Redundancy VPN by destination?
Hi all, I am trying to set up a vpn for one of my clients. they must have the same tunnel vpn with same source - destination traffic but destined for two different periods of public inquiry. so this should have sort of a primary vpn if it don't then a secondary vpn must support. This isn't the redundant Internet access provider scenario.
A network - B - vpn - terminate on X (most preffered)
A network - B - vpn - terminate on Y (less preferred)
On the ASA, you can do it with the primary encryption card with a higher priority than backup, but using the same ACL. If the first card cannot peer, the other will be implemented. It should be lower setting on the IPSec Security Association lifetime for this. You can also only defining the hub in single are created and the rays or receive only so that you do not have a RADIUS, creating a new SA when you do not want that it is for me.
Tags: Cisco Security
Similar Questions
-
Hi all
I need a solution for this implementation:
2 sites
2 internet connections each site (different suppliers)
1 ASA in each site
I need a config that allows me to have redundant VPN connections from one site to the other. I need to have a VPN using the, say, internet connection A of site 1 and internet connection from site 2 and if the internet connection A of site 1 goes down the VPN connect by using the internet connection B from site 1 to site 2 A internet connection. This must be done without user intervention.
If I can't do it with the ASA which can use to achieve this scenario? Another router (2900), a kind of load balancing?
I would like to use the ASA because I have a lot of inbound NAT configured and keeping addresses public IP on the SAA outside interface would be great.
Thank you, best regards.
Yes.
You can apply the same card encryption on both interfaces.
Also... If you have multiple VPN peers, they end on the same card encryption as well.
If you for example need many VPN Site to Site tunnels, you create a single card encryption with sequence numbers different to accept VPN connections.
Federico.
-
Question of redundancy VPN l2l using 2811 as endpoint devices
I have a new implementation of VPN L2L passes using two 2811 s than VPN terminal devices. I'll try to use the HSRP address between the public interfaces of both routers as VPN peer address. The problem that I found during the test is that the tunnel will become active and debugs watch the HSRP address as an invalid address to form the tunnel. Have a work-around, or a better plan for redundancy on peering address using similar devices? Thanks in advance.
