VRA7 deployment best practices
Hello
I'm looking at in the deployment of VRA7 with the NSX.
is it always best practices to get your vm management running on a cluster that is different to your virtual machines in the workload, the reason why I ask is NSX, with this integrated is better she is hung up on a vcentre or two. I found the documentation below but I al looking for a little more in detail in the physical setup and roll cventres how much a typical would need.
see you soon
Hi Skoch, thanks for the reply.
I imagined he would have a lot of bugs but our outgoing env is UAT, so we have an opportunity to upgrade and just continue to work with 7 and keep up to date... I think that 7 gives us some great improvements so hopefully worth long term.
We are trying to do the update in April / may so fingers crossed a new update is released.
see you soon
Tags: VMware
Similar Questions
-
Best practices deployment CD to the internet non-connected PC
Hello
Are there things or best practices to be careful during the deployment of CD player on the internet non-connected PC? We currently use drive X, which we are patching regularly via a field startup script. Specifically, I want to know:
(1) CD player can be deployed in the same way that we currently do for Reader X (i.e. first install the base of the file through msiexec.exe /i package in a startup script, and then install the latest hotfix files using msiexec /p also using a startup script)
(2) CD player does require authentication via internet, or can that be disabled via Adobe Customization Wizard or group policy?
(3) can I disable all related and all features which requires an internet connection via Adobe Customization Wizard or group policy for clouds?
(4) at - it nothing another important to know?
Thank you.
Here are answers to your questions:
(1) CD player can be deployed the same way we do it currently for Reader X (i.e. first install the basic package of the file through msiexec.exe /i in a startup script, and then install the latest hotfix using msiexec /p also using a startup script) - Yes, CD player can be deployed in the same way as the X drive. There is no difference.
(2) CD player does require authentication via internet, or can that be disabled via Adobe Customization Wizard or group policy? -No, only DC Acrobat requires it. However, CD player, is free and requires no all identifications.
(3) can I disable all related and all features which requires an internet connection via Adobe Customization Wizard or group policy for clouds? -Yes, you can disable all cloud related features through the Customization Wizard or group policy
Ben above mentioned, you must always keep your reader to update to the latest version which has the latest security related bugs.
I hope that I have answered all your questions, and it helps. If you have any question, please report.
Thank you
Vinod
-
Best practices - Production deployment
What is the best practice to deploy an application built custom production?
Where to deploy in administration server or managed based on server?
Thank you
ShankarHi Shankar,
It is always better deploy your application on the managed server. You don't need to restart your server admin you have to restart your server managed to change your environment in relation to your application. Server Admin is intended to administer all instances of managed server. You can have several different managed servers for different specific applications. So it's a best practice to deploy your application on the managed server.
Kind regards
Roxane -
NTFS file cluster best practice deployment of Windows server on vSphere 5.1?
What are best practices, VMware or Microsoft that I need to know to make sure the server that I created 2 x Windows Server 2008 SP2 Enterprise MSCS of NTFS file (active / passive Cluster) can operate reliably to be accessed by more than 1,000 people?
The underlying data disk is RDM because I need to replicate the LUNS in the DR site using the tool table of SANCopy.
- SCSI controller LSI Logic SAS in Paravirtual changed
Not really an option... This is not supported by VMware in an MSCS configuration...
/ Rubeck
-
SQL Server 2005 STD. best practice for deploying VCenter 4
Hi all
I I know what kind of criteria from database / best practices that I need to create to support VCenter Management Server v4?
I use Windows Server 2003 standard and SQL Server 2005 SP3 Standard edition.
Thank you.
Kind regards
AWT
Maybe this can help you.
MCP, VCP
-
Material LV real-time Ethernet com best practices
Hello
I just started to learn the LV in real-time, and until I get a new cRIO I just played with a former PSC-2220.
Everything works, I am reading the tutorals nice about RT and deployment/running example to this target applications.
However, I don't know what is the best practice, the IP address of this device handling. For easy installation, after a device reset (and install the new RT runtimes, etc) I put just the HW to obtain the dynamic IP address of my router (DHCP). My laptop connects to the same router via wifi.
