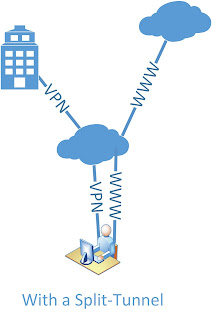
VPN, Internet and a Split Tunnels traffic
Please attached photo because I hope that explains what I really want to do, but here's the break down.
When a VPN Client connects to remote access to 1-ASA5510 I want all Internet traffic to send to 2 - ASA5510 instead of back to the default route. When it comes out 2-ASA5510, it passes through the content filter. 2 - ASA5510 has Split Tunnel put in place and we are trying to do away with Tunnel from SPlit.
I hope this is clear enough.
Any ideas would be helpful
Dan
Dan,
Difficult but doable! First of all, there is a nice feature in the ASA that allows configuration of remote proxy based on VPN profile by: -.
Group Policy <> attributes
use a MSIE-proxy-server method
Internet Explorer-proxy server value x.x.x.x
activate Internet Explorer-proxy local-bypass
Well Yes you guessed it - works only on Microsoft Internet Explorer.
I don't think that any policy based routing would work for you - bad luck.
But you can try another feature - traffic through the tunnel, which is normally used in the topllogy of EasyVPN: -.
Configuration of the ASA at the bottom, I probably would test this with the IP address of the 2651 router!
HTH.
Tags: Cisco Security
Similar Questions
-
Windows - Internet access, no split Tunnel L2TP VPN Clients does not
Greetings!
I have four ASA 5505 that I configured with 4 site to site VPN tunnels (works perfectly) to connect to our company facilities 4. The ASA is also configured with remote access L2TP/IPsec so that a specific group of users of portable computers can connect to and access to all facilities. It also works very well except for one important exception - my split tunnel setting doesn't seem to work, because I can't connect to the Internet outside the VPN resources.
I accept the inherent risk of allowing tunnels to split from a security point of view since I take the necessary steps to secure the systems used for remote access. I would appreciate any feedback on how to get the job of split tunnel.
Here is the configuration:
: Saved
:
ASA Version 1.0000 11
!
SGC hostname
domain somewhere.com
names of
COMMENTS COMMENTS LAN 192.168.2.0 name description
name 75.185.129.13 description of SGC - external INTERNAL ASA
name 172.22.0.0 description of SITE1-LAN Ohio management network
description of SITE2-LAN name 172.23.0.0 Lake Club Network
name 172.24.0.0 description of training3-LAN network Southwood
description of training3 - ASA 123.234.8.124 ASA Southwoods name
INTERNAL name 192.168.10.0 network Local INTERNAL description
description of name 192.168.11.0 INTERNAL - VPN VPN INTERNAL Clients
description of Apollo name 192.168.10.4 INTERNAL domain controller
description of DHD name 192.168.10.2 Access Point #1
description of GDO name 192.168.10.3 Access Point #2
description of Odyssey name 192.168.10.5 INTERNAL Test Server
CMS internal description INTERNAL ASA name 192.168.10.1
name 123.234.8.60 description of SITE1 - ASA ASA management Ohio
description of SITE2 - ASA 123.234.8.189 Lake Club ASA name
description of training3-VOICE name Southwood Voice Network 10.1.0.0
name 172.25.0.0 description of training3-WIFI wireless Southwood
!
interface Vlan1
nameif outside
security-level 0
IP address dhcp setroute
!
interface Vlan2
nameif INSIDE
security-level 100
255.255.255.0 SGC-internal IP address
!
interface Vlan3
nameif COMMENTS
security-level 50
IP 192.168.2.1 255.255.255.0
!
interface Ethernet0/0
Time Warner Cable description
!
interface Ethernet0/1
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/2
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/3
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/4
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/5
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/6
Description for Wireless AP Trunk Port
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
interface Ethernet0/7
Description for Wireless AP Trunk Port
switchport access vlan 2
switchport trunk allowed vlan 2-3
switchport vlan trunk native 2
switchport mode trunk
!
boot system Disk0: / asa821-11 - k8.bin
Disk0: / config.txt boot configuration
passive FTP mode
clock timezone IS - 5
clock to summer time EDT recurring
DNS domain-lookup outside
INTERNAL DNS domain-lookup
DNS domain-lookup GUEST
DNS server-group DefaultDNS
Name-Server 4.2.2.2
domain somewhere.com
permit same-security-traffic inter-interface
permit same-security-traffic intra-interface
DM_INLINE_TCP_1 tcp service object-group
EQ port 3389 object
port-object eq www
EQ object of the https port
EQ smtp port object
the DM_INLINE_NETWORK_1 object-group network
network-object SITE1-LAN 255.255.0.0
network-object SITE2-LAN 255.255.0.0
network-object training3-LAN 255.255.0.0
object-group training3-GLOBAL network
Southwood description Global Network
network-object training3-LAN 255.255.0.0
network-object training3-VOICE 255.255.0.0
network-object training3-WIFI 255.255.0.0
DM_INLINE_TCP_2 tcp service object-group
EQ port 5900 object
EQ object Port 5901
object-group network INTERNAL GLOBAL
Description Global INTERNAL Network
network-object INTERNAL 255.255.255.0
network-object INTERNALLY-VPN 255.255.255.0
access-list outside_access note Pings allow
outside_access list extended access permit icmp any CMS-external host
access-list outside_access note that VNC for Camille
outside_access list extended access permit tcp any host CMS-external object-group DM_INLINE_TCP_2
access-list outside_access note INTERNAL Services
outside_access list extended access permit tcp any host CMS-external object-group DM_INLINE_TCP_1
DefaultRAGroup_splitTunnelAcl list standard access allowed INTERNAL 255.255.255.0
access-list sheep extended ip INTERNAL 255.255.255.0 allow INTERNAL VPN 255.255.255.0
access-list extended sheep allowed ip IN-HOUSE-GLOBAL SITE1-LAN 255.255.0.0 object-group
access-list extended sheep allowed ip IN-HOUSE-GLOBAL SITE2-LAN 255.255.0.0 object-group
access-list extended sheep allowed ip object-IN-HOUSE-GLOBAL object group training3-GLOBAL
access-list INTERNAL-to-SITE1 extended permit ip IN-HOUSE-GLOBAL SITE1-LAN 255.255.0.0 object-group
access-list INTERNAL-to-training3 extended permitted ip object-IN-HOUSE-GLOBAL object group training3-GLOBAL
access-list INTERNAL-to-SITE2 extended permit ip IN-HOUSE-GLOBAL SITE2-LAN 255.255.0.0 object-group
no pager
Enable logging
exploitation forest asdm warnings
Debugging trace record
Outside 1500 MTU
MTU 1500 INTERNAL
MTU 1500 COMMENTS
192.168.11.1 mask - local 192.168.11.25 pool IN-HOUSE VPN IP 255.255.255.0
no failover
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 623.bin
enable ASDM history
ARP timeout 14400
Global 1 interface (outside)
(INTERNAL) NAT 0 access-list sheep
NAT (INTERNAL) 1 0.0.0.0 0.0.0.0
NAT (GUEST) 1 0.0.0.0 0.0.0.0
5900 5900 Camille netmask 255.255.255.255 interface static tcp (GUEST, outdoor)
3389 3389 Apollo netmask 255.255.255.255 interface static tcp (INDOOR, outdoor)
public static tcp (INDOOR, outdoor) interface www Apollo www netmask 255.255.255.255
public static tcp (INDOOR, outdoor) interface https Apollo https netmask 255.255.255.255
public static tcp (INDOOR, outdoor) interface smtp smtp Apollo netmask 255.255.255.255
5901 puppy 5901 netmask 255.255.255.255 interface static tcp (GUEST, outdoor)
Access-group outside_access in interface outside
Timeout xlate 0:05:00
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-registration DfltAccessPolicy
RADIUS protocol AAA-server Apollo
Apollo (INTERNAL) AAA-server Apollo
Timeout 5
key *.