Take a look at this doc about IOS IPSec HA.
-
Recovery site - redundant VPN peers
Hello all, thank you in advance for your expertise.
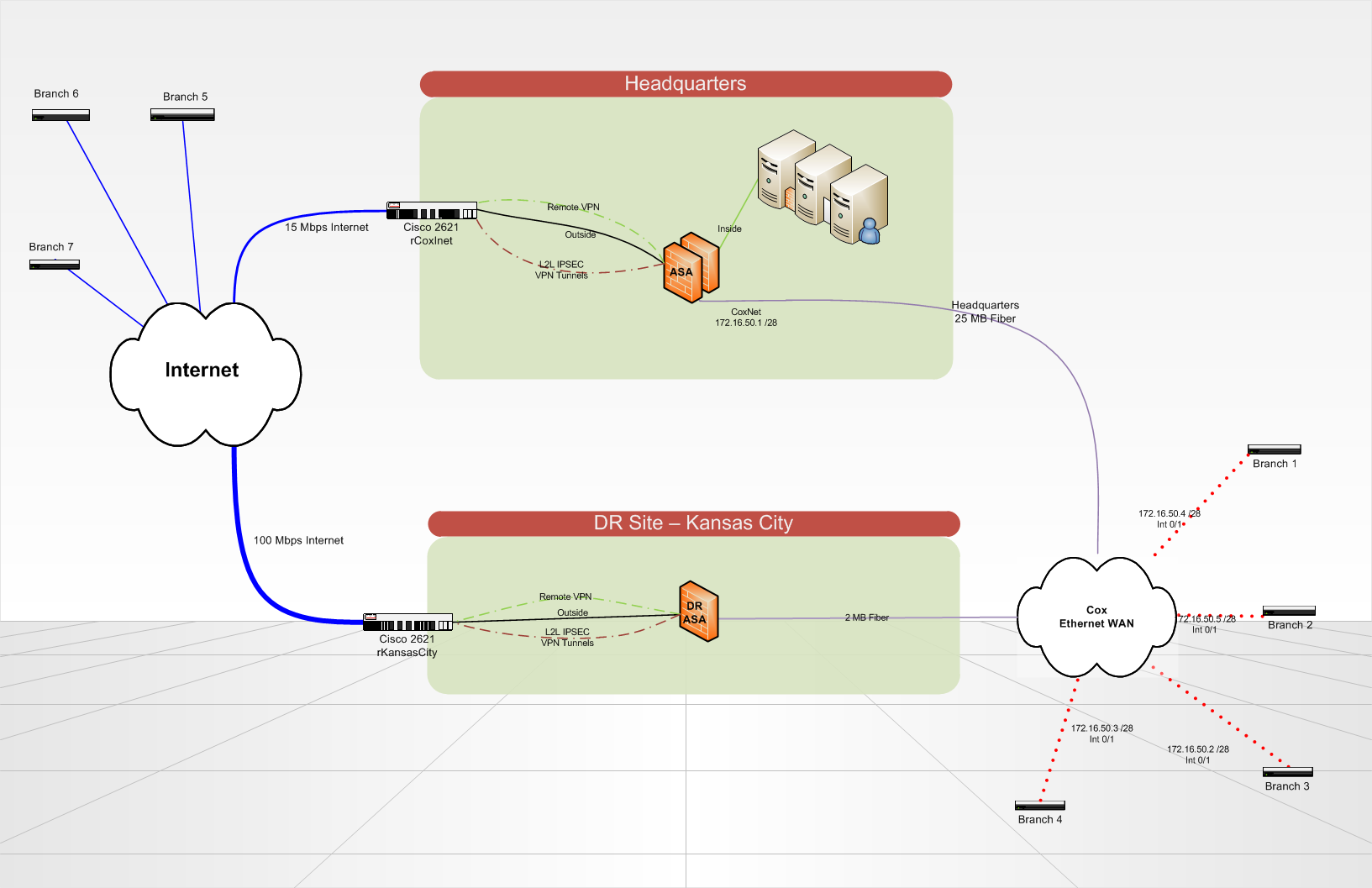
We put in place a recovery site disaster that will host the redundant copies of our servers and critical data in Kansas City. When disaster strikes, our headquarters site would be totally gone.
We currently have 7 locations that communicate to our HQ via VPN tunnels (whether on a circuit of the Internet or on a circuit of Cox Communications Ethernet WAN). Branch sites each can an ISR of Cisco 2821 router. At Headquarters and on the DR site, we use a Cisco ASA 5510 to terminate VPN tunnels and do everything that our column spinal routing. Routing on the ASA and branch routers is all static, using a routing protocol would be a nice update in the future... any ideas? We use IPSEC VPN lan lan tunnels 2, no GRE/VPN is used because it is not terminated by the ASA.
What is the best way to configure my routers for branch to automatically or manually failover to connect to one ASA different site of DR?
In addition, if my seat is still in place, but either my Internet or Cox headquarters ethernet circuit breaks down. How can I re - route all traffic in a loop to the seat on the right remains a circuit?
Is there a better way to do what I want to accomplish? BGP is not an option at this point due to its complexity.
Lucas,
To circumvent the two point separately.
The best way to provide active / standby time of reundancy is preferred peer in cryptographic cards (on the ISR routers).
You can choose to establish VPN to HQ and only if HQ is not aid you to DR, when HQ is you will EVENTUALLY return to it.
The answer to share of your questions may also be the preferred option by peers (and several counterparts in a crypto map entry).
This being said, you can try to send OSPF traffic to IPsec tunnel (and using the neighbor command to avoid the manipulation of mcast in pure IPsec).
Docs:
HTH,
Marcin
P. S.
If you want my personal opion, chaning ASAs in HQ and DR sites and put you in routers could make DMVPN or DVTI-ASIT scenario which gives you a lot more features ;-)
-
I have two sites with 2921 IPSec routers. Each router has 3 ethernet interfaces. A local area network, Internet, and an Ethernet based private circuit.
