the tunnel a connection to a host in our net 172.16.x.x is possible. A connection to a host 172.32.x.x is not possible.
172.16.x.x ping is shown in the log file of my firewall (where all packages should travel through). A ping to 172.32.x.x do not reache the firewall.
Thanks in advance.
Deleted lines of the PIX configuration intellectual property Audit.
Apply the following command
web_access of access list 1 line allow icmp a whole
in_to_out of access list 1 line allow icmp a whole
Tags: Cisco Security
Similar Questions
-
Routing access to Internet through an IPSec VPN Tunnel
Hello
I installed a VPN IPSec tunnel for a friend's business. At his desk at home, I installed a Cisco SA520 and at it is remote from the site I have a Cisco RVS4000. The IPSec VPN tunnel works very well. The remote site, it can hit all of its workstations and peripheral. I configured the RVS4000 working in router mode as opposed to the bridge. In the Home Office subnet is 192.168.1.0/24 while the subnet to the remote site is 192.168.2.0/24. The SA520 is configured as Internet gateway for the headquarters to 192.168.1.1. The remote desktop has a gateway 192.168.2.1.
I need to configure the remote site so that all Internet traffic will be routed via the Home Office. I have to make sure that whatever it is plugged into the Ethernet on the RVS4000 port will have its Internet traffic routed through the Internet connection on the SA520. Currently I can ping any device on the headquarters of the remote desktop, but I can't ping anything beyond the gateway (192.168.1.1) in the Home Office.
Any help would be greatly appreciated.
Thank you.
Hi William, the rvs4000 does not support the tunnel or esp transfer wild-card.
-
VPN tunnel between the concentrator 3005 and router Cisco 827
I am trying to establish a VPN tunnel between the Central Office with VPN 3005 and controller branch Cisco 827 router.
There is a router of perimeter with access set up in front of the 3005 list.
I quote the ACLs on the Central perimeter router instructionsuivante to allow traffic to permit ip 3005 - acl 101 all 193.188.X.X (address of the hub)
I get the following message appears when I try to ping a local host in the Central site.
Can Anyoune give me the correct steps to 827 and 3005.
Thank you
CCNP Ansar.
------------------------------------------------------------------------------------------------------
Debug crypto ISAKMP
encryption of debugging engine
Debug crypto his
debug output
------------------
1d20h: IPSEC (sa_request):,.
(Eng. msg key.) Local OUTGOING = 172.22.113.41, distance = 193.188.108.165.
local_proxy = 202.71.244.160/255.255.255.240/0/0 (type = 4),
remote_proxy = 128.128.1.78/255.255.255.255/0/0 (type = 1),
Protocol = ESP, transform = esp - esp-md5-hmac.
lifedur = 3600 s and KB 4608000,
SPI = 0x83B8AC1B (2209917979), id_conn = 0, keysize = 0, flags = 0x400D
1d20h: ISAKMP: ke received message (1/1)
1d20h: ISAKMP: 500 local port, remote port 500
1d20h: ISAKMP (0:1): entry = IKE_MESG_FROM_IPSEC, IKE_SA_REQ_MM
Former State = new State IKE_READY = IKE_I_MM1
1d20h: ISAKMP (0:1): early changes of Main Mode
1d20h: ISAKMP (0:1): lot of 193.188.108.165 sending (I) MM_NO_STATE
1d20h: ISAKMP (0:1): retransmission phase 1 MM_NO_STATE...
1d20h: ISAKMP (0:1): will increment the error counter on his: retransmit the phase 1
1d20h: ISAKMP (0:1): retransmission phase 1 MM_NO_STATE
1d20h: ISAKMP (0:1): lot of 193.188.108.165 sending (I) MM_NO_STATE
1d20h: ISAKMP (0:1): retransmission phase 1 MM_NO_STATE...
1d20h: ISAKMP (0:1): will increment the error counter on his: retransmit the phase 1
1d20h: ISAKMP (0:1): retransmission phase 1 MM_NO_STATE
1d20h: ISAKMP (0:1): lot of 193.188.108.165 sending (I) MM_NO_STATE
1d20h: IPSEC (key_engine): request timer shot: count = 1,.
You must also allow the esp Protocol in your ACL.
access-list 101 permit esp any host x.x.x.x (address of the hub)
Hope this helps,
-Nairi
-
SA520w routing through site-to-site VPN tunnels
I have several offices that are connected using site-to-site VPN tunnels and all will use the SA520W (firmware 2.1.18). I currently have 3 routers in place, router tunnels created for the router B and c of router. I need assistance with the configuration to allow the guests to router site B get to the router site C. I have attempted to add a static route, but get a destination unreachable host trying to ping. Also, if I connect to the router site has via the Cisco VPN client, I'm not able to get resources on each site, B, or C.
A - the site 10.10.0.0/24
Site B - 10.0.0.0/24
Site of the C - 10.25.0.0/24
Any help is greatly appreciated.
So, that's what you have configured correctly?
RTR_A
||
_____________ || ___________
|| ||
RTR_B RTR_C
Since there is no tunnel between B and C there is no way for us past that traffic through RTR_A for two reasons. The most important reason is that subnet 10.25.0.0/24 (rtr_c) is not allowed to pass through the IPSec tunnel (it's okay to IPSec?) of rtr_a ==> rtr_b. You can't just add a statement of road because your addresses are not routable which is the reason why it fails.