AAA authentication enable LOCAL console
the ssh LOCAL console AAA authentication
AAA authentication LOCAL telnet console
AAA authentication http LOCAL console
Enable http server
http 0.0.0.0 0.0.0.0 INTERNAL
http 0.0.0.0 0.0.0.0 COMMENTS
No snmp server location
No snmp Server contact
Community SNMP-server
Server enable SNMP traps snmp authentication linkup, linkdown cold start
Crypto ipsec transform-set ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ESP-DES-MD5 esp - esp-md5-hmac
Crypto ipsec transform-set ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ESP-AES-256-SHA 256 - aes - esp esp-sha-hmac
Crypto ipsec transform-set ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec transform-set esp-3des esp-sha-hmac TRANS_ESP_3DES_SHA
Crypto ipsec transform-set transit mode TRANS_ESP_3DES_SHA
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
life crypto ipsec security association seconds 28800
Crypto ipsec kilobytes of life - safety 4608000 association
SYSTEM_DEFAULT_CRYPTO_MAP game 65535 dynamic-map crypto transform-set ESP-3DES-SHA TRANS_ESP_3DES_SHA
correspondence address 1 card crypto outside_map INTERNAL SITE1
card crypto outside_map 1 set of peer SITE1 - ASA
card crypto outside_map 1 set of transformation-ESP-3DES-SHA
address for correspondence card crypto outside_map 2 INTERNAL training3
outside_map 2 peer training3 - ASA crypto card game
card crypto outside_map 2 game of transformation-ESP-3DES-SHA
address for correspondence outside_map 3 card crypto INTERNAL SITE2
game card crypto outside_map 3 peers SITE2 - ASA
card crypto outside_map 3 game of transformation-ESP-3DES-SHA
outside_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
outside_map interface card crypto outside
crypto ISAKMP allow outside
crypto ISAKMP policy 10
preshared authentication
3des encryption
sha hash
Group 2
life 86400
delimiter group @.
Telnet training3 - ASA 255.255.255.255 outside
Telnet SITE2 - ASA 255.255.255.255 outside
Telnet SITE1 - ASA 255.255.255.255 outside
Telnet 0.0.0.0 0.0.0.0 INTERNAL
Telnet 0.0.0.0 0.0.0.0 COMMENTS
Telnet timeout 60
SSH enable ibou
SSH training3 - ASA 255.255.255.255 outside
SSH SITE2 - ASA 255.255.255.255 outside
SSH SITE1 - ASA 255.255.255.255 outside
SSH 0.0.0.0 0.0.0.0 INTERNAL
SSH 0.0.0.0 0.0.0.0 COMMENTS
SSH timeout 60
Console timeout 0
access to the INTERNAL administration
Hello to tunnel L2TP 100
interface ID client DHCP-client to the outside
dhcpd dns 4.2.2.1 4.2.2.2
dhcpd ping_timeout 750
dhcpd outside auto_config
!
address INTERNAL 192.168.10.100 dhcpd - 192.168.10.200
dhcpd Apollo Odyssey interface INTERNAL dns
dhcpd somewhere.com domain INTERNAL interface
interface of dhcpd option 150 ip 10.1.1.40 INTERNAL
enable dhcpd INTERNAL
!
dhcpd address 192.168.2.100 - 192.168.2.200 COMMENTS
dhcpd dns 4.2.2.1 4.2.2.2 interface COMMENTS
enable dhcpd COMMENTS
!a basic threat threat detection
statistical threat detection port
Statistical threat detection Protocol
Statistics-list of access threat detection
a statistical threat detection tcp-interception rate-interval 30 burst-400-rate average rate 200
NTP server 192.43.244.18 prefer external source
WebVPN
allow outside
CSD image disk0:/securedesktop-asa-3.4.2048.pkg
SVC disk0:/sslclient-win-1.1.4.179.pkg 1 image
SVC disk0:/anyconnect-win-2.4.1012-k9.pkg 2 image
enable SVC
Group Policy DefaultRAGroup INTERNAL
attributes of Group Policy DefaultRAGroup
Server DNS 192.168.10.4 value
Protocol-tunnel-VPN l2tp ipsec
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list DefaultRAGroup_splitTunnelAcl
value by default-domain somewhere.com
Group Policy DefaultWEBVPNGroup INTERNAL
attributes of Group Policy DefaultWEBVPNGroup
VPN-tunnel-Protocol webvpn
Group Policy DefaultL2LGroup INTERNAL
attributes of Group Policy DefaultL2LGroup
Protocol-tunnel-VPN IPSec l2tp ipsec
Group Policy DefaultACVPNGroup INTERNAL
attributes of Group Policy DefaultACVPNGroup
VPN-tunnel-Protocol svc
attributes of Group Policy DfltGrpPolicy
value of 192.168.10.4 DNS Server 4.2.2.2
VPN - 25 simultaneous connections
VPN-idle-timeout no
Protocol-tunnel-VPN IPSec
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list DefaultRAGroup_splitTunnelAcl
value by default-domain somewhere.com
the value INTERNAL VPN address pools
chip-removal-disconnect disable card
WebVPN
SVC keepalive no
client of dpd-interval SVC no
dpd-interval SVC bridge no
value of customization DfltCustomization
attributes global-tunnel-group DefaultRAGroup
VPN INTERNAL address pool
Group Policy - by default-DefaultRAGroup
IPSec-attributes tunnel-group DefaultRAGroup
pre-shared-key *.
Disable ISAKMP keepalive
tunnel-group DefaultRAGroup ppp-attributes
No chap authentication
no authentication ms-chap-v1
ms-chap-v2 authentication
attributes global-tunnel-group DefaultWEBVPNGroup
VPN INTERNAL address pool
Group Policy - by default-DefaultWEBVPNGroup
tunnel-group 123.234.8.60 type ipsec-l2l
IPSec-attributes tunnel-group 123.234.8.60
pre-shared-key *.
tunnel-group 123.234.8.124 type ipsec-l2l
IPSec-attributes tunnel-group 123.234.8.124
pre-shared-key *.
tunnel-group 123.234.8.189 type ipsec-l2l
IPSec-attributes tunnel-group 123.234.8.189
pre-shared-key *.
type tunnel-group DefaultACVPNGroup remote access
attributes global-tunnel-group DefaultACVPNGroup
VPN INTERNAL address pool
Group Policy - by default-DefaultACVPNGroup
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the netbios
inspect the rsh
inspect the rtsp
inspect the skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect the tftp
inspect the sip
inspect xdmcp
inspect the http
inspect the they
!
global service-policy global_policy
context of prompt hostname
Cryptochecksum:423c807c0d63cb3e9aeceda977053f84
: end
ASDM image disk0: / asdm - 623.bin
ASDM location Camille 255.255.255.255 INTERNAL
ASDM location INTERNAL CGT-external 255.255.255.255
ASDM location INTERNAL SITE1-LAN 255.255.0.0
ASDM location INTERNAL SITE2-LAN 255.255.0.0
ASDM location INTERNAL training3-LAN 255.255.0.0
ASDM location INTERNAL training3 - ASA 255.255.255.255
ASDM location INTERNAL GDO 255.255.255.255
ASDM location INTERNAL SITE1 - ASA 255.255.255.255
ASDM location INTERNAL SITE2 - ASA 255.255.255.255
ASDM location INTERNAL training3-VOICE 255.255.0.0
ASDM location puppy 255.255.255.255 INTERNAL
enable ASDM historyI should also mention that my test clients are a combination of Windows XP, Windows 7, and Windows Mobile. Other that in specifying the preshared key and forcing L2TP/IPsec on the client side, the VPN settings on clients are the default settings with the help of MS-CHAP/MS-CHAPv2.