I need the site to site VPN between these routers, on the private circuit. However, this circuit fails on rare opportunity, so I want to have a VPN failover to review the Internet as a backup.
Doesn't matter to me if it's the primary failover / secondary or if there are load balanced with failover. What is essential, is that if a circuit fails, my remote site continues to communicate with the main office.
HSRP looks like I need two routers and I don't have one of the HSRP Protocol monitors several LAN interfaces.
I opened a case with TAC, but it has been a week without any progress.
Certainly, it is not so hard to do.
Hey Joe,
Router eigrp 100
Network 10.250.1.0 0.0.0.3 #10.250.1.1 is the IP address of the tunnel12
Network 10.250.1.4 0.0.0.3 #10.250.1.5 is the ip address of the tunnel122
network 192.168.1.0 # is the LAN segment that must be routed.
Remote router...
Router eigrp 100
Network 10.250.1.8 0.0.0.3 #10.250.1.9 is the IP address of the tunnel0
Network 10.250.1.12 0.0.0.3 #10.250.1.13 is the IP address of the tunnel1
network 192.168.12.0 # is the LAN segment that must be routed.
The two parties should normally be in the same subnet NW
for example if
You 12 is connected to tu0
then
one side have 10.250.1.1 and the other 10.250.1.2
If tu122 is connected to tu1
then
10.250.1.5 and the other side is 10.250.1.6
the two eigrp network should be the same
-
We have a VPN connection from site to site with a remote network and want to know if there is anyway to set a secondary IP address peer who would use VPNS to connect in case the primary became unavailable
Configuration of counterpart of backup for tunnel vpn on the same crypto map
Problem
You want to use several counterparts backup for a single vpn tunnel.
Solution
Configuration of several counterparts is equivalent to provide a list of relief. For each tunnel, the security apparatus tried to negotiate with the first peer in the list.
If this peer does not respond, the security apparatus made his way to the bottom of the list until a peer responds, or there is no peer more in the list.
The SAA must have a card encryption already configured as the primary counterpart. The secondary counterpart could be added after the primary.
This example configuration shows the primary counterpart as X.X.X.X and Y.Y.Y.Y as peer backup:
ASA (config) #crypto map mymap 10 peer set X.X.X.X Y.Y.Y.Y
http://www.Cisco.com/en/us/products/ps6120/products_tech_note09186a00807...
HTH
If useful rates
Sent by Cisco Support technique iPhone App
-
I have a scenario where I have 2 ISPS connected to a different 800 router. Inside network is a single a (10.10.10.0/24). It is a single office and this unique office has a L2L tunnel with another office (office-2). How configure failover and load balancing, and always keep the tunnel if one ISP goes down?
ciscobigcat,
I just asked one of the experts switch that I worked with and he told me the 4500 s cannot handle GRE tunnel even if they are L3 switches. So that would not work for you. 6500 or even the 3700 series switches should be able to do it without problem, but you should talk to your representative local sales to confirm.
You can absolutely send a tunnel through another tunnel. The concept is that build you a GRE tunnel between closure of the router behind the ASA closure on Router 1. Then you build plain ipsec between routers-1 tunnel and the ASA that match all ip traffic between the closure on Router-1 for the closure of the router behind the ASA.
-
Branch 5505, 1 circuit ISP, Dual - peer VPN Configuration for Data Center & Track Options
Hi all
I have a data center with two lines of ISP redundancy and two ASA 5520 for redundancy VPN to my branches. Each of my branches has 1 ASA 5505 with a base license and 1 ISP circuit. Currently all my VPN tunnels are built for data center main circuit ISP only, so if one goes down, I'm toast. I need to fix this. Problem is, I don't know how I can control failover on 5505 with 1 single line branch. Please see my picture for an example of how he looks at it right now.