Your only option is to create another tunnel between rtr_b and rtr_c. This may not be the ONLY option, but you should get what you need.
I hope this helps.
-
routing of traffic between vpn tunnels
Hello
I have a scenario like that.
There are two branch office vpn tunnels to the headquarters. I want to load balance the traffic on this two links using EIGRP.
in this way, another branch offic is also connected to the head office. now, I want to ensure the communication between two branch of the office through seat over these vpn tunnels.
Concerning
skrao
Hello
Here is a great link that describes a similar setup to yours:
http://www.Cisco.com/en/us/Tech/tk583/TK372/technologies_configuration_example09186a008009438e.shtml
Good reading and after return if there is anything that you are not clear.
PLS, don't forget to rate messages.
Paresh
-
I need to establish a vpn connection between my office and a computer over the internet, allowing access to the internal of the outside lan. I have a problem with my router and I am looking for a new.
Can I use x 3500 to establish a pptp vpn tunnel or it can work only as vpn passthrough?
This modem/router supports VPN passthrough for IPSec, PPTP and L2TP only. Try VPN Linksys Gigabit routers like the series of the LRT.
-
RV042 VPN tunnel with Samsung Ubigate ibg2600 need help
Hi all, ok before I completely remove all of my hair, I thought stop by here and ask the volume for you all with the hope that someone can track down the problem.
In short I am configuring a 'Gateway to gateway' vpn tunnel between two sites, I don't have access to the config of the router from Samsung, but the ISPS making sure that they followed my setup - watching newspapers RV042, I don't however see the reason for the failure - im no expert vpn...
Sorry if the log file turns on a bit, I didn't know where the beginning and the end was stupid I know... any advice would be greatly welcomed lol.
System log
Current time: Fri Sep 2 03:37:52 2009 all THE Log Log Log Log VPN Firewall Access system
Time
Type of event Message
2 sep 03:36:01 2009 value of VPN Log [Tunnel negotiation Info] Inbound SPI = c3bdba08
2 sep 03:36:01 2009 value of outbound SPI VPN Log [Tunnel negotiation Info] = c664c1ca
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation Info] > initiator send fast Mode 3rd package
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation Info] Quick Mode Phase 2 SA established, IPSec Tunnel connected
2 sep 03:36:02 2009 VPN journal Dead Peer Detection start, DPD delay = timeout = 10 sec 10 sec timer
2 sep 03:36:02 2009 VPN received log delete SA payload: ISAKMP State #627 removal
2 sep 03:36:02 2009 VPN Log Main Mode initiator
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation Info] > Send main initiator Mode 1 package
2 sep 03:36:02 2009 charge of VPN journal received Vendor ID Type = [Dead Peer Detection]
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation of Info]< initiator="" received="" main="" mode="" 2nd="" packet="">
2 sep 03:36:02 2009 VPN Log [Tunnel negotiation Info] > initiator send Mode main 3rd package
2 sep 03:36:03 2009 VPN Log [Tunnel negotiation of Info]< initiator="" received="" main="" mode="" 4th="" packet="">
2 sep 03:36:03 2009 Log [Tunnel negotiation Info] VPN > main initiator Mode to send 5 packs
2 sep 03:36:03 2009 Log [Tunnel negotiation Info] VPN > initiator receive hand Mode 6 Pack
2 sep 03:36:03 2009 log VPN main mode peer ID is ID_IPV4_ADDR: '87.85.xxx.xxx '.
2 sep 03:36:03 2009 Log [Tunnel negotiation Info] VPN Mode main Phase 1 SA established
2 sep 03:36:03 2009 log VPN [Tunnel negotiation Info] initiator Cookies = c527 d584 595 c 2c3b
2 sep 03:36:03 2009 log VPN [Tunnel negotiation Info] responder Cookies = b62c ca31 1a5f 673f
2 sep 03:36:03 2009 log quick launch Mode PSK VPN + TUNNEL + PFS
2 sep 03:36:03 2009 Log [Tunnel negotiation Info] VPN > initiator send fast Mode 1 package
2 sep 03:36:04 2009 VPN Log [Tunnel negotiation of Info]< initiator="" received="" quick="" mode="" 2nd="" packet="">
2 sep 03:36:04 2009 value of VPN Log [Tunnel negotiation Info] Inbound SPI = c3bdba09
2 sep 03:36:04 2009 value of outbound SPI VPN Log [Tunnel negotiation Info] = e3da1469
2 sep 03:36:04 2009 VPN Log [Tunnel negotiation Info] > initiator send fast Mode 3rd package
2 sep 03:36:04 2009 VPN Log [Tunnel negotiation Info] Quick Mode Phase 2 SA established, IPSec Tunnel connected
2 sep 03:36:04 2009 VPN journal Dead Peer Detection start, DPD delay = timeout = 10 sec 10 sec timer
2 sep 03:36:05 2009 VPN received log delete SA payload: ISAKMP State #629 removalPFS - off on tada and linksys router does not support the samsung lol! connected!