You must configure * intercept-dhcp enable * in your group strategy:
attributes of Group Policy DefaultRAGroup
attributes of Group Policy DefaultRAGroup
Server DNS 192.168.10.4 value
Protocol-tunnel-VPN l2tp ipsec
Split-tunnel-policy tunnelspecified
value of Split-tunnel-network-list DefaultRAGroup_splitTunnelAcl
value by default-domain somewhere.comIntercept-dhcp enable
-Latptop VPN clients (which I assume are on windows computers) is also the * use on remote network default gateway * box unchecked. It is located on the Advanced tab of VPN client TCP/IP properties. Select Client VPN > properties > Networking > TCP/IP Internet Protocol > properties > advanced and uncheck the box.
Alex
-
Internet access without split tunneling VPN PIX
I have a PIX 515E with code 6.31. I installed a VPN to allow access to the internal network from the Internet using the Cisco VPN client. It does not work properly. We have some sellers who demand that we come from our Internet IP range to allow us access to their database on the Internet. This works very well for our internal users, but I will allow users VPN for this also.
Is there a way to allow the user from the VPN client to use the Internet for business access to the internet instead of use the split tunneling to access the internet through their own connection? I would like users to vpn to be NAT would have réécrirait Internet and seeming come from our pool of Internet addresses. What I found references by using the split tunneling, but this won't work for me. Am I stuck getting a VPN concentrator to achieve?
Thank you
Josh
The PIX cannot route a package back on the same interface, he entered the, which includes a customer entering the interface external and routed VPN package back on the same interface.
A router or a VPN concentrator would be able to do this, but not a PIX, sorry.
-
Cisco easy VPN access Internet without Split Tunnel
Hey guys
IM wondering if anyone has a config that can help me get access to internet via an easy vpn tunnel on a cisco 877 router.
Basically, we are traveling to be users able to use the internet through vpn, rather than using split tunneling. The reason for this is that we have several sites that are attached by lists of external IP access for some services.
We hope that mobile users to interact with these sites through the central router and use external IP of access routers secure sites.
I hope that makes sense. I know that we can use a proxy but we also use other services of bases no proxy on these sites, it would be rather routed direct access.
Thank you
Luke
Hi Luke,.
Please use the installation of the client VPN (complete tunnel) link below.
Note the useful message.
Thank you
Kasi
-
The remote VPN Clients and Internet access
I apologize in advance if this question has already been addressed. I am currently using a PIX Firewall Version 6.1 520 (2) running. I have several remote users that VPN for the PIX. Once the VPN tunnel is started, they are more able to connect to internet from their local computers. Is there a configuation on the PIX that allows remote users to have access to the internet when you are connected to the PIX.
TIA,
Jeff Gulick
The Pix does not allow traffic enter and exit on the same interface. Therefore, a VPN user cannot access the Internet through the tunnel. If you use the Cisco client, enable tunneling split so that all traffic through the tunnel.
If you use PPTP, you can turn off the option that makes the remote network, the default gateway. However, local routes should be added to these clients when they connect.
Or you can use an additional interface on the firewall. One that puts an end to VPN tunnels and another providing for Internet connectivity. In this way the traffic is not enter/leave on the same interface.
Of course, it is preferable if the customer Internet traffic does not go through the tunnel. It wastes your bandwidth and has security problems as well. I suggest you use the client to Cisco and the split tunneling.
-
Press L2L VPN, IPSEC, and L2TP PIX connections
Hi all
I'm trying to implement a solution on my FW PIX (pix804 - 24.bin) to be able to support a VPN L2L session with VPN dynamic user sessions where clients will use a mix of IPSEC(Nat detection) and L2TP. We have always supported things IPSEC and that worked great for many years. I'm now trying to Add L2TP support, so that I can support Android phones/ipads, etc. as well as Windows with built in VPN l2tp clients clients. Everything works well except for the new features of L2TP. Allows you to complete one phase but then tries to use the card encryption that is used for the VPN L2L. It seems to fail because IP addresses are not in the configured ACL to the crypto-map L2L. Does anyone know if there are any questions all these configurations support both. And if not can you see what I have wrong here, which would make it not work. Here are the relevant training:
C515 - A # sh run crypto
Crypto ipsec transform-set esp-SHA-ESP-3DES-3des esp-sha-hmac
Crypto ipsec transform-set ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set of society-ras-esp-3des esp-md5-hmac
Crypto ipsec transform-set ESP-DES-MD5 esp - esp-md5-hmac
Crypto ipsec transform-set esp-3des esp-sha-hmac company-l2tp
life crypto ipsec security association seconds 28800
Crypto ipsec kilobytes of life - safety 4608000 association
Dynamic crypto map company-ras 1 correspondence address company-dynamic
company Dynamics-card crypto-ras 1 set pfs
Dynamic crypto map company-ras 1 transform-set ESP-SHA-3DES ESP-3DES-MD5 company-ras
Dynamic crypto map company-ras 1 lifetime of security association set seconds 28800
company Dynamics-card crypto-ras 1 kilobytes of life together - the association of safety 4608000
crypto dynamic-map-ras company 2 address company-dynamic game
crypto dynamic-map company-ras 2 transform-set of society-l2tp
crypto dynamic-map company-ras 2 set security association lifetime seconds 28800
company Dynamics-card crypto-ras 2 kilobytes of life together - the association of safety 4608000
card crypto company-map 1 correspondence address company-colo
card crypto company-card 1 set pfs
card crypto company-card 1 set counterpart colo-pix-ext
card crypto card company 1 value transform-set ESP-3DES-MD5 SHA-ESP-3DES
company-map 1 lifetime of security association set seconds 28800 crypto
card company-card 1 set security-association life crypto kilobytes 4608000
company-card 1 set nat-t-disable crypto card
company-card 2 card crypto ipsec-isakmp dynamic company-ras
business-card interface card crypto outside
crypto isakmp identity address
crypto ISAKMP allow outsideCrypto isakmp nat-traversal 3600
crypto ISAKMP policy 1
preshared authentication
3des encryption
sha hash
Group 2
life 86400
crypto ISAKMP policy 2
preshared authentication
3des encryption
md5 hash
Group 2
life 86400
C515 - A # sh run tunnel-group
attributes global-tunnel-group DefaultRAGroup
company-ras address pool
Group-LOCAL radius authentication server
Group Policy - by default-l2tp
IPSec-attributes tunnel-group DefaultRAGroup
pre-shared-key *.
tunnel-group DefaultRAGroup ppp-attributes
PAP Authentication
No chap authentication
ms-chap-v2 authentication
eap-proxy authentication
type tunnel-group company-ras remote access
tunnel-group global company-ras-attributes
company-ras address pool
Group-LOCAL radius authentication server
tunnel-group company-ras ipsec-attributes
pre-shared-key *.
type tunnel-group company-admin remote access
attributes global-tunnel-group company-admin
company-admin address pool
Group-LOCAL radius authentication server
company strategy-group-by default-admin
IPSec-attributes of tunnel-group company-admin
pre-shared-key *.