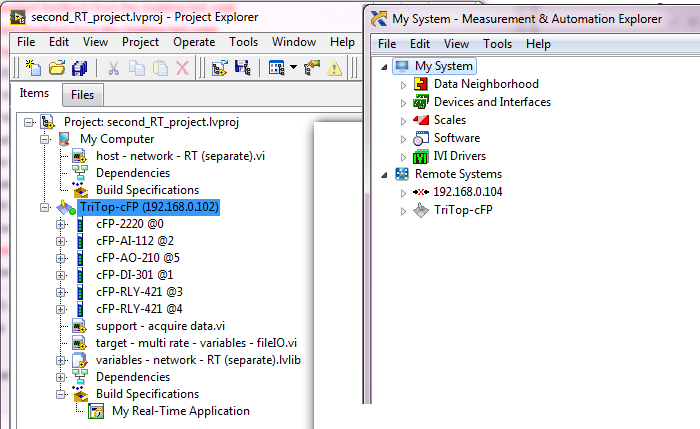
However, since after a few resets the target Gets a new IP (192.168.0.102, previous IP was... (104), I have to manually change the IP address in my project. Is it possible that the LV auto detects the target in my project? In addition, it seems that MAX retains the old information and creates a new line for the same target... so I guess that if the problem persists, MAX is going to fill?
 See screenshots below.
See screenshots below.As a solution, I'll try to use static IP for the target, so it must always use the same IP address.
What is the common procedure to avoid this kind of problems? Just using static IP? Or miss me him too something else here?
Thank you!
I just always use static IP addresses. It avoids just all kinds of questions, especially if you have several systems on the same network.
-
Best practices storage or advice
I try to develop a Java of BB application, currently appearing on local storage. The app will be for public use.
Someone has advice on when it is best to use the SD vs the persistent store? Is there a good best practices or document advice out there somewhere?
This application will have two types of data: preferences and what would be the data files on a desktop system.
I read on using the persistent store, and it seems to be a good option because of the level of control over the data for synchronization and such. But I noticed that some OSS BB applications use the SD card, not the persistent store.
If I'm going to deploy the application to the general public, I know that I'm working with many configurations as well as with the limits set by the policy of the company (assuming that these users can even install the app). So any advice on navigating these issues regarding the storage would be greatly appreciated.
Thank you!
The persistent store is fine for most cases.
If the transient data is very large, or must be copied to the device via the USB cable, then maybe the SD card should be considered.
However, many / most of the people do not have an SD card.
-
Best practices for the implementation of the power of fire
I am looking for a best practices deployment FireSight? Can someone help me?
Thank you
-mikgruff
There is not a general guide outside the configuration guide of product on the support page.
Partners have access to a guide designed for deployments of the value which is fairly comprehensive, but that is not published publicly.
There are some useful tips on recent presentations from Cisco Live in this area, but they are more PowerPoint as the deployment guide.
-
denying denying interceptor inline best practices
We recently deployed an inline IPS solution using software 5.1 7 E1. We wish to refuse-attacker-victim-pair-Inline for a few signatures on a particular subnet on the network but to destroy the rest.
To implement this correctly, I think that we must use Action SigEvent filters on the sensor and use the commands
> for all subnets agree that we want to allow deny actions for. I have seen that in the configuration of the sensor, you can implement in the section
> a > statement. My understanding is that does more for fleeing rather than deny solutions online. Am I right about that?
Please could someone on the list post that it is the best practical solution to deny deny attackers inline.
create 2 event action filters.
The first action event filter will match signatures and subnets you want to deny on and do not subtract all actions. Make sure that you set to "stop the match".
The following will match the same signature but the address 0.0.0.0 - 255.255.255.255. remove the appropriate actions.
The net result is that the filter action first event will apply when it matches and the second when it doesn't.
-
Best practices for the restart of the nodes of the ISE?