So the problem is that the data center LAN my branch has to go to is identical regardless of which circuit of data center is in the. And I know the ASA rules say only 1 VPN tunnel can be active at a time if flow are the same. So in this case, I know you usually do:
card crypto outside_map 1 set 12.x.xxx.20 50.xxx.xx.190 counterpart
and then configure route followed to control when cut down the primary counterpart and turn back up by peers. But where I have only 1 ISP on the side of the branch, I'll only have 1 default route: route outside 0.0.0.0 0.0.0.0 3.3.3.2 1, will be used that the active end counterpart is the primary or the secondary data center. Also, since I did not have a second track, I can't configure followed on the main road with an SLA that defines the trigger conditions, because there is nothing to ensure the follow-up of the routing.
How is - a would handle a situation like this? Are there other features that can be taken off the roads? I really need to be able to define "num-package 5 ' in ALS so my sites are not beat all day, but once again, without something to follow, I can't really set up a meaningful SLAS. Any help is appreciated.
Thanks for the additional explanation. It helps to clarify your environment. EIGRP running on the Remote would be a nice option, but I'm not sure that it is supported on the SAA. I ran EIGRP to remote peers using IOS routers (using the two ACCORD with IPsec and VTI tunnels tunnels) and it was very effective. But on the SAA, I believe that we must seek an alternative.
It seems to me that using reverse road Injection as part of your VPN site-to-site should work. With IPP the ASA inserts a static route to remote resources when the VPN tunnel is negotiated and traffic can flow. If you redistribute the static in EIGRP EIGRP then must learn the ways of any ASA a currently active tunnel. And who should provide the dynamic rollover you need.
HTH
Rick
-
Configure the Cisco VPN client to pass through the VPN site-to-site (GUI)
Hello
I say hat the chain and responses I've seen to achieve this goal have been great...
https://supportforums.Cisco.com/discussion/12234631/Cisco-ASA-5505-VPN-p...
and
https://supportforums.Cisco.com/document/12191196/AnyConnect-client-site...
My question is "we will get this configuration by using the graphical user interface for someone who is not notified about the command line?"
Thank you
Of course, all this can be configured via ASDM.
Looking at the second example you posted above, they point you first change:
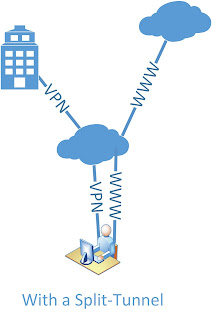
ACL split of the tunnel for the AnyConnect customer
This Configuration > remote access VPN > network (Client) access > AnyConnect connection profile > (chose the profile and select Edit) > (choose "Manage" next to group policy) > Edit > advanced > Split Tunneling > ensure that the policy does not "Inherit" but rather "Tunnel network list below" > Unselect "Inherit" next to the network list, then 'manage '. Enter your networks you want in the GUI in this dialog box. Click OK all the way back to the main window ASDM and click on apply.
You then change:
Crypto ACL for the tunnel from Site to Site
To do this, go to Configuration > VPN Site-to_site > connection profiles > (choose your profile and select edit) > add the VPN client address pool to the list of local network between protect networks. Yet once, click OK all the way back to the main window ASDM and click on apply.
Then, allow the
ASA to redirect back on the same interface traffic it receives
.. is defined under Configuration > Device Setup > Interfaces. (check the box at the bottom of this screen). Click on apply
Finally, there is the NAT exemption. For which go to Configuration > firewall > rules NAT. Add a NAT device rule before rules network object with Interface Source out, Source address your address pool VPN, the Destination address to include remote subnets and Action is Static Source NAT type source address and destination address remaining as original (i.e. without NAT). Once on OK all the way back to the main window ASDM and click on apply. Save and test.
Good luck. Don't forget to note the brand and posts useful when your question is answered.
-
Hello everyone
I have setup a VPN connection, which I can connect to. For all customers of connection, I want to give them an IP (from a subnet maybe) and let them use this IP address for all that they do.