PPP-attributes of tunnel-group company-admin
No chap authentication
ms-chap-v2 authentication
tunnel-group x.x.x.x type ipsec-l2l
tunnel-group ipsec-attributes x.x.x.x
pre-shared-key *.
ISAKMP keepalive retry threshold 15 10
C515 - A # sh run Group Policy
attributes of Group Policy DfltGrpPolicy
Server DNS 10.10.10.20 value 10.10.10.21
Protocol-tunnel-VPN IPSec
enable PFS
Split-tunnel-policy tunnelspecified
Split-tunnel-network-list value company-SPLIT-TUNNEL-ACL
company.int value by default-field
NAC-parameters DfltGrpPolicy-NAC-framework-create value
internal strategy of company-admin group
attributes of the strategy of company-admin group
WINS server no
DHCP-network-scope no
VPN-access-hour no
VPN - 20 simultaneous connections
VPN-idle-timeout 30
VPN-session-timeout no
Protocol-tunnel-VPN IPSec l2tp ipsec
disable the IP-comp
Re-xauth disable
Group-lock no
enable PFS
Split-tunnel-network-list value company-ADMIN-SPLIT-TUNNEL-ACL
L2TP strategy of Group internal
Group l2tp policy attributes
Server DNS 10.10.10.20 value 10.10.10.21
Protocol-tunnel-VPN l2tp ipsec
disable the PFS
Split-tunnel-policy tunnelall
company.int value by default-field
NAC-parameters DfltGrpPolicy-NAC-framework-create valueRelevant debug output
C515 - Has # Sep 03 02:09:33 [IKEv1 DEBUG]: IP = 66.25.14.195, Oakley proposal is acceptable
Sep 03 02:09:33 [IKEv1 DEBUG]: IP = 66.25.14.195, IKE Peer included IKE fragmentation capability flags: Main Mode: real aggressive Mode: false
Sep 03 02:09:33 [IKEv1 DEBUG]: IP = 66.25.14.195, IKE SA proposal # 1, turn # 1 entry IKE acceptable Matches # 3 overall
Sep 03 02:09:33 [IKEv1]: IP = 66.25.14.195, connection landed on tunnel_group DefaultRAGroup
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, status of automatic NAT detection: remote endpoint IS behind a NAT device this end is NOT behind a NAT device
Sep 03 02:09:33 [IKEv1]: IP = 66.25.14.195, connection landed on tunnel_group DefaultRAGroup
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, previously allocated memory of liberation for permission-dn-attributes
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, PHASE 1 COMPLETED
Sep 03 02:09:33 [IKEv1]: IP = 66.25.14.195, for this connection Keep-alive type: None
Sep 03 02:09:33 [IKEv1]: IP = 66.25.14.195, Keep-alives configured on, but the peer does not support persistent (type = None)
Sep 03 02:09:33 [IKEv1 DEBUG]: Group = DefaultRAGroup, IP = 66.25.14.195, timer to generate a new key to start P1: 21600 seconds.
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, data received in payload ID remote Proxy Host: address 172.16.0.104 17 of the Protocol, Port 0
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, data received in payload ID local Proxy Host: address x.x.x.x, 17 of the Protocol, Port 1701
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, detected L2TP/IPSec session.
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, QM IsRekeyed its not found old addr
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, static check card Crypto, check card company card, seq = 1 =...
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, static check card Crypto card = company-map, seq = 1, ACL does not proxy IDs src:66.25.14.195 dst: x.x.x.x
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, tunnel IPSec rejecting: no entry for crypto for proxy card proxy remote 66.25.14.195/255.255.255.255/17/0 local x.x.x.x/255.255.255.255/17/1701 on the outside interface
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, error QM WSF (P2 struct & 0x501c1f0, mess id 0xa181b866).
Sep 03 02:09:33 [IKEv1 DEBUG]: Group = DefaultRAGroup, IP = 66.25.14.195, case of mistaken IKE responder QM WSF (struct & 0x501c1f0), : QM_DONE EV_ERROR--> QM_BLD_MSG2 EV_NEGO_SA--> QM_BLD_MSG2, EV_IS_REKEY--> QM_BLD_MSG2, EV_CONFIRM_SA--> QM_BLD_MSG2, EV_PROC_MSG--> QM_BLD_MSG2, EV_HASH_OK--> QM_BLD_MSG2, NullEvent--> QM_BLD_MSG2, EV_COMP_HASH
Sep 03 02:09:33 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, peer table correlator Removing failed, no match!
Sep 03 02:09:33 [IKEv1]: ignoring msg SA brand with Iddm 204910592 dead because ITS removal
Sep 03 02:10:05 [IKEv1 DEBUG]: IP = 66.25.14.195, Oakley proposal is acceptable
Sep 03 02:10:05 [IKEv1 DEBUG]: IP = 66.25.14.195, IKE Peer included IKE fragmentation capability flags: Main Mode: real aggressive Mode: false
Sep 03 02:10:05 [IKEv1 DEBUG]: IP = 66.25.14.195, IKE SA proposal # 1, turn # 1 entry IKE acceptable Matches # 3 overall
Sep 03 02:10:05 [IKEv1]: IP = 66.25.14.195, connection landed on tunnel_group DefaultRAGroup
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, status of automatic NAT detection: remote endpoint IS behind a NAT device this end is NOT behind a NAT device
Sep 03 02:10:05 [IKEv1]: IP = 66.25.14.195, connection landed on tunnel_group DefaultRAGroup
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, previously allocated memory of liberation for permission-dn-attributes
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, PHASE 1 COMPLETED
Sep 03 02:10:05 [IKEv1]: IP = 66.25.14.195, for this connection Keep-alive type: None
Sep 03 02:10:05 [IKEv1]: IP = 66.25.14.195, Keep-alives configured on, but the peer does not support persistent (type = None)
Sep 03 02:10:05 [IKEv1 DEBUG]: Group = DefaultRAGroup, IP = 66.25.14.195, timer to generate a new key to start P1: 21600 seconds.
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, data received in payload ID remote Proxy Host: address 172.16.0.104 17 of the Protocol, Port 0
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, data received in payload ID local Proxy Host: address x.x.x.x, 17 of the Protocol, Port 1701
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, detected L2TP/IPSec session.
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, QM IsRekeyed its not found old addr
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, static check card Crypto, check card company card, seq = 1 =...