Hello community,
I administer an ISE installation with two nodes (I'm not a specialist of the ISE, my job is simply to manage the user/mac-addresses... but now I have to move my ISE a VMWare Cluster nodes to another VMWare Cluster.
(Both VMWare environments are connected to our network of the company, but are different environments. vMotion is not possible)
I want to stop ISE02, move it to our new VMWare environment and start it again.
That I could do this with our ISE01 node...
Are there best practices to achieve this? (Stop request first, stopl replikation etc.) ?
Can I really just reboot a node ISE - or I have consider something before I do this? After I did this?
All tasks after reboot?
Thanks for any answer!
ISE01
Administration, monitoring, Service policy
PRI (A), DRY (M)ISE02
Administration, monitoring, Service policy
SEC (A), PRI (M)There is a lot to consider here. If changing environments involves a change of IP address and IP extended, then your policies, profiles and DACL would also change among other things. If this is the case, create a new VM ISE in the new environment in evaluation license using the and recreate the old environment deployment by using the address of the new environment scheme. Then a new secondary node set rotation and enter it on the primary. Once this is done, you can re - host license from your old environment on your new environment. You can use this tool to re - host:
https://Tools.Cisco.com/swift/LicensingUI/loadDemoLicensee?formid=3999
If IP addressing is to stay the same, it becomes simpler.
First and always, perform an operational backup and configuration.
If the downtime is not a problem, or if you have a window of maintenance of an hour or so: just to close the two nodes. Transfer to the new environment and light them, head node first, of course.
If the downtime is a problem, stop the secondary node and transfer it to the new environment. Start the secondary node and when he comes back, stop the main node. Once that stopped services on the head node, promote the secondary node to the primary node.
Transfer of the FORMER primary node to the new environment and turn it on. She should play the role of secondary node. If it is not the case, assign this role through the GUI.
Remember, the proper way to shut down a node of ISE is:
request stop ise
Halt
By using these commands, the risk of database corruption decreases by 90% (remember to always backup).
Please rate useful messages and mark this question as answered if, in fact, does that answer your question. Otherwise, feel free to post additional questions.
Charles Moreton
-
test network for video conference. Cisco best practices
Are there documents and software to test the network not only immersive systems but the halls as well? Cisco TelePresence Readiness Assessment Manager? Please provide documents relating to best practices.
Thank you
Sent by Cisco Support technique iPad App
Hi Chris,
Please find the "Cisco TelePresence Network Systems Design Guide 2.0" document series CTS here:
https://supportforums.Cisco.com/docs/doc-23422
For T3 immersive systems, we have another document, please take a look at this document:
https://supportforums.Cisco.com/docs/doc-23391
Are there specific points of termination/infrastructure you would need more information ready network?
For more information concerning understanding Cisco TelePresence latency Jitter and loss targets and thresholds, please have a look here:
https://supportforums.Cisco.com/docs/doc-23423
The single telepresence network preparation software (AFAIK), is the old tool IPT. This tool will test your network deployment to check configurations appropriate to support the crossing of firewall solutions Cisco Expressway (I can send you this request separately if you wish).
Hope this helps,
Arne
-
ATA187 Port unused 2 - best practices?
Hello
I am deploying some ATA187s connection to CUCM 9.1.
I only need to use a port so the second port is not used, but I noticed from the ATA web page that it is trying to register with CUCM.
What is the best practice for port 2? -is it ok to leave set to CUCM or is it recommended to create a phone ATA187 in CUCM with DN is fake?
Or is it possible to disable the port 2?
Thank you
Hi James,
Life expectancy is to treat you well buddy!
For my 2 cents$ I prefer just to add a dummy DN to port 2 to keep
sending of the zillions of record attempts. There is a way to disable the port
(I'm sure) but I like just the path of least resistance especially when
You can use the port next week
See you soon!
Rob
"Why don't the best things always go away."
-The band
-
VCenter 6.0 upgrade vCenter Server 6.0 best practices?