Therefore, this:
and not current:
My inside is 192.168.1.0
My VPN IP pool is 192.168.30.5 - 200
My server (DNS, files, Web site) is 192.168.1.222Here's my setup. I scored what I thought might have something to do with it:
ASA Version 9.2 (1)
!
ciscoasa hostname
activate 8Ry2YjIyt7RRXU24 encrypted password
volatile xlate deny tcp any4 any4
volatile xlate deny tcp any4 any6
volatile xlate deny tcp any6 any4
volatile xlate deny tcp any6 any6
volatile xlate deny udp any4 any4 eq field
volatile xlate deny udp any4 any6 eq field
volatile xlate deny udp any6 any4 eq field
volatile xlate deny udp any6 any6 eq field
2KFQnbNIdI.2KYOU encrypted passwd
names of
pool of IP local IP-pool 192.168.30.5 - 192.168.30.200 mask 255.255.255.0
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
IP 192.168.1.253 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
IP address dhcp setroute
!
boot system Disk0: / asa921 - k8.bin
passive FTP mode
permit same-security-traffic intra-interface
network obj_any object
subnet 0.0.0.0 0.0.0.0
network of the object Server-25
Home 192.168.1.222
Description of the test server
network of the object server-80
Home 192.168.1.222
Description of the test server
network of the object server-443
Home 192.168.1.222
Description of the test server
network of the object server-2525
Home 192.168.1.222
Description of the test server
network of the object server-993
Home 192.168.1.222
Description of the test server
network of the object server-6001
Home 192.168.1.222
Description of the test server
network of the object server-6002
Home 192.168.1.222
Description of the test server
network of the object server-6003
Home 192.168.1.222
Description of the test server
network of the object server-6004
Home 192.168.1.222
Description of the test server
network of the VPN HOST object
192.168.30.0 subnet 255.255.255.0
the object to the Interior-net network
host 192.168.1.0
the VPN server object network
Home 192.168.1.222
outside_access_in list extended access permit tcp any object Server-25 eq smtp
outside_access_in list extended access permit tcp any object server-2525 2525 eq
outside_access_in list extended access permit tcp any object server-80 eq www
outside_access_in list extended access permit tcp any object server-443 https eq
outside_access_in list extended access permit tcp any object server-993 993 eq
outside_access_in list extended access permit tcp any object server-6001 eq 6001
outside_access_in list extended access permit tcp any object server-6002 6002 eq
outside_access_in list extended access permit tcp any object server-6003 eq 6003
outside_access_in list extended access permit tcp any object server-6004 eq 6004
outside_access_in to access ip 192.168.1.0 scope list allow 255.255.255.0 192.168.30.0 255.255.255.0
permit access-list Split-Tunnel-ACL standard 192.168.30.0 255.255.255.0
no pager
Enable logging
asdm of logging of information
Within 1500 MTU
Outside 1500 MTU
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 721.bin
don't allow no asdm history
ARP timeout 14400
no permit-nonconnected arp
NAT (indoor, outdoor) Interior-net Interior-NET static source static destination HOST-VPN-VPN-HOST
NAT VPN VPN-server destination (indoor, outdoor) static static source HOST-VPN-VPN-HOST
!
network obj_any object
NAT dynamic interface (indoor, outdoor)
network of the object Server-25
NAT (inside, outside) interface static tcp smtp smtp service
network of the object server-80
NAT (inside, outside) interface static tcp www www service
network of the object server-443
NAT (inside, outside) interface static tcp https https service
network of the object server-2525
NAT (inside, outside) interface static 2525 2525 tcp service
network of the object server-993
NAT (inside, outside) interface static tcp 993 993 service
network of the object server-6001
NAT (inside, outside) interface static tcp 6001 6001 service
network of the object server-6002
NAT (inside, outside) interface static tcp 6002 6002 service
network of the object server-6003
NAT (inside, outside) interface static 6003 6003 tcp service
network of the object server-6004
NAT (inside, outside) interface static service tcp 6004 6004
Access-group outside_access_in in interface outside
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
RADIUS AAA server HSS-auth-server protocol
allow only
AAA-server HSS-auth-server (inside) host 192.168.1.222
Timeout 5
key *.