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, static check card Crypto card = company-map, seq = 1, ACL does not proxy IDs src:66.25.14.195 dst: x.x.x.x
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, tunnel IPSec rejecting: no entry for crypto for proxy card proxy remote 66.25.14.195/255.255.255.255/17/0 local x.x.x.x/255.255.255.255/17/1701 on the outside interface
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, error QM WSF (P2 struct & 0x501c1f0, mess id 0xa5db9562).
Sep 03 02:10:05 [IKEv1 DEBUG]: Group = DefaultRAGroup, IP = 66.25.14.195, case of mistaken IKE responder QM WSF (struct & 0x501c1f0), : QM_DONE EV_ERROR--> QM_BLD_MSG2 EV_NEGO_SA--> QM_BLD_MSG2, EV_IS_REKEY--> QM_BLD_MSG2, EV_CONFIRM_SA--> QM_BLD_MSG2, EV_PROC_MSG--> QM_BLD_MSG2, EV_HASH_OK--> QM_BLD_MSG2, NullEvent--> QM_BLD_MSG2, EV_COMP_HASH
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, peer table correlator Removing failed, no match!
Sep 03 02:10:05 [IKEv1]: ignoring msg SA brand with Iddm 204914688 dead because ITS removalThe outputs of two debugging who worry are the following:
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, data received in payload ID remote Proxy Host: address 172.16.0.104 17 of the Protocol, Port 0
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, data received in payload ID local Proxy Host: address x.x.x.x, 17 of the Protocol, Port 1701Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, static check card Crypto, check card company card, seq = 1 =...
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, static check card Crypto card = company-map, seq = 1, ACL does not proxy IDs src:66.25.14.195 dst: x.x.x.x
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, tunnel IPSec rejecting: no entry for crypto for proxy card proxy remote 66.25.14.195/255.255.255.255/17/0 local x.x.x.x/255.255.255.255/17/1701 on the outside interface
Sep 03 02:10:05 [IKEv1]: Group = DefaultRAGroup, IP = 66.25.14.195, error QM WSF (P2 struct & 0x501c1f0, mess id 0xa5db9562).This seems to indicate that his NAT detection but then do not assign to the entry card cryptography because networks are encrypted are not in the configured ACL that is true. He needs to use dynamic input and it doesn't seem to be.
I need to create another dynamic map entry to make it work instead of add lines to the same dynamic with a lower (higher) priority map entry?
Thanks in advance for any help here.
Hello
That won't do the trick, l2tp clients are picky kindda, so you know if they do not hit the correct strategy first they just stop trying. Follow these steps:
correspondence from the company of dynamic-map crypto-ras 1 address company-dynamic
No crypto-card set pfs dynamic company-ras 1
No crypto dynamic-map company-ras-1 transform-set ESP-SHA-3DES ESP-3DES-MD5 company-ras
Dynamic crypto map company-ras 1 transform-set company-l2tp SHA-ESP-3DES ESP-3DES-MD5 company-ras
The foregoing will not affect existing customers of IPsec at all, these clients will not use the statement of pfs and will link even if the correspondence address is not configured (it is optional), besides Cisco IPsec clients will be affected first the mode of transport policy and fail however they will continue to try and hit another police PH2.
Regarding your last question, I was referring specifically to the support of l2tp for android, and Yes, you will need to run one of these versions.
http://www.Cisco.com/en/us/docs/security/ASA/asa82/release/notes/asarn82.html#wp431562
Tavo-
-
Tunnel VPN remote Internet and VPN remote VPN from Site to Site traffic?
Hello
We try to remote traffic from our users VPN tunnel through our ASA 5510 as well as to allow the only access for remote user VPN traffic to the other end of the all our VPN site-to-site connected to the same ASA. Basically, we who want to VPN in the network in order to access all of our networks business. We try to get away with this without using split Tunneling.
I can currently get internal traffic from the remote user VPN to reach all other vpn site-to-site tunnels without the internet in tunnel. The problem is when I add the following statement to the NAT:
NAT (outside) 1 10.10.19.0 255.255.255.0 * 10.10.19.0 is the address of the remote VPN Client
Internet traffic to the remote VPN starts to get in the tunnel, but I lose the opportunity to reach one of the other tunnels from site to site by the remote VPN tunnel.
I also begin to receive the following errors in the journal of the ASA
3 July 1, 2009 12:34:18 305005 10.10.19.255 137 no group of translation not found for udp src outside:10.10.19.3/137 dst outside:10.10.19.255/137
Any help with how NAT statements must be defined for this work would be appreciated.
Thank you
Will be
Will,
the link of this post for your scenario of vpn hub & speak reference, you problem may be on exempt nat rules.
Have a second look at your sheep rules.
Be sure to eliminate tunnel rules related to rheumatoid arthritis, as appropriate, to not let him get in the way of splitting.
If always emits discribe topology for l2ls and info logic RA and sanatized hub config asa... but I think if you look at the thread above, you should be able to solve.
Concerning
-
Problems with basic setup and split tunneling VPN
I created a SSL VPN in an ASA CISCO ASDM 6.6 8.6 running.
IM able to connect to the VPN and reach all the devices with the LAN but I am not able to browse the web. When I activate the tunnel split Im able to browse the web, but then Im not able to reach any internal device.
Here is part of the show's run:network of the RedInterna object
150.211.101.0 subnet 255.255.255.0
Description Red Interna
network of the NETWORK_OBJ_10.4.1.0_28 object
subnet 10.4.1.0 255.255.255.240
inside_access_in list extended access permitted ip object RedInterna all
Standard access list VPN_INTERNET allow 150.211.101.0 255.255.255.0
pager lines 24
Enable logging
asdm of logging of information
Outside 1500 MTU
Within 1500 MTU
management of MTU 1500
local pool VPN_POOL 10.4.1.1 - 10.4.1.14 255.255.255.240 IP mask
failover
secondary failover lan unit
failover lan interface GigabitEthernet0 fail-1/2
key changeover *.
failover interface ip fail-1 10.3.1.21 255.255.255.252 watch 10.3.1.22
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 66114.bin
enable ASDM history
ARP timeout 14400
NAT (inside, outside) static source any any static destination NETWORK_OBJ_10.4.1.0_28 NETWORK_OBJ_10.4.1.0_28 non-proxy-arp-search to itinerary
!
NAT source auto after (indoor, outdoor) dynamic one interface
inside_access_in access to the interface inside group
Route outside 0.0.0.0 0.0.0.0 187.217.68.145 1
Route inside 10.0.0.0 255.0.0.0 10.1.1.78 1
Route inside 150.211.0.0 255.255.0.0 10.1.1.78 1WebVPN
allow outside
AnyConnect image disk0:/anyconnect-win-3.1.00495-k9.pkg 1
AnyConnect enable
tunnel-group-list activate
internal GroupPolicy_VPN_ group strategy
attributes of Group Policy GroupPolicy_VPN_
WINS server no
value of server DNS 8.8.8.8
client ssl-VPN-tunnel-Protocol
dominio.com.MX value by default-field
type tunnel-group VPN_ remote access
attributes global-tunnel-group VPN_
address VPN_POOL pool
Group Policy - by default-GroupPolicy_VPN_
tunnel-group VPN_ webvpn-attributes
enable VPN_ group-alias
!I m don't know if Im missing a few small details or Setup. Any help will be much appreciated.
Thank you!!!Hello
When you use full VPN Tunnel (which is the default setting), you will have a number of things that you need to configure on the SAA.