Can someone help me best practices for best practices of vCenter server 6.0
These KB should help you to best practices and upgrade guide
Deployment Guide
https://www.VMware.com/files/PDF/Techpaper/VMware-vCenter-Server6-deployment-guide.PDF
Best practices
and new features have the peculiarity of cross
-
Best practices for network configuration of vSphere with two subnets?
Well, then I'll set up 3 ESXi hosts connected to storage shared with two different subnets. I configured the iSCSI initiator and the iSCSI with his own default gateway - 192.168.1.1 - targets through a Cisco router and did the same with the hosts configured with its own default gateway - 192.168.2.2. I don't know if I should have a router in the middle to route traffic between two subnets since I use iSCSI ports linking and grouping of NETWORK cards. If I shouldn't use a physical router, how do I route the traffic between different subnets and use iSCSI ports binding at the same time. What are the best practices for the implementation of a network with two subnets vSphere (ESX host network: iSCSI network)? Thank you in advance.
Install the most common iSCSI would be traffic between hosts and
the storage is not being routed, because a router it could reduce performance.
If you have VLAN 10(192.168.1.0/24) iSCSI, VLAN 20 (192.168.2.0/24) ESX
MGMT and VLAN 30 (192.168.3.0/24) comments VMs and VLAN 40 (192.168.4.0/24)
vMotion a deployment scenario might be something like:
NIC1 - vSwitch 0 - active VMK (192.168.1.10) MGMT, vMotion VMK (192.168.4.10)
standby
NIC2 - vSwitch 1 - current (VLAN30) guest virtual machine port group
NIC3 - vSwitch 2 - active VMK1 (192.168.1.10) iSCSI
NIC4 - vSwitch 2 - active VMK2 (192.168.1.11) iSCSI
NIC5 - vSwitch 1 - current (VLAN30) guest virtual machine port group
NIC6 - vSwitch 0 - MGMT VMK (192.168.2.10) standby, vMotion
VMK (192.168.4.10) active
You would place you on VLAN 10 storage with an IP address of something like target
192.168.1.8 and iSCSI traffic would remain on this VLAN. The default value
gateway configured in ESXi would be the router the VLAN 20 with an ip address of
something like 192.168.2.1. I hope that scenario help set some options.
Tuesday, June 24, 2014 19:16, vctl [email protected]>
-
Best practices for backup of vCenter device and ESXi hosts?
Hello
I have a new VMware environment based on 5.5 ESXi and vCenter Server Appliance. A few questions:
- What is the best practice to perform the backup of the vCenter Server Appliance? I set up the camera with the embedded SQL Express database.
- It's recommended to backup the ESXi host or is it easier to any re - install failure?
Best regards
,Thor-Egil
Hello
You can use VMware VDP to backup your device of vCenter. It is included in essentials, standard, enterprise, and enterprise as well as licenses.
I won't have backups of ESXi servers. Restore the backup would take more time that the deployment of a new ESXi.Only thing, you may want to consider is to enable logging remotely, so you can see why the hosts failed.
Concerning
Tim
Maybe you are looking for
-
How do I permanently remove iBook titles
I would like to delete some songs completely rather than keep them in the cloud.
-
Can I avoid excessive use of disk storage capacity by removing the old/obsolete updates... ?
Hello world. I use Windows Vista Home Basic. Updates are very frequent, and some are quite heavy. Do the sizes of these updates accumulate and continue to use the capacity of the disc over the course of months or years, or new updates replace those p
-
Applications open only twice after the connection
I have a user when he logs in the morning a clicks on Word or Excel or Outlook, IE 8.0, it will launch two instances of the application. If you close the two and then click the shortcurt once again, that it opens only once. It runs windows xp SP3, Of
-
System File Checker detects files from oembios that cannot be repaired
I ran the System File Checker on my computer Dell Dimension, and he found files that cannot be repaired: oembios.dat, oembios.sig and oembios.bin. The computer has Windows XP with Service Pack 3 installed and was purchased new in December 2002. The o
-
Photos are stretched on the monitor
Photos are stretched on the monitor and look larger than they actually are. How to make photos to display normally, they are then print?