-
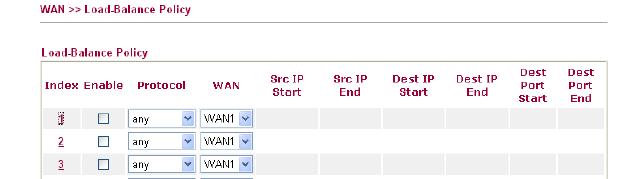
VPN connected, stream out of VPN tunnel
I mean that we have in place of the VPN Sites manage to sites with 2 RV042 router but it seams not as I wanted. Are you sure that each transfer of data through Router 2 will go into the VPN tunnel or it shuts down the VPN tunnel. I checked the routing table and saw that:
Sources mask Gateway Interface
2 1 or wan wan IP 255.255.255.0 ipsec0 private
By default 0.0.0.0 (ip wan 1 or 2) wan1 or wan2
.........
So what you think what sense data will pass through the line, it will go through the ipsec section or through wan1 or wan2. Ofcouse each data will pass through wan1 or wan2, but it can go inside the ipsec tunnel or ipsec outside tunnel. If she goes inside the ipsec tunnel, everything is ok, but if this isn't the case, transfer of unsecured data. I'm trying to access some website is not in private ip and it was outside ipsec tunnel go, I can capture and now that you have access.
Why with linksys have 2 work as draytek product even photos follow:
Can someone help me to answer this question, thank you for your attention
1. it depends on what the tunnels of your business allows. As I've written before, there are other protocols that allows you to route traffic through the VPN tunnel. Only IPSec cannot do this. For example, if your company uses GRE over IPSec then they can route traffic through their tunnels. Your RV does not support this.
2. If it's really plain IPSec then you cannot configure several subnets. You can try to implement the security group remote as a subnet more grand, such as 10.0.0.0/8. Of course the groups must match on both sides.
3. If you want to route all traffic through the tunnel, and then try to set the local/remote security to 0.0.0.0/0.0.0.0 group. Maybe it works.
The configuration of IPSec in the RV042 does not allow extremely complex configurations. It's mainly to connect two subnets between them.
-
VPN tunnel cascade w / SW NSA FWs
Hello
I have questions about VPN cascading between 3 firewall SonicWALL NSA. Let me explain my situation and what I want to achieve.
As shown in the diagram above, I have 3 branches connected to the Internet, which advanced to the LAN is the NSA SW FW. There is a VPN tunnel between each site: Site_A Site_ B, Site_A Site_ C, Site_B Site_ C. The Internet of the Site A traffic is redirected to the Site B. This Site A Cross Site B to access the Internet and LAN B. Site A through C access LAN C Site.
My question is: is it possible to remove the tunnel VPN Site_A-Site_C to and instead, through Site B to C LAN access? If so, how you can achieve this configuration?
What worries me is the VPN tunnel options that allow you to redirect all Internet traffic or a specific destination of LAN through objects (screenshots from Site A) address:
Without the redirection of Internet traffic, I thought about creating a group of addresses, including 2 B LAN and LAN C address objects. But I want to keep the Internet through Site B traffic redirection.
What do you think?
Thanks in advance for your help.
Hello
My comments below:
If you route indeed all traffic from A to B, the following must fill.
1. remove the tunnel A C
Ok.
2. site B will have A subnet that is defined as a local resource for C
Do you mean this by local resource?
3 C is going to have A subnet defined as remote resource
Ok.
If you route any traffic from A to B, the following must fill.
First step would be to remove the tunnel VPN between A and C, but I guess that you have assumed that it was already done.
1. define the C subnet as a remote resource on Site A
Yes, like a remote network for the A - B VPN tunnel.
2. tunnel of site B to A will need to subnet C defined as local resource
Ok.
3. tunnel of site B and C will need subnet defined as local resource
Ok.
4. the site will need to subnet C has defined as remote resource
Yes.
I'll do a test soon with 3 sites and see how it goes.
-
Hi all
I have a little problem concerning ASA and syslogs. I have a tunnel from site to site between a local ASA and ASA distance. Behind the ASA local, I have a central syslog server (which has no ASA as default gateway) which collects messages from all network devices and I want to get messages from the ASA remote as well.
The tunnel protects traffic between local networks behind each ASA, which includes ASA inside remote interface as well. The problem is that if I specify on the SAA distance my syslog server it does not pass through the VPN tunnel. The ASA remote sees my server syslog as being 'outside' so he's using the external IP address as the source-interface for the syslog message. Which of course does not pass through the tunnel. As much as I know there is no way to configure the interface source for logging under the SAA, that you can do on a normal IOS router.
I've found a few documents explaining this Setup on CCO, but they all imply I have extend the list for interesting traffic to access allow remote UDP/514 of the PIX traffic outside my local syslog server interface. This isn't something I want to do what I would get in routing complication in my LAN with a public IP address of the ASA remote.
Any suggestions? I thought I could use some sort of NAT on the ASA remote so that all traffic for my local network a source the remote PIX is translated on the inside interface, which in theory should pass the package via the tunnel. I did not go so far.
Any help is appreciated.
Best regards
Stefan
You can define the interface that the ASA will use to send the newspapers "syslog_ip host record.
Make sure you also do "access management".
Then the SAA should source the syslogs from inside the interface, which is probably encrypted with the crypto ACL.
I hope it helps.
PK
-
People,
You can help me understand how I can fix the following issues I have with a 1721 router (Version 12.3 (8) T5) and client VPN 4.6.01.x please.