identity of the user by default-domain LOCAL
Enable http server
http 192.168.1.0 255.255.255.0 inside
No snmp server location
No snmp Server contact
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec pmtu aging infinite - the security association
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 define ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
outside_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
outside_map interface card crypto outside
trustpool crypto ca policy
Crypto isakmp nat-traversal 30
Crypto ikev1 allow outside
IKEv1 crypto policy 10
authentication crack
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 20
authentication rsa - sig
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 30
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 40
authentication crack
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 50
authentication rsa - sig
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 60
preshared authentication
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 70
authentication crack
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 80
authentication rsa - sig
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 90
preshared authentication
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 100
authentication crack
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 110
authentication rsa - sig
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 120
preshared authentication
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 130
authentication crack
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 140
authentication rsa - sig
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 150
preshared authentication
the Encryption
sha hash
Group 2
life 86400
Telnet timeout 5
SSH stricthostkeycheck
SSH timeout 5
SSH group dh-Group1-sha1 key exchange
Console timeout 0interface ID client DHCP-client to the outside
dhcpd outside auto_config
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
internal HSSvpn group strategy
attributes of Group Policy HSSvpn
value of server WINS 192.168.1.222
value of server DNS 192.168.1.222
Ikev1 VPN-tunnel-Protocol
Split-tunnel-policy tunnelall
Split-tunnel-network-list value Split-Tunnel-ACL
HSS.dk value by default-field
activate dns split-tunnel-all
type tunnel-group HSSvpn remote access
attributes global-tunnel-group HSSvpn
address IP-pool pool
HSS-auth-server authentication-server-group
Group Policy - by default-HSSvpn
password-management
IPSec-attributes tunnel-group HSSvpn
IKEv1 pre-shared-key *.
tunnel-group HSSvpn ppp-attributes
No chap authentication
no authentication ms-chap-v1
ms-chap-v2 authentication
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:c85ff8bf61669bef56b4dad704a4930a
: endHello
Change Split Tunnel VPN in full Tunnel VPN, you have really do much in your configuration.
Seems that have already changed you the 'tunnelspecified' 'tunnelall' in configurations of the 'group policy' . You can delete the setup but that defines the ACL of Split Tunnel
attributes of Group Policy HSSvpn
No split-tunnel-network-list value Split-Tunnel-ACLSeems that you use an internal AAA server to manage authentication rather than on the SAA. I guess if you want to assign a specific IP address for VPN user/username, then it must be done on the side Server?
If you had the "username" on the SAA configurations you can set it up under its framework which "username" IP address gets when he or she connects with the VPN Client.
As naturally as you start using the complete Tunnel and all traffic from the VPN Client starts to get in the tunnel to the ASA you will need a NAT for VPN Client users Internet traffic. You can configure this NAT like this for example:
network of the VPN-POOL object
192.168.30.0 subnet 255.255.255.0interface of VPN-POOL dynamic NAT (outside, outside) after auto source
Note that this is a manual of NAT / double NAT statement real "nat" IS NOT inserted under the 'object' , but the 'object' is rather created it can be used in the "nat" command. I see that your other dynamic PAT configurations are configured with NAT Auto / object NAT network. You can do this like that too if you wish. Personally I do like that.
But as I said before, it seems that you have already configured the VPN to be full of Tunnel. It is perhaps not as it is? While it is connected with VPN, you should be able to check the secure routes (or something like that) section to see if it says "0.0.0.0" If Yes, then it should be tunneling all traffic.
Hope this helps :)
-Jouni
-
Jabber of Cisco on Cisco ipsec VPN client
Hello
I wonder if anyone has had this problem. I am currently using the 9.2.3 J4W customer and when I use Jabber in my office, everything works fine. IM works very well and my incoming and outgoing calls work. The question I have is when I work from home on my personal wifi and customer VPN Cisco (version 5.0.07.0290) ipsec remote in my area that the instant messaging and presence features work fine however only outgoing calls work. With Jabber, I can dial any DN in my organization and a willingness to work. The only problem is when someone tries to call me, I'll never get an alert for the incoming call. However my ip back to my desk phone will be keep ringing and I'll see the voicemail and calls to jabber? For some reason any call does not make for me on my VPN session. I'm not sure of what could be the problem. Jabber has certain requirements on ipsec VPN to work? We use the ASA 5510 firewall and VPN endpoint.