First, the ASA by default will not allow traffic to enter via an interface and then exit through the same interface. It is essentially, what happens when the customer VPN traffic comes to the ASA and then heads on the Internet. In your case the traffic goes through the 'outside' and leaves via the 'outside' interface.
You will need this command
permit same-security-traffic intra-interface
You can check if their licence at the moment with the command
See the race same-security-traffic
Second, VPN users will need to have the NAT configuration like all users LAN behind the ASA real. So you basically configure dynamic PAT for 'outside' to 'outside' traffic
You can get there with the following configuration
network of the VPN-PAT object
subnet 10.4.1.0 255.255.255.240
dynamic NAT interface (outdoors, outdoor)
I suppose it should do for you to be able to connect to the Internet and the LAN when the VPN is active.
Hope this helps
Let me know how it goes.
-Jouni
-
Internet access with VPN Client to ASA and full effect tunnel
I'm trying to migrate our concentrator at our new 5520 s ASA. The concentrator has been used only for VPN Client connections, and I have not the easiest road. However, I, for some reason, can't access to internet through our business network when I've got profiles with lots of tunneling.
I've included the configuration file, with many public IP information and omitted site-to-site tunnels. I left all the relevant stuff on tunnel-groups and group strategies concerning connectivity of VPN clients. The range of addresses that I use for VPN clients is 172.16.254.0/24. The group, with what I'm trying to access the internet "adsmgt" and the complete tunnel to our network part is fine.
As always, any help is appreciated. Thank you!
Hüseyin... good to see you come back.. bud, yes try these Hüseyin sugesstiong... If we looked to be ok, we'll try a different approach...
IM thinking too, because complete tunnel is (no separation) Jim ASA has to go back for the outbound traffic from the internet, a permit same-security-traffic intra-interface, instruction should be able to do it... but Jim start by Hüseyin suggestions.
Rgds
Jorge
-
Help: Customer Cisco VPN & Split Tunnel but not Internet
Hi Forum.
We are faced with this problem: after having successfully open a VPN connection with the Cisco VPN Client to a router Cisco, the rest of the world are not properly available more.
This is what has been verified / so far attempted to identify the problem on a Windows Vista computer:
-Router: Split Tunneling is allowed according to sysop
-On the VPN-Client: "allow Local Lan access" is checked
-On the Client (statistics): only STI VPN-rout configured listed unter "guarantee routes." "Local Lan routes" is empty.
-Calling 'http://www.google.com' in IE fails
-Call ' 74.125.232.116' (IE IP) IE works / ping the IP works.
-nslookup properly lists the current DNS server
-nslookup www.google.com resolves correctly the name of intellectual property
It seems that it is not that the connection with the rest of the Internet is deleted, but DNS resolution fails somehow, even though all signs point to the appropriate DNS server is in force and although the command line can resolve the name.
does anyone have a tip how to debug this correctly?
No worries Pat...
Sent by Cisco Support technique iPhone App
-Please evaluate solutions
-
Access remote VPN, no split tunneling, internet access. Translation NAT problem
Hi all, I'm new to the forum. I have a Cisco ASA 5505 with confusing (to me) question NAT.
Unique external IP (outside interface) with several translations of NAT static object to allow the redirection of port of various internal devices. The configuration worked smoothly during the past years.
Recently, I configured a without the split tunneling VPN remote access and access to the internet and noticed yesterday that my port forwarding has stopped working.
I reviewed the new rules for the VPN NAT and found the culprit.
I've been reviewing the rules again and again, and all I can think about and interpret it, I don't know how this rule affects the port forwarding on the device or how to fix.
Here's the NAT rules, I have in place: ('inactive' rule is the culprit. Once I have turn on this rule, the port forwarding hits a wall)
NAT (inside, outside) static source any any static destination VPN_Subnet VPN_Subnet non-proxy-arp-search to itinerary
NAT (outside, outside) static source VPN_Subnet VPN_Subnet VPN_Subnet VPN_Subnet non-proxy-arp-search of route static destination
NAT (outside, outside) source VPN_Subnet dynamic interface inactive
!
network obj_any object
NAT dynamic interface (indoor, outdoor)
network of the XXX_HTTP object
NAT (inside, outside) interface static tcp www www service
Access-group outside_access_in in interface outside
Route outside 0.0.0.0 0.0.0.0 xxx.xxx.xxx.xxx 1Any help would be appreciated.
Try changing the nat rule to VPN_Subnet interface of nat (outside, outside) the after-service automatic dynamic source
With respect,
Safwan
-
Unable to connect to the internet and VPN in the network.
I have an ADSL account and when I vpn in our network using cisco VPN 3015 vpn client can't access the internet more locally. I have to use our internal proxy server on the network. Is it possible to make the vpn tunnel but also use the local internet DSL for browsing connection?
You must set up split tunnelling tunnel, while only some packets are sent through the tunnel, the rest get out in clear packages just as usual.
In 3015, create a list of network under Config - Mgmt policy - traffic Mgmt - list networks, this list includes your internal networks (you want to be dug traffic). Then go under the group to which the client connects to, on the Client configuration tab, select only the network of tunnels in the list, and then select your list from the drop-down list box. Reconnect and're you good to go.
Keep in the spirit of split-mining is considered a bit of a security risk because your PC is now accessible from the Internet AND you have a VPN directly in your internal network. If someone can take possession of your PC, then they have access to everything. You can also watch in allowing both client firewall stuff.
-
Easy VPN between two ASA 9.5 - Split tunnel does not
Hi guys,.
We have set up a site to site vpn using easy configuration vpn between ver 9.5 race (1) two ASA. The tunnels are up and ping is reached between sites. I also configured split tunnel for internet traffic under the overall strategy of the ASA easy vpn server. But for some unknown reason all the customer same internet traffic is sent to the primary site. I have configured NAT to relieve on the side of server and client-side. Please advise if no limitation so that the installation program.
Thank you and best regards,
Arjun T P
I have the same question and open a support case.
It's a bug in the software 9.5.1. See the bug: CSCuw22886
-
Hello everyone
I have setup a VPN connection, which I can connect to. For all customers of connection, I want to give them an IP (from a subnet maybe) and let them use this IP address for all that they do.
Therefore, this:
and not current:
My inside is 192.168.1.0
My VPN IP pool is 192.168.30.5 - 200
My server (DNS, files, Web site) is 192.168.1.222Here's my setup. I scored what I thought might have something to do with it:
ASA Version 9.2 (1)
!
ciscoasa hostname
activate 8Ry2YjIyt7RRXU24 encrypted password
volatile xlate deny tcp any4 any4
volatile xlate deny tcp any4 any6
volatile xlate deny tcp any6 any4
volatile xlate deny tcp any6 any6
volatile xlate deny udp any4 any4 eq field
volatile xlate deny udp any4 any6 eq field
volatile xlate deny udp any6 any4 eq field
volatile xlate deny udp any6 any6 eq field
2KFQnbNIdI.2KYOU encrypted passwd
names of
pool of IP local IP-pool 192.168.30.5 - 192.168.30.200 mask 255.255.255.0
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
IP 192.168.1.253 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
IP address dhcp setroute
!