BTW, the server at 192.168.3.2 is a file, DNS, WINS server and proxy for the LAN environment. All the staff of the PC is required to use the proxy but visitors on the 192.168.2.0 network can access the internet directly.
Back to my questions. I have the obligation to set up a VPN tunnel to connect to a PC that is running Terminal Server services / remote desktop on a PC to 192.168.1.9. When running the VPN software on the laptop I get a login prompt and everything seems fine. I ping the addresses of router and that works.
But the three things I don't understand:
1. I can't telnet with great success to the loopback address of the router, as well as other addresses 192.168.x.x. very well, but why is it possible that I can telnet to the 192.168.4.1 loopback address?
2. I can't DRC to the server on 192.168.3.2. The server can (and) accepts connections on a subnet, I created the network of 192.168.6.x I put up as VLAN6 on SEA4 (the port of spare on the map of ether 4 ports). The only thing I did not in the configuration of the interface was the nat ip within the statement.
3. I can't do a nslookup through the tunnel VPN (delays all the time) and neither can I http to the IIS server on the same 192.168.3.2 box. What I mean here is that other applications seem to work except telnet!)
Then...:
Why the telnet is so special? I thought that if I could telnet to the router, then I should be able to access the server. And before ask you, there is no firewall or whatever it is executed on the server by stopping this stupid connections. Hey, I'm the guy from router, not the jockey of server!
I've managed to misinterpret the statement "corresponds to the address 105" in the cryptomap? The ACL would reflect the traffic flow both ways?
I should have a statement of hash in the section of "crypto isakmp policy 5. The client indicates that the connection is OK then why should I need it?
I appreciate your time to help. I was scratching my head a lot in the last two days.
Timothy
Your NAT config, it is what kills you here. You can telnet to the router interface, because then the NAT configuration does not take effect (because NAT doesn't happen for passing traffic THROUGH the router, FOR her). You must refuse the IPSec traffic to be NAT would have, otherwise, it does not match the encryption access list and is not encrypted on the way back.
Your 100 access list is incorrect, remove it and add in the following:
access-list 100 deny ip 192.168.0.0 0.0.255.255 192.168.5.0 0.0.0.255
access-list 100 permit ip 192.168.0.0 0.0.255.255 everything
That said NAT VPN traffic does 192.168.5.0, but NAT do it if he goes anywhere else (Internet).
Also, you seem to have defined a map static encryption for your customer traffic, it is not used and may cause you problems with the list of access-105. Follow these steps to get rid of it and just use the dynamic encryption card:
no card crypto clientmap 1
You just need to have dynamic instance map (number 20) crypto left in your config file.
-
I have read on several posts on the topic and still think I'm missing something, I'm looking for help.
Basically, I'm now implementing multiple VPN tunnels for external connections. We strive to keep the external "private addresses" our basic using NAT network.
I can get the Tunnel to work without problems using the ACL SHEEP; However, this technique requires that our internal network is aware of their external addresses "private." Our goal is to enter an address on the inside that is NAT to the external address 'private' and then shipped via the VPN tunnel. Basically to hide the external address 'private' of our internal systems that they would appear as thought the connection was one of our own networks.
The reverse is true coming from their external 'private' network. Any information of "their" private network external origin would result in our 'private' on arrival address space.
Is this possible? I am attaching a schema, which could help.
Hello
Yes, this should be possible. Lets say you allocate 10.112.2.250 as the address that you use to present the external server 192.168.10.10.
On your ASA device
public static 10.112.2.250 (exterior, Interior) 192.168.10.10 netmask 255.255.255.255
You will need to make sure that when the system tries to connect to 10.112.2.250 it is routed to the device of the SAA.
HTH
Jon
-
Site to site VPN tunnel - cannot ping the second interface of the firewall peer inside2
I have two ASA 5505 firewall each with a basic license: FWa and FWb. currently there is a VPN tunnel between them work. I added a second (inside2) interface to the firewall, FWb, but I can't ping firewall FWa, so that I can ping the inside interface of FWa.
I can ping the FWb inside interface 192.168.20.1 from the FWa inside 172.16.1.1 interface, but I can not ping to the 10.52.100.10 of the FWa FWb inside2 interface. I can not ping the gateway host FWa 10.52.100.1.
I show the essential configuration of two firewalls as well as the debug icmp output on the two firewalls that I ping the internal interfaces and of FWa FWb inside2.
=========================================================Here is a skeleton of the FWa configuration:
name 172.16.1.0 network-inside
name 192.168.20.0 HprCnc Thesys
name 10.52.100.0 ring52-network
name 10.53.100.0 ring53-network
name S.S.S.S outside-interfaceinterface Vlan1
nameif inside
security-level 100
IP 172.16.1.1 255.255.255.0
!
interface Vlan2
Description Connection to 777 VLAN to work around static Comast external Modem and IP address.