Thank you
William Gonzalez
CCNA R & S
William,
We recently had this problem: one of my other network admins had to prosecute with TAC, their resolution is to add
a static NAT on our ASA for external source outside translation is your VPN network, destination is your VPN network.
Thank you
-
Configure several IPSec VPN between Cisco routers
I would like to create multiple ipsec VPN between 3 routers. Before applying it, I would like to check on the config I wrote to see if it works. It's just on RouterA configuration for virtual private networks to RouterB, and RouterC.
As you can apply in a cyptomap by interface, I say with the roadmap, that it should be able to manage traffic for both routers. Or is there a better way to do it?
RouterA - 1.1.1.1
RouterB - 2.2.2.2
RouterC - 3.3.3.3
RouterA
crypto ISAKMP policy 10
BA 3des
preshared authentication
Group 2
ISAKMP crypto key RouterB address 2.2.2.2
ISAKMP crypto keys RouterC address 3.3.3.3
invalid-spi-recovery crypto ISAKMP
ISAKMP crypto keepalive 5 10 periodicals
ISAKMP crypto nat keepalive 30
!
life crypto ipsec security association seconds 28800
!
Crypto ipsec transform-set AES - SHA esp - aes 256 esp-sha-hmac
!
outsidemap 20 ipsec-isakmp crypto map
defined peer 2.2.2.2
game of transformation-AES-SHA
match address 222
outsidemap 30 ipsec-isakmp crypto map
defined peer 3.3.3.3
game of transformation-AES-SHA
match address 333
!
interface GigabitEthernet0/0
Description * Internet *.
NAT outside IP
outsidemap card crypto
!
interface GigabitEthernet0/1
Description * LAN *.
IP 1.1.1.1 255.255.255.0
IP nat inside
!
IP nat inside source map route RouterA interface GigabitEthernet0/0 overload
!
access-list 222 allow ip 1.1.1.0 0.0.0.255 2.2.2.0 0.0.0.255
access-list 223 deny ip 1.1.1.0 0.0.0.255 2.2.2.0 0.0.0.255
access-list 223 allow ip 1.1.1.0 0.0.0.255 any
access-list 333 allow ip 1.1.1.0 0.0.0.255 3.3.3.0 0.0.0.255
access-list 334 deny ip 1.1.1.0 0.0.0.255 3.3.3.0 0.0.0.255
access-list 334 allow ip 1.1.1.0 0.0.0.255 any
!
!
RouterA route map permit 10
corresponds to the IP 223 334
Hi Chris,
The two will remain active.
The configuration you have is for several ste VPN site is not for the redundant VPN.
The config for the redundant VPN is completely different allows so don't confuse is not with it.
In the redundant VPN configuration both peers are defined in the same card encryption.
Traffic that should be passed through the tunnel still depend on the access list, we call in the card encryption.
This access-lsist is firstly cheked and as a result, the traffic is passed through the correct tunnel
HTH!
Concerning
Regnier
Please note all useful posts
-
I do a search in the search of the best solution for switching between two ASA and hoped that someone wants to point me in the right direction.
The situation is this, we got:
-Head Office 2:
Each is equipped with an ASA 5505
-10 branches
Each is equipped with a 887 integrated services router.
Each is BranchOffice must have a redundant VPN connection at the headquarters of these two, and they all need to use the first person as main and the other in high school. In case of failure, all branches need to use the second connection VPN going the second seat.
In my research, I'm looking for the best possible solution, with faster failover, but have no idea where to start my research.
I hope someone has a good answer for this one.
Thank you very much in advance,
Kind regards
Dwayne
I do not understand why people continue to use ASA devices for VPN endpoint. the ASA is NOT designed for complex VPN scenarios. It is designed for simple scenarios. In terms of VPN by using comparison, ASA is a person with a basic education while Cisco IOS is like a person with a college degree.