boot system Disk0: / asa921 - k8.bin
passive FTP mode
permit same-security-traffic intra-interface
network obj_any object
subnet 0.0.0.0 0.0.0.0
network of the object Server-25
Home 192.168.1.222
Description of the test server
network of the object server-80
Home 192.168.1.222
Description of the test server
network of the object server-443
Home 192.168.1.222
Description of the test server
network of the object server-2525
Home 192.168.1.222
Description of the test server
network of the object server-993
Home 192.168.1.222
Description of the test server
network of the object server-6001
Home 192.168.1.222
Description of the test server
network of the object server-6002
Home 192.168.1.222
Description of the test server
network of the object server-6003
Home 192.168.1.222
Description of the test server
network of the object server-6004
Home 192.168.1.222
Description of the test server
network of the VPN HOST object
192.168.30.0 subnet 255.255.255.0
the object to the Interior-net network
host 192.168.1.0
the VPN server object network
Home 192.168.1.222
outside_access_in list extended access permit tcp any object Server-25 eq smtp
outside_access_in list extended access permit tcp any object server-2525 2525 eq
outside_access_in list extended access permit tcp any object server-80 eq www
outside_access_in list extended access permit tcp any object server-443 https eq
outside_access_in list extended access permit tcp any object server-993 993 eq
outside_access_in list extended access permit tcp any object server-6001 eq 6001
outside_access_in list extended access permit tcp any object server-6002 6002 eq
outside_access_in list extended access permit tcp any object server-6003 eq 6003
outside_access_in list extended access permit tcp any object server-6004 eq 6004
outside_access_in to access ip 192.168.1.0 scope list allow 255.255.255.0 192.168.30.0 255.255.255.0
permit access-list Split-Tunnel-ACL standard 192.168.30.0 255.255.255.0
no pager
Enable logging
asdm of logging of information
Within 1500 MTU
Outside 1500 MTU
ICMP unreachable rate-limit 1 burst-size 1
ASDM image disk0: / asdm - 721.bin
don't allow no asdm history
ARP timeout 14400
no permit-nonconnected arp
NAT (indoor, outdoor) Interior-net Interior-NET static source static destination HOST-VPN-VPN-HOST
NAT VPN VPN-server destination (indoor, outdoor) static static source HOST-VPN-VPN-HOST
!
network obj_any object
NAT dynamic interface (indoor, outdoor)
network of the object Server-25
NAT (inside, outside) interface static tcp smtp smtp service
network of the object server-80
NAT (inside, outside) interface static tcp www www service
network of the object server-443
NAT (inside, outside) interface static tcp https https service
network of the object server-2525
NAT (inside, outside) interface static 2525 2525 tcp service
network of the object server-993
NAT (inside, outside) interface static tcp 993 993 service
network of the object server-6001
NAT (inside, outside) interface static tcp 6001 6001 service
network of the object server-6002
NAT (inside, outside) interface static tcp 6002 6002 service
network of the object server-6003
NAT (inside, outside) interface static 6003 6003 tcp service
network of the object server-6004
NAT (inside, outside) interface static service tcp 6004 6004
Access-group outside_access_in in interface outside
Timeout xlate 03:00
Pat-xlate timeout 0:00:30
Timeout conn 01:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
Sunrpc timeout 0:10:00 h323 0:05:00 h225 mgcp from 01:00 0:05:00 mgcp-pat 0:05:00
Sip timeout 0:30:00 sip_media 0:02:00 prompt Protocol sip-0: 03:00 sip - disconnect 0:02:00
Timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
Floating conn timeout 0:00:00
dynamic-access-policy-registration DfltAccessPolicy
RADIUS AAA server HSS-auth-server protocol
allow only
AAA-server HSS-auth-server (inside) host 192.168.1.222
Timeout 5
key *.
identity of the user by default-domain LOCAL
Enable http server
http 192.168.1.0 255.255.255.0 inside
No snmp server location
No snmp Server contact
Crypto ipsec transform-set ikev1 ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-DES-SHA esp - esp-sha-hmac
Crypto ipsec transform-set ikev1 SHA-ESP-3DES esp-3des esp-sha-hmac
Crypto ipsec transform-set ikev1 esp ESP-DES-MD5-esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-3DES-MD5-esp-3des esp-md5-hmac
Crypto ipsec transform-set ikev1 ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-SHA aes - esp esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
Crypto ipsec transform-set ikev1 ESP-AES-128-MD5-esp - aes esp-md5-hmac
Crypto ipsec pmtu aging infinite - the security association
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 define ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA MD5-ESP-3DES ESP-DES-SHA ESP-DES-MD5
outside_map card crypto 65535-isakmp dynamic ipsec SYSTEM_DEFAULT_CRYPTO_MAP
outside_map interface card crypto outside
trustpool crypto ca policy
Crypto isakmp nat-traversal 30
Crypto ikev1 allow outside
IKEv1 crypto policy 10
authentication crack
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 20
authentication rsa - sig
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 30
preshared authentication
aes-256 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 40
authentication crack
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 50
authentication rsa - sig
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 60
preshared authentication
aes-192 encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 70
authentication crack
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 80
authentication rsa - sig
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 90
preshared authentication
aes encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 100
authentication crack
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 110
authentication rsa - sig
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 120
preshared authentication
3des encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 130
authentication crack
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 140
authentication rsa - sig
the Encryption
sha hash
Group 2
life 86400
IKEv1 crypto policy 150
preshared authentication
the Encryption
sha hash
Group 2
life 86400
Telnet timeout 5
SSH stricthostkeycheck
SSH timeout 5
SSH group dh-Group1-sha1 key exchange
Console timeout 0interface ID client DHCP-client to the outside
dhcpd outside auto_config
!
a basic threat threat detection
Statistics-list of access threat detection
no statistical threat detection tcp-interception
internal HSSvpn group strategy
attributes of Group Policy HSSvpn
value of server WINS 192.168.1.222
value of server DNS 192.168.1.222
Ikev1 VPN-tunnel-Protocol
Split-tunnel-policy tunnelall
Split-tunnel-network-list value Split-Tunnel-ACL
HSS.dk value by default-field
activate dns split-tunnel-all
type tunnel-group HSSvpn remote access
attributes global-tunnel-group HSSvpn
address IP-pool pool
HSS-auth-server authentication-server-group
Group Policy - by default-HSSvpn
password-management
IPSec-attributes tunnel-group HSSvpn
IKEv1 pre-shared-key *.
tunnel-group HSSvpn ppp-attributes
No chap authentication
no authentication ms-chap-v1
ms-chap-v2 authentication
!
class-map inspection_default
match default-inspection-traffic
!
!
type of policy-card inspect dns preset_dns_map
parameters
maximum message length automatic of customer
message-length maximum 512
Policy-map global_policy
class inspection_default
inspect the preset_dns_map dns
inspect the ftp
inspect h323 h225
inspect the h323 ras
inspect the rsh
inspect the rtsp
inspect esmtp
inspect sqlnet
inspect the skinny
inspect sunrpc
inspect xdmcp
inspect the sip
inspect the netbios
inspect the tftp
Review the ip options
!
global service-policy global_policy
context of prompt hostname
no remote anonymous reporting call
Cryptochecksum:c85ff8bf61669bef56b4dad704a4930a
: endHello
Change Split Tunnel VPN in full Tunnel VPN, you have really do much in your configuration.