nameif outside
security-level 0
outside interface IP address 255.255.255.240the DM_INLINE_NETWORK_5 object-group network
network-object HprCnc Thesys 255.255.255.0
ring52-network 255.255.255.0 network-object
ring53-network 255.255.255.0 network-objectthe DM_INLINE_NETWORK_3 object-group network
ring52-network 255.255.255.0 network-object
network-object HprCnc Thesys 255.255.255.0
ring53-network 255.255.255.0 network-objectoutside-interface of the access-list extended permitted Outside_5_cryptomap ip host object-group DM_INLINE_NETWORK_3
inside_nat_outbound list extended access allowed inside-network ip, 255.255.255.0 DM_INLINE_NETWORK_5 object-group
permit access list extended ip host 173.162.149.72 Outside_nat0_outbound aus_asx_uat 255.255.255.0NAT (inside) 0 access-list sheep
NAT (inside) 101-list of access inside_nat_outbound
NAT (inside) 101 0.0.0.0 0.0.0.0
NAT (outside) 0-list of access Outside_nat0_outboundcard crypto VPN 5 corresponds to the address Outside_5_cryptomap
card crypto VPN 5 set pfs Group1
VPN 5 set peer D.D.D.D crypto card
VPN 5 value transform-set VPN crypto card
tunnel-group D.D.D.D type ipsec-l2l
IPSec-attributes tunnel-Group D.D.D.D
pre-shared key *.=========================================================
FWb:
name 10.52.100.0 ring52-network
name 10.53.100.0 ring53-network
name 10.51.100.0 ring51-network
name 10.54.100.0 ring54-networkinterface Vlan1
nameif inside
security-level 100
address 192.168.20.1 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
address IP D.D.D.D 255.255.255.240
!
interface Vlan52
prior to interface Vlan1
nameif inside2
security-level 100
IP 10.52.100.10 255.255.255.0the DM_INLINE_NETWORK_3 object-group network
ring52-network 255.255.255.0 network-object
ring53-network 255.255.255.0 network-objectthe DM_INLINE_NETWORK_2 object-group network
ring52-network 255.255.255.0 network-object
object-network 192.168.20.0 255.255.255.0
ring53-network 255.255.255.0 network-objectinside_nat0_outbound to access extended list ip 192.168.20.0 allow 255.255.255.0 host S.S.S.S
inside2_nat0_outbound list extended access allowed object-group DM_INLINE_NETWORK_3 S.S.S.S ip hostoutside_1_cryptomap list extended access allowed object-group DM_INLINE_NETWORK_2 S.S.S.S ip host
NAT (inside) 0-list of access inside_nat0_outbound
NAT (inside) 1 0.0.0.0 0.0.0.0
inside2_nat0_outbound (inside2) NAT 0 access list
NAT (inside2) 1 0.0.0.0 0.0.0.0Route inside2 network ring51 255.255.255.0 10.52.100.1 1
Route inside2 network ring53 255.255.255.0 10.52.100.1 1
Route inside2 network ring54 255.255.255.0 10.52.100.1 1card crypto outside_map 1 match address outside_1_cryptomap
card crypto outside_map 1 set pfs Group1
outside_map game 1 card crypto peer S.S.S.S
card crypto outside_map 1 set of transformation-ESP-3DES-SHA
outside_map interface card crypto outsidetunnel-group S.S.S.S type ipsec-l2l
IPSec-attributes tunnel-group S.S.S.S
pre-shared key *.=========================================================================
I'm Tournai on icmp trace debugging on both firewalls and could see the traffic arriving at the inside2 interface, but never return to FWa.Ping Successul FWa inside the interface on FWb
FWa # ping 192.168.20.1
Type to abort escape sequence.
Send 5, echoes ICMP 100 bytes to 192.168.20.1, time-out is 2 seconds:
Echo request ICMP from outside-interface to 192.168.20.1 ID = 32068 seq = 23510 len = 72
! ICMP echo reply to 192.168.20.1 in outside-interface ID = 32068 seq = 23510 len = 72
....FWb #.
Echo ICMP of S.S.S.S to 192.168.20.1 ID request = 32068 seq = 23510 len = 72
ICMP echo reply 192.168.20.1 S.S.S.S ID = 32068 seq = 23510 len = 72
==============================================================================
Successful ping of Fwa on a host connected to the inside interface on FWbFWa # ping 192.168.20.15
Type to abort escape sequence.
Send 5, echoes ICMP 100 bytes to 192.168.20.15, wait time is 2 seconds:
Echo request ICMP from outside-interface to 192.168.20.15 ID = seq 50862 = 18608 len = 72
! ICMP echo reply to 192.168.20.15 in outside-interface ID = seq 50862 = 18608 len = 72
...FWb #.
Inside outside:S.S.S.S ICMP echo request: 192.168.20.15 ID = seq 50862 = 18608 len = 72
ICMP echo reply to Interior: 192.168.20.15 outside:S.S.S.S ID = seq 50862 = 18608 len = 72===========================
Unsuccessful ping of FWa to inside2 on FWb interfaceFWa # ping 10.52.100.10
Send 5, echoes ICMP 100 bytes to 10.52.100.10, wait time is 2 seconds:
Echo request ICMP from outside-interface to 10.52.100.10 ID = 19752 seq = 63173 len = 72
? Echo request ICMP from outside-interface to 10.52.100.10 ID = 19752 seq = 63173 len = 72
...FWb #.
10.52.100.10 ID of S.S.S.S ICMP echo request = 19752 seq = 63173 len = 72
10.52.100.10 ID of S.S.S.S ICMP echo request = 19752 seq = 63173 len = 72
....==================================================================================
Unsuccessful ping of Fwa to a host of related UI inside2 on FWb
FWa # ping 10.52.100.1
Type to abort escape sequence.