For the scenario, you will be much better using Cisco IOS routers everywhere, where you can implement the GRE/IPSec or DMVPN. Both cases will be sastify to your needs.
-
Hello!
We have an old VPN router in our office with VPN tunnels configured in other countries, but it has greatly reduced the speed of the internet connection, we decided to change. Therefore, we bought a RV180 router to replace the old.
I have properly configured the existing tunnels to VPN site-to-site on RV180, this part works fine. But I have a problem with the network address translation. Here are the current settings of the old router:
VPN tunnel settings:
Local network: 192.168.223.160
Local subnet mask: 255.255.255.240
Remote network: 10.10.3.0
Remote subnet mask: 255.255.255.0Source NAT:
Protocol: ALL
Source addr. : NO
Dest. addr. : 10.10.3.0/24
Translation addr. : 192.168.223.161
Outgoing interface: VPNDestination NAT:
Protocol: ALL
Source addr. : NO
Dest. addr. : 192.168.223.161
Translation addr. : 192.168.1.1 (router LAN addr.)
Input interface: VPNProtocol: ALL
Source addr. : NO
Dest. addr. : 192.168.223.162
Translation addr. : 192.168.1.235 (fix a host IP)
Input interface: VPNHow could I implement these settings on the RV180? I only found specific NAT, is not appropriate for us, I think.
As I said, the VPN tunnel works fine, I can access the subnet of 10.10.3.x.
(I don't have access to the other side of the tunnel).
Can someone help me?
Thank you!
Ákos
Hello
Regarding the RV180 router, there is no way to install this type of configuration for the VPN tunnel. As you said, the router supports only the one-to-one NAT.
Can you explain what is the ultimate goal? Maybe we can come up with a workaround.
-
Hello
I have a PIX 501 running V6.3 and already have VPN users destined for the external interface of the pix using the VPNGroup, but I wanted to see if this is possible.
1. I want ti will not only have the name and the password for the vpngroup to allow them access I want to add the prompt for the user ID and password so that they must provide proof of identity valid AD and the password before they can complete the vpn connection. I want to use MS ISA to be able to do. I found the doc were it shows how to authenticate with a local user, but not tie it in the accession of the AD.
2. I would also enable remote ssh rights administrator for the pix of anywhere, is it possible without having an exact IP address? I know of a prospective security that this type of access is not recommended, so if anyone has any suggestions I would be very happy.
Thank you!
Brian
1. of course, it's what you're looking for (http://www.cisco.com/en/US/products/hw/vpndevc/ps2030/products_configuration_example09186a00800b6099.shtml).
Simply add the commands:
vpnaccess AAA-server to the radius Protocol
AAA-server vpnaccess (inside) host x.x.x.x Bonneau
customer of authentication vpnaccess crypto card
This will make all users to authenticate via Radius Server to x.x.x.x, you will have to configure it to work with your AD domain name.
2 SSH access must be opened by IP address, but if you do not know the address the user IP will come, just enter the following to open access to all IP addresses:
SSH 0 0 outside
Of course, this has security implications as you mentioned.
Maybe you are looking for
-
Upgrade hard drive hybrid on m7-1015dx
I want to spend my hard drive on my laptop 1015dx m7. Installing the new hard drive and try to install windows, I get the error saying "Windows Setup could not configure windows to run on the hardware in the computer." According to me, the issue is t
-
When sending an Email containing pictures, I get the Message "one or more of the images could not be transmitted. When I send this message to my address, I see the little red X in place of the image. How can I fix it? original title: Live Mail
-
Research of old English & German letter style/fonts
I'm looking for models from different countries letter syle/fontsThanks for your help joe
-
After removing the virus, I'm more able to send the outgoing signal. The computer says that it cannot open the windows firewall internet connection sharing service. The message is related service is not running. I went into msconfig file and everythi
-
The mouse freezes intermittently
I have the same problem, this is clearly mentioned in the LienSuivant. According to what I do the program in the program, the mouse can freeze in 5 minutes or 2 hours or 6 hours. I tried to check the malicious software and hardware to the lpost below