Seems that have already changed you the 'tunnelspecified' 'tunnelall' in configurations of the 'group policy' . You can delete the setup but that defines the ACL of Split Tunnel
attributes of Group Policy HSSvpn
No split-tunnel-network-list value Split-Tunnel-ACLSeems that you use an internal AAA server to manage authentication rather than on the SAA. I guess if you want to assign a specific IP address for VPN user/username, then it must be done on the side Server?
If you had the "username" on the SAA configurations you can set it up under its framework which "username" IP address gets when he or she connects with the VPN Client.
As naturally as you start using the complete Tunnel and all traffic from the VPN Client starts to get in the tunnel to the ASA you will need a NAT for VPN Client users Internet traffic. You can configure this NAT like this for example:
network of the VPN-POOL object
192.168.30.0 subnet 255.255.255.0interface of VPN-POOL dynamic NAT (outside, outside) after auto source
Note that this is a manual of NAT / double NAT statement real "nat" IS NOT inserted under the 'object' , but the 'object' is rather created it can be used in the "nat" command. I see that your other dynamic PAT configurations are configured with NAT Auto / object NAT network. You can do this like that too if you wish. Personally I do like that.
But as I said before, it seems that you have already configured the VPN to be full of Tunnel. It is perhaps not as it is? While it is connected with VPN, you should be able to check the secure routes (or something like that) section to see if it says "0.0.0.0" If Yes, then it should be tunneling all traffic.
Hope this helps :)
-Jouni
-
Split tunnel with ASA 5510 and PIX506.
Hello
I have the production between Asa 5510 (main office) and Pix 506 VPN tunnel. It is configured so that all traffic is encrypted and moves through the tunnel. This includes remote users behind Pix Internet traffic. I would like to use split tunnel and direct Internet traffic hitting the web directly from Pix instead of going through the tunnel. How can I do this safely? Please see current config Pix below:
:
6.3 (5) PIX version
interface ethernet0 car
interface ethernet1 10baset
ethernet0 nameif outside security0
nameif ethernet1 inside the security100clock timezone EDT - 5
clock to summer time EDT recurring 2 Sun Mar 2:00 1 Sun Nov 02:00
No fixup protocol dns
fixup protocol ftp 21
fixup protocol h323 h225 1720
fixup protocol h323 ras 1718-1719
fixup protocol http 80
fixup protocol they 389
fixup protocol rsh 514
fixup protocol rtsp 554
fixup protocol sip 5060
No fixup protocol sip udp 5060
fixup protocol 2000 skinny
fixup protocol smtp 25
fixup protocol sqlnet 1521
no correction protocol tftp 69
names of
allow VPN 192.x.x.x 255.255.255.0 ip access list one
LocalNet ip access list allow a whole
pager lines 20
opening of session
monitor debug logging
logging warnings put in buffered memory
logging trap warnings
Outside 1500 MTU
Within 1500 MTU
IP address outside 24.x.x.x 255.255.255.0
IP address inside192.x.x.x 255.255.255.0
IP audit name Outside_Attack attack action alarm down reset
IP audit name Outside_Recon info action alarm down reset
interface IP outside the Outside_Recon check
interface IP outside the Outside_Attack check
alarm action IP verification of information
reset the IP audit attack alarm drop action
disable signing verification IP 2000
disable signing verification IP 2001
disable signing verification IP 2004
disable signing verification IP 2005
disable signing verification IP 2150
PDM logging 100 information
history of PDM activate
ARP timeout 14400
Global 1 interface (outside)
NAT (inside) 0 access-list LocalNet
Route outside 0.0.0.0 0.0.0.0 24.x.x.x
Timeout xlate 03:00
Timeout conn 01:00 half-closed 0:10:00 udp 0: CPP 02:00 0:10:00 01:00 h225
H323 timeout 0:05:00 mgcp 0: sip from 05:00 0:30:00 sip_media 0:02:00
Sip timeout - disconnect 0:02:00 prompt Protocol sip-0: 03:00
Timeout, uauth 0:05:00 absolute
GANYMEDE + Protocol Ganymede + AAA-server
AAA-server GANYMEDE + 3 max-failed-attempts
AAA-server GANYMEDE + deadtime 10
RADIUS Protocol RADIUS AAA server
AAA-server RADIUS 3 max-failed-attempts
AAA-RADIUS deadtime 10 Server
AAA-server local LOCAL Protocol
Enable http server
enable floodguard
Permitted connection ipsec sysopt
Crypto ipsec transform-set esp-3des esp-md5-hmac AMC
map UrgentCare 10 ipsec-isakmp crypto
card crypto UrgentCare 10 corresponds to the VPN address
card crypto UrgentCare 10 set counterpart x.x.x.x
card crypto UrgentCare 10 value transform-set AMC
UrgentCare interface card crypto outside
ISAKMP allows outside
ISAKMP key * address x.x.x.x 255.255.255.255 netmask
ISAKMP identity address
part of pre authentication ISAKMP policy 20
ISAKMP policy 20 3des encryption
ISAKMP policy 20 md5 hash
20 2 ISAKMP policy group
ISAKMP duration strategy of life 20 86400
SSH timeout 15
Console timeout 0
Terminal width 80
Cryptochecksum:9701c306b05151471c437f29695ffdbd
: endI would do something by changing the acl that applies to your crypto card. You want to know what you want to support above the tunnel and then deny other networks.
If you have:
192.168.3.0/24
192.168.4.0/24
10.10.10.0/24
172.16.0.0/16
Do something like:
VPN access list allow 192.x.x.x ip 255.255.255.0 192.168.3.0 255.255.255.0
VPN access list allow 192.x.x.x ip 255.255.255.0 192.168.4.0 255.255.255.0
VPN access list allow 192.x.x.x ip 255.255.255.0 10.10.10.0 255.255.255.0
VPN access list allow 192.x.x.x 255.255.255.0 ip 172.16.0.0 255.255.0.0
Then when the traffic is destined for something other than these networks, it will go not to the ISP instead of the tunnel.
HTH,
John
Maybe you are looking for
-
Touchpad does not work on my Satellite C670D - 10 c
Hi all I own a Toshiba Satellite C670D - 10 c with OS installed seven Ultimate (64-bit).To enable the touchpad I did a lot of things, I've updated the BIOS, I have reset the BIOS, I downloaded Synaptics Touch Pad Driver and installed. Still today and
-
With LabVIEW how to control an instrument with a RS232 output, using a USB RS232 converter cable.
With LabVIEW how to control an instrument with a RS232 output, using a USB RS232 converter cable, since I do not have rs232 ports. I have two instruments I want for the control in this way. One is a guarantee of strength Imada SPAS with RS232 output.
-
MSSQL Server Management Studio - Exception was thrown by the target of a call.
Hello I ran a backup in MSSQL Sever Mananagement Studio and I got the error message "Exception was thrown by the target of an invocation." Can someone explain what it means and how to fix it? It happens during the task of "Verifying the database In
-
I have installed my HP printer 6500 wireless and every time I start up I get a message that says that the serscan.sys on Windows XP Home Edition CD ROM file is necessary. The path it is looking is C:\WINDOWS\system32\DRVSTORE\hpwscu01_D71A5E815C9E 2C
-
Problems of scrolling up and down on the computer.
I got a new hard drive on my Sony va10 VGN-N10J windows vista, now I can't scroll upwards or downwards using the key only the sidebar, had put base drivers, can help to someone, there is no update is available, I can see for this problem.