Send 5, echoes ICMP 100 bytes to 10.52.100.1, wait time is 2 seconds:
Echo request ICMP from outside-interface to 10.52.100.1 ID = 11842 seq = 15799 len = 72FWb #.
Echo request ICMP outside:S.S.S.S to inside2:10.52.100.1 ID = 11842 seq = 15799 len = 72
Echo request ICMP outside:S.S.S.S to inside2:10.52.100.1 ID = 11842 seq = 15799 len = 72=======================
Thank you
Hi odelaporte2,
Is very probably the "access management" command is not applied in the second inside, only inside primary (see the race management) which will confirm.
This command can be applied to an interface at a time, for example, if the law is now applied to the inside, it can not be applied to the inside2 at the same time.
It may be useful
-Randy-
-
RV016 split support VPN tunnel?
I read a rumor that the RV016 does not support split VPN tunnels.
See here:
My understanding is that on my router RV042 VPN tunnels will send internet traffic to the local gateway and send the traffic through the VPN tunnel only if they are intended for the remote subnet. It is my understanding of the "split tunnel".
Is it not true with the RV016?
Your understanding on split tunnel is correct. RV016 behaves like RV042 in this regard.
-
Cisco ASA 5515 two asa firewall ipsec vpn tunnel is not coming
HelloW everyone.
I configured ipsec vpn tunnel between Singapore and Malaysia with asa firewall.
but the vpn does not come to the top. can someone tell me what can be the root cause?
Here is the configuration of twa asa: (I changed the ip address all the)
Singapore:
See the race
ASA 2.0000 Version 4
!
ASA5515-SSG520M hostname
activate the encrypted password of PVSASRJovmamnVkD
names of
!
interface GigabitEthernet0/0
nameif inside
security-level 100
IP 192.168.15.4 255.255.255.0
!
interface GigabitEthernet0/1
nameif DMZ
security-level 50
IP 192.168.5.3 255.255.255.0
!
interface GigabitEthernet0/2
nameif outside
security-level 0
IP 160.83.172.8 255.255.255.224
<--- more="" ---="">
!
<--- more="" ---="">
interface GigabitEthernet0/3
<--- more="" ---="">
Shutdown
<--- more="" ---="">
No nameif
<--- more="" ---="">
no level of security
<--- more="" ---="">
no ip address
!
interface GigabitEthernet0/4
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/5
nameif test
security-level 100
IP 192.168.168.219 255.255.255.0
!
interface Management0/0
management only
nameif management
security-level 100
IP 192.168.1.1 255.255.255.0
!
connection of the banner ^ C please disconnect if you are unauthorized access ^ C
connection of the banner please disconnect if you are unauthorized access
boot system Disk0: / asa922-4-smp - k8.bin
passive FTP mode
network of the SG object
<--- more="" ---="">
192.168.15.0 subnet 255.255.255.0
network of the MK object
192.168.6.0 subnet 255.255.255.0
service of the TCP_5938 object
Service tcp destination eq 5938
Team Viewer description
service tcp_3306 object
Service tcp destination eq 3306
service tcp_465 object
tcp destination eq 465 service
service tcp_587 object
Service tcp destination eq 587
service tcp_995 object
tcp destination eq 995 service
service of the TCP_9000 object
tcp destination eq 9000 service
network of the Inside_host object
Home 192.168.15.202
service tcp_1111 object
Service tcp destination eq 1111
service tcp_7878 object
Service tcp destination eq 7878
service tcp_5060 object
SIP, service tcp destination eq
<--- more="" ---="">
service tcp_5080 object
Service tcp destination eq 5080
network of the NETWORK_OBJ_192.168.15.0_24 object
192.168.15.0 subnet 255.255.255.0
inside_access_in list extended access allowed object SG ip everything
OUTSIDE_IN list extended access permit tcp any newspaper EQ 9000 Inside_host object
access extensive list ip 192.168.15.0 outside_cryptomap allow 255.255.255.0 object MK
pager lines 24
Enable logging
timestamp of the record
exploitation forest-size of the buffer of 30000
debug logging in buffered memory
recording of debug trap
debugging in the history record
asdm of logging of information
host test 192.168.168.231 record
host test 192.168.168.203 record
Within 1500 MTU
MTU 1500 DMZ
Outside 1500 MTU
test MTU 1500
management of MTU 1500
no failover
<--- more="" ---="">
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 7221.bin
don't allow no asdm history
ARP timeout 14400
no permit-nonconnected arp
NAT (inside, outside) static source SG SG static destination MK MK non-proxy-arp-search to itinerary
!
network of the SG object
NAT dynamic interface (indoor, outdoor)
network of the Inside_host object
NAT (inside, outside) interface static 9000 9000 tcp service
inside_access_in access to the interface inside group
Access-group OUTSIDE_IN in interface outside
Route outside 0.0.0.0 0.0.0.0 160.83.172.x 1
Route inside 10.0.1.0 255.255.255.0 192.168.15.199 1
Route inside 10.0.2.0 255.255.255.0 192.168.15.199 1
Route inside 10.0.11.0 255.255.255.0 192.168.15.199 1
Route inside 10.1.0.0 255.255.0.0 192.168.15.199 1
Route inside 10.8.0.0 255.255.0.0 192.168.15.199 1
Route inside 10.104.0.0 255.255.0.0 192.168.15.199 1
Route inside 192.168.8.0 255.255.255.0 192.168.15.199 1
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
<--- more="" ---="">
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
identity of the user by default-domain LOCAL
the ssh LOCAL console AAA authentication
Enable http serverCommunity trap SNMP-server host test 192.168.168.231 *.
No snmp server location
No snmp Server contact
Server enable SNMP traps syslog
Crypto ipsec transform-set ikev1 VPN-TRANSFORM esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
<--- more="" ---="">
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA-TRANS-aes - esp esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-128-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-TRANS-aes - esp esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-128-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA-TRANS esp-aes-192 esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-192-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5-TRANS esp-aes-192 esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-192-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA-TRANS esp-aes-256 esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-256-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5-TRANS esp-aes-256 esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-256-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-SHA-TRANS esp-3des esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-3DES-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-TRANS esp-3des esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-3DES-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
<--- more="" ---="">
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA-TRANS esp - esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-DES-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-DES-MD5-TRANS esp - esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-DES-MD5-TRANS mode transit
Crypto ipsec pmtu aging infinite - the security association
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 define ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
crypto CRYPTO - map 2 map corresponds to the address outside_cryptomap
card crypto CRYPTO-map 2 set peer 103.246.3.54
card crypto CRYPTO-map 2 set ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
card crypto CRYPTO-map 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
CRYPTO-card interface card crypto outside
trustpool crypto ca policy
Crypto ikev1 allow outside
IKEv1 crypto policy 10
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400Console timeout 0
management of 192.168.1.2 - dhcpd address 192.168.1.254
enable dhcpd management
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
SSL encryption rc4-aes128-sha1 aes256-3des-sha1 sha1 sha1
internal GroupPolicy1 group strategy
attributes of Group Policy GroupPolicy1
Ikev1 VPN-tunnel-Protocol
username, password admin eY/fQXw7Ure8Qrz7 encrypted privilege 15
username gmsadmin password HS/VyK0jtJ/PANQT encrypted privilege 15
tunnel-group 143.216.30.7 type ipsec-l2l
tunnel-group 143.216.30.7 General-attributes
Group Policy - by default-GroupPolicy1
<--- more="" ---="">
IPSec-attributes tunnel-group 143.216.30.7
IKEv1 pre-shared-key *.
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
Overall description
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
<--- more="" ---="">
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:ccce9a600b491c8db30143590825c01d
: endMalaysia:
:
ASA 2.0000 Version 4
!
hostname ASA5515-SSG5-MK
activate the encrypted password of PVSASRJovmamnVkD
names of
!
interface GigabitEthernet0/0
nameif inside
security-level 100
IP 192.168.6.70 255.255.255.0
!
interface GigabitEthernet0/1
nameif DMZ
security-level 50
IP 192.168.12.2 255.255.255.0
!
interface GigabitEthernet0/2
nameif outside
security-level 0
IP 143.216.30.7 255.255.255.248
<--- more="" ---="">
!
interface GigabitEthernet0/3
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/4
Shutdown
No nameif
no level of security
no ip address
!
interface GigabitEthernet0/5
nameif test
security-level 100
IP 192.168.168.218 255.255.255.0
!
interface Management0/0
management only
nameif management
security-level 100
IP 192.168.1.1 255.255.255.0
!
<--- more="" ---="">
Interface Port - Channel 1
No nameif
no level of security
IP 1.1.1.1 255.255.255.0
!
boot system Disk0: / asa922-4-smp - k8.bin
passive FTP mode
clock timezone GMT + 8 8
network of the SG object
192.168.15.0 subnet 255.255.255.0
network of the MK object
192.168.6.0 subnet 255.255.255.0
service of the TCP_5938 object
Service tcp destination eq 5938
Team Viewer description
service tcp_3306 object
Service tcp destination eq 3306
service tcp_465 object
tcp destination eq 465 service
service tcp_587 object
Service tcp destination eq 587
service tcp_995 object
tcp destination eq 995 service
service of the TCP_9000 object
<--- more="" ---="">
tcp destination eq 9000 service
network of the Inside_host object
Home 192.168.6.23
service tcp_1111 object
Service tcp destination eq 1111
service tcp_7878 object
Service tcp destination eq 7878
service tcp_5060 object
SIP, service tcp destination eq
service tcp_5080 object
Service tcp destination eq 5080
network of the NETWORK_OBJ_192.168.2.0_24 object
192.168.6.0 subnet 255.255.255.0
inside_access_in list extended access allowed object SG ip everything
VPN-INTERESTING-TRAFFIC extended access list permit ip object MK SG
OUTSIDE_IN list extended access permit tcp any newspaper EQ 9000 Inside_host object
outside_cryptomap to access extended list ip 192.168.6.0 allow 255.255.255.0 object SG
pager lines 24
Enable logging
timestamp of the record
exploitation forest-size of the buffer of 30000
debug logging in buffered memory
recording of debug trap
asdm of logging of information
<--- more="" ---="">
host test 192.168.168.231 record
host test 192.168.168.203 record
Within 1500 MTU
MTU 1500 DMZ
Outside 1500 MTU
test MTU 1500
management of MTU 1500
reverse IP check management interface path
no failover
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 7221.bin
don't allow no asdm history
ARP timeout 14400
no permit-nonconnected arp
NAT (inside, outside) static source MK MK static destination SG SG route no-proxy-arp-search
NAT (inside, outside) static source NETWORK_OBJ_192.168.2.0_24 NETWORK_OBJ_192.168.2.0_24 static destination SG SG route no-proxy-arp-search
!
network of the MK object
NAT dynamic interface (indoor, outdoor)
network of the Inside_host object
NAT (inside, outside) interface static 9000 9000 tcp service
inside_access_in access to the interface inside group
Access-group OUTSIDE_IN in interface outside
Route outside 0.0.0.0 0.0.0.0 143.216.30.x 1
<--- more="" ---="">
Route inside 10.2.0.0 255.255.0.0 192.168.6.200 1
Route inside 10.6.0.0 255.255.0.0 192.168.6.200 1
Route inside 192.168.254.0 255.255.255.0 192.168.6.200 1
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
identity of the user by default-domain LOCAL
AAA authentication http LOCAL console
the ssh LOCAL console AAA authentication
Enable http serverNo snmp server location
No snmp Server contact
Crypto ipsec transform-set ikev1 VPN-TRANSFORM esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
<--- more="" ---="">
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA-TRANS-aes - esp esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-128-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-TRANS-aes - esp esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-128-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA-TRANS esp-aes-192 esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-192-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5-TRANS esp-aes-192 esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-192-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA-TRANS esp-aes-256 esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-AES-256-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5-TRANS esp-aes-256 esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-AES-256-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-SHA-TRANS esp-3des esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-3DES-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-TRANS esp-3des esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-3DES-MD5-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
<--- more="" ---="">
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA-TRANS esp - esp-sha-hmac
Crypto ipsec ikev1 transform-set ESP-DES-SHA-TRANS mode transit
Crypto ipsec transform-set ikev1 ESP-DES-MD5-TRANS esp - esp-md5-hmac
Crypto ipsec ikev1 transform-set ESP-DES-MD5-TRANS mode transit
Crypto ipsec pmtu aging infinite - the security association
crypto CRYPTO - map 2 map corresponds to the address outside_cryptomap
card crypto CRYPTO-map 2 set peer 160.83.172.8
card crypto CRYPTO-map 2 set ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
CRYPTO-card interface card crypto outside
trustpool crypto ca policy
Crypto ikev1 allow outside
IKEv1 crypto policy 10
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400
SSH timeout 60
SSH group dh-Group1-sha1 key exchange
Console timeout 0
management of 192.168.1.2 - dhcpd address 192.168.1.254
enable dhcpd management
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
SSL encryption rc4-aes128-sha1 aes256-3des-sha1 sha1 sha1
attributes of Group Policy DfltGrpPolicy
Ikev1 VPN-tunnel-Protocol l2tp ipsec without ssl-client
internal GroupPolicy1 group strategy
attributes of Group Policy GroupPolicy1
Ikev1 VPN-tunnel-Protocol
username, password admin eY/fQXw7Ure8Qrz7 encrypted privilege 15
username gmsadmin password HS/VyK0jtJ/PANQT encrypted privilege 15
<--- more="" ---="">
tunnel-group MK SG type ipsec-l2l
IPSec-attributes tunnel-group MK-to-SG
IKEv1 pre-shared-key *.
tunnel-group 160.83.172.8 type ipsec-l2l
tunnel-group 160.83.172.8 General-attributes
Group Policy - by default-GroupPolicy1
IPSec-attributes tunnel-group 160.83.172.8
IKEv1 pre-shared-key *.
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
<--- more="" ---="">
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:d41d8cd98f00b204e9800998ecf8427e
: endGood news, that VPN has been implemented!
According to the ping problem, my suggestion is to check, if some type of firewall based on host computers on both sides block ICMP requests.
Anyway, you can still use the capture of packets on the inside of the interfaces of the two ASAs, to check if the ICMP traffic is to reach the ASA.
In addition, you can try to enable ICMP inspection:
Policy-map global_policy
class inspection_defaultinspect the icmp
inspect the icmp error
Maybe you are looking for
-
How long do you need to renew Apple router?
Hi guys! Today I discovered that my modem is end of life cycle of Comcast that I sorta understand it it is 3 years or more. I'm going to buy a new modem, but the issue now is I've got my time Capsule from Apple the same time as the modem and it is 3
-
Periodic complete Lock up on M9402F running Vista Home Premo 64
I had my computer (HP Pavilion Elite m9400 desktop PC series) m9402f loaded with Vista Home Premium 64 from BestBuy a few months (mid-November) and shortly after getting it, the whole system locked on me. I don't get the blue screen of death, instea
-
Cannot use the default monitor
I have a Mac Pro 2009, 2.66 Ghz quad-core with 32 GB of RAM. I installed a graphics card from Nvidia GTX 960 with 4 GB of RAM after you download the latest drivers from the site Web of Nvidia and them preferring rather than the default drivers El Cap
-
OfficeJet Pro 6830: Problem with printhead
My operating system is Mac OS X 10.5 Yosemite but who did not have the menu drop down. In any case, I too more ink for my Officejet Pro 6830. I ran through the troubleshooting suggestions, nothing worked. I've unplugged and took ink and back in.
-
R400 stuck to the screen ThinkPad won't start or go to BIOS
I made sure that the machine was not in sleep or hibernation mode, and the user declares that the machine was fine a few hours ago. I removed the hard drive, but the behavior has not changed... Any ideas or is this or I have to plan an on-site visit
